微服务安全实战——Spring Authorization Server与OAuth2.1深度整合:从授权码模式到Gateway统一认证
news2026/3/20 5:12:02
1. Spring Authorization Server与OAuth2.1核心概念在微服务架构中身份认证和授权是保障系统安全的关键环节。Spring Authorization Server作为新一代认证授权框架完美支持OAuth2.1协议规范。与传统的Spring Security OAuth2相比它带来了更简洁的API设计和更强的安全性保障。OAuth2.1在OAuth2.0基础上做了重要改进移除了密码模式password和简化模式implicit这两种安全性较低的授权方式强制要求授权码模式必须使用PKCE扩展新增设备授权码模式Device Code用于物联网等特殊场景明确要求所有通信必须使用HTTPS协议典型授权码模式交互流程用户访问客户端应用点击登录按钮客户端将用户重定向到授权服务器的认证端点/oauth2/authorize用户在授权页面完成认证并同意授权授权服务器通过回调地址返回授权码code客户端使用授权码向令牌端点/oauth2/token请求访问令牌资源服务器验证令牌后返回受保护资源// 授权请求示例 http://auth-server:9000/oauth2/authorize? response_typecode client_idweb-client redirect_urihttps://client/callback scoperead_profile statexyz123 code_challengeK2-lX84oW4h... code_challenge_methodS2562. 认证服务器深度配置实战2.1 基础环境搭建首先需要准备以下环境JDK 17Spring Authorization Server要求Spring Boot 3.1.4Spring Authorization Server 1.1.2Maven核心依赖dependency groupIdorg.springframework.boot/groupId artifactIdspring-boot-starter-oauth2-authorization-server/artifactId /dependency dependency groupIdorg.springframework.boot/groupId artifactIdspring-boot-starter-security/artifactId /dependency2.2 安全配置详解认证服务器的核心配置类需要实现以下关键组件Configuration EnableWebSecurity public class AuthServerConfig { // 授权服务器过滤器链 Bean Order(1) public SecurityFilterChain authServerSecurityFilterChain(HttpSecurity http) throws Exception { OAuth2AuthorizationServerConfiguration.applyDefaultSecurity(http); http .exceptionHandling(exceptions - exceptions .authenticationEntryPoint(new LoginUrlAuthenticationEntryPoint(/login)) ) .oauth2ResourceServer(server - server.jwt(Customizer.withDefaults())); return http.build(); } // 默认安全过滤器链 Bean Order(2) public SecurityFilterChain defaultSecurityFilterChain(HttpSecurity http) throws Exception { http .authorizeHttpRequests(authorize - authorize .anyRequest().authenticated() ) .formLogin(Customizer.withDefaults()); return http.build(); } // 用户详情服务 Bean public UserDetailsService userDetailsService() { UserDetails user User.withUsername(admin) .password({bcrypt}$2a$10$...) .roles(ADMIN) .build(); return