OpenClaw 解决运行一些漏洞
news2026/3/18 8:58:42
1.发现问题运行 openclaw status 发现3个严重的安全威胁$ openclaw status OpenClaw2026.3.13(61d171a)— The only crabinyour contacts you actually want to hear from. 11:54:50[plugins]feishu_doc: Registered feishu_doc, feishu_app_scopes11:54:50[plugins]feishu_chat: Registered feishu_chat tool11:54:50[plugins]feishu_wiki: Registered feishu_wiki tool11:54:50[plugins]feishu_drive: Registered feishu_drive tool11:54:50[plugins]feishu_bitable: Registered bitable tools │11:54:50[plugins]feishu_doc: Registered feishu_doc, feishu_app_scopes11:54:50[plugins]feishu_chat: Registered feishu_chat tool11:54:50[plugins]feishu_wiki: Registered feishu_wiki tool11:54:50[plugins]feishu_drive: Registered feishu_drive tool11:54:50[plugins]feishu_bitable: Registered bitable tools ◇ │ ◇ OpenClaw status Overview ┌─────────────────┬───────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────┐ │ Item │ Value │ ├─────────────────┼───────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────┤ │ Dashboard │ http://127.0.0.1:18789/ │ │ OS │ linux6.8.0-71-generic(x64)·node24.14.0 │ │ Tailscale │ off │ │ Channel │ stable(default)│ │ Update │pnpm·npmlatest2026.3.13 │ │ Gateway │local· ws://127.0.0.1:18789(local loopback)· unreachable(missing scope: operator.read)│ │ Gatewayservice│ systemd installed · enabled · running(pid793469, state active)│ │ Nodeservice│ systemd not installed │ │ Agents │1·1bootstrapfilepresent · sessions2· default main active 14h ago │ │ Memory │0files ·0chunks · dirty · sources memory · plugin memory-core · vector unknown · fts ready · cache on(0)│ │ Probes │ skipped(use --deep)│ │ Events │ none │ │ Heartbeat │ 30m(main)│ │ Sessions │2active · default MiniMax-M2.5(200k ctx)· ~/.openclaw/agents/main/sessions/sessions.json │ └─────────────────┴───────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────┘ Security audit Summary:3critical ·4warn ·1info CRITICAL Open groupPolicy with elevated tools enabled FoundgroupPolicyopenat: - channels.feishu.groupPolicy With tools.elevated enabled, a prompt injectioninthose rooms can become a high-impact incident. Fix: SetgroupPolicyallowlistand keep elevated allowlists extremely tight. CRITICAL Open groupPolicy with runtime/filesystem tools exposed FoundgroupPolicyopenat: - channels.feishu.groupPolicy Risky tool exposure contexts: - agents.defaults(sandboxoff;runtime[exec, process];fs[read, wri… Fix: Foropengroups, prefertools.profilemessaging(or deny group:runtime/group:fs),settools.fs.workspaceOnlytrue, and useagents.defaults.sandbox.modeallforexposed agents. CRITICAL Feishu security warning Feishu[default]groups:groupPolicyopenallows any member to trigger(mention-gated). Setchannels.feishu.groupPolicyallowlist