ubuntu系统检测内核配置是否支持Docker核心模块
news2026/3/28 2:00:19
有一些内核缺少 Docker 所需的核心模块overlayfs、bridge、iptables 相关等所以在安装docker之前可以先检查一下。脚本可以检测Kernel配置是否符合Docker的运行要求源地址https://github.com/moby/moby/blob/master/contrib/check-config.shcheck-config.sh脚本内容如下#!/usr/bin/env sh set -e EXITCODE0 # bits of this were adapted from lxc-checkconfig # see also https://github.com/lxc/lxc/blob/lxc-1.0.2/src/lxc/lxc-checkconfig.in possibleConfigs /proc/config.gz /boot/config-$(uname -r) /usr/src/linux-$(uname -r)/.config /usr/src/linux/.config if [ $# -gt 0 ]; then CONFIG$1 else : ${CONFIG:/proc/config.gz} fi if ! command -v zgrep /dev/null 21; then zgrep() { zcat $2 | grep $1 } fi useColortrue if [ $NO_COLOR 1 ] || [ ! -t 1 ]; then useColorfalse fi kernelVersion$(uname -r) kernelMajor${kernelVersion%%.*} kernelMinor${kernelVersion#$kernelMajor.} kernelMinor${kernelMinor%%.*} is_set() { zgrep CONFIG_$1[y|m] $CONFIG /dev/null } is_set_in_kernel() { zgrep CONFIG_$1y $CONFIG /dev/null } is_set_as_module() { zgrep CONFIG_$1m $CONFIG /dev/null } color() { # if stdout is not a terminal, then dont do color codes. if [ $useColor false ]; then return 0 fi codes if [ $1 bold ]; then codes1 shift fi if [ $# -gt 0 ]; then code case $1 in # see https://en.wikipedia.org/wiki/ANSI_escape_code#Colors black) code30 ;; red) code31 ;; green) code32 ;; yellow) code33 ;; blue) code34 ;; magenta) code35 ;; cyan) code36 ;; white) code37 ;; esac if [ $code ]; then codes${codes:$codes;}$code fi fi printf \033[%sm $codes } wrap_color() { text$1 shift color $ printf %s $text color reset echo } wrap_good() { echo $(wrap_color $1 white): $(wrap_color $2 green) } wrap_bad() { echo $(wrap_color $1 bold): $(wrap_color $2 bold red) } wrap_warning() { wrap_color 2 $* red } check_flag() { if is_set_in_kernel $1; then wrap_good CONFIG_$1 enabled elif is_set_as_module $1; then wrap_good