new InMemoryUserDetailsManager(user); } // 客户端注册仓库 Bean public RegisteredClientRepository registeredClientRepository() { RegisteredClient client RegisteredClient.withId(UUID.randomUUID().toString()) .clientId(web-client) .clientSecret({bcrypt}$2a$10$...) .clientAuthenticationMethod(ClientAuthenticationMethod.CLIENT_SECRET_BASIC) .authorizationGrantType(AuthorizationGrantType.AUTHORIZATION_CODE) .authorizationGrantType(AuthorizationGrantType.REFRESH_TOKEN) .redirectUri(https://client/callback) .scope(read_profile) .clientSettings(ClientSettings.builder() .requireAuthorizationConsent(true) .requireProofKey(true) // 强制PKCE .build()) .build(); return new InMemoryRegisteredClientRepository(client); } // JWT相关配置 Bean public JWKSourceSecurityContext jwkSource() { KeyPair keyPair generateRsaKey(); RSAPublicKey publicKey (RSAPublicKey) keyPair.getPublic(); RSAPrivateKey privateKey (RSAPrivateKey) keyPair.getPrivate(); RSAKey rsaKey new RSAKey.Builder(publicKey) .privateKey(privateKey) .keyID(UUID.randomUUID().toString()) .build(); JWKSet jwkSet new JWKSet(rsaKey); return new ImmutableJWKSet(jwkSet); } private static KeyPair generateRsaKey() { KeyPair keyPair; try { KeyPairGenerator keyPairGenerator KeyPairGenerator.getInstance(RSA); keyPairGenerator.initialize(2048); keyPair keyPairGenerator.generateKeyPair(); } catch (Exception ex) { throw new IllegalStateException(ex); } return keyPair; } }2.3 PKCE增强流程解析PKCEProof Key for Code Exchange是OAuth2.1对授权码模式的重要增强能有效防止授权码拦截攻击。其核心流程如下客户端生成随机字符串code_verifier43-128字符对code_verifier进行SHA256哈希得到code_challenge授权请求时携带code_challenge和methodS256令牌请求时携带原始code_verifier授权服务器验证code_verifier的哈希是否匹配// PKCE工具类示例 public class PkceUtil { public static String generateCodeVerifier() { SecureRandom secureRandom new SecureRandom(); byte[] codeVerifier new byte[32]; secureRandom.nextBytes(codeVerifier); return Base64.getUrlEncoder().withoutPadding().encodeToString(codeVerifier); } public static String generateCodeChallenge(String codeVerifier) throws NoSuchAlgorithmException { byte[] bytes codeVerifier.getBytes(StandardCharsets.US_ASCII); MessageDigest md MessageDigest.getInstance(SHA-256); md.update(bytes, 0, bytes.length); byte[] digest md.digest(); return Base64.getUrlEncoder().withoutPadding().encodeToString(digest); } }3. 