VXLAN分布式网关跨VPC互通
news2026/3/20 16:45:40
ENSP模拟器拓扑图设备脚本Leaf1脚本Leaf1dis cu!Software Version V200R005C10SPC607B607!Last configuration was updated at 2026-03-19 21:04:1600:00!Last configuration was saved at 2026-03-19 22:14:3800:00#sysname Leaf1#device board 17 board-type CE-MPUBdevice board 1 board-type CE-LPUE#evpn-overlay enable#ip vpn-instance vpc1ipv4-familyroute-distinguisher 100:100vpn-target 5000:5000 export-extcommunityvpn-target 5000:5000 export-extcommunity evpnvpn-target 5000:5000 import-extcommunityvpn-target 5000:5000 import-extcommunity evpnvxlan vni 5000#bfd#bridge-domain 100vxlan vni 100evpnroute-distinguisher 100:100vpn-target 100:100 export-extcommunityvpn-target 5000:5000 export-extcommunityvpn-target 100:100 import-extcommunityvpn-target 5000:5000 import-extcommunity#bridge-domain 200vxlan vni 200evpnroute-distinguisher 100:200vpn-target 200:200 export-extcommunityvpn-target 5000:5000 export-extcommunityvpn-target 200:200 import-extcommunity#aaa#authentication-scheme default#authorization-scheme default#accounting-scheme default#domain default#domain default_admin#interface Vbdif100ip binding vpn-instance vpc1ip address 192.168.10.254 255.255.255.0arp broadcast-detect enablemac-address 0000-5e00-0020vxlan anycast-gateway enablearp collect host enable#interface Vbdif200ip binding vpn-instance vpc1ip address 192.168.20.254 255.255.255.0arp broadcast-detect enablemac-address 0000-5e00-0021vxlan anycast-gateway enablearp collect host enable#interface MEth0/0/0undo shutdown#interface GE1/0/0undo portswitchundo shutdownip address 192.168.0.2 255.255.255.252ospf network-type p2pospf enable 1 area 0.0.0.0#interface GE1/0/1undo shutdown#interface GE1/0/1.10 mode l2encapsulation dot1q vid 10bridge-domain 100#interface GE1/0/1.20 mode l2encapsulation dot1q vid 20bridge-domain 200#interface GE1/0/2shutdown#interface GE1/0/3shutdown#interface GE1/0/4shutdown#interface GE1/0/5shutdown#interface GE1/0/6shutdown#interface GE1/0/7shutdown#interface GE1/0/8shutdown#interface GE1/0/9shutdown#interface LoopBack0ip address 10.1.1.1 255.255.255.255ospf enable 1 area 0.0.0.0#interface LoopBack1ip address 192.168.10.1 255.255.255.255ospf enable 1 area 0.0.0.0#interface Nve1source 10.1.1.1vni 100 head-end peer-list protocol bgpvni 200 head-end peer-list protocol bgpvni 300 head-end peer-list protocol bgp#interface NULL0#bgp 100router-id 192.168.10.1peer 192.168.10.3 as-number 100peer 192.168.10.3 connect-interface LoopBack1#ipv4-family unicastpeer 192.168.10.3 enable#ipv4-family vpn-instance vpc1default-route importedimport-route directimport-route staticadvertise l2vpn evpn#l2vpn-family evpnpolicy vpn-targetpeer 192.168.10.3 enablepeer 192.168.10.3 advertise irb#ospf 1 router-id 192.168.10.1bfd all-interfaces enablebfd all-interfaces min-tx-interval 500 min-rx-interval 500lsa-arrival-interval intelligent-timer 50 50 50area 0.0.0.0#ssh authorization-type default aaa#ssh server cipher aes256_gcm aes128_gcm aes256_ctr aes192_ctr aes128_ctr aes256_cbc aes128_cbc 3des_cbc#ssh server dh-exchange min-len 1024#ssh client cipher aes256_gcm aes128_gcm aes256_ctr aes192_ctr aes128_ctr aes256_cbc aes128_cbc 3des_cbc#user-interface con 0#vm-manager#returnLeaf3脚本Leaf3dis cu!Software Version V200R005C10SPC607B607!Last configuration was updated at 2026-03-19 21:13:4900:00!Last configuration was saved at 2026-03-19 22:14:4100:00#sysname Leaf3#device board 17 board-type CE-MPUBdevice board 1 board-type CE-LPUE#evpn-overlay