writeup
news2026/3/31 21:37:07
3-hafuhafu - Writeup by AI题目信息项目内容平台BugKu类型Crypto (RSA)考点RSA 加密、大数分解、私钥计算题目描述题目给出了一个 RSA 公钥和一段 Base64 编码的密文要求解密得到 flag。公钥信息pk (25572000680139535995611501720832880791477922165939342981900803052781801299380515116746468338767634903543966903733806796606602206278399959935132433794098659859300196212479681357625729637405673432324426686371817007872620401911782200407165085213561959188129407530503934445657941975876616947807157374921539755157591354073652053446791467492853468641331291383821277151309959102082454909164831353055082841581194955483740168677333571647148118920605752176786316535817860771644086331929655259439187676703604894258185651165017526744816185992824404330229600417035596255176459265305168198215607187593109533971751842888237880624087, 65537)密文DTlEiAKLE24m19es4TBWl4Uo2MvmQMEYqWBCFggWJlJSjCwl3fT9322ytgudiQW2raDh53e6t2ed ygpFOPMsAPXlU469rlmVng5JyDl0CF0ypevnaM5iCvNT2mBoDadIYnPBVGMtj9HVVPDpMIgv5b F9N5ddQS7JB21oDdQBdDLTkKvcSqegtjNFv04R8yrqOMZYpzdCRRw0j/MMt2JefC6z36mjrTL85 A9EKlwKg5ydW7qELycfjBvzB/cwJ7mJ2I0xVPToa3sSLNDyddFttATwU6wmCa4XaWpTwVR/PfET2 FRj0p8UwYSDdlLLh6gRUVURpT2jc9zx/rhOw考点分析考点分值权重说明RSA 识别10%从公钥格式识别出这是 RSA 加密大数分解40%使用在线工具分解 2048 位的 NRSA 原理30%理解 RSA 加解密过程和数学原理编程实现20%编写 Python 脚本完成解密解题思路技术路线图读取公钥提取 N 和 e分解 N 获取 p,q计算φN计算私钥 dBase64 解码密文RSA 解密提取 Flag核心步骤识别加密方式从pk (N, e)格式识别出是 RSA 公钥分解大数 N使用 factordb.com 等在线工具分解 2048 位的 N计算私钥利用公式d e^(-1) mod φ(N)计算私钥 d解密数据使用 RSA 解密公式m c^d mod n详细步骤步骤 1: 分析公钥参数从题目中提取N 2557200068…8806240872048 位e 65537标准公钥指数步骤 2: 分解大数 N访问 factordb.com 输入 N 进行查询得到分解结果p 149930380465516707151079321019435489399072155945793735032334088844599773034021170995501688132861944516938448679935403246643441984203770825485165700862168437691254557323938150173733659070945061763789341407547559935070758242521126066900261360899379463301621378242061934281538210192731229473900396425739817670867 q 170559166199281256887953076784727902849936084815549184550874370897326056825177365209113910954088389779180174518262922176726833811470419181874717574929460298509184863124213663255559781224744696195678069242025195218017449489985102637547369070225979448169459840545693721393354651993457943927480894225788038743661验证p * q N✓步骤 3: 计算欧拉函数 φ(N)phi(p-1)*(q-1)步骤 4: 计算私钥 ddinverse_mod(e,phi)其中inverse_mod使用扩展欧几里得算法实现。步骤 5: RSA 解密# Base64 解码密文ciphertext_bytesbase64.b64decode(ciphertext_b64)# 转换为整数cint.from_bytes(ciphertext_bytes,big)# RSA 解密mpow(c,d,N)# 转换为字节plaintextlong_to_bytes(m)完整代码#!