channels.feishu.groupAll… WARN Reverse proxy headers are not trusted gateway.bind is loopback and gateway.trustedProxies is empty. If you expose the Control UI through a reverse proxy, configure trusted proxies so local-client c… Fix: Set gateway.trustedProxies to your proxy IPs or keep the Control UI local-only. WARN Feishu doc create can grant requester permissions channels.feishu tools includedoc;feishu_doc actioncreatecan grant document access to the trusted requesting Feishu user. Fix: Disable channels.feishu.tools.doc when not needed, and restrict tool accessforuntrusted prompts. WARN Some gateway.nodes.denyCommands entries are ineffective gateway.nodes.denyCommands uses exactnodecommand-name matching only(for examplesystem.run), not shell-text filtering inside acommandpayload. - Unknown … Fix: Use exactcommandnames(for example: canvas.present, canvas.hide, canvas.navigate, canvas.eval, canvas.snapshot, canvas.a2ui.push, canvas.a2ui.pushJSONL, canvas.a2ui.reset). If you need broader restrictions, remove riskycommandIDs from allowCommands/default workflows and tighten tools.exec policy. … 1moreFull report: openclaw security audit Deep probe: openclaw security audit--deepChannels ┌──────────┬─────────┬────────┬───────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────┐ │ Channel │ Enabled │ State │ Detail │ ├──────────┼─────────┼────────┼───────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────┤ │ Feishu │ ON │ OK │ configured │ └──────────┴─────────┴────────┴───────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────┘ Sessions ┌──────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────┬────────┬─────────┬──────────────┬────────────────────────────────┐ │ Key │ Kind │ Age │ Model │ Tokens │ ├──────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────┼────────┼─────────┼──────────────┼────────────────────────────────┤ │ agent:main:feishu:group:oc_fbe0… │ group │ 14h ago │ MiniMax-M2.5 │ 23k/200k(11%)· ️97% cached │ │ agent:main:feishu:direct:ou_d9b… │ direct │ 14h ago │ MiniMax-M2.5 │ 13k/200k(6%)· ️25% cached │ └──────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────┴────────┴─────────┴──────────────┴────────────────────────────────┘ FAQ: https://docs.openclaw.ai/faq Troubleshooting: https://docs.openclaw.ai/troubleshooting Next steps: Need to share? openclaw status--allNeed to debug live? openclaw logs--followFix reachability first: openclaw gateway probe查看详细的问题原因$ openclaw security audit--deep OpenClaw2026.3.13(61d171a)Im the assistant your terminal demanded, not the one your sleep schedule requested. 