enable#ip vpn-instance vpc1ipv4-familyroute-distinguisher 200:100vpn-target 5000:5000 export-extcommunityvpn-target 5000:5000 export-extcommunity evpnvpn-target 5000:5000 import-extcommunityvpn-target 5000:5000 import-extcommunity evpnvxlan vni 5000#ip vpn-instance vpc2ipv4-familyroute-distinguisher 200:200vpn-target 5001:5001 export-extcommunityvpn-target 5001:5001 export-extcommunity evpnvpn-target 5001:5001 import-extcommunityvpn-target 5001:5001 import-extcommunity evpnvxlan vni 5001#bfd#bridge-domain 100vxlan vni 100evpnroute-distinguisher 200:100vpn-target 100:100 export-extcommunityvpn-target 5000:5000 export-extcommunityvpn-target 100:100 import-extcommunity#bridge-domain 200vxlan vni 200evpnroute-distinguisher 200:200vpn-target 200:200 export-extcommunityvpn-target 5000:5000 export-extcommunityvpn-target 200:200 import-extcommunity#bridge-domain 300vxlan vni 300evpnroute-distinguisher 200:300vpn-target 300:300 export-extcommunityvpn-target 5001:5001 export-extcommunityvpn-target 300:300 import-extcommunity#aaa#authentication-scheme default#authorization-scheme default#accounting-scheme default#domain default#domain default_admin#interface Vbdif100ip binding vpn-instance vpc1ip address 192.168.10.254 255.255.255.0arp broadcast-detect enablemac-address 0000-5e00-0020vxlan anycast-gateway enablearp collect host enable#interface Vbdif200ip binding vpn-instance vpc1ip address 192.168.20.254 255.255.255.0arp broadcast-detect enablemac-address 0000-5e00-0021vxlan anycast-gateway enablearp collect host enable#interface Vbdif300ip binding vpn-instance vpc2ip address 192.168.30.254 255.255.255.0arp broadcast-detect enablemac-address 0000-5e00-0022vxlan anycast-gateway enablearp collect host enable#interface MEth0/0/0undo shutdown#interface GE1/0/0undo portswitchundo shutdownip address 192.168.0.6 255.255.255.252ospf network-type p2pospf enable 1 area 0.0.0.0#interface GE1/0/1undo shutdown#interface GE1/0/1.10 mode l2encapsulation dot1q vid 10bridge-domain 100#interface GE1/0/1.20 mode l2encapsulation dot1q vid 20bridge-domain 200#interface GE1/0/1.30 mode l2encapsulation dot1q vid 30bridge-domain 300#interface GE1/0/2undo shutdown#interface GE1/0/3undo shutdown#interface GE1/0/4undo shutdown#interface GE1/0/5undo shutdown#interface GE1/0/6shutdown#interface GE1/0/7shutdown#interface GE1/0/8shutdown#interface GE1/0/9shutdown#interface LoopBack0ip address 10.2.2.2 255.255.255.255ospf enable 1 area 0.0.0.0#interface LoopBack1ip address 192.168.10.2 255.255.255.255ospf enable 1 area 0.0.0.0#interface Nve1source 10.2.2.2vni 100 head-end peer-list protocol bgpvni 200 head-end peer-list protocol bgpvni 300 head-end peer-list protocol bgp#interface NULL0#bgp 100router-id 192.168.10.2peer 192.168.10.3 as-number 100peer 192.168.10.3 connect-interface LoopBack1#ipv4-family unicastpeer 192.168.10.3 enable#ipv4-family vpn-instance vpc1default-route importedimport-route directimport-route staticadvertise l2vpn evpn#l2vpn-family evpnpolicy vpn-targetpeer 192.168.10.3 enablepeer 192.168.10.3 advertise irb#ospf 1 router-id 192.168.10.2bfd all-interfaces enablebfd all-interfaces min-tx-interval 500 min-rx-interval 500lsa-arrival-interval intelligent-timer 50 50 50area 0.0.0.0#ssh authorization-type default aaa#ssh server cipher aes256_gcm aes128_gcm aes256_ctr aes192_ctr aes128_ctr aes256_cbc aes128_cbc 3des_cbc#ssh server dh-exchange min-len 1024#ssh client cipher aes256_gcm aes128_gcm aes256_ctr aes192_ctr