/usr/bin/env python3# -*- coding: utf-8 -*-importbase64frommathimportgcddefextended_gcd(a,b):扩展欧几里得算法ifa0:returnb,0,1else:g,y,xextended_gcd(b%a,a)returng,x-(b//a)*y,ydefinverse_mod(a,m):计算模逆元g,x,yextended_gcd(a,m)ifg!1:raiseException(modular inverse does not exist)else:returnx%mdeflong_to_bytes(n):将整数转换为字节串ifn0:raiseValueError(n must be non-negative)byte_length(n.bit_length()7)//8result[]whilen0:result.append(n0xff)n8result.reverse()whilelen(result)byte_length:result.insert(0,0)returnbytes(result)# 公钥信息N25572000680139535995611501720832880791477922165939342981900803052781801299380515116746468338767634903543966903733806796606602206278399959935132433794098659859300196212479681357625729637405673432324426686371817007872620401911782200407165085213561959188129407530503934445657941975876616947807157374921539755157591354073652053446791467492853468641331291383821277151309959102082454909164831353055082841581194955483740168677333571647148118920605752176786316535817860771644086331929655259439187676703604894258185651165017526744816185992824404330229600417035596255176459265305168198215607187593109533971751842888237880624087e65537# 分解后的素数因子p149930380465516707151079321019435489399072155945793735032334088844599773034021170995501688132861944516938448679935403246643441984203770825485165700862168437691254557323938150173733659070945061763789341407547559935070758242521126066900261360899379463301621378242061934281538210192731229473900396425739817670867q170559166199281256887953076784727902849936084815549184550