网关统一认证集成方案3.1 Spring Cloud Gateway配置网关作为微服务入口需要承担令牌中继和路由转发职责# application.yml spring: cloud: gateway: routes: - id: resource-service uri: lb://resource-service predicates: - Path/api/** filters: - TokenRelay # 关键令牌中继过滤器 security: oauth2: client: provider: auth-server: issuer-uri: http://auth-server:9000 registration: gateway-client: provider: auth-server client-id: gateway-client client-secret: secret authorization-grant-type: authorization_code redirect-uri: {baseUrl}/login/oauth2/code/{registrationId} scope: openid,profile3.2 安全过滤器链配置网关需要同时处理两种安全场景对外的OAuth2客户端流程用户登录对内的JWT令牌验证服务间调用Configuration EnableWebFluxSecurity public class GatewaySecurityConfig { Bean public SecurityWebFilterChain securityWebFilterChain(ServerHttpSecurity http) { http .authorizeExchange(exchanges - exchanges .pathMatchers(/login/**, /assets/**).permitAll() .anyExchange().authenticated() ) .oauth2Login(Customizer.withDefaults()) .oauth2ResourceServer(server - server .jwt(jwt - jwt .jwkSetUri(http://auth-server:9000/oauth2/jwks) ) ); return http.build(); } }3.3 令牌中继实现原理TokenRelay过滤器的工作机制从当前请求提取访问令牌如果令牌即将过期自动使用刷新令牌获取新令牌将令牌添加到下游请求的Authorization头对于WebSocket等特殊协议需要自定义中继逻辑// 自定义令牌中继示例 public class CustomTokenRelayFilter implements GlobalFilter { private final ReactiveClientRegistrationRepository clientRegistrationRepository; private final ServerOAuth2AuthorizedClientRepository authorizedClientRepository; Override public MonoVoid filter(ServerWebExchange exchange, GatewayFilterChain chain) { return ReactiveSecurityContextHolder.getContext() .map(SecurityContext::getAuthentication) .flatMap(authentication - authorizedClientRepository.loadAuthorizedClient( gateway-client, authentication, exchange ) ) .map(OAuth2AuthorizedClient::getAccessToken) .flatMap(token - { exchange.getRequest() .mutate() .headers(headers - headers.setBearerAuth(token.getTokenValue())); return chain.filter(exchange); }); } }4. 