aes128_ctr aes256_cbc aes128_cbc 3des_cbc#user-interface con 0#vm-manager#returnLeaf3Spine1脚本Spine1dis cu!Software Version V200R005C10SPC607B607!Last configuration was updated at 2026-03-19 22:37:4100:00!Last configuration was saved at 2026-03-19 22:38:0000:00#sysname Spine1#device board 17 board-type CE-MPUBdevice board 1 board-type CE-LPUE#evpn-overlay enable#ip vpn-instance externalipv4-familyroute-distinguisher 300:300vpn-target 5002:5002 export-extcommunityvpn-target 5002:5002 export-extcommunity evpnvpn-target 5002:5002 import-extcommunityvpn-target 5002:5002 import-extcommunity evpnvxlan vni 5002#ip vpn-instance vpc1ipv4-familyroute-distinguisher 300:100vpn-target 5000:5000 export-extcommunityvpn-target 5000:5000 export-extcommunity evpnvpn-target 5000:5000 import-extcommunityvpn-target 5000:5000 import-extcommunity evpnvxlan vni 5000#ip vpn-instance vpc2ipv4-familyroute-distinguisher 300:200vpn-target 5001:5001 export-extcommunityvpn-target 5001:5001 export-extcommunity evpnvpn-target 5001:5001 import-extcommunityvpn-target 5001:5001 import-extcommunity evpnvxlan vni 5001#bfd#bridge-domain 400vxlan vni 400evpnroute-distinguisher 300:400vpn-target 400:400 export-extcommunityvpn-target 5000:5000 export-extcommunityvpn-target 400:400 import-extcommunity#bridge-domain 500vxlan vni 500evpnroute-distinguisher 300:500vpn-target 500:500 export-extcommunityvpn-target 5001:5001 export-extcommunityvpn-target 500:500 import-extcommunity#bridge-domain 600vxlan vni 600evpnroute-distinguisher 300:600vpn-target 600:600 export-extcommunityvpn-target 5002:5002 export-extcommunityvpn-target 600:600 import-extcommunity#bridge-domain 700vxlan vni 700evpnroute-distinguisher 300:700vpn-target 700:700 export-extcommunityvpn-target 5002:5002 export-extcommunityvpn-target 700:700 import-extcommunity#aaa#authentication-scheme default#authorization-scheme default#accounting-scheme default#domain default#domain default_admin#interface Vbdif400ip binding vpn-instance vpc1ip address 10.0.0.1 255.255.255.252arp broadcast-detect enablemac-address 0000-5e00-0023vxlan anycast-gateway enablearp collect host enable#interface Vbdif500ip binding vpn-instance vpc2ip address 10.0.1.1 255.255.255.252arp broadcast-detect enablemac-address 0000-5e00-0024vxlan anycast-gateway enablearp collect host enable#interface Vbdif600ip binding vpn-instance externalip address 10.0.2.1 255.255.255.252arp broadcast-detect enablemac-address 0000-5e00-0025vxlan anycast-gateway enablearp collect host enable#interface Vbdif700ip binding vpn-instance externalip address 112.43.3.146 255.255.255.252arp broadcast-detect enablemac-address 0000-5e00-0026vxlan anycast-gateway enablearp collect host enable#interface MEth0/0/0undo shutdown#interface GE1/0/0undo portswitchundo shutdownip address 192.168.0.1 255.255.255.252ospf network-type p2pospf enable 1 area 0.0.0.0#interface GE1/0/1undo portswitchundo shutdownip address 192.168.0.5 255.255.255.252ospf network-type p2pospf enable 1 area 0.0.0.0#interface GE1/0/2undo shutdown#interface GE1/0/2.1000 mode l2encapsulation dot1q vid 1000bridge-domain 400#interface GE1/0/2.1001 mode l2encapsulation dot1q vid 1001bridge-domain 500#interface GE1/0/2.1002 mode l2encapsulation dot1q vid 1002bridge-domain 600#interface GE1/0/3undo shutdown#interface GE1/0/3.1003 mode l2encapsulation dot1q vid 1003bridge-domain 700interface LoopBack0ip address 10.3.3.3 255.255.255.255ospf enable 1 area 0.0.0.0#interface LoopBack1ip