874370897326056825177365209113910954088389779180174518262922176726833811470419181874717574929460298509184863124213663255559781224744696195678069242025195218017449489985102637547369070225979448169459840545693721393354651993457943927480894225788038743661# Base64 密文ciphertext_b64DTlEiAKLE24m19es4TBWl4Uo2MvmQMEYqWBCFggWJlJSjCwl3fT9322ytgudiQW2raDh53e6t2ed ygpFOPMsAPXlU469rlmVng5JyDl0CF0ypevnaM5iCvNT2mBoDadIYnPBVGMtj9HVVPDpMIgv5b F9N5ddQS7JB21oDdQBdDLTkKvcSqegtjNFv04R8yrqOMZYpzdCRRw0j/MMt2JefC6z36mjrTL85 A9EKlwKg5ydW7qELycfjBvzB/cwJ7mJ2I0xVPToa3sSLNDyddFttATwU6wmCa4XaWpTwVR/PfET2 FRj0p8UwYSDdlLLh6gRUVURpT2jc9zx/rhOwdefmain():print(*60)print(BugKu CTF - Crypto - 8-3-hafuhafu)print(*60)# 验证分解print(\n[步骤 1] 验证 N 的分解...)ifp*qN:print([] 验证成功p * q N)else:print([-] 验证失败)return# 计算欧拉函数print(\n[步骤 2] 计算欧拉函数 φ(N)...)phi(p-1)*(q-1)# 验证 e 与 phi 互质print(\n[步骤 3] 验证 gcd(e, φ(N)) 1...)ggcd(e,phi)ifg1:print(f[] 验证成功gcd(e, φ(N)) 1)else:print(f[-] 验证失败gcd(e, φ(N)) {g})return# 计算私钥 dprint(\n[步骤 4] 计算私钥 d...)try:dinverse_mod(e,phi)print(f[] 私钥 d 计算成功)exceptExceptionasex:print(f[-] 计算失败{ex})return# RSA 解密print(\n[步骤 5] RSA 解密...)try:ciphertext_bytesbase64.b64decode(ciphertext_b64)cint.from_bytes(ciphertext_bytes,big)mpow(c,d,N)plaintextlong_to_bytes(m)# 查找 