资源服务器保护实战4.1 基础配置资源服务器需要验证JWT令牌并检查权限spring: security: oauth2: resourceserver: jwt: issuer-uri: http://auth-server:9000对应的安全配置类Configuration EnableWebSecurity EnableMethodSecurity public class ResourceServerConfig { Bean public SecurityFilterChain securityFilterChain(HttpSecurity http) throws Exception { http .authorizeHttpRequests(requests - requests .requestMatchers(/public/**).permitAll() .anyRequest().authenticated() ) .oauth2ResourceServer(server - server .jwt(jwt - jwt .decoder(jwtDecoder()) ) ); return http.build(); } Bean public JwtDecoder jwtDecoder() { return NimbusJwtDecoder.withJwkSetUri(http://auth-server:9000/oauth2/jwks).build(); } }4.2 权限控制策略三种常见的权限控制方式基于Scope的权限控制GetMapping(/profile) PreAuthorize(hasAuthority(SCOPE_profile)) public UserProfile getProfile() { // 实现逻辑 }基于角色的权限控制PostMapping(/users) PreAuthorize(hasRole(ADMIN)) public void createUser(RequestBody User user) { // 实现逻辑 }自定义权限逻辑public class PermissionEvaluatorImpl implements PermissionEvaluator { Override public boolean hasPermission( Authentication authentication, Object targetId, String permission ) { Jwt jwt (Jwt) authentication.getPrincipal(); // 自定义权限判断逻辑 return true; } }4.3 令牌自省与黑名单对于需要即时撤销令牌的场景可以实现令牌黑名单Service public class TokenBlacklistService { private final RedisTemplateString, Object redisTemplate; public void blacklistToken(String jti, Duration ttl) { redisTemplate.opsForValue().set( blacklist: jti, revoked, ttl ); } public boolean isTokenRevoked(String jti) { return redisTemplate.hasKey(blacklist: jti); } } Configuration public class JwtDecoderConfig { Bean public JwtDecoder jwtDecoder(TokenBlacklistService blacklistService) { NimbusJwtDecoder decoder NimbusJwtDecoder .withJwkSetUri(http://auth-server:9000/oauth2/jwks) .build(); decoder.setJwtValidator(new DelegatingOAuth2TokenValidator( new JwtTimestampValidator(), new JwtIssuerValidator(http://auth-server:9000), new JwtClaimValidatorString(jti, jti - !blacklistService.isTokenRevoked(jti) ) )); return decoder; } }5. 