address 192.168.10.3 255.255.255.255ospf enable 1 area 0.0.0.0#interface Nve1source 10.3.3.3vni 400 head-end peer-list protocol bgpvni 500 head-end peer-list protocol bgp#interface NULL0#bgp 100router-id 192.168.10.3peer 192.168.10.1 as-number 100peer 192.168.10.1 connect-interface LoopBack1peer 192.168.10.2 as-number 100peer 192.168.10.2 connect-interface LoopBack1#ipv4-family unicastpeer 192.168.10.1 enablepeer 192.168.10.2 enable#ipv4-family vpn-instance vpc1default-route importedimport-route directimport-route staticadvertise l2vpn evpn#ipv4-family vpn-instance vpc2default-route importedimport-route directimport-route staticadvertise l2vpn evpn#l2vpn-family evpnundo policy vpn-targetpeer 192.168.10.1 enablepeer 192.168.10.1 advertise irbpeer 192.168.10.1 reflect-clientpeer 192.168.10.2 enablepeer 192.168.10.2 advertise irbpeer 192.168.10.2 reflect-client#ospf 1 router-id 192.168.10.3bfd all-interfaces enablebfd all-interfaces min-tx-interval 500 min-rx-interval 500lsa-arrival-interval intelligent-timer 50 50 50area 0.0.0.0#ip route-static vpn-instance vpc1 0.0.0.0 0.0.0.0 10.0.0.2ip route-static vpn-instance vpc1 192.168.30.0 255.255.255.0 10.0.0.2ip route-static vpn-instance vpc2 0.0.0.0 0.0.0.0 10.0.1.2ip route-static vpn-instance vpc2 192.168.10.0 255.255.255.0 10.0.1.2ip route-static vpn-instance vpc2 192.168.20.0 255.255.255.0 10.0.1.2ip route-static vpn-instance external 0.0.0.0 0.0.0.0 112.43.3.145ip route-static vpn-instance external 192.168.10.0 255.255.255.0 10.0.2.2ip route-static vpn-instance external 192.168.20.0 255.255.255.0 10.0.2.2ip route-static vpn-instance external 192.168.30.0 255.255.255.0 10.0.2.2#ssh authorization-type default aaa#ssh server cipher aes256_gcm aes128_gcm aes256_ctr aes192_ctr aes128_ctr aes256_cbc aes128_cbc 3des_cbc#ssh server dh-exchange min-len 1024#ssh client cipher aes256_gcm aes128_gcm aes256_ctr aes192_ctr aes128_ctr aes256_cbc aes128_cbc 3des_cbc#user-interface con 0#vm-manager#returnFW防火墙脚本FW-Adis cu2026-03-19 15:19:57.780!Software Version V500R005C10SPC300#sysname FW-A#l2tp domain suffix-separator #vlan batch 1000 to 1002#ipsec sha2 compatible enable#undo telnet server enableundo telnet ipv6 server enable#update schedule location-sdb weekly Sun 23:24#firewall defend action discard#banner enable#user-manage web-authentication security port 8887undo privacy-statement englishundo privacy-statement chinesepage-settinguser-manage security version tlsv1.1 tlsv1.2password-policylevel highuser-manage single-sign-on aduser-manage single-sign-on tsmuser-manage single-sign-on radiususer-manage auto-sync online-user#web-manager security version tlsv1.1 tlsv1.2web-manager enableweb-manager security enable#firewall dataplane to manageplane application-apperceive default-action drop#undo ips log merge enable#decoding uri-cache disable#update schedule ips-sdb daily 03:45update schedule av-sdb daily 03:45update schedule sa-sdb daily 03:45update schedule cnc daily 03:45update schedule file-reputation daily 03:45#vsys enableresource-class r0##vsys name vpc1 1assign vlan 1000#vsys name vpc2 2assign vlan 1001#vsys name external 3assign vlan 1002#ip vpn-instance defaultipv4-family#ip vpn-instance externalipv4-familyipv6-family#ip vpn-instance vpc1ipv4-familyipv6-family#ip vpn-instance vpc2ipv4-familyipv6-family#time-range worktimeperiod-range 08:00:00 to 18:00:00 working-day#ike proposal defaultencryption-algorithm aes-256 aes-192 aes-128dh group14authentication-algorithm