flagplaintext_strplaintext.decode(latin-1)ifflag{inplaintext_str:startplaintext_str.find(flag{)endplaintext_str.find(},start)1flagplaintext_str[start:end]print(f\n{*60})print(f[] Flag:{flag})print(f{*60})exceptExceptionasex:print(f[-] 解密失败{ex})importtraceback traceback.print_exc()if__name____main__:main()实际输出 BugKu CTF - Crypto - 8-3-hafuhafu [步骤 1] 验证 N 的分解... [] 验证成功p * q N [步骤 2] 计算欧拉函数 φ(N)... [步骤 3] 验证 gcd(e, φ(N)) 1... [] 验证成功gcd(e, φ(N)) 1 [步骤 4] 计算私钥 d... [] 私钥 d 计算成功 [步骤 5] RSA 解密... [*] Base64 解码完成密文长度256 bytes [*] 解密计算完成 [] 提取到 Flag: flag{XXX} 总结关键知识点RSA 加密原理公钥(N, e)私钥d加密c m^e mod N解密m c^d mod N大数分解对于 2048 位的 RSA如果 N 可以在 factordb.com 等数据库中查到就能快速分解这是 CTF 中常见的 RSA 题型模逆元计算使用扩展欧几里得算法d e^(-1) mod φ(N)工具推荐工具用途链接factordb.com在线大数分解http://factordb.com/AlpertronECM 因数分解https://www.alpertron.com.ar/ECM.HTMYAFU本地大数分解工具GitHubSageMath数学计算软件https://www.sagemath.org/原始提问请阅读目录下的文件解出这道 CTF 题目。
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。如若转载,请注明出处:http://www.coloradmin.cn/o/2469773.html
如若内容造成侵权/违法违规/事实不符,请联系多彩编程网进行投诉反馈,一经查实,立即删除!相关文章
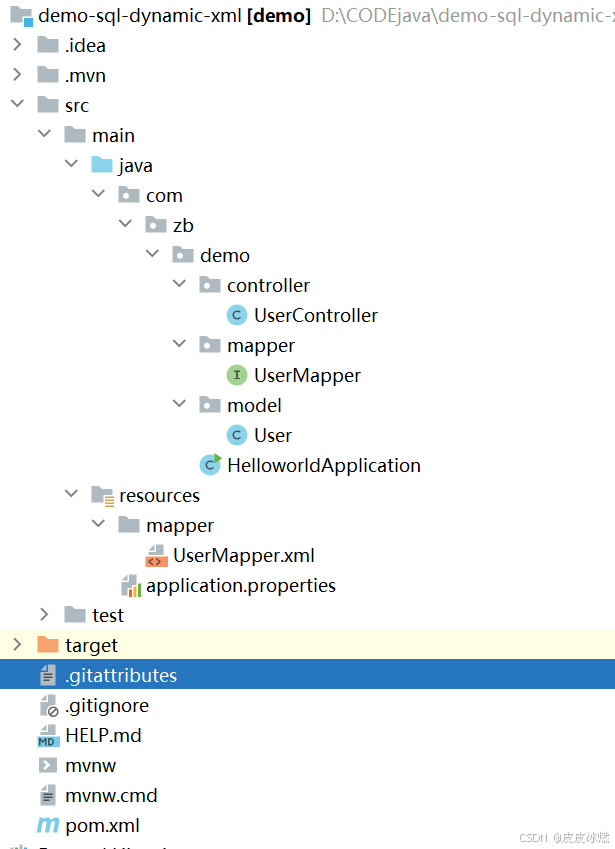
SpringBoot-17-MyBatis动态SQL标签之常用标签
文章目录 1 代码1.1 实体User.java1.2 接口UserMapper.java1.3 映射UserMapper.xml1.3.1 标签if1.3.2 标签if和where1.3.3 标签choose和when和otherwise1.4 UserController.java2 常用动态SQL标签2.1 标签set2.1.1 UserMapper.java2.1.2 UserMapper.xml2.1.3 UserController.ja…
