robust互斥锁实现原理(futex内核态源码分析)
news2026/4/10 8:33:50
由于OOMavm一直被内核kill -9杀掉。最终会出现avm重启报错bos_em_service: Fatal glibc error: pthread_mutex_lock.c:450 (__pthread_mutex_lock_full): assertion failed: e ! ESRCH || !robust。这个锁是共享内存上的一个robust互斥锁。而且该BUG报了好几例。正常的来讲如果用户态没有出现内存踩踏不将用户态的lock值踩踏或者将线程的robust list踩坏是不会出现这种错误的。大概率是oom_reaper的原因待深入分析如上图看assert的地方可知当pthread_mutex_lock尝试通过CAS直接上锁失败将系统调用futex_lock_pi陷入内核态然后futex_lock_pi返回了ESRCH错误码但是根据robust互斥锁的设计初衷他是不可能返回ESRCH错误码的。如上图跟踪futex_lock_pi只有这一个地方返回ESRCH。根据他的注释是线程的robust链表损坏或者锁的lock值被踩踏损坏才会出现这错误。接下来深度分析robust相关futex源码。用户态上锁核心代码1THREAD_SETMEM (THREAD_SELF, robust_head.list_op_pending,(void *) (((uintptr_t) mutex-__data.__list.__next)| 1));2oldval atomic_compare_and_exchange_val_acq (mutex-__data.__lock,newval, 0);3if (oldval ! 0){/* The mutex is locked. The kernel will now take care ofeverything. /int private (robust? PTHREAD_ROBUST_MUTEX_PSHARED (mutex): PTHREAD_MUTEX_PSHARED (mutex));int e __futex_lock_pi64 (mutex-__data.