生产环境最佳实践5.1 性能优化方案令牌签名算法选择RS256推荐非对称加密私钥签名公钥验证HS256对称加密只适合内部服务间通信缓存策略Bean public JWKSourceSecurityContext jwkSource() { // 使用CachingJWKSource包装原始JWKSource JWKSourceSecurityContext original new ImmutableJWKSet(jwkSet); return new CachingJWKSource(original, 300, 3600); }数据库存储优化CREATE TABLE oauth2_authorized_client ( client_registration_id VARCHAR(100) NOT NULL, principal_name VARCHAR(200) NOT NULL, access_token_type VARCHAR(100) NOT NULL, access_token_value BYTEA NOT NULL, access_token_issued_at TIMESTAMP NOT NULL, access_token_expires_at TIMESTAMP NOT NULL, PRIMARY KEY (client_registration_id, principal_name) );5.2 高可用设计认证服务器集群部署要点共享JWKSource密钥集使用数据库存储客户端和授权信息配置Redis缓存令牌和授权码负载均衡器配置会话保持灾难恢复方案定期备份密钥对准备备用密钥用于紧急轮换实现密钥自动轮换机制5.3 监控与审计关键监控指标认证请求QPS令牌签发延迟异常授权尝试次数令牌撤销率审计日志配置Bean public AuditorAwareString auditorAware() { return () - Optional.ofNullable(SecurityContextHolder.getContext()) .map(SecurityContext::getAuthentication) .map(Authentication::getName); } Entity public class AuthAuditLog { Id private String id; private String clientId; private String userId; private String eventType; // LOGIN, LOGOUT, TOKEN_ISSUED private String ipAddress; private String userAgent; CreatedDate private Instant createdAt; }6. 常见问题排查指南6.1 授权码流程问题典型错误1invalid_grant - 授权码无效检查授权码是否过期默认5分钟确认重定向URI与注册配置完全一致验证PKCE的code_verifier是否正确典型错误2unauthorized_client - 客户端未授权检查客户端是否配置了authorization_code授权类型确认客户端密钥是否正确验证客户端认证方法basic/post6.2 令牌验证问题JWT签名无效确认资源服务器与认证服务器的时钟同步检查JWKSet端点是否可访问验证令牌中的iss声明是否匹配配置的issuer-uri令牌过期过早# 认证服务器配置 spring: security: oauth2: authorization-server: token: access-token-time-to-live: 1h refresh-token-time-to-live: 30d6.3 网关集成问题令牌未中继到下游服务确认Gateway添加了TokenRelay过滤器检查下游服务的Authorization头是否被覆盖验证WebClient是否配置了OAuth2过滤器CORS问题处理Bean public CorsWebFilter corsFilter() { CorsConfiguration config new CorsConfiguration(); config.addAllowedOrigin(*); config.addAllowedHeader(*); config.addAllowedMethod(*); UrlBasedCorsConfigurationSource source new UrlBasedCorsConfigurationSource(); source.registerCorsConfiguration(/**, config); return new CorsWebFilter(source); }7. 