sha2-512 sha2-384 sha2-256authentication-method pre-shareintegrity-algorithm hmac-sha2-256prf hmac-sha2-256#aaaauthentication-scheme defaultauthentication-scheme admin_localauthentication-scheme admin_radius_localauthentication-scheme admin_hwtacacs_localauthentication-scheme admin_ad_localauthentication-scheme admin_ldap_localauthentication-scheme admin_radiusauthentication-scheme admin_hwtacacsauthentication-scheme admin_adauthorization-scheme defaultaccounting-scheme defaultdomain defaultservice-type internetaccess ssl-vpn l2tp ikeinternet-access mode passwordreference user current-domainmanager-user audit-adminpassword cipher %%#TDB%JK6Lzsa-e~7G9S/m/dnVKE(U,iEyf)]*nk;S/p9%%service-type web terminallevel 15manager-user api-adminpassword cipher %%I^{f!cfW%MXqMQvi3[(s)WjUcPNsv7.97pDTmYB)Zs%%level 15manager-user adminpassword cipher %%dF7d$HG6hl0!$ts(U57#5V)A\PBro6!ZdUA0ZkWQ7#85%%service-type web terminallevel 15role system-adminrole device-adminrole device-admin(monitor)role audit-adminbind manager-user audit-admin role audit-adminbind manager-user admin role system-admin#interface Vlanif1000ip binding vpn-instance vpc1ip address 10.0.0.2 255.255.255.252service-manage http permitservice-manage https permitservice-manage ping permitservice-manage ssh permitservice-manage telnet permit#interface Vlanif1001ip binding vpn-instance vpc2ip address 10.0.1.2 255.255.255.252service-manage http permitservice-manage https permitservice-manage ping permitservice-manage ssh permitservice-manage telnet permit#interface Vlanif1002ip binding vpn-instance externalip address 10.0.2.2 255.255.255.252service-manage http permitservice-manage https permitservice-manage ping permitservice-manage ssh permitservice-manage telnet permit#l2tp-group default-lns#interface GigabitEthernet0/0/0undo shutdownip binding vpn-instance defaultip address 192.168.0.1 255.255.255.0alias GE0/METH#interface GigabitEthernet1/0/0portswitchundo shutdownport link-type trunkport trunk allow-pass vlan 1000 to 1002#interface Virtual-if0#interface Virtual-if1ip address 20.0.0.1 255.255.255.0#interface Virtual-if2ip address 20.0.0.2 255.255.255.0#interface Virtual-if3ip address 20.0.0.3 255.255.255.0#interface NULL0#firewall zone localset priority 100#firewall zone trustset priority 85add interface GigabitEthernet0/0/0#firewall zone untrustset priority 5#firewall zone dmzset priority 50#ip route-static vpn-instance vpc1 0.0.0.0 0.0.0.0 vpn-instance externalip route-static vpn-instance vpc1 192.168.30.0 255.255.255.0 vpn-instance vpc2ip route-static vpn-instance vpc2 0.0.0.0 0.0.0.0 vpn-instance externalip route-static vpn-instance vpc2 192.168.10.0 255.255.255.0 vpn-instance vpc1ip route-static vpn-instance vpc2 192.168.20.0 255.255.255.0 vpn-instance vpc1ip route-static vpn-instance external 192.168.10.0 255.255.255.0 vpn-instance vpc1ip route-static vpn-instance external 192.168.20.0 255.255.255.0 vpn-instance vpc1ip route-static vpn-instance external 192.168.30.0 255.255.255.0 vpn-instance vpc2#undo ssh server compatible-ssh1x enablessh authentication-type default passwordssh server cipher aes256_ctr aes128_ctrssh server hmac sha2_256 sha1ssh client cipher aes256_ctr aes128_ctrssh client hmac sha2_256 sha1#firewall forward cross-vsys extended#firewall detect ftp#user-interface con 0authentication-mode aaauser-interface vty 0 4authentication-mode aaaprotocol inbound sshuser-interface vty 16 20#pki realm default#sa#location#multi-linkifmode