CONFIG_$1 enabled (as module) else wrap_bad CONFIG_$1 missing EXITCODE1 fi } check_flags() { for flag in $; do printf -- - check_flag $flag done } check_command() { if command -v $1 /dev/null 21; then wrap_good $1 command available else wrap_bad $1 command missing EXITCODE1 fi } check_device() { if [ -c $1 ]; then wrap_good $1 present else wrap_bad $1 missing EXITCODE1 fi } check_sysctl() { val$(sysctl -n $1) want$2 if [ $val $want ]; then wrap_good sysctl $1 enabled else wrap_bad sysctl $1 disabled fi } if [ ! -e $CONFIG ]; then wrap_warning warning: $CONFIG does not exist, searching other paths for kernel config ... for tryConfig in $possibleConfigs; do if [ -e $tryConfig ]; then CONFIG$tryConfig break fi done if [ ! -e $CONFIG ]; then wrap_warning error: cannot find kernel config wrap_warning try running this script again, specifying the kernel config: wrap_warning CONFIG/path/to/kernel/.config $0 or $0 /path/to/kernel/.config exit 1 fi fi wrap_color info: reading kernel config from $CONFIG ... white echo echo Generally Necessary: printf -- - if [ $(stat -f -c %t /sys/fs/cgroup 2 /dev/null) 63677270 ]; then wrap_good cgroup hierarchy cgroupv2 cgroupv2ControllerFile/sys/fs/cgroup/cgroup.controllers if [ -f $cgroupv2ControllerFile ]; then echo Controllers: for controller in cpu cpuset io memory pids; do if grep -qE (^| )$controller($| ) $cgroupv2ControllerFile; then echo - $(wrap_good $controller available) else echo - $(wrap_bad $controller missing) fi done else wrap_bad $cgroupv2ControllerFile nonexistent?? fi # TODO find an efficient way to check if cgroup.freeze exists in subdir else cgroupSubsystemDir$(sed -rne /^[^ ] ([^ ]) cgroup ([^ ]*,)?(cpu|cpuacct|cpuset|devices|freezer|memory)[, ].