13:48:37 [plugins] feishu_doc: Registered feishu_doc, feishu_app_scopes 13:48:37 [plugins] feishu_chat: Registered feishu_chat tool 13:48:37 [plugins] feishu_wiki: Registered feishu_wiki tool 13:48:37 [plugins] feishu_drive: Registered feishu_drive tool 13:48:37 [plugins] feishu_bitable: Registered bitable tools OpenClaw security audit Summary: 3 critical · 5 warn · 1 info Run deeper: openclaw security audit --deep CRITICAL security.exposure.open_groups_with_elevated Open groupPolicy with elevated tools enabled Found groupPolicyopen at: - channels.feishu.groupPolicy With tools.elevated enabled, a prompt injection in those rooms can become a high-impact incident. Fix: Set groupPolicyallowlist and keep elevated allowlists extremely tight. security.exposure.open_groups_with_runtime_or_fs Open groupPolicy with runtime/filesystem tools exposed Found groupPolicyopen at: - channels.feishu.groupPolicy Risky tool exposure contexts: - agents.defaults (sandboxoff; runtime[exec, process]; fs[read, write, edit, apply_patch]; fs.workspaceOnlyfalse) Prompt injection in open groups can trigger command/file actions in these contexts. Fix: For open groups, prefer tools.profilemessaging (or deny group:runtime/group:fs), set tools.fs.workspaceOnlytrue, and use agents.defaults.sandbox.modeall for exposed agents. channels.feishu.warning.1 Feishu security warning Feishu[default] groups: groupPolicyopen allows any member to trigger (mention-gated). Set channels.feishu.groupPolicyallowlist channels.feishu.groupAllowFrom to restrict senders. WARN gateway.trusted_proxies_missing Reverse proxy headers are not trusted gateway.bind is loopback and gateway.trustedProxies is empty. If you expose the Control UI through a reverse proxy, configure trusted proxies so local-client checks cannot be spoofed. Fix: Set gateway.trustedProxies to your proxy IPs or keep the Control UI local-only. channels.feishu.doc_owner_open_id Feishu doc create can grant requester permissions channels.feishu tools include doc; feishu_doc action create can grant document access to the trusted requesting Feishu user. Fix: Disable channels.feishu.tools.doc when not needed, and restrict tool access for untrusted prompts. gateway.nodes.deny_commands_ineffective Some gateway.nodes.denyCommands entries are ineffective gateway.nodes.denyCommands uses exact node command-name matching only (for example system.run), not shell-text filtering inside a command payload. - Unknown command names (not in defaults/allowCommands): camera.snap (did you mean: camera.list), camera.clip (did you mean: camera.list), screen.record, contacts.add, calendar.add, reminders.add (did you mean: reminders.list), sms.send Fix: Use exact command names (for example: canvas.present, canvas.hide, canvas.navigate, canvas.eval, canvas.snapshot, canvas.a2ui.push, canvas.a2ui.pushJSONL, canvas.a2ui.reset). If you need broader restrictions, remove risky command IDs from allowCommands/default workflows and tighten tools.exec policy. security.trust_model.multi_user_heuristic Potential multi-user setup detected (personal-assistant model warning) Heuristic signals indicate this gateway may be reachable by multiple users: - channels.feishu.groupPolicyopen Runtime/process tools are exposed without full sandboxing in at least one context. Potential high-impact tool exposure contexts: - agents.defaults (sandboxoff; runtime[exec, process]; fs[read, write, edit, apply_patch]; fs.workspaceOnlyfalse) OpenClaws default security model is personal-assistant(one trusted operator boundary), not hostile multi-tenant isolation on one shared gateway. Fix: Ifusersmay be mutually untrusted,splittrust boundaries(separate gateways credentials, ideally separate OS users/hosts). If you intentionally run shared-user access,setagents.defaults.sandbox.modeall, keeptools.fs.workspaceOnlytrue, deny runtime/fs/web tools unless required, and keep personal/private identities credentials off that runtime. gateway.probe_failed Gateway probe failed(deep)missing scope: operator.read Fix: Runopenclaw status --allto debug connectivity/auth,thenre-runopenclaw security audit --deep.INFO summary.attack_surface Attack surface summary groups:open1,allowlist0tools.elevated: enabled hooks.webhooks: disabled hooks.internal: enabled browser control: enabled trust model: personal assistant(one trusted operator boundary), not hostile multi-tenant on one shared gateway2. 查看原因查看飞书群组策略$ openclaw config get channels.feishu.groupPolicy OpenClaw2026.3.13(61d171a)— I run on caffeine, JSON5, and the audacity ofit worked on my machine.open13:56:51[plugins]feishu_doc: Registered feishu_doc, feishu_app_scopes13:56:51[plugins]feishu_chat: Registered feishu_chat tool13:56:51[plugins]feishu_wiki: Registered feishu_wiki tool13:56:51[plugins]feishu_drive: Registered feishu_drive tool13:56:51[plugins]feishu_bitable: Registered bitable tools2.1 CRITICAL: 开放群组策略 高危工具启用2.1.1 问题本质飞书群组策略设为 open同时启用了 tools.elevated特权工具2.1.2 攻击场景攻击者 → 加入公开飞书群 → OpenClaw 机器人→ 注入恶意提示词 → 调用高危工具如 exec/sandbox-off→ 完全控制服务器2.1.3 修改# openclaw.yamlchannels:feishu:groupPolicy:allowlist# 改为白名单制groupAllowFrom:-oc_your-trusted-group-id-1-oc_your-trusted-group-id-2tools:elevated:false也可以用命令修改设置飞书群组策略为白名单制$ openclaw configsetchannels.feishu.groupPolicyallowlist添加 groupAllowFrom 白名单打开飞书 App 进入群点击下图的右上方的…打开设置其中群组ID为下图中的会话ID$ openclaw configsetchannels.feishu.groupAllowFrom[oc_fbe0e81468794e8bf2d13635f70c2138] OpenClaw 2026.3.13(61d171a)— Powered by open source,sustained by spite and good documentation.