进阶功能扩展7.1 自定义授权模式实现自定义的OAuth2授权类型public class DeviceCodeAuthenticationProvider implements AuthenticationProvider { Override public Authentication authenticate(Authentication authentication) { DeviceCodeAuthenticationToken token (DeviceCodeAuthenticationToken) authentication; // 验证设备码逻辑 return new DeviceCodeAuthentication(token.getDeviceCode(), token.getPrincipal(), token.getAuthorities()); } Override public boolean supports(Class? authentication) { return DeviceCodeAuthenticationToken.class.isAssignableFrom(authentication); } } Configuration public class DeviceCodeConfig { Bean Order(Ordered.HIGHEST_PRECEDENCE) public SecurityFilterChain deviceCodeFilterChain(HttpSecurity http) throws Exception { http .securityMatcher(/device_authorize) .authorizeHttpRequests(authorize - authorize .anyRequest().authenticated() ) .oauth2ResourceServer(server - server .jwt(Customizer.withDefaults()) ); return http.build(); } }7.2 多因素认证集成在授权码流程中加入MFA验证Controller public class MfaController { GetMapping(/mfa/verify) public String mfaVerifyPage() { return mfa-verify; } PostMapping(/mfa/verify) public RedirectView verifyCode(RequestParam String code, HttpSession session) { if (validateMfaCode(code)) { session.setAttribute(mfaVerified, true); return new RedirectView(/oauth2/authorize? session.getAttribute(authorizationQuery)); } throw new BadCredentialsException(Invalid MFA code); } } Component public class MfaAuthenticationChecker implements AuthenticationChecker { Override public void check(Authentication authentication, AuthorizationGrantType grantType) { if (grantType AuthorizationGrantType.AUTHORIZATION_CODE !authentication.getDetails().getAttribute(mfaVerified)) { throw new OAuth2AuthenticationException(OAuth2ErrorCodes.ACCESS_DENIED); } } }7.3 联邦身份集成与第三方身份提供商如微信、企业微信集成Bean public ClientRegistrationRepository clientRegistrationRepository() { return new