*$/ { s//\1/p; q } /proc/mounts) cgroupDir$(dirname $cgroupSubsystemDir) if [ -d $cgroupDir/cpu ] || [ -d $cgroupDir/cpuacct ] || [ -d $cgroupDir/cpuset ] || [ -d $cgroupDir/devices ] || [ -d $cgroupDir/freezer ] || [ -d $cgroupDir/memory ]; then echo $(wrap_good cgroup hierarchy properly mounted) [$cgroupDir] else if [ $cgroupSubsystemDir ]; then echo $(wrap_bad cgroup hierarchy single mountpoint!) [$cgroupSubsystemDir] else wrap_bad cgroup hierarchy nonexistent?? fi EXITCODE1 echo $(wrap_color (see https://github.com/tianon/cgroupfs-mount) yellow) fi fi if [ $(cat /sys/module/apparmor/parameters/enabled 2 /dev/null) Y ]; then printf -- - if command -v apparmor_parser /dev/null 21; then wrap_good apparmor enabled and tools installed else wrap_bad apparmor enabled, but apparmor_parser missing printf if command -v apt-get /dev/null 21; then wrap_color (use apt-get install apparmor to fix this) elif command -v yum /dev/null 21; then wrap_color (your best bet is yum install apparmor-parser) else wrap_color (look for an apparmor package for your distribution) fi EXITCODE1 fi fi check_flags \ NAMESPACES NET_NS PID_NS IPC_NS UTS_NS \ CGROUPS CGROUP_CPUACCT CGROUP_DEVICE CGROUP_FREEZER CGROUP_SCHED CPUSETS MEMCG \ KEYS \ VETH BRIDGE BRIDGE_NETFILTER \ IP_NF_FILTER IP_NF_MANGLE IP_NF_TARGET_MASQUERADE \ IP6_NF_FILTER IP6_NF_MANGLE IP6_NF_TARGET_MASQUERADE \ NETFILTER_XT_MATCH_ADDRTYPE \ NETFILTER_XT_MATCH_CONNTRACK \ NETFILTER_XT_MATCH_IPVS \ NETFILTER_XT_MARK \ IP_NF_RAW IP_NF_NAT NF_NAT \ IP6_NF_RAW IP6_NF_NAT NF_NAT \ POSIX_MQUEUE # (POSIX_MQUEUE is required for bind-mounting /dev/mqueue into containers) if [ $kernelMajor -lt 4 ] || ([ $kernelMajor -eq 4 ] [ $kernelMinor -lt 8 ]); then check_flags DEVPTS_MULTIPLE_INSTANCES fi if [ $kernelMajor -lt 5 ] || [ $kernelMajor -eq 5 -a $kernelMinor -le 1 ]; then check_flags NF_NAT_IPV4 fi if [ $kernelMajor -lt 5 ] || [ $kernelMajor -eq 5 -a $kernelMinor -le 2 ]; then check_flags NF_NAT_NEEDED fi # check availability