proportion-of-weight#right-manager server-group#device-classificationdevice-group pcdevice-group mobile-terminaldevice-group undefined-group#user-manage server-sync tsm#security-policydefault action permit#auth-policy#traffic-policy#policy-based-route#nat-policy#quota-policy#pcp-policy#dns-transparent-policy#rightm-policy#return#防火墙FWA虚拟系统VPC1脚本switch vsys vpc1#l2tp domain suffix-separator #firewall defend action discard#page-settingpassword-policylevel high#time-range worktimeperiod-range 08:00:00 to 18:00:00 working-day#aaaauthentication-scheme defaultauthentication-scheme admin_localauthentication-scheme admin_radius_localauthentication-scheme admin_hwtacacs_localauthentication-scheme admin_ad_localauthentication-scheme admin_ldap_localauthentication-scheme admin_radiusauthentication-scheme admin_hwtacacsauthentication-scheme admin_adauthorization-scheme defaultaccounting-scheme defaultdomain defaultservice-type internetaccess ssl-vpn l2tp ikeinternet-access mode passwordreference user current-domainrole system-adminrole device-adminrole device-admin(monitor)role audit-admin#interface Vlanif1000ip binding vpn-instance vpc1ip address 10.0.0.2 255.255.255.252service-manage http permitservice-manage https permitservice-manage ping permitservice-manage ssh permitservice-manage telnet permit#l2tp-group default-lns#interface Virtual-if1ip address 20.0.0.1 255.255.255.0#sa#firewall zone localset priority 100#firewall zone trustset priority 85add interface Vlanif1000#firewall zone untrustset priority 5add interface Virtual-if1#firewall zone dmzset priority 50#location#multi-linkifmode proportion-of-weight#security-policyrule name 10.0toexternalsource-address 192.168.10.0 mask 255.255.255.0destination-address 50.50.50.50 mask 255.255.255.255action permitrule name 20.0-externalsource-address 192.168.20.0 mask 255.255.255.0destination-address 50.50.50.50 mask 255.255.255.255action permitrule name vpc1-vpc2source-address 192.168.10.0 mask 255.255.255.0source-address 192.168.20.0 mask 255.255.255.0destination-address 192.168.30.0 mask 255.255.255.0action permitrule name vpc2-vpc1source-address 192.168.30.0 mask 255.255.255.0destination-address 192.168.10.0 mask 255.255.255.0destination-address 192.168.20.0 mask 255.255.255.0action permit#auth-policy#traffic-policy#policy-based-route#nat-policy#quota-policy#pcp-policy#ip route-static 192.168.10.0 255.255.255.0 10.0.0.1ip route-static 192.168.20.0 255.255.255.0 10.0.0.1#return#防火墙FWA虚拟系统VPC2#switch vsys vpc2#l2tp domain suffix-separator #firewall defend action discard#page-settingpassword-policylevel high#time-range worktimeperiod-range 08:00:00 to 18:00:00 working-day#aaaauthentication-scheme defaultauthentication-scheme admin_localauthentication-scheme admin_radius_localauthentication-scheme admin_hwtacacs_localauthentication-scheme admin_ad_localauthentication-scheme admin_ldap_localauthentication-scheme admin_radiusauthentication-scheme admin_hwtacacsauthentication-scheme admin_adauthorization-scheme defaultaccounting-scheme defaultdomain defaultservice-type internetaccess ssl-vpn l2tp ikeinternet-access mode passwordreference user current-domainrole system-adminrole device-adminrole device-admin(monitor)role audit-admin#interface Vlanif1001ip binding vpn-instance vpc2ip address 10.0.1.2 255.255.255.252service-manage http permitservice-manage https permitservice-manage ping permitservice-manage ssh permitservice-manage telnet permit#l2tp-group