│ ◇ Doctor warnings ──────────────────────────────────────────────────────────────────────────╮ │ │ │-channels.feishu.groupPolicy isallowlistbut groupAllowFrom(and allowFrom)is empty │ │ — allgroupmessages will be silently dropped.Add sender IDs to │ │ channels.feishu.groupAllowFrom or channels.feishu.allowFrom,orsetgroupPolicy to │ │open.│ │ │ ├────────────────────────────────────────────────────────────────────────────────────────────╯ 15:33:05[plugins]feishu_doc: Registered feishu_doc,feishu_app_scopes 15:33:05[plugins]feishu_chat: Registered feishu_chat tool 15:33:05[plugins]feishu_wiki: Registered feishu_wiki tool 15:33:05[plugins]feishu_drive: Registered feishu_drive tool 15:33:05[plugins]feishu_bitable: Registered bitable tools Config overwrite:/home/ubuntu/.openclaw/openclaw.json(sha256 3d5921137dc1d249dd8d393ee7300d14def2a7f221ace70e31d9d2fb50bf93fe- 1971afbbf204ae4d04b16553a37e61cc6fc276230762f353259e4a0e7e46b439,backup/home/ubuntu/.openclaw/openclaw.json.bak)然后查看$ openclaw config get channels.feishu OpenClaw 2026.3.13(61d171a)— Runs on a Raspberry Pi.Dreams of a rack in Iceland.{enabled: true,appId:cli_a939527feb38dbcc,appSecret:__OPENCLAW_REDACTED__,connectionMode:websocket,domain:feishu,groupPolicy:allowlist,groupAllowlist:[oc_fbe0e81468794e8bf2d13635f70c2138]}15:19:37[plugins]feishu_doc: Registered feishu_doc,feishu_app_scopes 15:19:37[plugins]feishu_chat: Registered feishu_chat tool 15:19:37[plugins]feishu_wiki: Registered feishu_wiki tool 15:19:37[plugins]feishu_drive: Registered feishu_drive tool 15:19:37[plugins]feishu_bitable: Registered bitable tools禁用 elevated 工具$ openclaw configsettools.elevated{enabled: false}然后查看$ openclaw config get tools OpenClaw 2026.3.13(61d171a)— I run on caffeine,JSON5,and the audacity ofit worked on my machine.{profile:coding,elevated:{enabled: false}}2.2 开放群组 runtime/filesystem 工具暴露2.2.1 问题本质agents.defaults 配置危险sandboxoff关闭沙箱runtime: [exec, process] (允许执行系统命令和管理进程)fs: [read, write] (允许读写文件系统)2.2.2 攻击场景任何飞书群成员均可通过构造恶意提示词让机器人执行任意系统命令或删除/窃取服务器文件:提示词注入 → 读取 /etc/passwd、写入 WebShell、执行任意命令2.2.3 修改# 1. 强制沙箱模式为 all$ openclaw configsetagents.defaults.sandbox.modeoff# 禁用工具$ openclaw configsettools.deny[exec,process]# 设置 fs 工具仅在工作目录$ openclaw configsettools.fs.workspaceOnly true# 设置飞书工具为 messaging 模式仅消息功能$ openclaw configsetchannels.feishu.tools.profilemessaging2.3 WARN: 反向代理头未信任2.3.1 风险如果通过 Nginx/Apache 暴露 Control UI无法识别真实客户端 IP可能绕过 IP 白名单2.3.2 修复查看需要加入白名单的IP$ curl ipinfo.io/IP 114.106.107.153把IP 加入白名单$ openclaw configsetgateway.trustedProxies[114.106.107.153]2.4 WARN: 飞书文档创建权限泄露2.4.1 问题feishu_doc.create 会自动给调用者飞书用户授予文档权限2.4.2 攻击场景攻击者让机器人创建文档 → 自动获得该文档编辑权 → 可能用于传播恶意内容2.4.2 修复openclaw configsetchannels.feishu.tools.doc false2.5 WARN: denyCommands 配置无效2.5.1 问题gateway.nodes.denyCommands 只匹配精确命令名不匹配命令内容2.5.2 修复openclaw configsetgateway.nodes.denyCommands[system.run]3. 