__lock, 0 / unused /,NULL, private);if (e ESRCH || e EDEADLK){assert (e ! EDEADLK|| (kind ! PTHREAD_MUTEX_ERRORCHECK_NP kind ! PTHREAD_MUTEX_RECURSIVE_NP));/ ESRCH can happen only for non-robust PI mutexes wherethe owner of the lock died. */assert (e ! ESRCH || !robust);/* Delay the thread indefinitely. /while (1)__futex_abstimed_wait64 ((unsigned int){0}, 0,0 / ignored */, NULL, private);}oldval mutex-__data.__lock;assert (robust || (oldval FUTEX_OWNER_DIED) 0);}4__asm ( ::: memory);ENQUEUE_MUTEX (mutex);/* We need to clear op_pending after we enqueue the mutex. */__asm ( ::: memory);THREAD_SETMEM (THREAD_SELF, robust_head.list_op_pending, NULL);大概解释下上述代码意图。robust互斥锁上锁前先将锁加入线程的list_op_pending链表。然后尝试通过CAS在用户态上锁如果上锁失败则进入步骤3.如果上锁成功则将锁加入线程的list链表并从list_op_pending移除。list_op_pending的设计意图是防止上锁成功后还未加入list链表被kill内核在do_exit的时候就无法释放锁。接下来着重分析用户态上锁失败调用futex_lock_p系统调用及内核在do_exit释放进程的时候是如何处理robust互斥锁的。可以猜到do_exit的时候内核会遍历线程的list_op_pending和list链表然后做处理。futex_cleanup_begin是上一个锁mutex_lock(tsk-futex_exit_mutex);tsk-futex_state FUTEX_STATE_EXITING;futex_cleanup_end是 mutex_unlock(tsk-futex_exit_mutex);重点在cleanup.他调用exit_robust_list遍历list_op_pending和list链表执行handle_futex_death函数。