InMemoryClientRegistrationRepository( ClientRegistration.withRegistrationId(wechat) .clientId(wechat-appid) .clientSecret(wechat-secret) .authorizationGrantType(AuthorizationGrantType.AUTHORIZATION_CODE) .redirectUri({baseUrl}/login/oauth2/code/wechat) .scope(snsapi_login) .authorizationUri(https://open.weixin.qq.com/connect/qrconnect) .tokenUri(https://api.weixin.qq.com/sns/oauth2/access_token) .userInfoUri(https://api.weixin.qq.com/sns/userinfo) .userNameAttributeName(openid) .clientName(微信) .build() ); }
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。如若转载,请注明出处:http://www.coloradmin.cn/o/2428815.html
如若内容造成侵权/违法违规/事实不符,请联系多彩编程网进行投诉反馈,一经查实,立即删除!相关文章
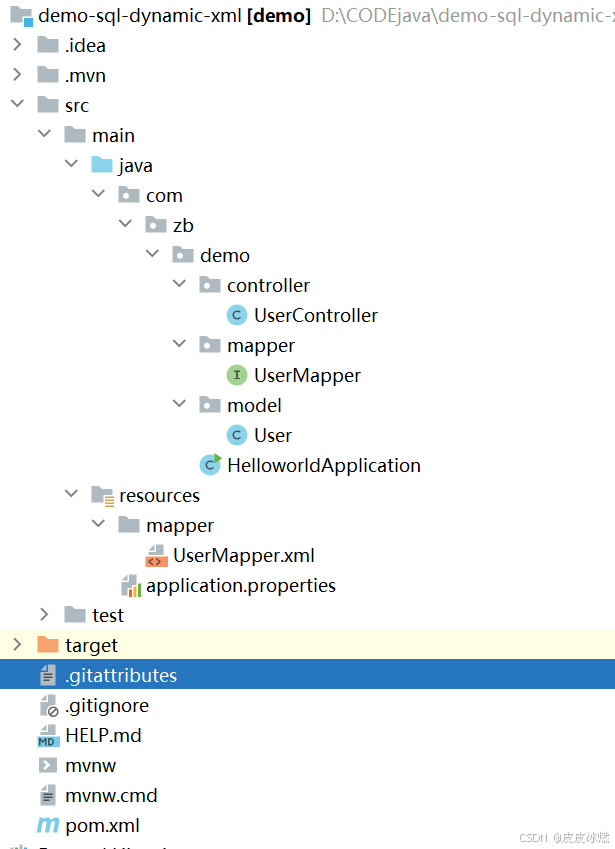
SpringBoot-17-MyBatis动态SQL标签之常用标签
文章目录 1 代码1.1 实体User.java1.2 接口UserMapper.java1.3 映射UserMapper.xml1.3.1 标签if1.3.2 标签if和where1.3.3 标签choose和when和otherwise1.4 UserController.java2 常用动态SQL标签2.1 标签set2.1.1 UserMapper.java2.1.2 UserMapper.xml2.1.3 UserController.ja…
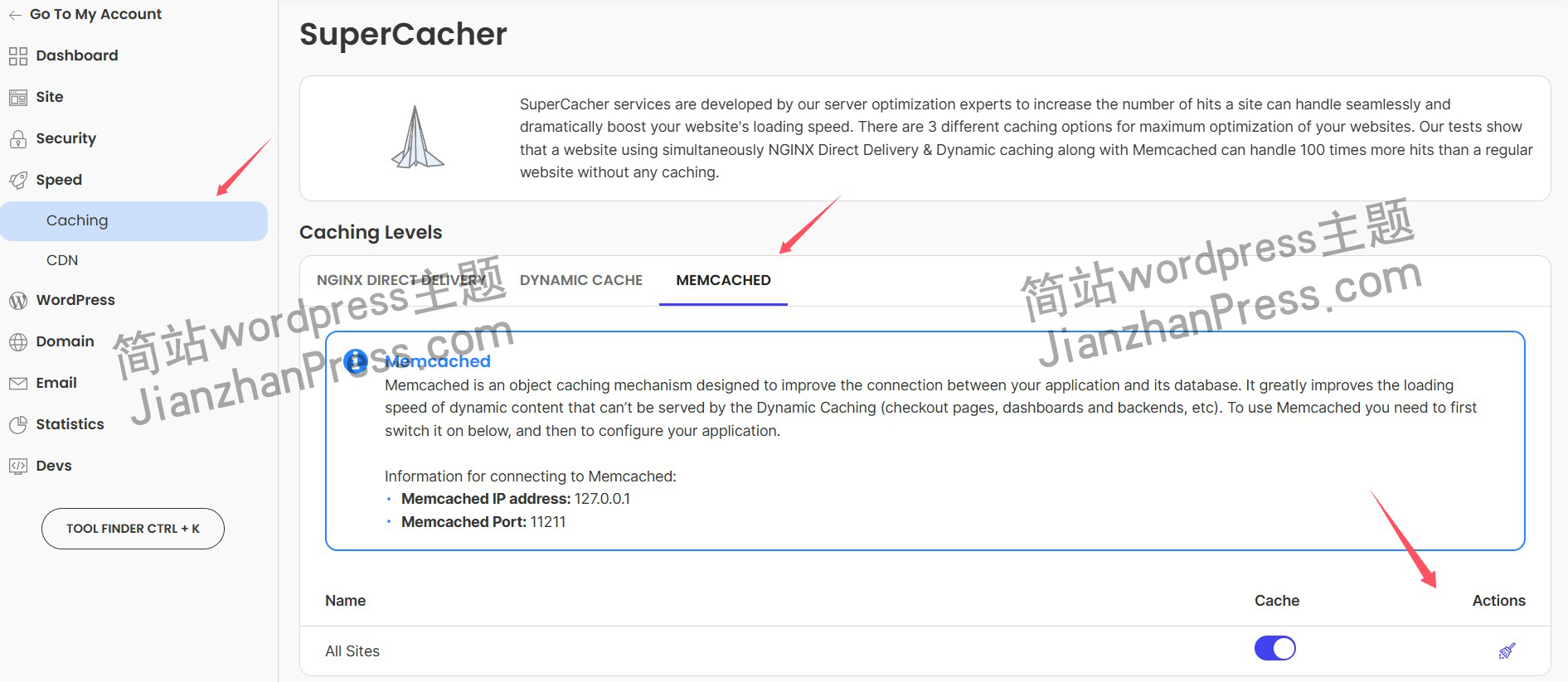
wordpress后台更新后 前端没变化的解决方法
使用siteground主机的wordpress网站,会出现更新了网站内容和修改了php模板文件、js文件、css文件、图片文件后,网站没有变化的情况。
不熟悉siteground主机的新手,遇到这个问题,就很抓狂,明明是哪都没操作错误&#x…
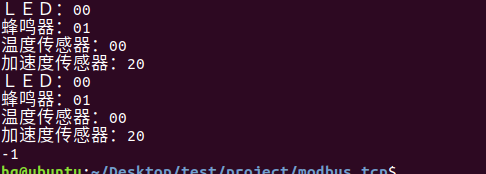
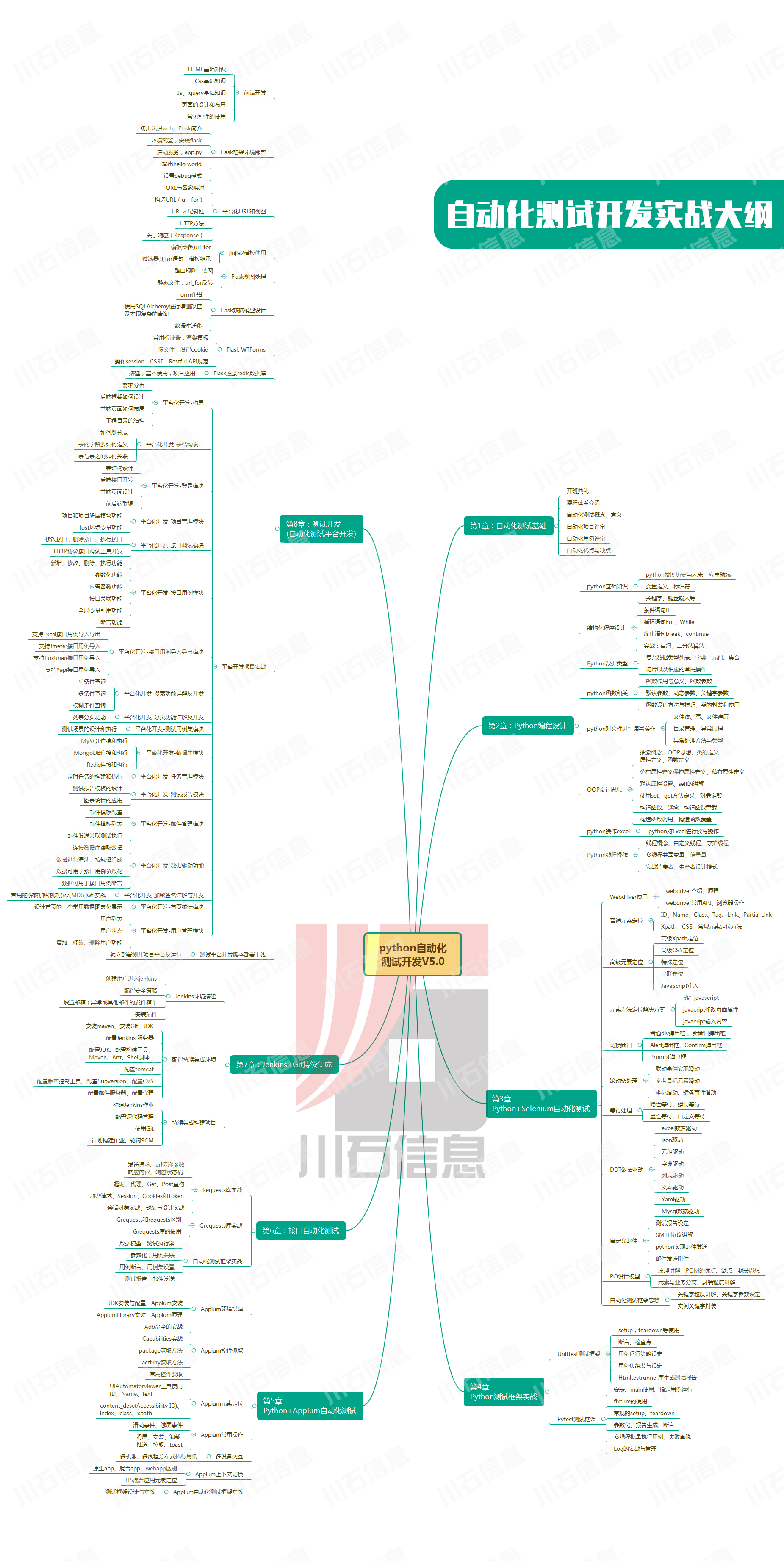
网络编程(Modbus进阶)
思维导图 Modbus RTU(先学一点理论)
概念 Modbus RTU 是工业自动化领域 最广泛应用的串行通信协议,由 Modicon 公司(现施耐德电气)于 1979 年推出。它以 高效率、强健性、易实现的特点成为工业控制系统的通信标准。 包…
UE5 学习系列(二)用户操作界面及介绍
这篇博客是 UE5 学习系列博客的第二篇,在第一篇的基础上展开这篇内容。博客参考的 B 站视频资料和第一篇的链接如下:
【Note】:如果你已经完成安装等操作,可以只执行第一篇博客中 2. 新建一个空白游戏项目 章节操作,重…
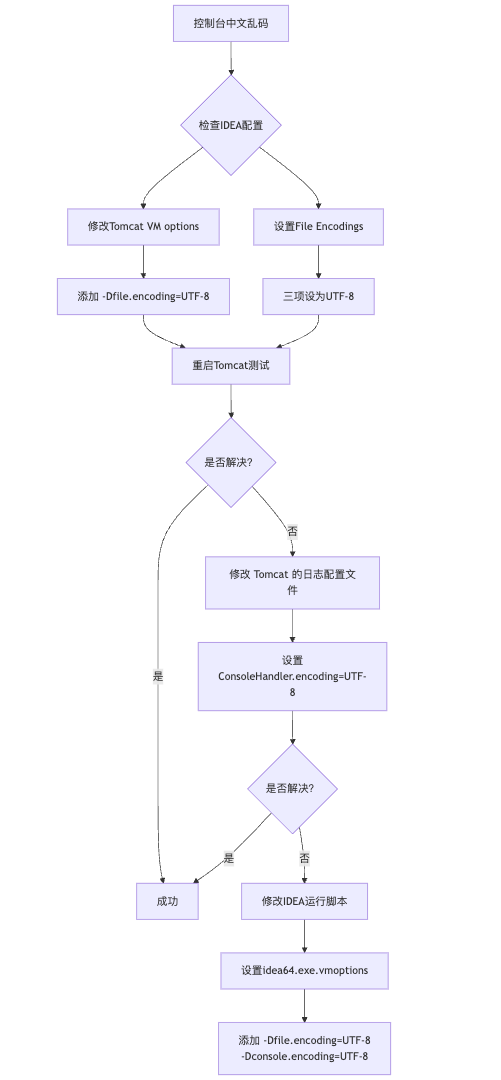
IDEA运行Tomcat出现乱码问题解决汇总
最近正值期末周,有很多同学在写期末Java web作业时,运行tomcat出现乱码问题,经过多次解决与研究,我做了如下整理:
原因:
IDEA本身编码与tomcat的编码与Windows编码不同导致,Windows 系统控制台…
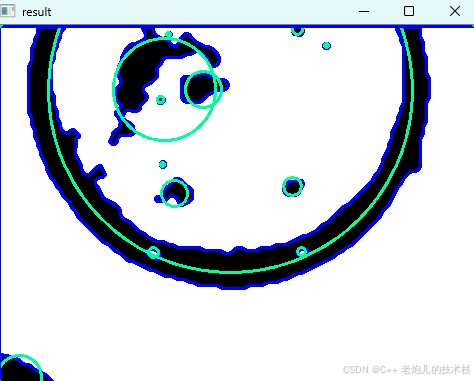
利用最小二乘法找圆心和半径
#include <iostream>
#include <vector>
#include <cmath>
#include <Eigen/Dense> // 需安装Eigen库用于矩阵运算 // 定义点结构
struct Point { double x, y; Point(double x_, double y_) : x(x_), y(y_) {}
}; // 最小二乘法求圆心和半径 …
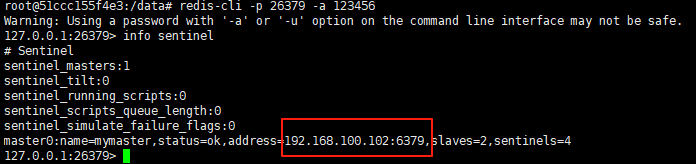
使用docker在3台服务器上搭建基于redis 6.x的一主两从三台均是哨兵模式
一、环境及版本说明
如果服务器已经安装了docker,则忽略此步骤,如果没有安装,则可以按照一下方式安装: 1. 在线安装(有互联网环境): 请看我这篇文章 传送阵>> 点我查看 2. 离线安装(内网环境):请看我这篇文章 传送阵>> 点我查看
说明:假设每台服务器已…