of BPF_CGROUP_DEVICE support if [ $kernelMajor -ge 5 ] || ([ $kernelMajor -eq 4 ] [ $kernelMinor -ge 15 ]); then check_flags CGROUP_BPF fi echo echo Optional Features: { check_flags USER_NS } { check_flags SECCOMP check_flags SECCOMP_FILTER } { check_flags CGROUP_PIDS } { # Kernel v5.8 removes MEMCG_SWAP_ENABLED and deprecates MEMCG_SWAP. if [ $kernelMajor -lt 5 ] || [ $kernelMajor -eq 5 -a $kernelMinor -lt 8 ]; then CODE${EXITCODE} check_flags MEMCG_SWAP MEMCG_SWAP_ENABLED # FIXME this check is cgroupv1-specific if [ -e /sys/fs/cgroup/memory/memory.memsw.limit_in_bytes ]; then echo $(wrap_color (cgroup swap accounting is currently enabled) bold black) EXITCODE${CODE} elif is_set MEMCG_SWAP ! is_set MEMCG_SWAP_ENABLED; then echo $(wrap_color (cgroup swap accounting is currently not enabled, you can enable it by setting boot option swapaccount1) bold black) fi else # Kernel v5.8 enables swap accounting by default. echo $(wrap_color (cgroup swap accounting is currently enabled) bold black) fi } { if is_set LEGACY_VSYSCALL_NATIVE; then printf -- - wrap_bad CONFIG_LEGACY_VSYSCALL_NATIVE enabled echo $(wrap_color (dangerous, provides an ASLR-bypassing target with usable ROP gadgets.) bold black) elif is_set LEGACY_VSYSCALL_EMULATE; then printf -- - wrap_good CONFIG_LEGACY_VSYSCALL_EMULATE enabled elif is_set LEGACY_VSYSCALL_NONE; then printf -- - wrap_bad CONFIG_LEGACY_VSYSCALL_NONE enabled echo $(wrap_color (containers using eglibc 2.13 will not work. Switch to bold black) echo $(wrap_color CONFIG_VSYSCALL_[NATIVE|EMULATE] or use vsyscall[native|emulate] bold black) echo $(wrap_color on kernel command line. Note that this will disable ASLR for the, bold black) echo $(wrap_color VDSO which may assist in exploiting security vulnerabilities.) bold black) # else Older kernels (prior to 3dc33bd30f3e, released in v4.40-rc1) do # not have these LEGACY_VSYSCALL options and are effectively # LEGACY_VSYSCALL_EMULATE. Even older kernels are presumably # effectively LEGACY_VSYSCALL_NATIVE. fi } if [ $kernelMajor -lt 4 ] || ([ $kernelMajor -eq 4 ] [ $kernelMinor -le 5 ]); then check_flags MEMCG_KMEM fi if [ $kernelMajor -lt 3 ] || ([ $kernelMajor -eq 3 ] [ $kernelMinor -le 18 ]); then check_flags RESOURCE_COUNTERS fi if [ $kernelMajor -lt 3 ] || ([ $kernelMajor -eq 3 ] [ $kernelMinor -le 13 ]); then netprioNETPRIO_CGROUP else netprioCGROUP_NET_PRIO fi if [ $kernelMajor -lt 5 ]; then check_flags IOSCHED_CFQ CFQ_GROUP_IOSCHED fi check_flags \ BLK_CGROUP BLK_DEV_THROTTLING \ CGROUP_PERF \ CGROUP_HUGETLB \ NET_CLS_CGROUP $netprio \ CFS_BANDWIDTH FAIR_GROUP_SCHED \ IP_NF_TARGET_REDIRECT \ IP_SCTP \ IP_VS \ IP_VS_NFCT \ IP_VS_PROTO_TCP \ IP_VS_PROTO_UDP \ IP_VS_RR \ SECURITY_SELINUX \ SECURITY_APPARMOR check_flags \ NFT_CT \ NFT_FIB_IPV4 \ NFT_FIB_IPV6 \ NFT_FIB \ NFT_MASQ \ NFT_NAT \ NF_TABLES if ! is_set EXT4_USE_FOR_EXT2; then check_flags EXT3_FS EXT3_FS_XATTR EXT3_FS_POSIX_ACL EXT3_FS_SECURITY if ! is_set EXT3_FS || ! is_set EXT3_FS_XATTR || ! is_set EXT3_FS_POSIX_ACL || ! is_set EXT3_FS_SECURITY; then echo $(wrap_color (enable these ext3 configs if you are using ext3 as backing filesystem) bold black) fi fi check_flags EXT4_FS EXT4_FS_POSIX_ACL EXT4_FS_SECURITY if ! is_set EXT4_FS || ! is_set EXT4_FS_POSIX_ACL || ! is_set EXT4_FS_SECURITY; then if is_set EXT4_USE_FOR_EXT2; then echo $(wrap_color enable these ext4 configs if you are using ext3 or ext4 as backing filesystem bold black) else echo $(wrap_color enable these ext4 configs if you are using ext4 as backing filesystem bold black) fi fi echo - Network Drivers: echo - \$(wrap_color bridge blue)\: check_sysctl net.ipv4.ip_forward 1 | sed s/^/ - / check_sysctl net.ipv6.conf.all.forwarding 1 | sed s/^/ - / check_sysctl net.ipv6.conf.default.forwarding 1 | sed s/^/ - / echo - \$(wrap_color overlay blue)\: check_flags VXLAN BRIDGE_VLAN_FILTERING | sed s/^/ / echo Optional (for encrypted networks): check_flags CRYPTO CRYPTO_AEAD CRYPTO_GCM CRYPTO_SEQIV CRYPTO_GHASH \ XFRM XFRM_USER XFRM_ALGO INET_ESP NETFILTER_XT_MATCH_BPF | sed s/^/ / if [ $kernelMajor -lt 5 ] || [ $kernelMajor -eq 5 -a $kernelMinor -le 3 ]; then check_flags INET_XFRM_MODE_TRANSPORT | sed s/^/ / fi echo - \$(wrap_color ipvlan blue)\: check_flags IPVLAN | sed s/^/ / echo - \$(wrap_color macvlan blue)\: check_flags MACVLAN DUMMY | sed s/^/ / echo - \$(wrap_color ftp,tftp client in container blue)\: check_flags NF_NAT_FTP NF_CONNTRACK_FTP NF_NAT_TFTP NF_CONNTRACK_TFTP | sed s/^/ / # only fail if no storage drivers available CODE${EXITCODE} EXITCODE0 STORAGE1 echo - Storage Drivers: echo - \$(wrap_color btrfs blue)\: check_flags BTRFS_FS | sed s/^/ / check_flags BTRFS_FS_POSIX_ACL | sed s/^/ / [ $EXITCODE 0 ] STORAGE0 EXITCODE0 echo - \$(wrap_color overlay blue)\: check_flags OVERLAY_FS | sed s/^/ / [ $EXITCODE 0 ] STORAGE0 EXITCODE0 echo - \$(wrap_color zfs blue)\: printf - check_device /dev/zfs printf - check_command zfs printf - check_command zpool [ $EXITCODE 0 ] STORAGE0 EXITCODE0 EXITCODE$CODE [ $STORAGE 1 ] EXITCODE1 echo check_limit_over() { if [ $(cat $1) -le $2 ]; then wrap_bad - $1 $(cat $1) wrap_color This should be set to at least $2, for example set: sysctl -w kernel/keys/root_maxkeys1000000 bold black EXITCODE1 else wrap_good - $1 $(cat $1) fi } echo Limits: check_limit_over /proc/sys/kernel/keys/root_maxkeys 10000 echo exit $EXITCODEchmod x check-config.sh./check-config.sh输出内容结果主要是两部分Generally Necessary: 表示必要的配置如果有显示missing的地方需要在内核配置中打开重新编译烧录内核以支持DockerOptional Features: 是可选配置根据需要打开。
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。如若转载,请注明出处:http://www.coloradmin.cn/o/2456389.html