static int handle_futex_death(u32 __user *uaddr, struct task_struct *curr,bool pi, bool pending_op){u32 uval, nval, mval;pid_t owner;int err;/* Futex address must be 32bit aligned */if ((((unsigned long)uaddr) % sizeof(*uaddr)) ! 0)return -1;retry:if (get_user(uval, uaddr))return -1;owner uval FUTEX_TID_MASK;if (pending_op !pi !owner) {futex_wake(uaddr, 1, 1, FUTEX_BITSET_MATCH_ANY);return 0;}if (owner ! task_pid_vnr(curr))return 0;mval (uval FUTEX_WAITERS) | FUTEX_OWNER_DIED;修改用户态锁的值if ((err futex_cmpxchg_value_locked(nval, uaddr, uval, mval))) {switch (err) {case -EFAULT:if (fault_in_user_writeable(uaddr))return -1;goto retry;case -EAGAIN:cond_resched();goto retry;default:WARN_ON_ONCE(1);return err;}}if (nval ! uval)goto retry;if (!pi (uval FUTEX_WAITERS))futex_wake(uaddr, 1, 1, FUTEX_BITSET_MATCH_ANY);return 0;}接下来看系统调用int futex_lock_pi_atomic(u32 __user *uaddr, struct futex_hash_bucket *hb,union futex_key *key,struct futex_pi_state **ps,struct task_struct *task,struct task_struct **exiting,int set_waiters){u32 uval, newval, vpid task_pid_vnr(task);struct futex_q *top_waiter;int ret;if (futex_get_value_locked(uval, uaddr))return -EFAULT;if (unlikely(should_fail_futex(true)))return -EFAULT;if ((unlikely((uval FUTEX_TID_MASK) vpid)))return -EDEADLK;if ((unlikely(should_fail_futex(true))))return -EDEADLK;top_waiter futex_top_waiter(hb, key);if (top_waiter)//优先级反转处理感兴趣自行分析return attach_to_pi_state(uaddr, uval, top_waiter-pi_state, ps);if (!(uval FUTEX_TID_MASK)) {//内核在handle_futex_death改了锁的值进入ifnewval uval FUTEX_OWNER_DIED;newval | vpid;ret lock_pi_update_atomic(uaddr, uval, newval);if (ret)return ret;return 1;//上锁成功}newval uval | FUTEX_WAITERS;ret lock_pi_update_atomic(uaddr, uval, newval);//修改锁的值为newvalif (ret)return ret;return attach_to_pi_owner(uaddr, newval, key, ps, exiting);//会 调用handle_exit_race}static int attach_to_pi_owner(u32 __user *uaddr, u32 uval, union futex_key *key,struct futex_pi_state **ps,struct task_struct **exiting){pid_t pid uval FUTEX_TID_MASK;struct task_struct *p;if (!pid)return -EAGAIN;p find_get_task_by_vpid(pid);if (!p)return handle_exit_race(uaddr, uval, NULL);if (unlikely(p-flags PF_KTHREAD)) {put_task_struct(p);return -EPERM;}raw_spin_lock_irq(p-pi_lock);if (unlikely(p-futex_state ! FUTEX_STATE_OK)) {int ret