default-lns#interface Virtual-if2ip address 20.0.0.2 255.255.255.0#sa#firewall zone localset priority 100#firewall zone trustset priority 85add interface Vlanif1001#firewall zone untrustset priority 5add interface Virtual-if2#firewall zone dmzset priority 50#location#multi-linkifmode proportion-of-weight#security-policyrule name vpc1-vpc2source-address 192.168.10.0 mask 255.255.255.0source-address 192.168.20.0 mask 255.255.255.0destination-address 192.168.30.0 mask 255.255.255.0action permitrule name vpc2-vpc1source-address 192.168.30.0 mask 255.255.255.0destination-address 192.168.10.0 mask 255.255.255.0destination-address 192.168.20.0 mask 255.255.255.0action permit#auth-policy#traffic-policy#policy-based-route#nat-policy#quota-policy#pcp-policy#ip route-static 192.168.30.0 255.255.255.0 10.0.1.1#return#防火墙FWA虚拟系统externalswitch vsys external#l2tp domain suffix-separator #firewall defend action discard#page-settingpassword-policylevel high#time-range worktimeperiod-range 08:00:00 to 18:00:00 working-day#aaaauthentication-scheme defaultauthentication-scheme admin_localauthentication-scheme admin_radius_localauthentication-scheme admin_hwtacacs_localauthentication-scheme admin_ad_localauthentication-scheme admin_ldap_localauthentication-scheme admin_radiusauthentication-scheme admin_hwtacacsauthentication-scheme admin_adauthorization-scheme defaultaccounting-scheme defaultdomain defaultservice-type internetaccess ssl-vpn l2tp ikeinternet-access mode passwordreference user current-domainrole system-adminrole device-adminrole device-admin(monitor)role audit-admin#interface Vlanif1002ip binding vpn-instance externalip address 10.0.2.2 255.255.255.252service-manage http permitservice-manage https permitservice-manage ping permitservice-manage ssh permitservice-manage telnet permit#l2tp-group default-lns#interface Virtual-if3ip address 20.0.0.3 255.255.255.0#sa#firewall zone localset priority 100#firewall zone trustset priority 85#firewall zone untrustset priority 5add interface Virtual-if3add interface Vlanif1002#firewall zone dmzset priority 50#location#multi-linkifmode proportion-of-weight#security-policyrule name 10.0toexternalsource-address 192.168.10.0 mask 255.255.255.0destination-address 50.50.50.50 mask 255.255.255.255action permitrule name 20.0-externalsource-address 192.168.20.0 mask 255.255.255.0destination-address 50.50.50.50 mask 255.255.255.255action permit#auth-policy#traffic-policy#policy-based-route#nat-policy#quota-policy#pcp-policy#ip route-static 0.0.0.0 0.0.0.0 10.0.2.1#return终端测试PC1到同VPC下PC2 192.168.10.1----192.168.20.1查看Leaf交换机的BGP EVPN 2类MAC路由查看Leaf交换机的arp学习情况PC1到不同VPC下PC3 192.168.10.1----192.168.30.1查看Leaf交换机的vrf vpc1路由表下一跳10.3.3.3走VXLAN隧道到Spine节点Spine节点通过配置的vrf vpc1 静态路由转发到防火墙vlan1000接口地址10.0.0.2FWA节点虚拟系统vpc1通过静态路由转发至FWA虚拟系统vpc2 Virtual-if2接口FWA节点虚拟系统vpc2通过配置的静态路由转发到Spine1节点的vpc2平面互联接口10.0.1.1FWA防火墙会话情况PC1至外部网络LSW1 192.168.10.1---50.50.50.50PC2至外部网络LSW1 192.168.20.1---50.50.50.50PC3由于在防火墙虚拟系统vpc2和external上配置了应用控制策略无法正常访问外部网络LSW1192.168.30.1---50.50.50.50外部网络LSW1由于在防火墙虚拟系统vpc1和external上配置了应用控制策略无法正常反向访问vpc1 vpc2 50.50.50.50----192.168.10.1 50.50.50.50----192.168.20.1
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。如若转载,请注明出处:http://www.coloradmin.cn/o/2430508.html
如若内容造成侵权/违法违规/事实不符,请联系多彩编程网进行投诉反馈,一经查实,立即删除!相关文章
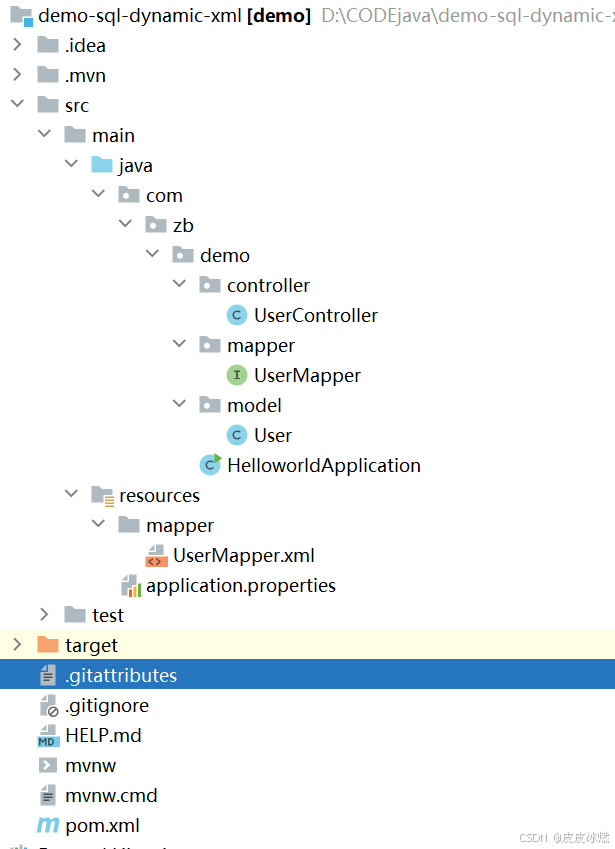
SpringBoot-17-MyBatis动态SQL标签之常用标签