如若内容造成侵权/违法违规/事实不符,请联系多彩编程网进行投诉反馈,一经查实,立即删除!相关文章
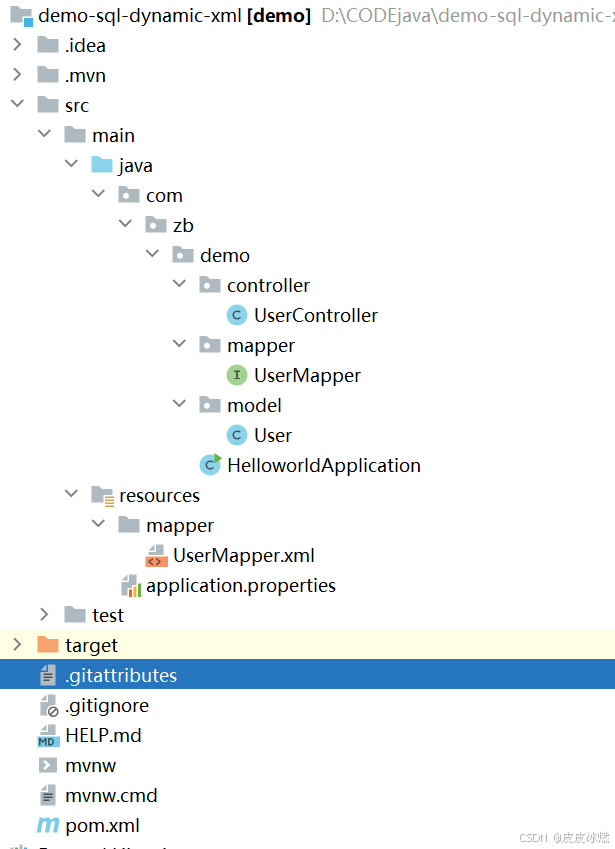
SpringBoot-17-MyBatis动态SQL标签之常用标签
文章目录 1 代码1.1 实体User.java1.2 接口UserMapper.java1.3 映射UserMapper.xml1.3.1 标签if1.3.2 标签if和where1.3.3 标签choose和when和otherwise1.4 UserController.java2 常用动态SQL标签2.1 标签set2.1.1 UserMapper.java2.1.2 UserMapper.xml2.1.3 UserController.ja…
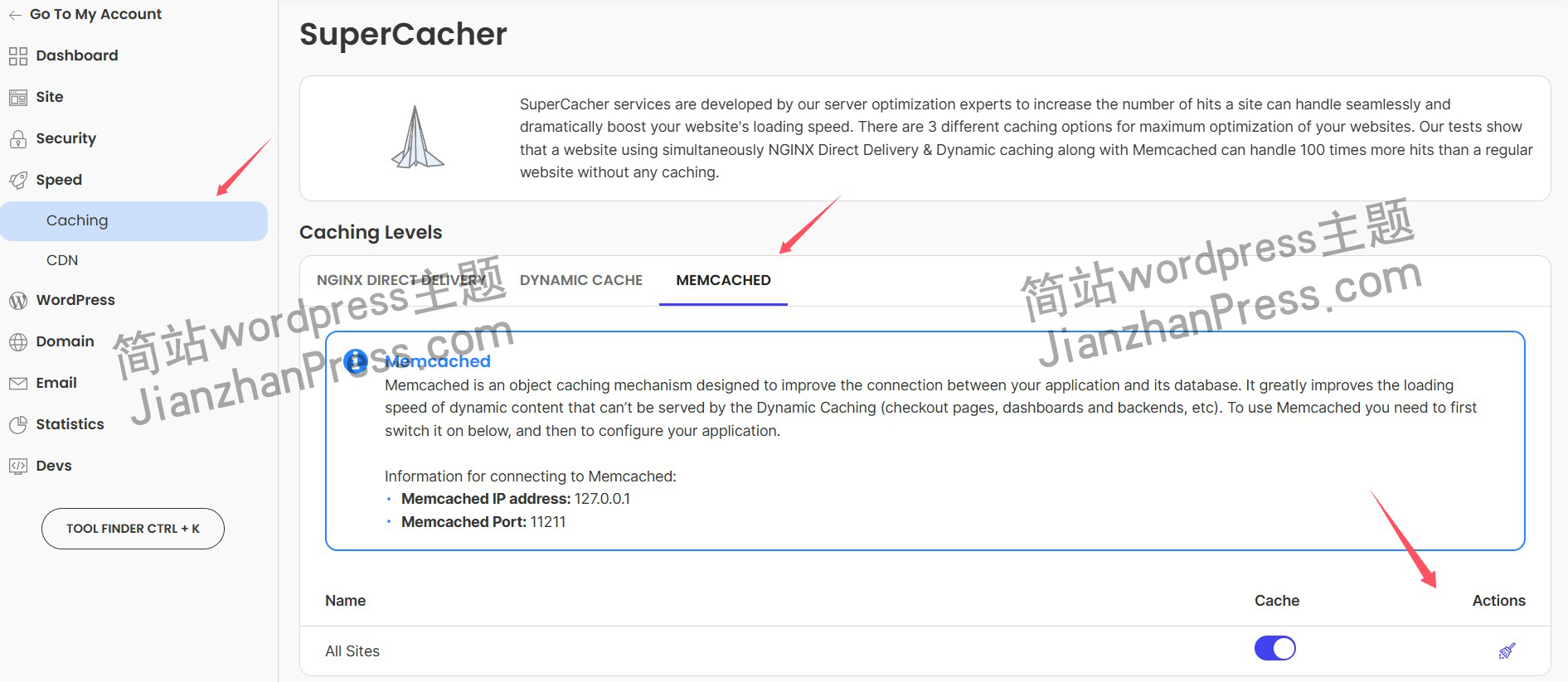
wordpress后台更新后 前端没变化的解决方法
使用siteground主机的wordpress网站,会出现更新了网站内容和修改了php模板文件、js文件、css文件、图片文件后,网站没有变化的情况。
不熟悉siteground主机的新手,遇到这个问题,就很抓狂,明明是哪都没操作错误&#x…
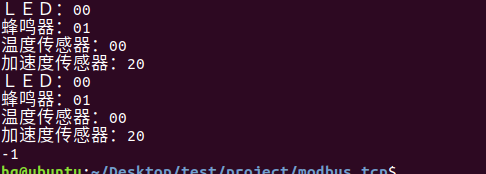
网络编程(Modbus进阶)
思维导图 Modbus RTU(先学一点理论)
概念 Modbus RTU 是工业自动化领域 最广泛应用的串行通信协议,由 Modicon 公司(现施耐德电气)于 1979 年推出。它以 高效率、强健性、易实现的特点成为工业控制系统的通信标准。 包…
UE5 学习系列(二)用户操作界面及介绍
这篇博客是 UE5 学习系列博客的第二篇,在第一篇的基础上展开这篇内容。博客参考的 B 站视频资料和第一篇的链接如下:
【Note】:如果你已经完成安装等操作,可以只执行第一篇博客中 2. 新建一个空白游戏项目 章节操作,重…
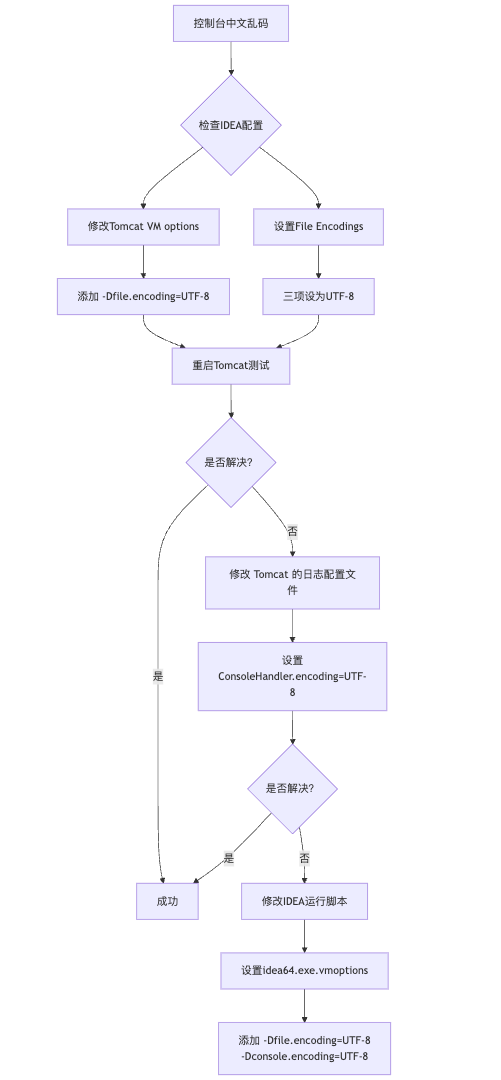
IDEA运行Tomcat出现乱码问题解决汇总
最近正值期末周,有很多同学在写期末Java web作业时,运行tomcat出现乱码问题,经过多次解决与研究,我做了如下整理:
原因:
IDEA本身编码与tomcat的编码与Windows编码不同导致,Windows 系统控制台…
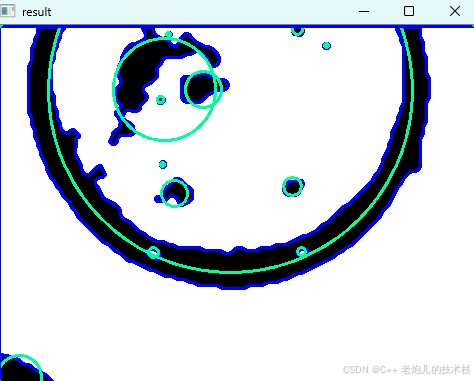
利用最小二乘法找圆心和半径
#include <iostream>
#include <vector>
#include <cmath>
#include <Eigen/Dense> // 需安装Eigen库用于矩阵运算 // 定义点结构
struct Point { double x, y; Point(double x_, double y_) : x(x_), y(y_) {}
}; // 最小二乘法求圆心和半径 …
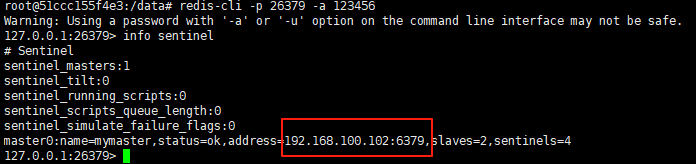
使用docker在3台服务器上搭建基于redis 6.x的一主两从三台均是哨兵模式
一、环境及版本说明
如果服务器已经安装了docker,则忽略此步骤,如果没有安装,则可以按照一下方式安装: 1. 在线安装(有互联网环境): 请看我这篇文章 传送阵>> 点我查看 2. 离线安装(内网环境):请看我这篇文章 传送阵>> 点我查看
说明:假设每台服务器已…
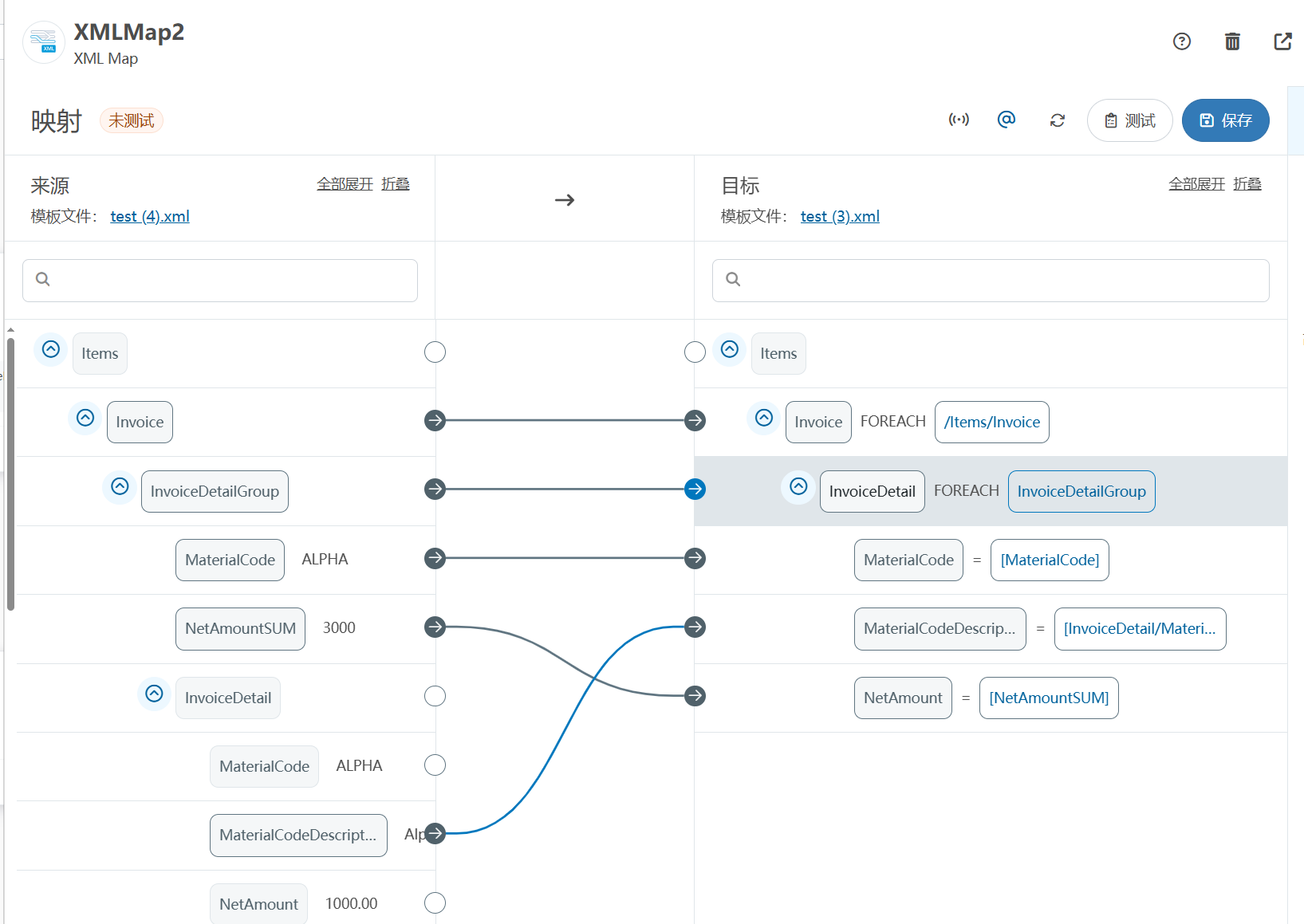
XML Group端口详解
在XML数据映射过程中,经常需要对数据进行分组聚合操作。例如,当处理包含多个物料明细的XML文件时,可能需要将相同物料号的明细归为一组,或对相同物料号的数量进行求和计算。传统实现方式通常需要编写脚本代码,增加了开…
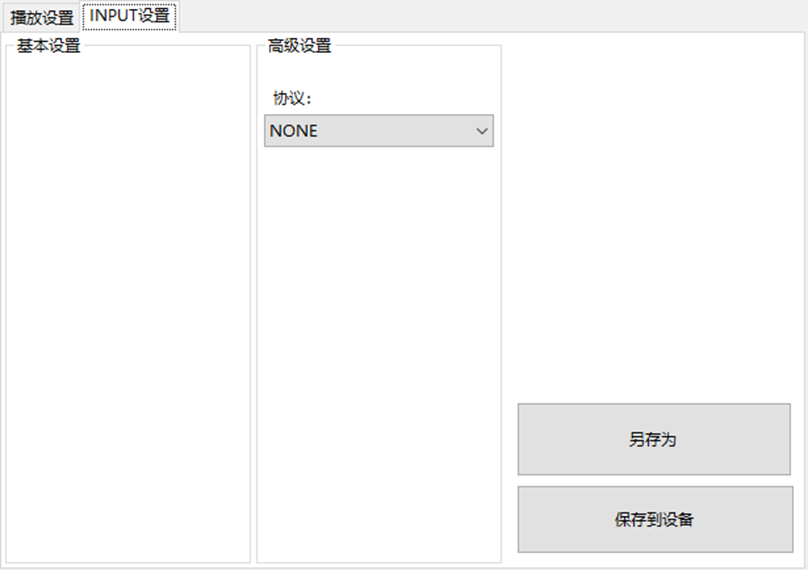
LBE-LEX系列工业语音播放器|预警播报器|喇叭蜂鸣器的上位机配置操作说明