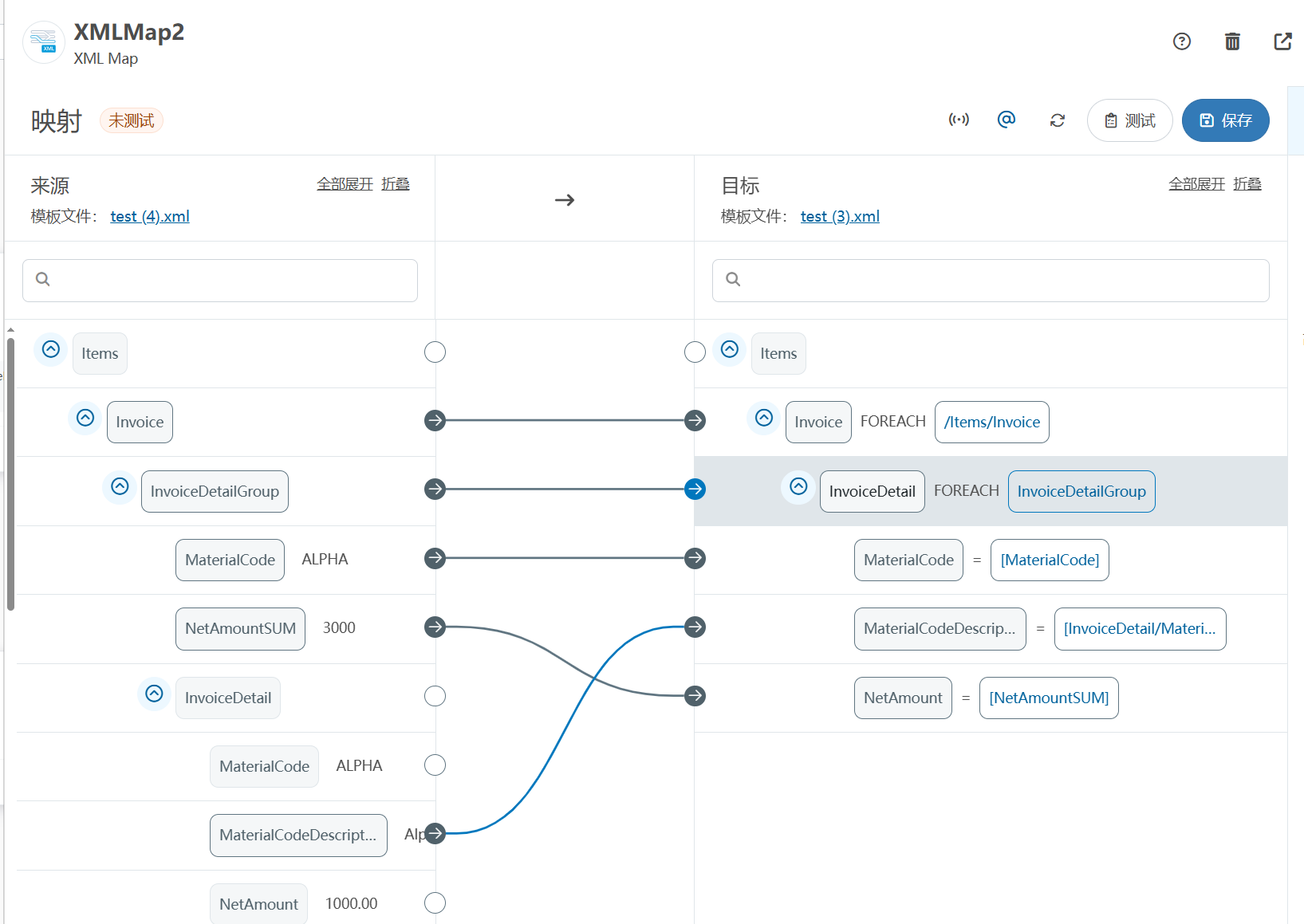
XML Group端口详解
在XML数据映射过程中,经常需要对数据进行分组聚合操作。例如,当处理包含多个物料明细的XML文件时,可能需要将相同物料号的明细归为一组,或对相同物料号的数量进行求和计算。传统实现方式通常需要编写脚本代码,增加了开…
LBE-LEX系列工业语音播放器|预警播报器|喇叭蜂鸣器的上位机配置操作说明
LBE-LEX系列工业语音播放器|预警播报器|喇叭蜂鸣器专为工业环境精心打造,完美适配AGV和无人叉车。同时,集成以太网与语音合成技术,为各类高级系统(如MES、调度系统、库位管理、立库等)提供高效便捷的语音交互体验。
L…
(LeetCode 每日一题) 3442. 奇偶频次间的最大差值 I (哈希、字符串)
题目:3442. 奇偶频次间的最大差值 I 思路 :哈希,时间复杂度0(n)。 用哈希表来记录每个字符串中字符的分布情况,哈希表这里用数组即可实现。
C版本:
class Solution {
public:int maxDifference(string s) {int a[26]…
【大模型RAG】拍照搜题技术架构速览:三层管道、两级检索、兜底大模型
摘要
拍照搜题系统采用“三层管道(多模态 OCR → 语义检索 → 答案渲染)、两级检索(倒排 BM25 向量 HNSW)并以大语言模型兜底”的整体框架: 多模态 OCR 层 将题目图片经过超分、去噪、倾斜校正后,分别用…
【Axure高保真原型】引导弹窗
今天和大家中分享引导弹窗的原型模板,载入页面后,会显示引导弹窗,适用于引导用户使用页面,点击完成后,会显示下一个引导弹窗,直至最后一个引导弹窗完成后进入首页。具体效果可以点击下方视频观看或打开下方…
接口测试中缓存处理策略
在接口测试中,缓存处理策略是一个关键环节,直接影响测试结果的准确性和可靠性。合理的缓存处理策略能够确保测试环境的一致性,避免因缓存数据导致的测试偏差。以下是接口测试中常见的缓存处理策略及其详细说明:
一、缓存处理的核…
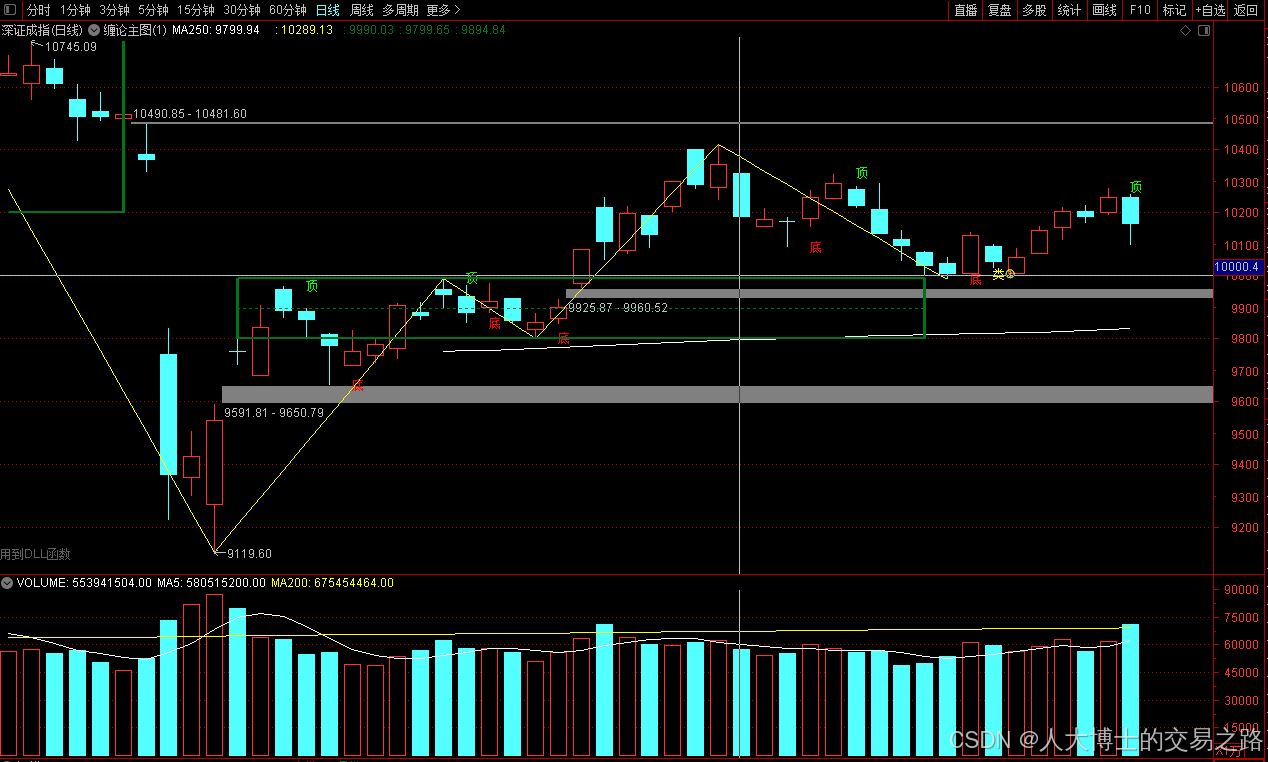
龙虎榜——20250610
上证指数放量收阴线,个股多数下跌,盘中受消息影响大幅波动。 深证指数放量收阴线形成顶分型,指数短线有调整的需求,大概需要一两天。 2025年6月10日龙虎榜行业方向分析 1. 金融科技
代表标的:御银股份、雄帝科技
驱动…
观成科技:隐蔽隧道工具Ligolo-ng加密流量分析
1.工具介绍
Ligolo-ng是一款由go编写的高效隧道工具,该工具基于TUN接口实现其功能,利用反向TCP/TLS连接建立一条隐蔽的通信信道,支持使用Let’s Encrypt自动生成证书。Ligolo-ng的通信隐蔽性体现在其支持多种连接方式,适应复杂网…
铭豹扩展坞 USB转网口 突然无法识别解决方法
当 USB 转网口扩展坞在一台笔记本上无法识别,但在其他电脑上正常工作时,问题通常出在笔记本自身或其与扩展坞的兼容性上。以下是系统化的定位思路和排查步骤,帮助你快速找到故障原因:
背景:
一个M-pard(铭豹)扩展坞的网卡突然无法识别了,扩展出来的三个USB接口正常。…
未来机器人的大脑:如何用神经网络模拟器实现更智能的决策?
编辑:陈萍萍的公主一点人工一点智能 未来机器人的大脑:如何用神经网络模拟器实现更智能的决策?RWM通过双自回归机制有效解决了复合误差、部分可观测性和随机动力学等关键挑战,在不依赖领域特定归纳偏见的条件下实现了卓越的预测准…
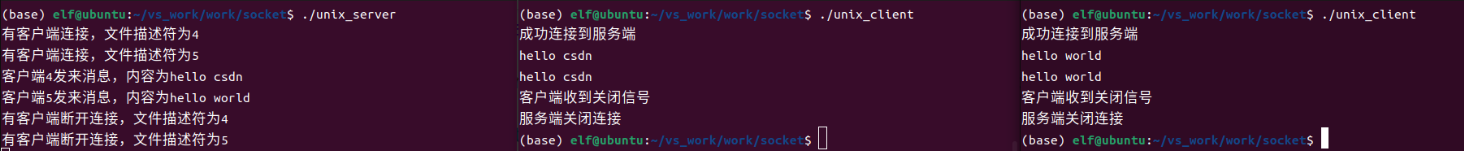
Linux应用开发之网络套接字编程(实例篇)
服务端与客户端单连接
服务端代码
#include <sys/socket.h>
#include <sys/types.h>
#include <netinet/in.h>
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <arpa/inet.h>
#include <pthread.h>
…
华为云AI开发平台ModelArts
华为云ModelArts:重塑AI开发流程的“智能引擎”与“创新加速器”!
在人工智能浪潮席卷全球的2025年,企业拥抱AI的意愿空前高涨,但技术门槛高、流程复杂、资源投入巨大的现实,却让许多创新构想止步于实验室。数据科学家…
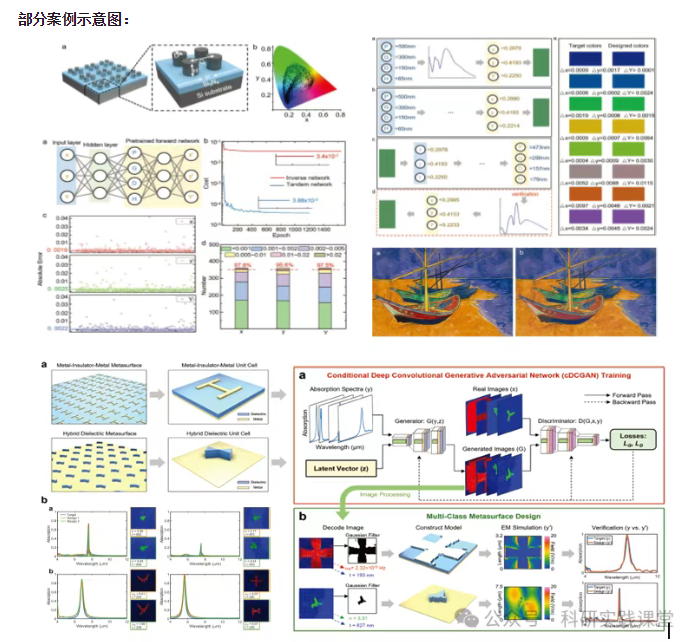
深度学习在微纳光子学中的应用
深度学习在微纳光子学中的主要应用方向
深度学习与微纳光子学的结合主要集中在以下几个方向:
逆向设计 通过神经网络快速预测微纳结构的光学响应,替代传统耗时的数值模拟方法。例如设计超表面、光子晶体等结构。
特征提取与优化 从复杂的光学数据中自…