文章目录 1 代码1.1 实体User.java1.2 接口UserMapper.java1.3 映射UserMapper.xml1.3.1 标签if1.3.2 标签if和where1.3.3 标签choose和when和otherwise1.4 UserController.java2 常用动态SQL标签2.1 标签set2.1.1 UserMapper.java2.1.2 UserMapper.xml2.1.3 UserController.ja…
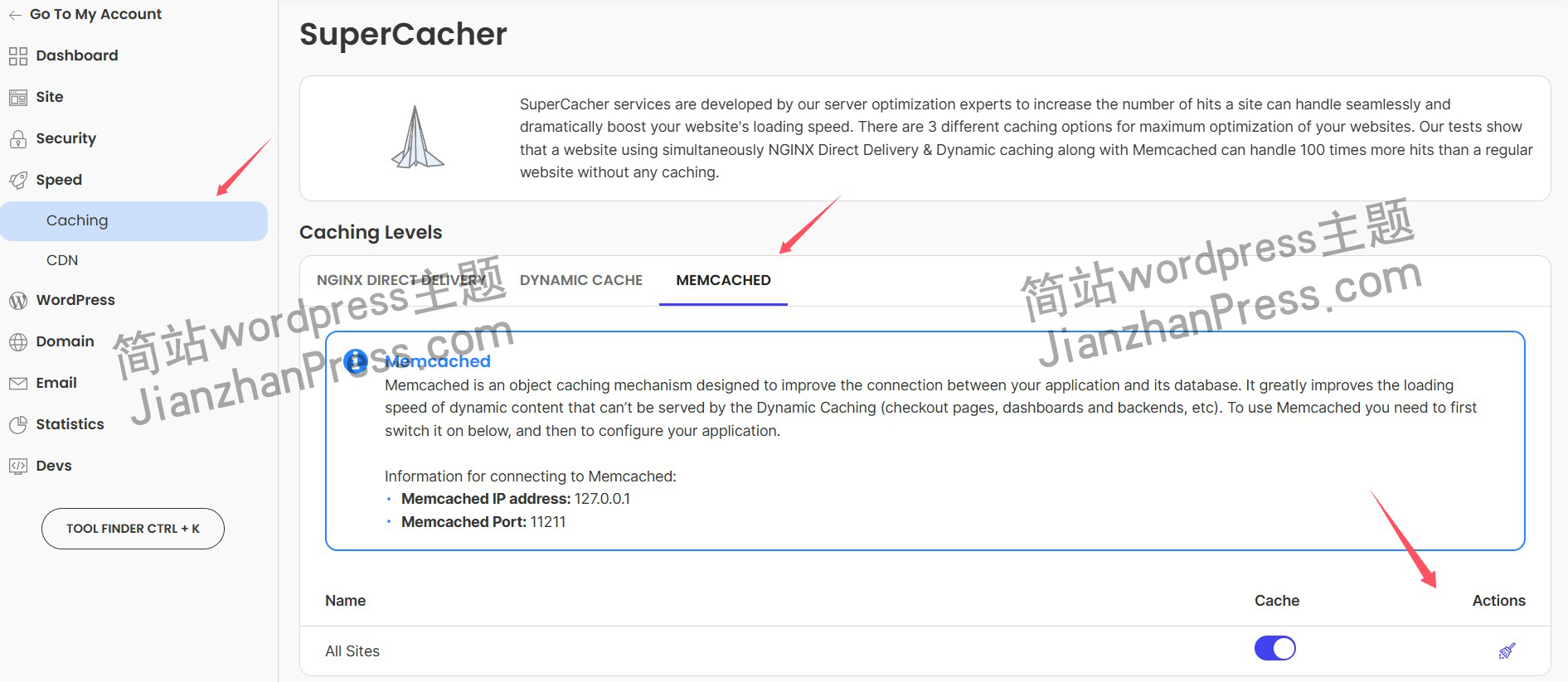
wordpress后台更新后 前端没变化的解决方法
使用siteground主机的wordpress网站,会出现更新了网站内容和修改了php模板文件、js文件、css文件、图片文件后,网站没有变化的情况。
不熟悉siteground主机的新手,遇到这个问题,就很抓狂,明明是哪都没操作错误&#x…
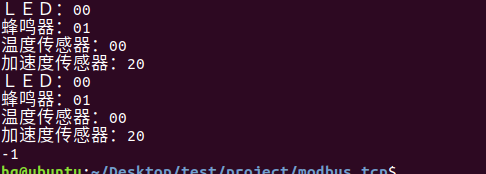
网络编程(Modbus进阶)
思维导图 Modbus RTU(先学一点理论)
概念 Modbus RTU 是工业自动化领域 最广泛应用的串行通信协议,由 Modicon 公司(现施耐德电气)于 1979 年推出。它以 高效率、强健性、易实现的特点成为工业控制系统的通信标准。 包…
UE5 学习系列(二)用户操作界面及介绍
这篇博客是 UE5 学习系列博客的第二篇,在第一篇的基础上展开这篇内容。博客参考的 B 站视频资料和第一篇的链接如下:
【Note】:如果你已经完成安装等操作,可以只执行第一篇博客中 2. 新建一个空白游戏项目 章节操作,重…
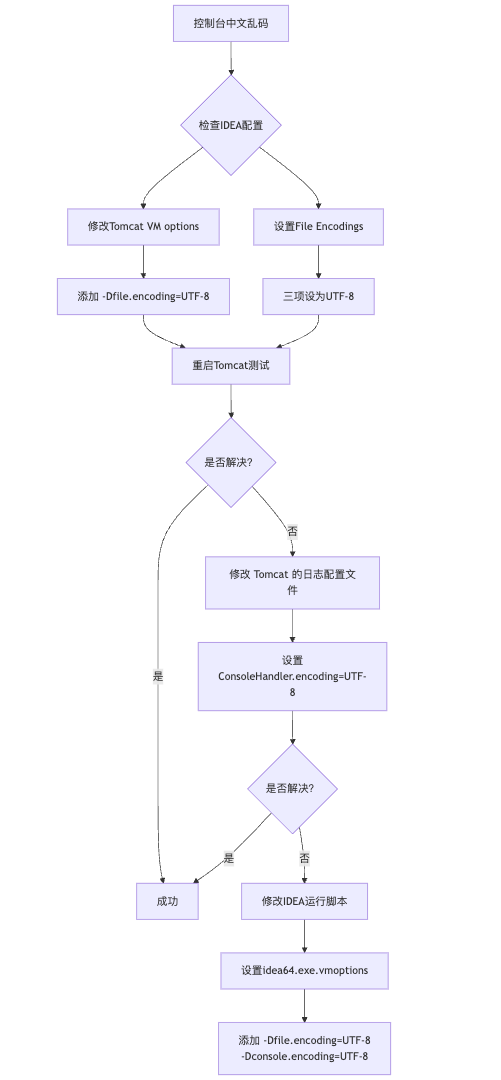
IDEA运行Tomcat出现乱码问题解决汇总
最近正值期末周,有很多同学在写期末Java web作业时,运行tomcat出现乱码问题,经过多次解决与研究,我做了如下整理:
原因:
IDEA本身编码与tomcat的编码与Windows编码不同导致,Windows 系统控制台…
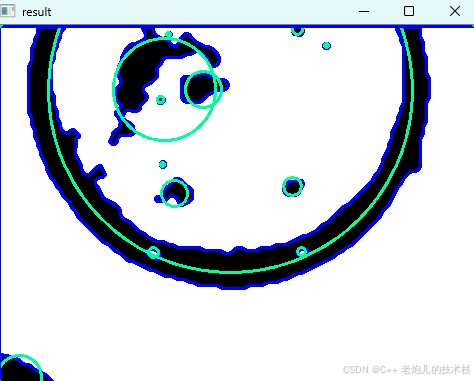
利用最小二乘法找圆心和半径
#include <iostream>
#include <vector>
#include <cmath>
#include <Eigen/Dense> // 需安装Eigen库用于矩阵运算 // 定义点结构
struct Point { double x, y; Point(double x_, double y_) : x(x_), y(y_) {}
}; // 最小二乘法求圆心和半径 …
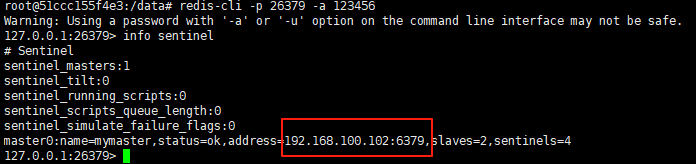
使用docker在3台服务器上搭建基于redis 6.x的一主两从三台均是哨兵模式
一、环境及版本说明
如果服务器已经安装了docker,则忽略此步骤,如果没有安装,则可以按照一下方式安装: 1. 在线安装(有互联网环境): 请看我这篇文章 传送阵>> 点我查看 2. 离线安装(内网环境):请看我这篇文章 传送阵>> 点我查看
说明:假设每台服务器已…
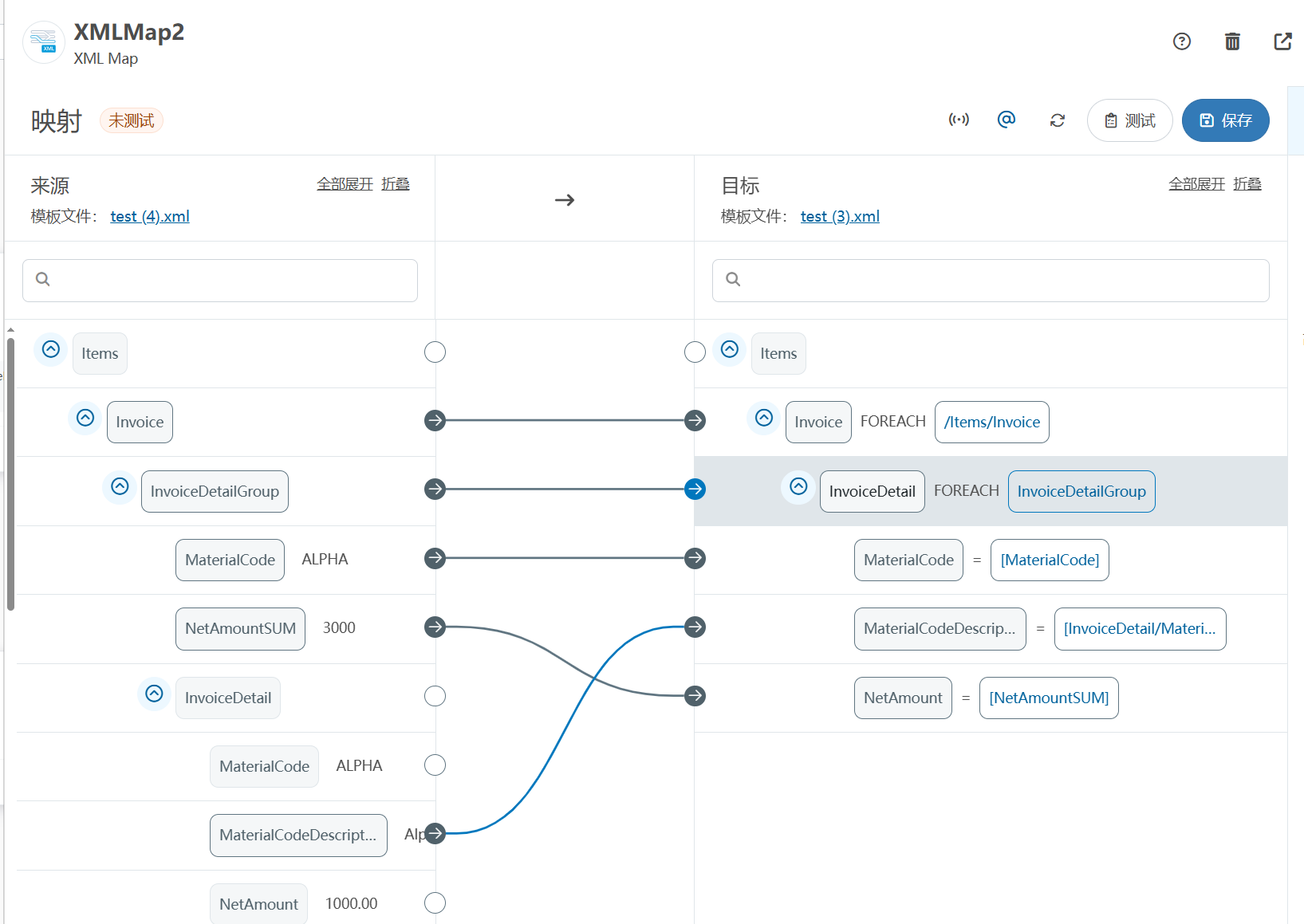
XML Group端口详解
在XML数据映射过程中,经常需要对数据进行分组聚合操作。例如,当处理包含多个物料明细的XML文件时,可能需要将相同物料号的明细归为一组,或对相同物料号的数量进行求和计算。传统实现方式通常需要编写脚本代码,增加了开…
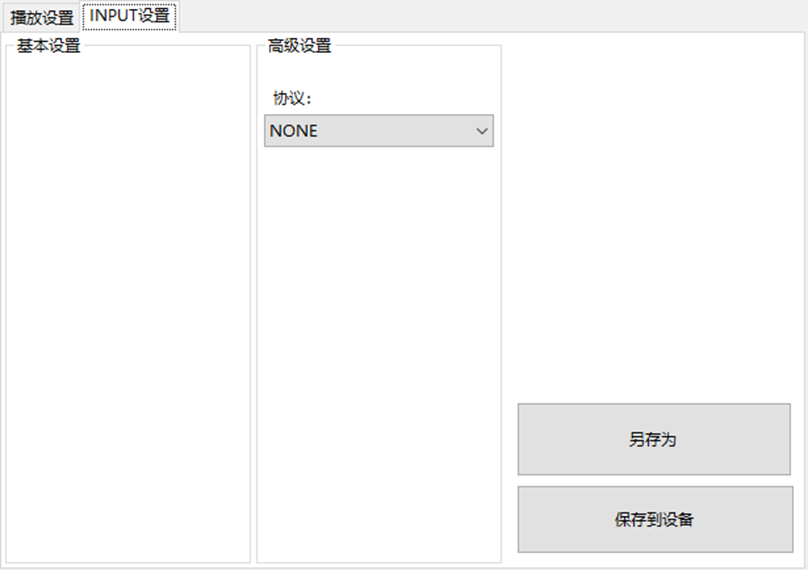
LBE-LEX系列工业语音播放器|预警播报器|喇叭蜂鸣器的上位机配置操作说明
LBE-LEX系列工业语音播放器|预警播报器|喇叭蜂鸣器专为工业环境精心打造,完美适配AGV和无人叉车。同时,集成以太网与语音合成技术,为各类高级系统(如MES、调度系统、库位管理、立库等)提供高效便捷的语音交互体验。
L…
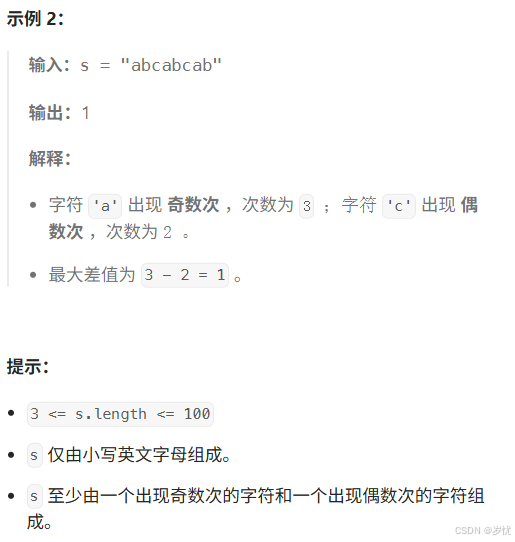
(LeetCode 每日一题) 3442. 奇偶频次间的最大差值 I (哈希、字符串)
题目:3442. 奇偶频次间的最大差值 I 思路 :哈希,时间复杂度0(n)。 用哈希表来记录每个字符串中字符的分布情况,哈希表这里用数组即可实现。
C版本:
class Solution {
public:int maxDifference(string s) {int a[26]…
【大模型RAG】拍照搜题技术架构速览:三层管道、两级检索、兜底大模型
摘要
拍照搜题系统采用“三层管道(多模态 OCR → 语义检索 → 答案渲染)、两级检索(倒排 BM25 向量 HNSW)并以大语言模型兜底”的整体框架: 多模态 OCR 层 将题目图片经过超分、去噪、倾斜校正后,分别用…
【Axure高保真原型】引导弹窗
今天和大家中分享引导弹窗的原型模板,载入页面后,会显示引导弹窗,适用于引导用户使用页面,点击完成后,会显示下一个引导弹窗,直至最后一个引导弹窗完成后进入首页。具体效果可以点击下方视频观看或打开下方…
接口测试中缓存处理策略
在接口测试中,缓存处理策略是一个关键环节,直接影响测试结果的准确性和可靠性。合理的缓存处理策略能够确保测试环境的一致性,避免因缓存数据导致的测试偏差。以下是接口测试中常见的缓存处理策略及其详细说明:
一、缓存处理的核…
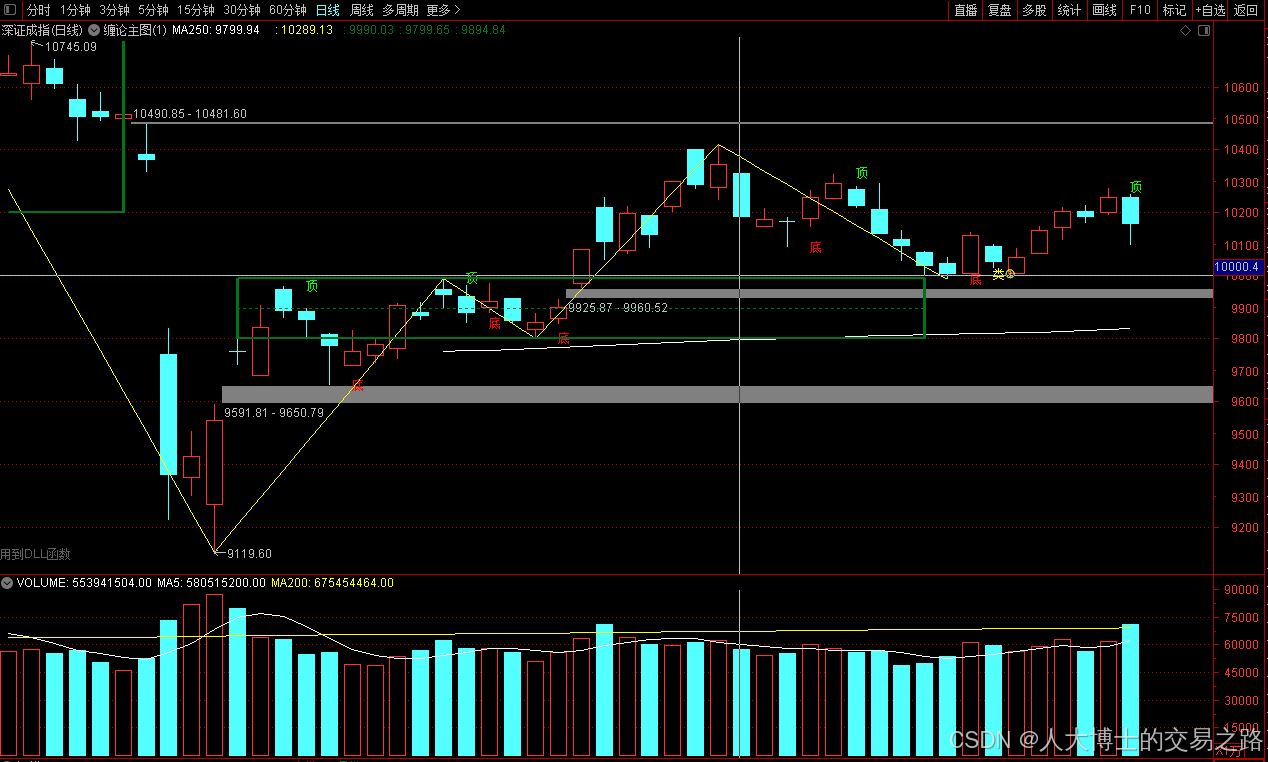
龙虎榜——20250610
上证指数放量收阴线,个股多数下跌,盘中受消息影响大幅波动。 深证指数放量收阴线形成顶分型,指数短线有调整的需求,大概需要一两天。 2025年6月10日龙虎榜行业方向分析 1. 金融科技
代表标的:御银股份、雄帝科技
驱动…
观成科技:隐蔽隧道工具Ligolo-ng加密流量分析
1.工具介绍
Ligolo-ng是一款由go编写的高效隧道工具,该工具基于TUN接口实现其功能,利用反向TCP/TLS连接建立一条隐蔽的通信信道,支持使用Let’s Encrypt自动生成证书。Ligolo-ng的通信隐蔽性体现在其支持多种连接方式,适应复杂网…
铭豹扩展坞 USB转网口 突然无法识别解决方法
当 USB 转网口扩展坞在一台笔记本上无法识别,但在其他电脑上正常工作时,问题通常出在笔记本自身或其与扩展坞的兼容性上。以下是系统化的定位思路和排查步骤,帮助你快速找到故障原因:
背景:
一个M-pard(铭豹)扩展坞的网卡突然无法识别了,扩展出来的三个USB接口正常。…
未来机器人的大脑:如何用神经网络模拟器实现更智能的决策?
编辑:陈萍萍的公主一点人工一点智能 未来机器人的大脑:如何用神经网络模拟器实现更智能的决策?RWM通过双自回归机制有效解决了复合误差、部分可观测性和随机动力学等关键挑战,在不依赖领域特定归纳偏见的条件下实现了卓越的预测准…
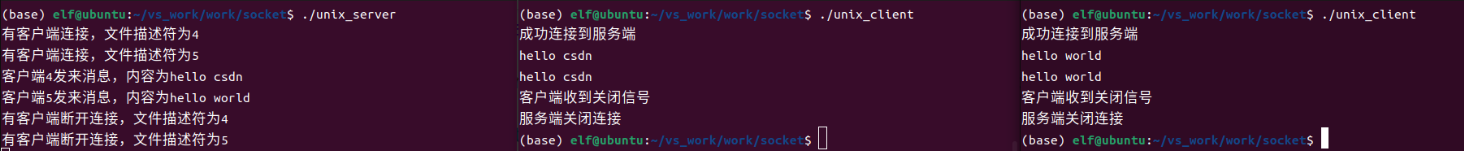
Linux应用开发之网络套接字编程(实例篇)
服务端与客户端单连接
服务端代码
#include <sys/socket.h>
#include <sys/types.h>
#include <netinet/in.h>
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <arpa/inet.h>
#include <pthread.h>
…
华为云AI开发平台ModelArts
华为云ModelArts:重塑AI开发流程的“智能引擎”与“创新加速器”!
在人工智能浪潮席卷全球的2025年,企业拥抱AI的意愿空前高涨,但技术门槛高、流程复杂、资源投入巨大的现实,却让许多创新构想止步于实验室。数据科学家…
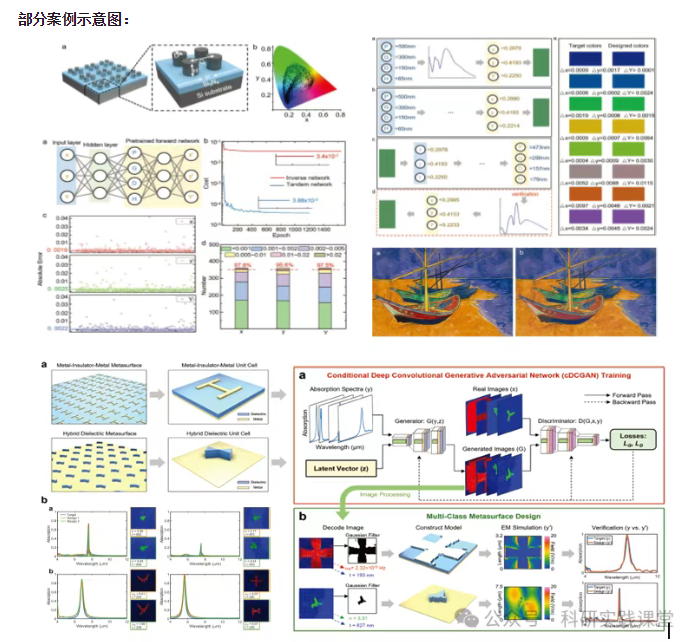
深度学习在微纳光子学中的应用
深度学习在微纳光子学中的主要应用方向
深度学习与微纳光子学的结合主要集中在以下几个方向:
逆向设计 通过神经网络快速预测微纳结构的光学响应,替代传统耗时的数值模拟方法。例如设计超表面、光子晶体等结构。
特征提取与优化 从复杂的光学数据中自…