handle_exit_race(uaddr, uval, p);raw_spin_unlock_irq(p-pi_lock);if (ret -EBUSY)*exiting p;elseput_task_struct(p);return ret;}留给读者的问题do_exit和pthread_mutex_lock并发修改lock值它怎么做的同步
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。如若转载,请注明出处:http://www.coloradmin.cn/o/2502275.html
如若内容造成侵权/违法违规/事实不符,请联系多彩编程网进行投诉反馈,一经查实,立即删除!相关文章
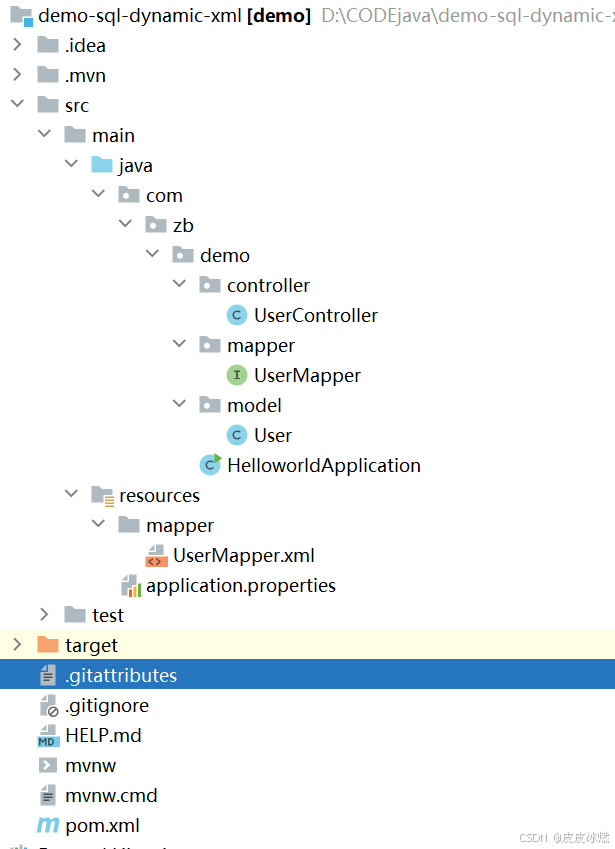
SpringBoot-17-MyBatis动态SQL标签之常用标签
文章目录 1 代码1.1 实体User.java1.2 接口UserMapper.java1.3 映射UserMapper.xml1.3.1 标签if1.3.2 标签if和where1.3.3 标签choose和when和otherwise1.4 UserController.java2 常用动态SQL标签2.1 标签set2.1.1 UserMapper.java2.1.2 UserMapper.xml2.1.3 UserController.ja…
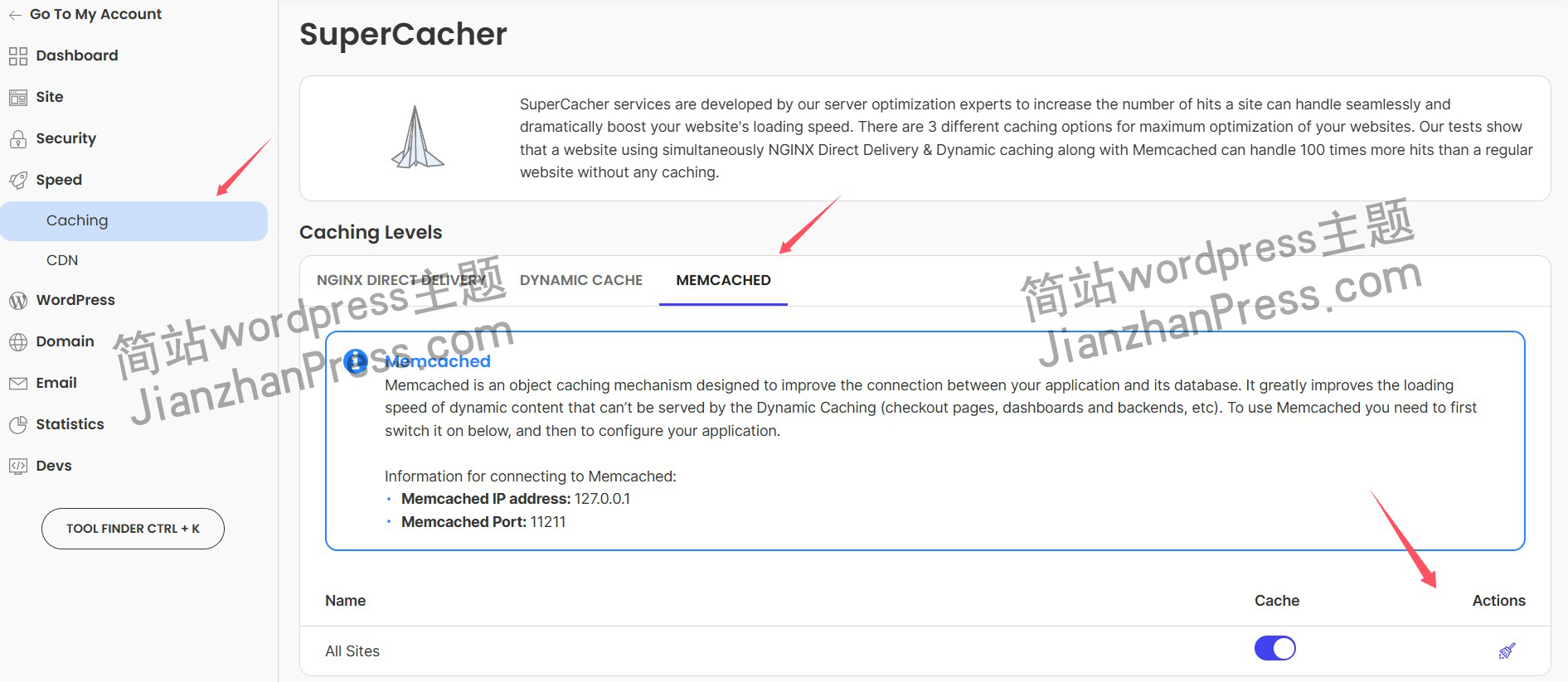
wordpress后台更新后 前端没变化的解决方法
使用siteground主机的wordpress网站,会出现更新了网站内容和修改了php模板文件、js文件、css文件、图片文件后,网站没有变化的情况。
不熟悉siteground主机的新手,遇到这个问题,就很抓狂,明明是哪都没操作错误&#x…
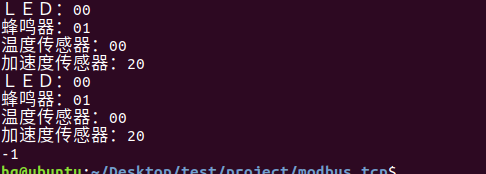
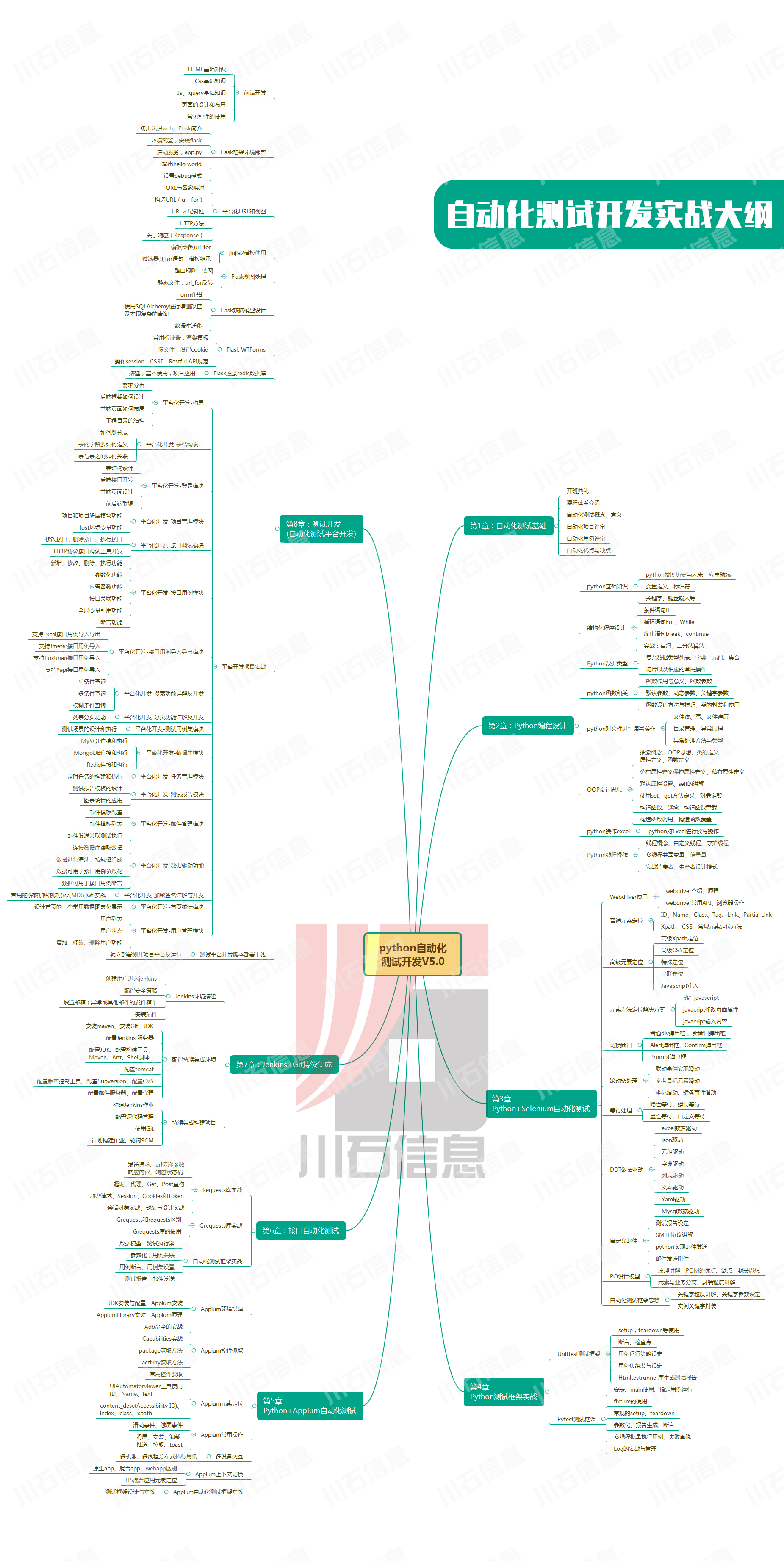
网络编程(Modbus进阶)
思维导图 Modbus RTU(先学一点理论)
概念 Modbus RTU 是工业自动化领域 最广泛应用的串行通信协议,由 Modicon 公司(现施耐德电气)于 1979 年推出。它以 高效率、强健性、易实现的特点成为工业控制系统的通信标准。 包…
UE5 学习系列(二)用户操作界面及介绍
这篇博客是 UE5 学习系列博客的第二篇,在第一篇的基础上展开这篇内容。博客参考的 B 站视频资料和第一篇的链接如下:
【Note】:如果你已经完成安装等操作,可以只执行第一篇博客中 2. 新建一个空白游戏项目 章节操作,重…
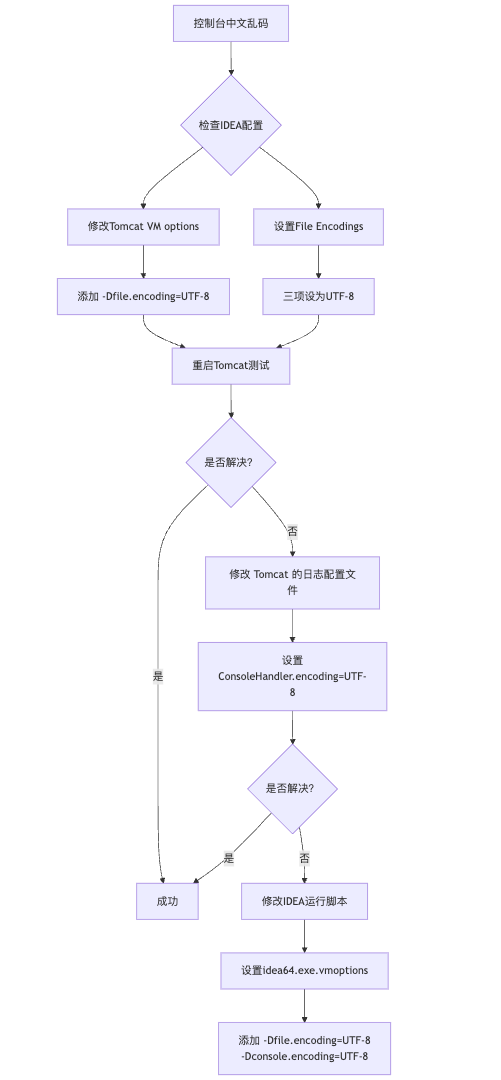
IDEA运行Tomcat出现乱码问题解决汇总
最近正值期末周,有很多同学在写期末Java web作业时,运行tomcat出现乱码问题,经过多次解决与研究,我做了如下整理:
原因:
IDEA本身编码与tomcat的编码与Windows编码不同导致,Windows 系统控制台…
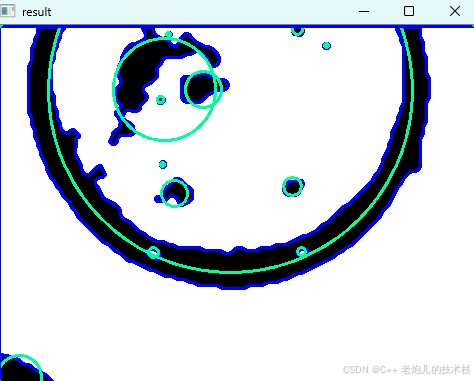
利用最小二乘法找圆心和半径
#include <iostream>
#include <vector>
#include <cmath>
#include <Eigen/Dense> // 需安装Eigen库用于矩阵运算 // 定义点结构
struct Point { double x, y; Point(double x_, double y_) : x(x_), y(y_) {}
}; // 最小二乘法求圆心和半径 …
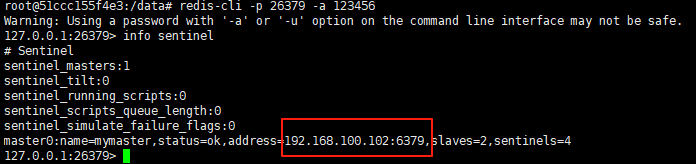
使用docker在3台服务器上搭建基于redis 6.x的一主两从三台均是哨兵模式
一、环境及版本说明
如果服务器已经安装了docker,则忽略此步骤,如果没有安装,则可以按照一下方式安装: 1. 在线安装(有互联网环境): 请看我这篇文章 传送阵>> 点我查看 2. 离线安装(内网环境):请看我这篇文章 传送阵>> 点我查看
说明:假设每台服务器已…
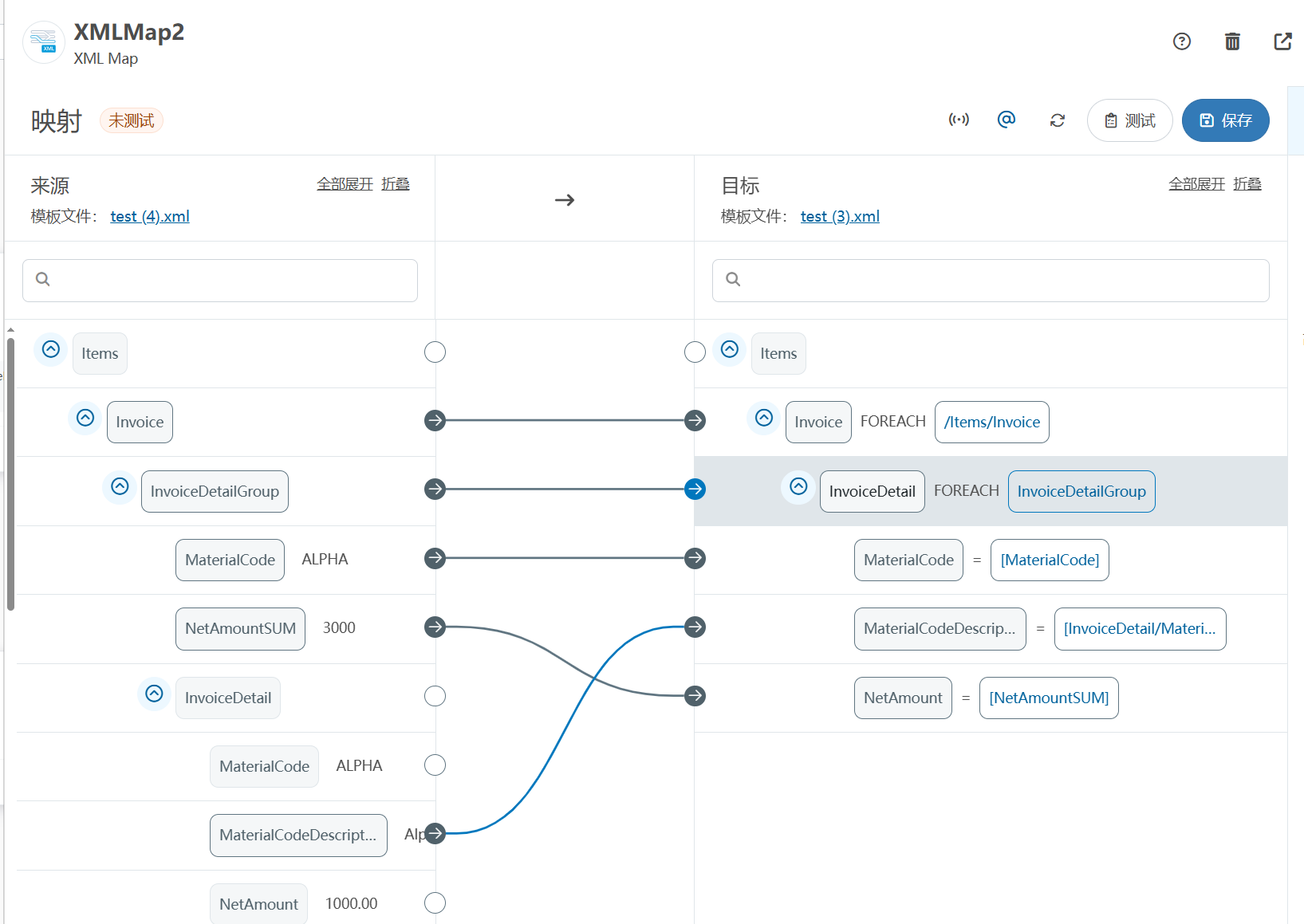
XML Group端口详解
在XML数据映射过程中,经常需要对数据进行分组聚合操作。例如,当处理包含多个物料明细的XML文件时,可能需要将相同物料号的明细归为一组,或对相同物料号的数量进行求和计算。传统实现方式通常需要编写脚本代码,增加了开…
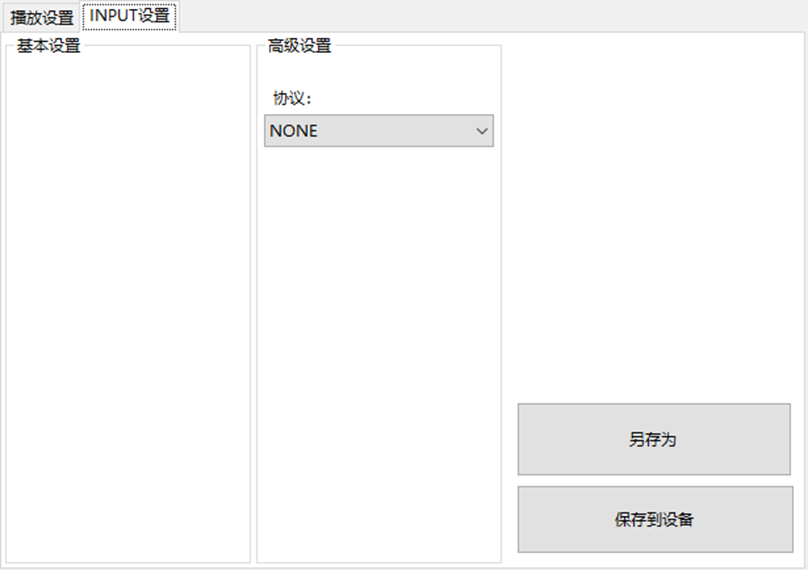
LBE-LEX系列工业语音播放器|预警播报器|喇叭蜂鸣器的上位机配置操作说明
LBE-LEX系列工业语音播放器|预警播报器|喇叭蜂鸣器专为工业环境精心打造,完美适配AGV和无人叉车。同时,集成以太网与语音合成技术,为各类高级系统(如MES、调度系统、库位管理、立库等)提供高效便捷的语音交互体验。
L…
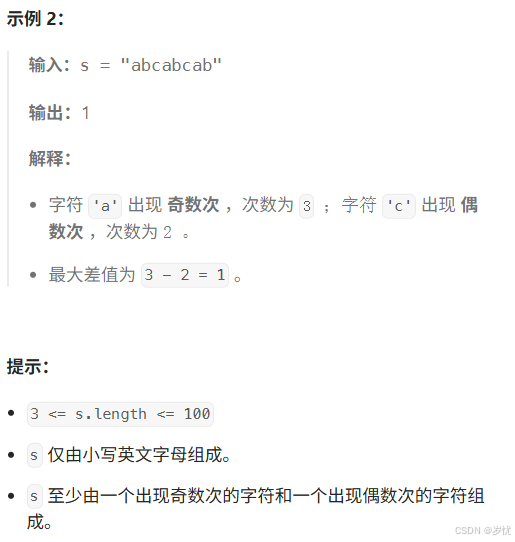