LBE-LEX系列工业语音播放器|预警播报器|喇叭蜂鸣器专为工业环境精心打造,完美适配AGV和无人叉车。同时,集成以太网与语音合成技术,为各类高级系统(如MES、调度系统、库位管理、立库等)提供高效便捷的语音交互体验。
L…
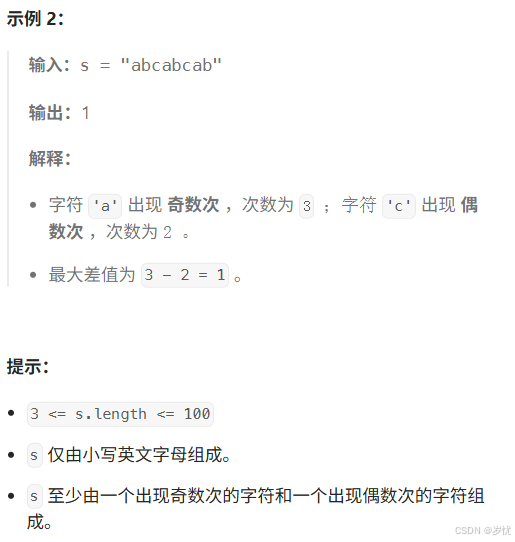
(LeetCode 每日一题) 3442. 奇偶频次间的最大差值 I (哈希、字符串)
题目:3442. 奇偶频次间的最大差值 I 思路 :哈希,时间复杂度0(n)。 用哈希表来记录每个字符串中字符的分布情况,哈希表这里用数组即可实现。
C版本:
class Solution {
public:int maxDifference(string s) {int a[26]…
【大模型RAG】拍照搜题技术架构速览:三层管道、两级检索、兜底大模型
摘要
拍照搜题系统采用“三层管道(多模态 OCR → 语义检索 → 答案渲染)、两级检索(倒排 BM25 向量 HNSW)并以大语言模型兜底”的整体框架: 多模态 OCR 层 将题目图片经过超分、去噪、倾斜校正后,分别用…
【Axure高保真原型】引导弹窗
今天和大家中分享引导弹窗的原型模板,载入页面后,会显示引导弹窗,适用于引导用户使用页面,点击完成后,会显示下一个引导弹窗,直至最后一个引导弹窗完成后进入首页。具体效果可以点击下方视频观看或打开下方…
接口测试中缓存处理策略
在接口测试中,缓存处理策略是一个关键环节,直接影响测试结果的准确性和可靠性。合理的缓存处理策略能够确保测试环境的一致性,避免因缓存数据导致的测试偏差。以下是接口测试中常见的缓存处理策略及其详细说明:
一、缓存处理的核…
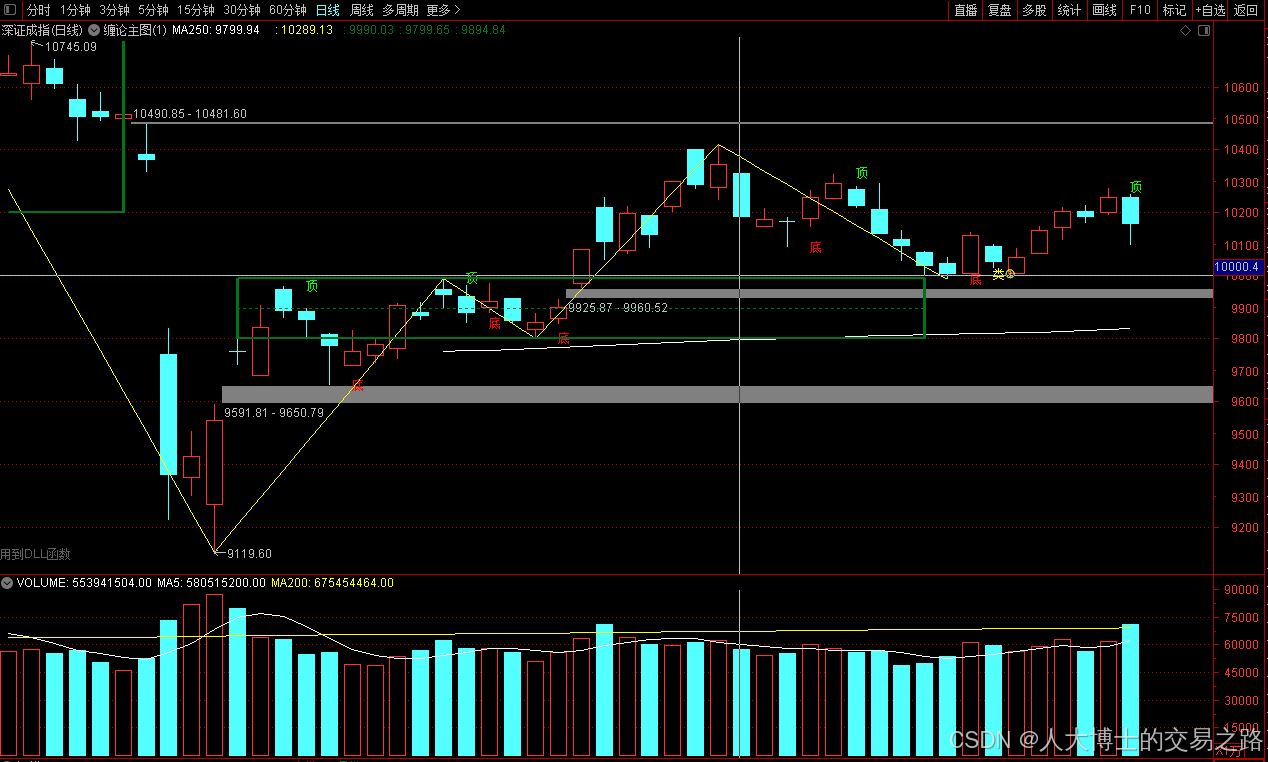
龙虎榜——20250610
上证指数放量收阴线,个股多数下跌,盘中受消息影响大幅波动。 深证指数放量收阴线形成顶分型,指数短线有调整的需求,大概需要一两天。 2025年6月10日龙虎榜行业方向分析 1. 金融科技
代表标的:御银股份、雄帝科技
驱动…
观成科技:隐蔽隧道工具Ligolo-ng加密流量分析
1.工具介绍
Ligolo-ng是一款由go编写的高效隧道工具,该工具基于TUN接口实现其功能,利用反向TCP/TLS连接建立一条隐蔽的通信信道,支持使用Let’s Encrypt自动生成证书。Ligolo-ng的通信隐蔽性体现在其支持多种连接方式,适应复杂网…
铭豹扩展坞 USB转网口 突然无法识别解决方法
当 USB 转网口扩展坞在一台笔记本上无法识别,但在其他电脑上正常工作时,问题通常出在笔记本自身或其与扩展坞的兼容性上。以下是系统化的定位思路和排查步骤,帮助你快速找到故障原因:
背景:
一个M-pard(铭豹)扩展坞的网卡突然无法识别了,扩展出来的三个USB接口正常。…
未来机器人的大脑:如何用神经网络模拟器实现更智能的决策?
编辑:陈萍萍的公主一点人工一点智能 未来机器人的大脑:如何用神经网络模拟器实现更智能的决策?RWM通过双自回归机制有效解决了复合误差、部分可观测性和随机动力学等关键挑战,在不依赖领域特定归纳偏见的条件下实现了卓越的预测准…
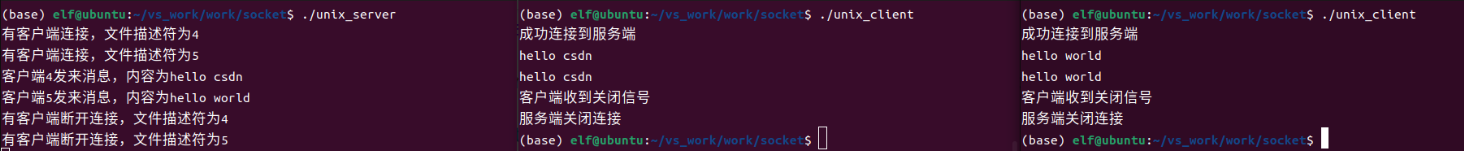
Linux应用开发之网络套接字编程(实例篇)
服务端与客户端单连接
服务端代码
#include <sys/socket.h>
#include <sys/types.h>
#include <netinet/in.h>
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <arpa/inet.h>
#include <pthread.h>
…
华为云AI开发平台ModelArts
华为云ModelArts:重塑AI开发流程的“智能引擎”与“创新加速器”!
在人工智能浪潮席卷全球的2025年,企业拥抱AI的意愿空前高涨,但技术门槛高、流程复杂、资源投入巨大的现实,却让许多创新构想止步于实验室。数据科学家…
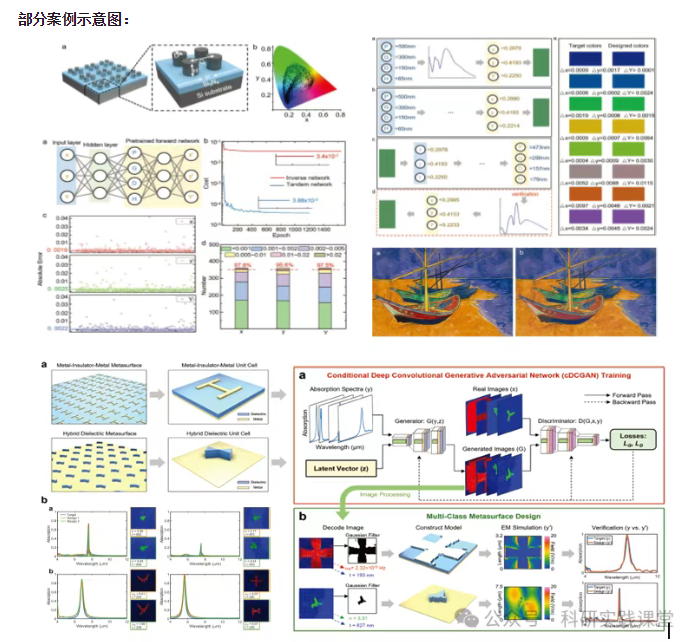
深度学习在微纳光子学中的应用
深度学习在微纳光子学中的主要应用方向
深度学习与微纳光子学的结合主要集中在以下几个方向:
逆向设计 通过神经网络快速预测微纳结构的光学响应,替代传统耗时的数值模拟方法。例如设计超表面、光子晶体等结构。
特征提取与优化 从复杂的光学数据中自…