检查检验3.1 检查整体服务状态$ openclaw status OpenClaw 2026.3.13(61d171a)— Claws out,commit in—lets ship something mildly responsible.18:41:54[plugins]feishu_doc: Registered feishu_app_scopes 18:41:54[plugins]feishu_chat: Registered feishu_chat tool 18:41:54[plugins]feishu_wiki: Registered feishu_wiki tool 18:41:54[plugins]feishu_drive: Registered feishu_drive tool 18:41:54[plugins]feishu_bitable: Registered bitable tools │ 18:41:54[plugins]feishu_doc: Registered feishu_app_scopes 18:41:54[plugins]feishu_chat: Registered feishu_chat tool 18:41:54[plugins]feishu_wiki: Registered feishu_wiki tool 18:41:54[plugins]feishu_drive: Registered feishu_drive tool 18:41:54[plugins]feishu_bitable: Registered bitable tools ◇ │ ◇ OpenClaw status Overview ┌─────────────────┬─────────────────────────────────────────────────────────────────────────────────────────────────────┐ │ Item │ Value │ ├─────────────────┼─────────────────────────────────────────────────────────────────────────────────────────────────────┤ │ Dashboard │ http://127.0.0.1:18789/ │ │ OS │ linux 6.8.0-71-generic(x64)· node 24.14.0 │ │ Tailscale │ off │ │ Channel │ stable(default)│ │ Update │ pnpm · npm latest 2026.3.13 │ │ Gateway │ local · ws://127.0.0.1:18789(local loopback)· unreachable(missing scope: operator.read)│ │ Gateway service │ systemd installed · enabled · running(pid 1130434,state active)│ │ Node service │ systemd not installed │ │ Agents │ 1 · 1 bootstrap file present · sessions 2 · default main active 3h ago │ │ Memory │ 0 files · 0 chunks · dirty · sources memory · plugin memory-core · vector unknown · fts ready · │ │ │ cache on(0)│ │ Probes │ skipped(use--deep)│ │ Events │ none │ │ Heartbeat │ 30m(main)│ │ Sessions │ 2 active · default MiniMax-M2.5(200k ctx)· ~/.openclaw/agents/main/sessions/sessions.json │ └─────────────────┴─────────────────────────────────────────────────────────────────────────────────────────────────────┘ Security audit Summary: 0 critical · 0 warn · 1 info No critical or warn findings detected.Full report: openclaw security audit Deep probe: openclaw security audit--deep Channels ┌──────────┬─────────┬────────┬─────────────────────────────────────────────────────────────────────────────────────────┐ │ Channel │ Enabled │ State │ Detail │ ├──────────┼─────────┼────────┼─────────────────────────────────────────────────────────────────────────────────────────┤ │ Feishu │ ON │ OK │ configured │ └──────────┴─────────┴────────┴─────────────────────────────────────────────────────────────────────────────────────────┘ Sessions ┌─────────────────────────────────────────────────────┬────────┬─────────┬──────────────┬───────────────────────────────┐ │ Key │ Kind │ Age │ Model │ Tokens │ ├─────────────────────────────────────────────────────┼────────┼─────────┼──────────────┼───────────────────────────────┤ │ agent:main:feishu:group:oc_fbe0… │group│ 3h ago │ MiniMax-M2.5 │ 15k/200k(7%)· ️ 69% cached │ │ agent:main:feishu:direct:ou_d9b… │ direct │ 21h ago │ MiniMax-M2.5 │ 13k/200k(6%)· ️ 25% cached │在这里插入代码片 └─────────────────────────────────────────────────────┴────────┴─────────┴──────────────┴───────────────────────────────┘ FAQ: https://docs.openclaw.ai/faq Troubleshooting: https://docs.openclaw.ai/troubleshooting Next steps: Need to share? openclaw status--all Need to debug live? openclaw logs--follow Fix reachability first: openclaw gateway probe3.2 检查 Gateway 运行状态$ openclaw gateway status OpenClaw 2026.3.13(61d171a)— Welcome to the command line: where dreams compile and confidence segfaults.18:43:34[plugins]feishu_doc: Registered feishu_app_scopes 18:43:34[plugins]feishu_chat: Registered feishu_chat tool 18:43:34[plugins]feishu_wiki: Registered feishu_wiki tool 18:43:34[plugins]feishu_drive: Registered feishu_drive tool 18:43:34[plugins]feishu_bitable: Registered bitable tools │ ◇ Service: systemd(enabled)File logs:/tmp/openclaw/openclaw-2026-03-17.log Command:/home/ubuntu/.nvm/versions/node/v24.14.0/bin/node/home/ubuntu/.nvm/versions/node/v24.14.0/lib/node_modules/openclaw/dist/index.js gateway--port 18789 Service file: ~/.config/systemd/user/openclaw-gateway.service Service env: OPENCLAW_GATEWAY_PORT18789 Service config looks out of date or non-standard.Service config issue: Gateway service uses Nodefroma version manager;it canbreakafter upgrades.(/home/ubuntu/.nvm/versions/node/v24.14.0/bin/node)Service config issue: System Node 22 LTS(22.16)or Node 24 not found;install it before migrating awayfromversion managers.Recommendation: runopenclaw doctor(oropenclaw doctor --repair).Config(cli): ~/.openclaw/openclaw.json Config(service): ~/.openclaw/openclaw.json Gateway: bindloopback(127.0.0.1),port18789(service args)Probe target: ws://127.0.0.1:18789 Dashboard: http://127.0.0.1:18789/ Probe note: Loopback-only gateway;only local clients can connect.Runtime: running(pid 1130434,state active,sub running,lastexit0,reason 0)RPC probe: ok Listening: 127.0.0.1:18789 Troubles: run openclaw status Troubleshooting: https://docs.openclaw.ai/troubleshooting3.3 执行全面诊断$ openclaw doctor3.4 检查通信渠道连通性$ openclaw channels status--probe OpenClaw 2026.3.13(61d171a)— iMessage green bubble