这个反编译的比较深
一,从附件的图标看是python打包的exe文件,先用pyinstxtractor.py 解包
生成的文件在main.exe_extracted目录下,在这里边找到main
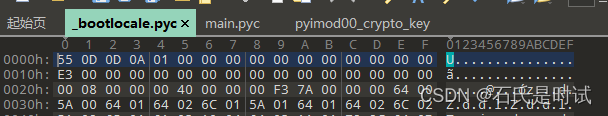
二,把main改名为pyc然后加上头
这个头从包里找一个带头的pyc文件(这里用的_boot文件)把E3前边的16字节插进来
三,用uncompyle6反编译,生成mai.py
N0WayBack\春节红包题\Re_rabbit_Game>uncompyle6 main.pyc > main.py
四,打开main.py查看流程,这里需要运行114514次magic_s()每次会进行一个LCG处理
if self.score < 114514:
self.magic_s()
self.score += 1LCG
def magic_s(self):
p = 16045690984230472446
a = 114514
b = 1919810
self.magic = (a * self.magic + b) % p
然后会打印解密的flag
def print_flag(self):
key = str(self.magic)[:16]
enc = AES.new(key.encode(), AES.MODE_ECB)
flag = enc.decrypt(self.FLAG)
print(flag)
self.draw_text(flag, 22, WHITE, WIDTH / 2, HEIGHT / 2)
self.draw_text('Happy 2023!!!!!', 22, WHITE, WIDTH / 2, HEIGHT / 2 - 40)
五,这里要对FLAG进行AES解密,key在secret里
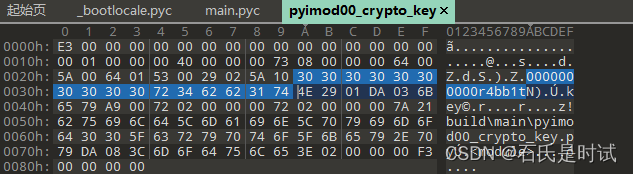
from secret import flag问大姥,这个自己写导入的secret都在 PYZ-00目录里,文件是经过aes加密和zlib压缩
PYZ-00.pyz_extracted六,用网上的脚本进行解密解压,生成secret.pyc文件
import glob
import zlib
import tinyaes
from pathlib import Path
CRYPT_BLOCK_SIZE = 16
# key obtained from pyimod00_crypto_key
key = bytes('0000000000r4bb1t', 'utf-8')
for p in ['secret.pyc.encrypted']: #Path("PYZ-00.pyz_extracted").glob("**/*.pyc.encrypted"):
inf = open(p, 'rb') # encrypted file input
outf = open('secret.py', 'wb') # output file
# Initialization vector
iv = inf.read(CRYPT_BLOCK_SIZE)
cipher = tinyaes.AES(key, iv)
# Decrypt and decompress
plaintext = zlib.decompress(cipher.CTR_xcrypt_buffer(inf.read()))
# Write pyc header
# The header below is for Python 3.8
outf.write(b'\x55\x0d\x0d\x0a\0\0\0\0\0\0\0\0\0\0\0\0')
# Write decrypted data
outf.write(plaintext)
inf.close()
outf.close()
# Delete .pyc.encrypted file
#p.unlink()这里的aes用的key在pyimod00_crypto_key 文件里,这也是个pyc文件,可以反编译也可以直接看,拿到key
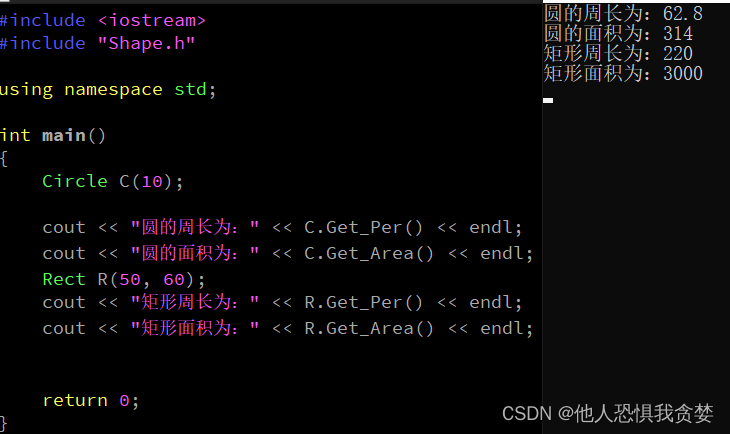
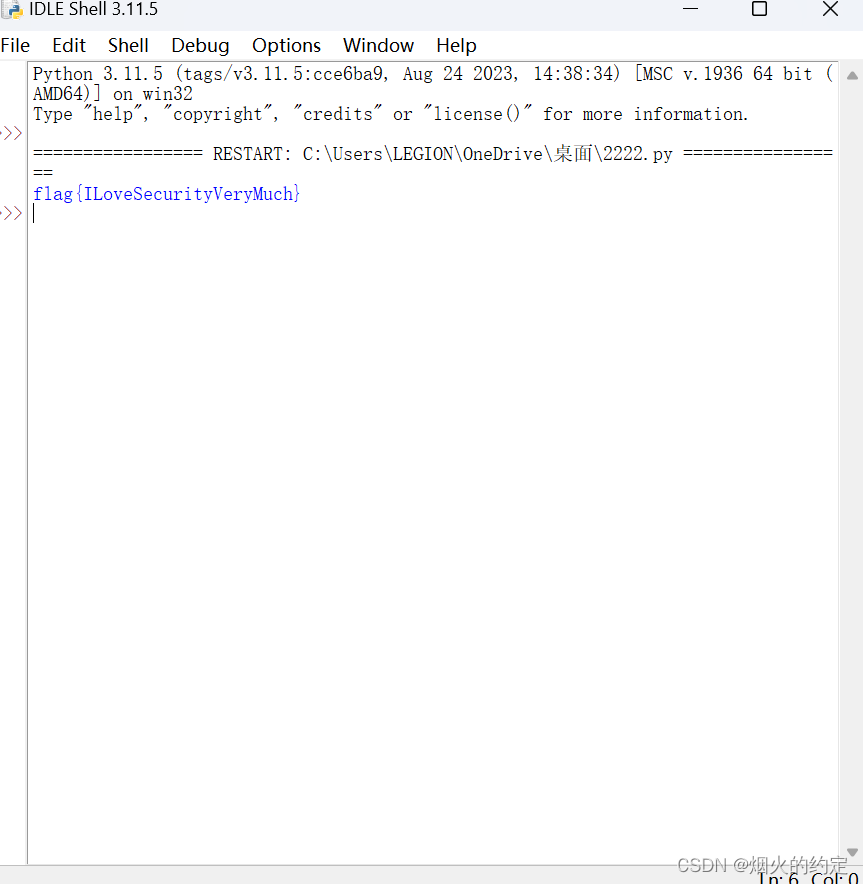
七,得到flag后对,编写代码利用原用函数解密
from Crypto.Cipher import AES
FLAG = bytes.fromhex('17e8fb647b4b10cc8182f0f76649f08bd2d33eacb5fa4ca865d99062f8d0b4c479d7d2328081121536c26c6a4150efb5')
magic = 0
def magic_s():
global magic
p = 16045690984230472446
a = 114514
b = 1919810
magic = (a * magic + b) % p
def print_flag():
key = str(magic)[:16]
enc = AES.new(key.encode(), AES.MODE_ECB)
flag = enc.decrypt(FLAG)
print(flag)
for _ in range(114514):
magic_s()
print_flag()
#