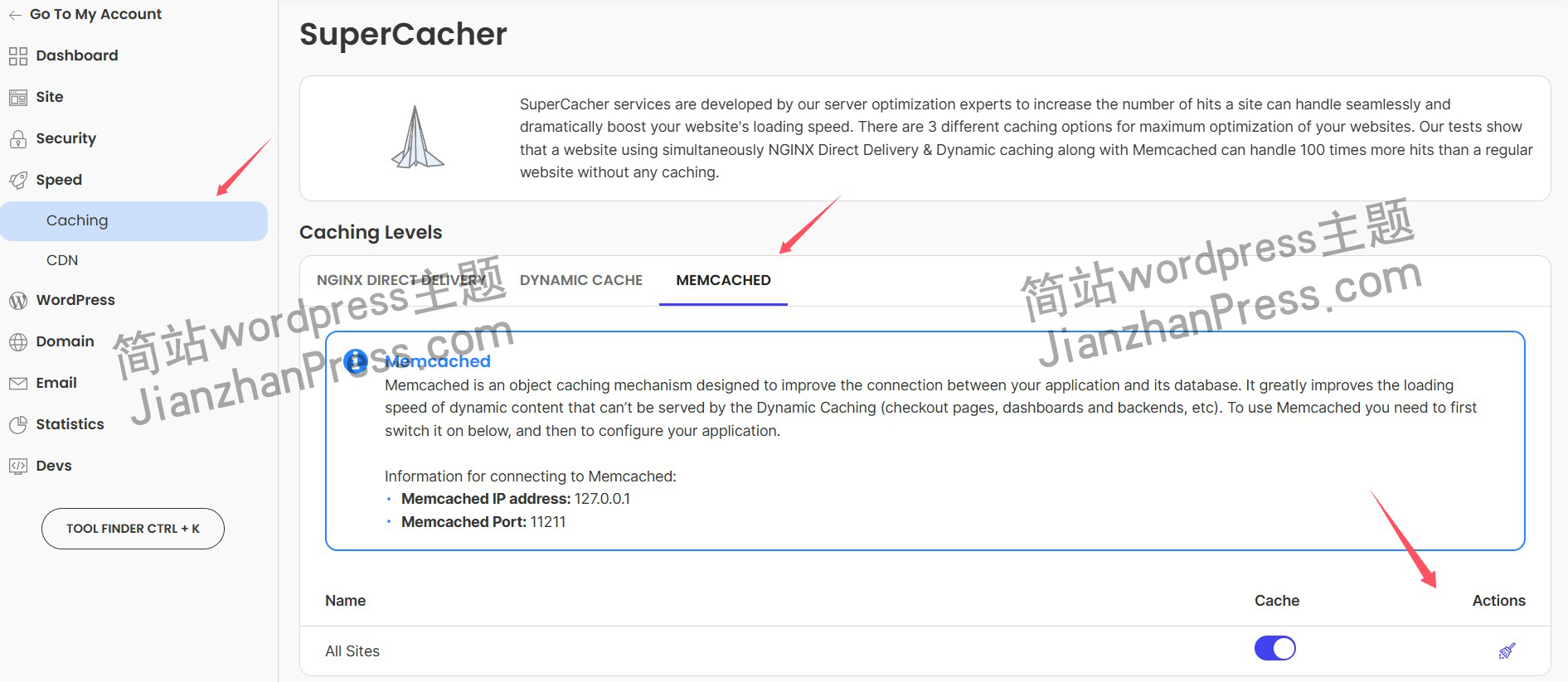
wordpress后台更新后 前端没变化的解决方法
使用siteground主机的wordpress网站,会出现更新了网站内容和修改了php模板文件、js文件、css文件、图片文件后,网站没有变化的情况。
不熟悉siteground主机的新手,遇到这个问题,就很抓狂,明明是哪都没操作错误&#x…
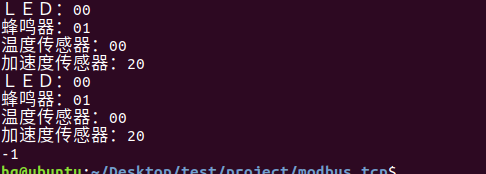
网络编程(Modbus进阶)
思维导图 Modbus RTU(先学一点理论)
概念 Modbus RTU 是工业自动化领域 最广泛应用的串行通信协议,由 Modicon 公司(现施耐德电气)于 1979 年推出。它以 高效率、强健性、易实现的特点成为工业控制系统的通信标准。 包…
UE5 学习系列(二)用户操作界面及介绍
这篇博客是 UE5 学习系列博客的第二篇,在第一篇的基础上展开这篇内容。博客参考的 B 站视频资料和第一篇的链接如下:
【Note】:如果你已经完成安装等操作,可以只执行第一篇博客中 2. 新建一个空白游戏项目 章节操作,重…
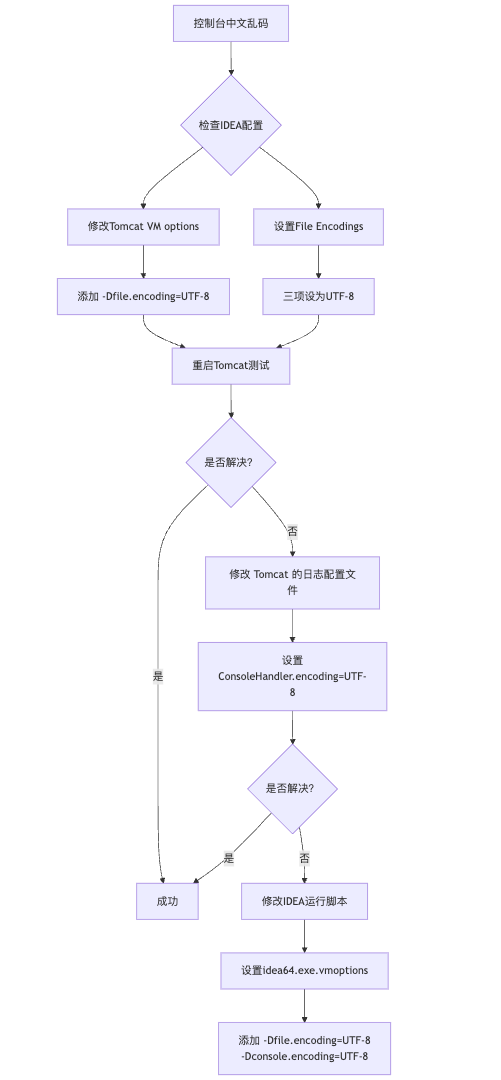
IDEA运行Tomcat出现乱码问题解决汇总
最近正值期末周,有很多同学在写期末Java web作业时,运行tomcat出现乱码问题,经过多次解决与研究,我做了如下整理:
原因:
IDEA本身编码与tomcat的编码与Windows编码不同导致,Windows 系统控制台…
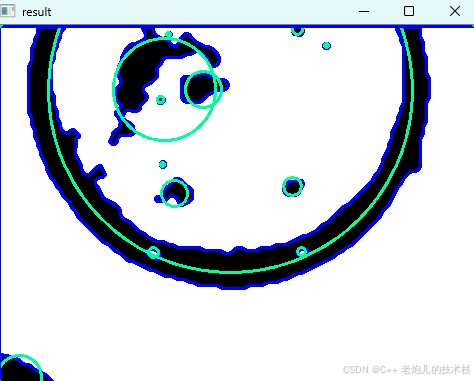
利用最小二乘法找圆心和半径
#include <iostream>
#include <vector>
#include <cmath>
#include <Eigen/Dense> // 需安装Eigen库用于矩阵运算 // 定义点结构
struct Point { double x, y; Point(double x_, double y_) : x(x_), y(y_) {}
}; // 最小二乘法求圆心和半径 …
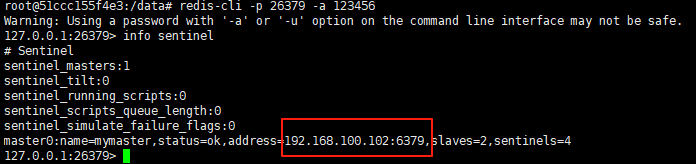
使用docker在3台服务器上搭建基于redis 6.x的一主两从三台均是哨兵模式
一、环境及版本说明
如果服务器已经安装了docker,则忽略此步骤,如果没有安装,则可以按照一下方式安装: 1. 在线安装(有互联网环境): 请看我这篇文章 传送阵>> 点我查看 2. 离线安装(内网环境):请看我这篇文章 传送阵>> 点我查看
说明:假设每台服务器已…
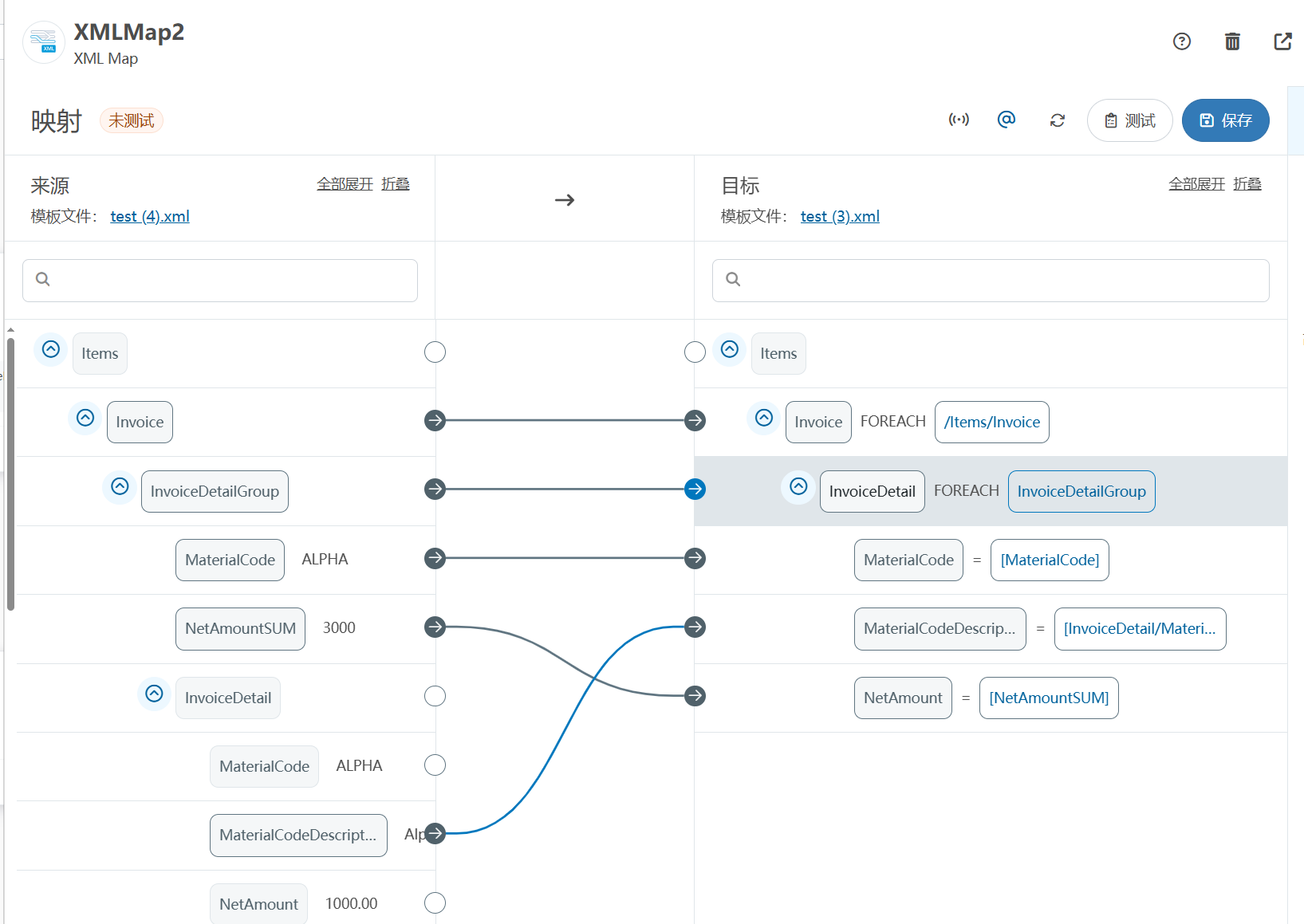
XML Group端口详解
在XML数据映射过程中,经常需要对数据进行分组聚合操作。例如,当处理包含多个物料明细的XML文件时,可能需要将相同物料号的明细归为一组,或对相同物料号的数量进行求和计算。传统实现方式通常需要编写脚本代码,增加了开…