(LeetCode 每日一题) 3442. 奇偶频次间的最大差值 I (哈希、字符串)
题目:3442. 奇偶频次间的最大差值 I 思路 :哈希,时间复杂度0(n)。 用哈希表来记录每个字符串中字符的分布情况,哈希表这里用数组即可实现。
C版本:
class Solution {
public:int maxDifference(string s) {int a[26]…
【大模型RAG】拍照搜题技术架构速览:三层管道、两级检索、兜底大模型
摘要
拍照搜题系统采用“三层管道(多模态 OCR → 语义检索 → 答案渲染)、两级检索(倒排 BM25 向量 HNSW)并以大语言模型兜底”的整体框架: 多模态 OCR 层 将题目图片经过超分、去噪、倾斜校正后,分别用…
【Axure高保真原型】引导弹窗
今天和大家中分享引导弹窗的原型模板,载入页面后,会显示引导弹窗,适用于引导用户使用页面,点击完成后,会显示下一个引导弹窗,直至最后一个引导弹窗完成后进入首页。具体效果可以点击下方视频观看或打开下方…
接口测试中缓存处理策略
在接口测试中,缓存处理策略是一个关键环节,直接影响测试结果的准确性和可靠性。合理的缓存处理策略能够确保测试环境的一致性,避免因缓存数据导致的测试偏差。以下是接口测试中常见的缓存处理策略及其详细说明:
一、缓存处理的核…
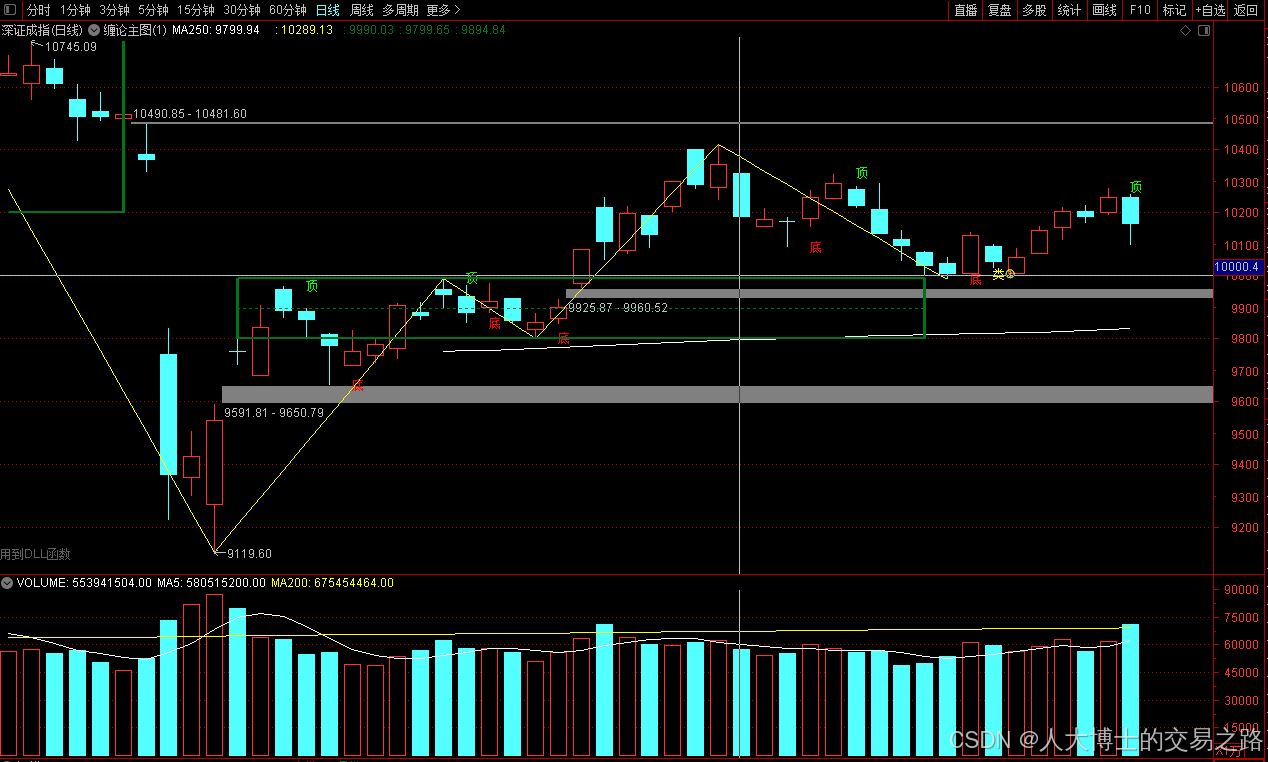
龙虎榜——20250610
上证指数放量收阴线,个股多数下跌,盘中受消息影响大幅波动。 深证指数放量收阴线形成顶分型,指数短线有调整的需求,大概需要一两天。 2025年6月10日龙虎榜行业方向分析 1. 金融科技
代表标的:御银股份、雄帝科技
驱动…
观成科技:隐蔽隧道工具Ligolo-ng加密流量分析
1.工具介绍
Ligolo-ng是一款由go编写的高效隧道工具,该工具基于TUN接口实现其功能,利用反向TCP/TLS连接建立一条隐蔽的通信信道,支持使用Let’s Encrypt自动生成证书。Ligolo-ng的通信隐蔽性体现在其支持多种连接方式,适应复杂网…
铭豹扩展坞 USB转网口 突然无法识别解决方法
当 USB 转网口扩展坞在一台笔记本上无法识别,但在其他电脑上正常工作时,问题通常出在笔记本自身或其与扩展坞的兼容性上。以下是系统化的定位思路和排查步骤,帮助你快速找到故障原因:
背景:
一个M-pard(铭豹)扩展坞的网卡突然无法识别了,扩展出来的三个USB接口正常。…
未来机器人的大脑:如何用神经网络模拟器实现更智能的决策?