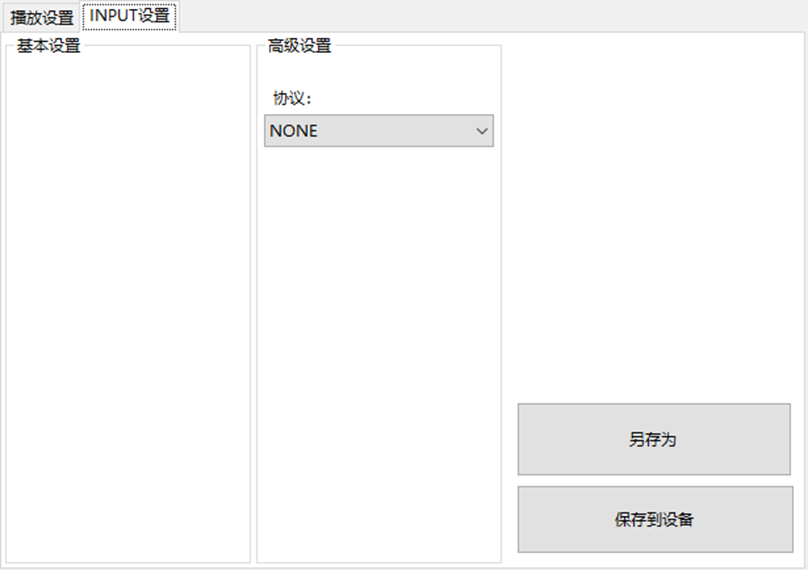
LBE-LEX系列工业语音播放器|预警播报器|喇叭蜂鸣器的上位机配置操作说明
LBE-LEX系列工业语音播放器|预警播报器|喇叭蜂鸣器专为工业环境精心打造,完美适配AGV和无人叉车。同时,集成以太网与语音合成技术,为各类高级系统(如MES、调度系统、库位管理、立库等)提供高效便捷的语音交互体验。
L…
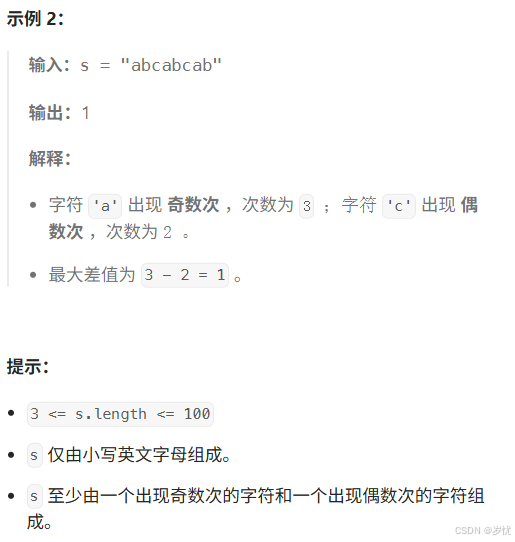
(LeetCode 每日一题) 3442. 奇偶频次间的最大差值 I (哈希、字符串)
题目:3442. 奇偶频次间的最大差值 I 思路 :哈希,时间复杂度0(n)。 用哈希表来记录每个字符串中字符的分布情况,哈希表这里用数组即可实现。
C版本:
class Solution {
public:int maxDifference(string s) {int a[26]…
【大模型RAG】拍照搜题技术架构速览:三层管道、两级检索、兜底大模型
摘要
拍照搜题系统采用“三层管道(多模态 OCR → 语义检索 → 答案渲染)、两级检索(倒排 BM25 向量 HNSW)并以大语言模型兜底”的整体框架: 多模态 OCR 层 将题目图片经过超分、去噪、倾斜校正后,分别用…
【Axure高保真原型】引导弹窗
今天和大家中分享引导弹窗的原型模板,载入页面后,会显示引导弹窗,适用于引导用户使用页面,点击完成后,会显示下一个引导弹窗,直至最后一个引导弹窗完成后进入首页。具体效果可以点击下方视频观看或打开下方…
接口测试中缓存处理策略
在接口测试中,缓存处理策略是一个关键环节,直接影响测试结果的准确性和可靠性。合理的缓存处理策略能够确保测试环境的一致性,避免因缓存数据导致的测试偏差。以下是接口测试中常见的缓存处理策略及其详细说明:
一、缓存处理的核…
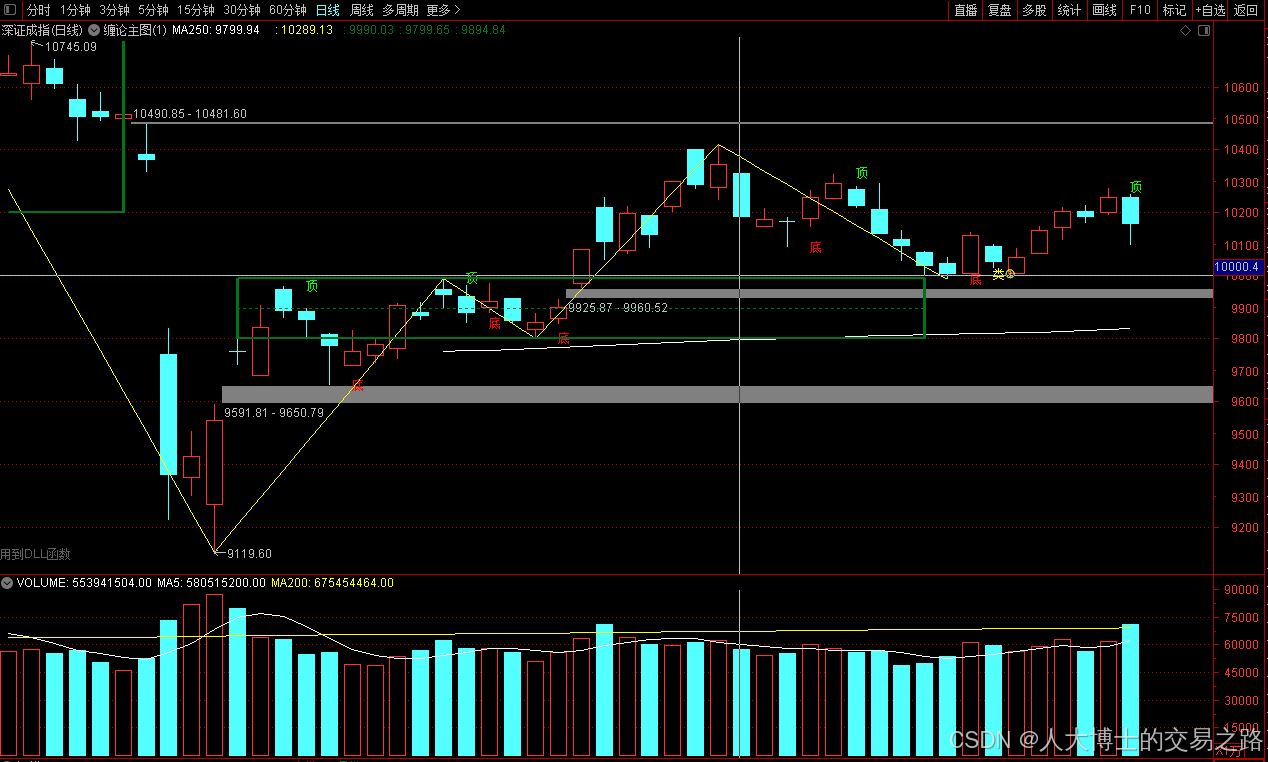
龙虎榜——20250610
上证指数放量收阴线,个股多数下跌,盘中受消息影响大幅波动。 深证指数放量收阴线形成顶分型,指数短线有调整的需求,大概需要一两天。 2025年6月10日龙虎榜行业方向分析 1. 金融科技
代表标的:御银股份、雄帝科技
驱动…
观成科技:隐蔽隧道工具Ligolo-ng加密流量分析
1.工具介绍
Ligolo-ng是一款由go编写的高效隧道工具,该工具基于TUN接口实现其功能,利用反向TCP/TLS连接建立一条隐蔽的通信信道,支持使用Let’s Encrypt自动生成证书。Ligolo-ng的通信隐蔽性体现在其支持多种连接方式,适应复杂网…
铭豹扩展坞 USB转网口 突然无法识别解决方法
当 USB 转网口扩展坞在一台笔记本上无法识别,但在其他电脑上正常工作时,问题通常出在笔记本自身或其与扩展坞的兼容性上。以下是系统化的定位思路和排查步骤,帮助你快速找到故障原因:
背景:
一个M-pard(铭豹)扩展坞的网卡突然无法识别了,扩展出来的三个USB接口正常。…
未来机器人的大脑:如何用神经网络模拟器实现更智能的决策?