编辑:陈萍萍的公主一点人工一点智能 未来机器人的大脑:如何用神经网络模拟器实现更智能的决策?RWM通过双自回归机制有效解决了复合误差、部分可观测性和随机动力学等关键挑战,在不依赖领域特定归纳偏见的条件下实现了卓越的预测准…
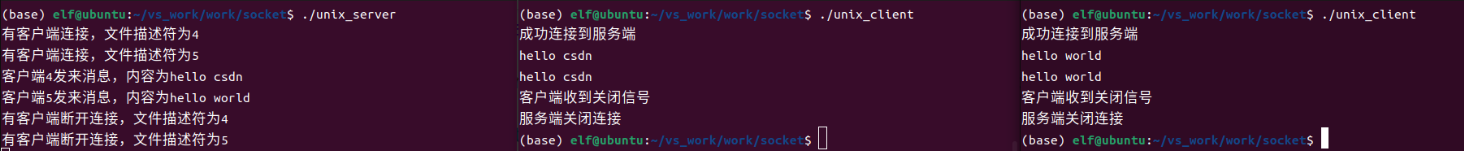
Linux应用开发之网络套接字编程(实例篇)
服务端与客户端单连接
服务端代码
#include <sys/socket.h>
#include <sys/types.h>
#include <netinet/in.h>
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <arpa/inet.h>
#include <pthread.h>
…
华为云AI开发平台ModelArts
华为云ModelArts:重塑AI开发流程的“智能引擎”与“创新加速器”!
在人工智能浪潮席卷全球的2025年,企业拥抱AI的意愿空前高涨,但技术门槛高、流程复杂、资源投入巨大的现实,却让许多创新构想止步于实验室。数据科学家…
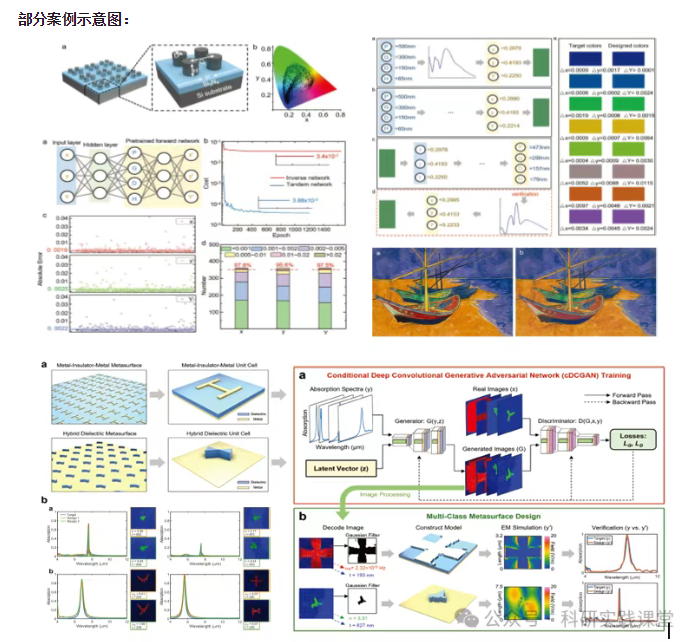
深度学习在微纳光子学中的应用
深度学习在微纳光子学中的主要应用方向
深度学习与微纳光子学的结合主要集中在以下几个方向:
逆向设计 通过神经网络快速预测微纳结构的光学响应,替代传统耗时的数值模拟方法。例如设计超表面、光子晶体等结构。
特征提取与优化 从复杂的光学数据中自…