编辑:陈萍萍的公主一点人工一点智能 未来机器人的大脑:如何用神经网络模拟器实现更智能的决策?RWM通过双自回归机制有效解决了复合误差、部分可观测性和随机动力学等关键挑战,在不依赖领域特定归纳偏见的条件下实现了卓越的预测准…
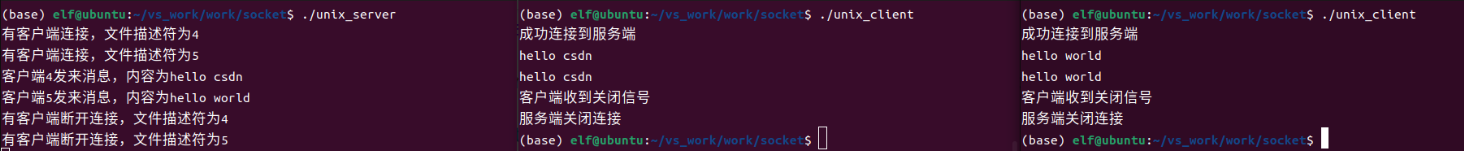
Linux应用开发之网络套接字编程(实例篇)
服务端与客户端单连接
服务端代码
#include <sys/socket.h>
#include <sys/types.h>
#include <netinet/in.h>
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <arpa/inet.h>
#include <pthread.h>
…
华为云AI开发平台ModelArts
华为云ModelArts:重塑AI开发流程的“智能引擎”与“创新加速器”!
在人工智能浪潮席卷全球的2025年,企业拥抱AI的意愿空前高涨,但技术门槛高、流程复杂、资源投入巨大的现实,却让许多创新构想止步于实验室。数据科学家…
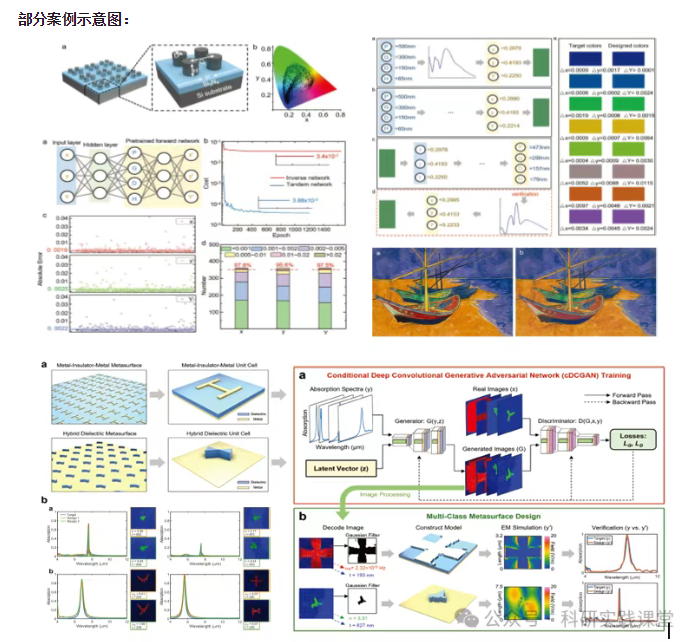
深度学习在微纳光子学中的应用
深度学习在微纳光子学中的主要应用方向
深度学习与微纳光子学的结合主要集中在以下几个方向:
逆向设计 通过神经网络快速预测微纳结构的光学响应,替代传统耗时的数值模拟方法。例如设计超表面、光子晶体等结构。
特征提取与优化 从复杂的光学数据中自…