energy,butforeveryone.18:47:46[plugins]feishu_doc: Registered feishu_app_scopes 18:47:46[plugins]feishu_chat: Registered feishu_chat tool 18:47:46[plugins]feishu_wiki: Registered feishu_wiki tool 18:47:46[plugins]feishu_drive: Registered feishu_drive tool 18:47:46[plugins]feishu_bitable: Registered bitable tools │ 18:47:46[plugins]feishu_doc: Registered feishu_app_scopes 18:47:46[plugins]feishu_chat: Registered feishu_chat tool 18:47:46[plugins]feishu_wiki: Registered feishu_wiki tool 18:47:46[plugins]feishu_drive: Registered feishu_drive tool 18:47:46[plugins]feishu_bitable: Registered bitable tools ◇ Gateway reachable.-Feishu default: enabled,configured,running,works Tip: status--deep adds gateway health probes to status output(requires a reachable gateway).3.5 实时查看日志$ openclaw logs--follow3.6 查看占用端口的进程$ lsof-i :18789 COMMAND PID USER FDTYPEDEVICE SIZE/OFF NODE NAME openclaw- 1136191 ubuntu 22u IPv4 5821514 0t0 TCP localhost:18789(LISTEN)openclaw- 1136191 ubuntu 23u IPv6 5821515 0t0 TCP ip6-localhost:18789(LISTEN)
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。如若转载,请注明出处:http://www.coloradmin.cn/o/2422359.html
如若内容造成侵权/违法违规/事实不符,请联系多彩编程网进行投诉反馈,一经查实,立即删除!相关文章
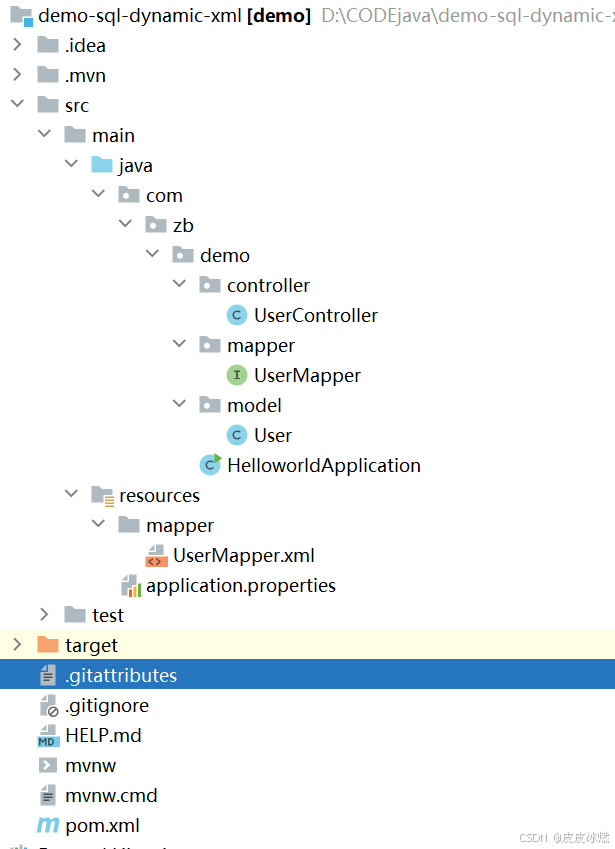
SpringBoot-17-MyBatis动态SQL标签之常用标签
文章目录 1 代码1.1 实体User.java1.2 接口UserMapper.java1.3 映射UserMapper.xml1.3.1 标签if1.3.2 标签if和where1.3.3 标签choose和when和otherwise1.4 UserController.java2 常用动态SQL标签2.1 标签set2.1.1 UserMapper.java2.1.2 UserMapper.xml2.1.3 UserController.ja…
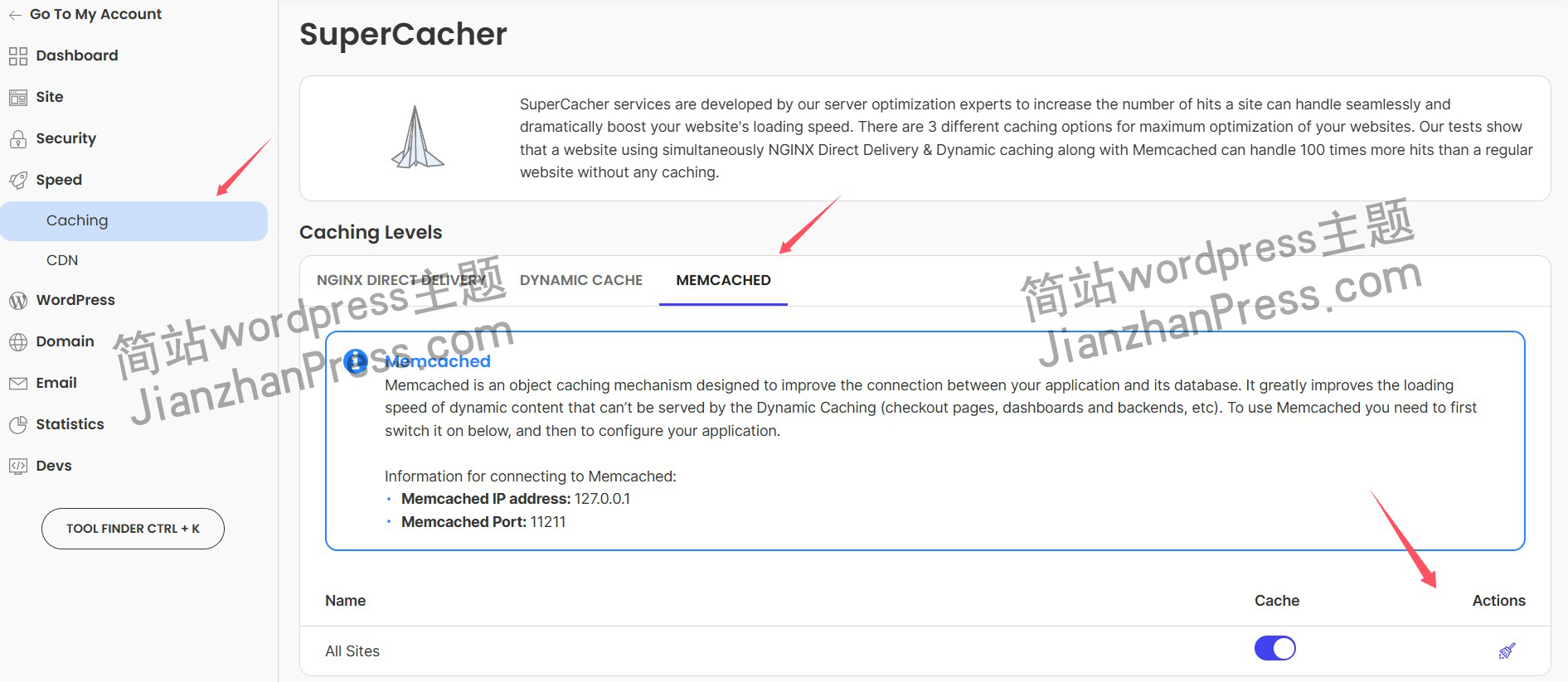
wordpress后台更新后 前端没变化的解决方法
使用siteground主机的wordpress网站,会出现更新了网站内容和修改了php模板文件、js文件、css文件、图片文件后,网站没有变化的情况。
不熟悉siteground主机的新手,遇到这个问题,就很抓狂,明明是哪都没操作错误&#x…
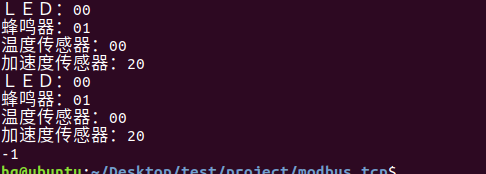
网络编程(Modbus进阶)
思维导图 Modbus RTU(先学一点理论)
概念 Modbus RTU 是工业自动化领域 最广泛应用的串行通信协议,由 Modicon 公司(现施耐德电气)于 1979 年推出。它以 高效率、强健性、易实现的特点成为工业控制系统的通信标准。 包…
UE5 学习系列(二)用户操作界面及介绍
这篇博客是 UE5 学习系列博客的第二篇,在第一篇的基础上展开这篇内容。博客参考的 B 站视频资料和第一篇的链接如下:
【Note】:如果你已经完成安装等操作,可以只执行第一篇博客中 2. 新建一个空白游戏项目 章节操作,重…
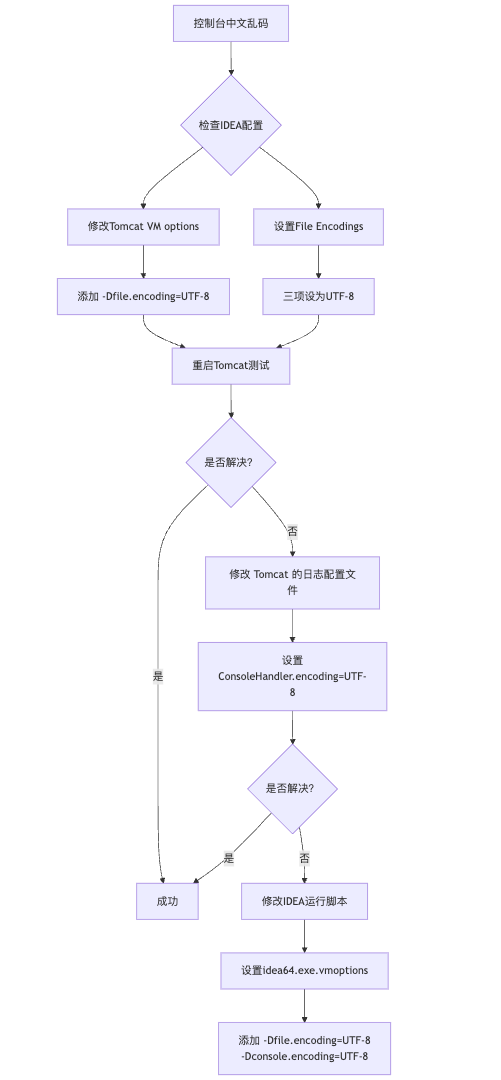
IDEA运行Tomcat出现乱码问题解决汇总
最近正值期末周,有很多同学在写期末Java web作业时,运行tomcat出现乱码问题,经过多次解决与研究,我做了如下整理:
原因:
IDEA本身编码与tomcat的编码与Windows编码不同导致,Windows 系统控制台…
利用最小二乘法找圆心和半径
#include <iostream>
#include <vector>
#include <cmath>
#include <Eigen/Dense> // 需安装Eigen库用于矩阵运算 // 定义点结构
struct Point { double x, y; Point(double x_, double y_) : x(x_), y(y_) {}
}; // 最小二乘法求圆心和半径 …
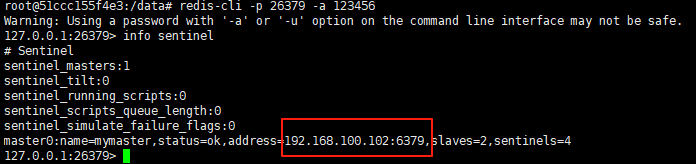
使用docker在3台服务器上搭建基于redis 6.x的一主两从三台均是哨兵模式
一、环境及版本说明
如果服务器已经安装了docker,则忽略此步骤,如果没有安装,则可以按照一下方式安装: 1. 在线安装(有互联网环境): 请看我这篇文章 传送阵>> 点我查看 2. 离线安装(内网环境):请看我这篇文章 传送阵>> 点我查看
说明:假设每台服务器已…
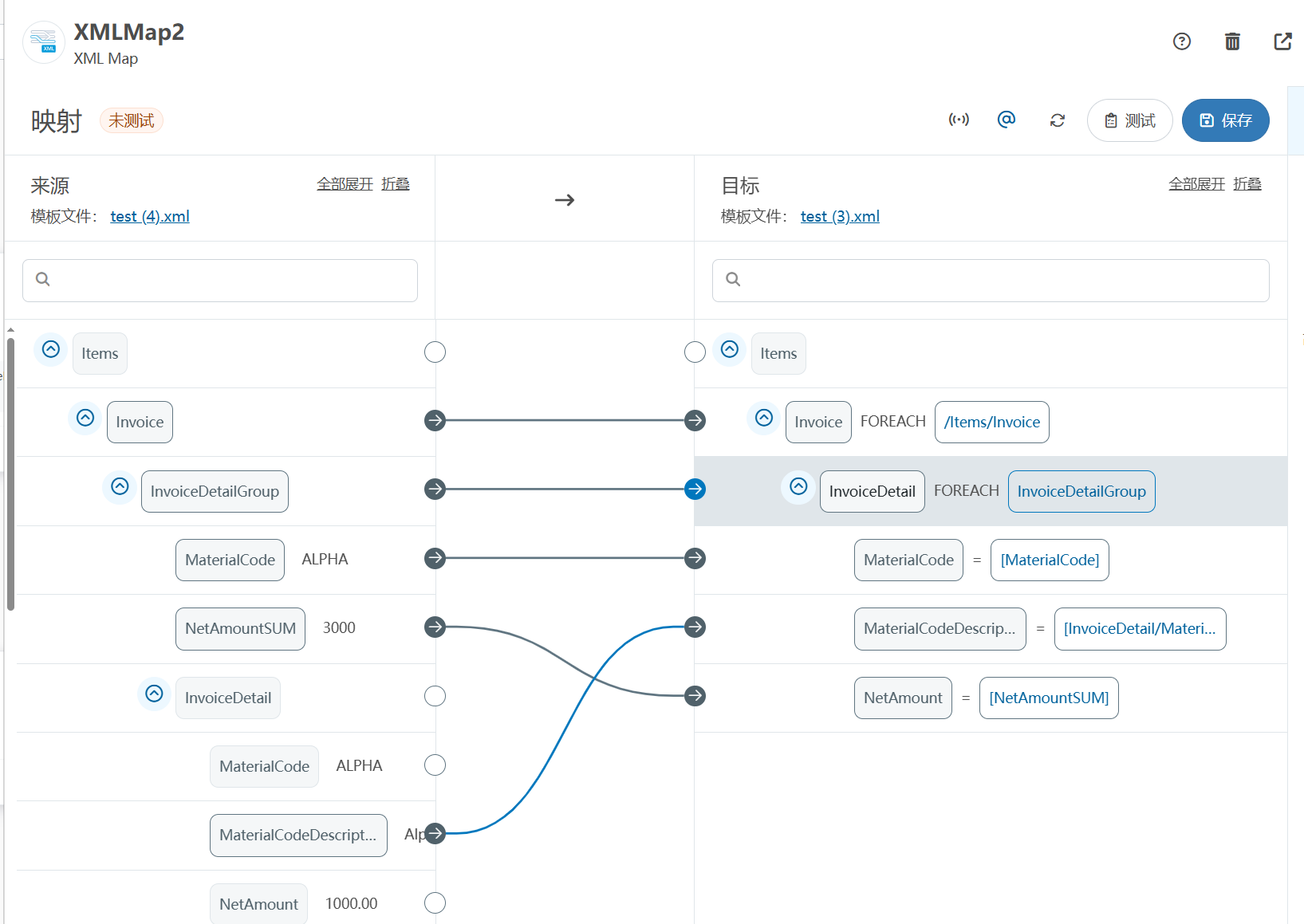
XML Group端口详解
在XML数据映射过程中,经常需要对数据进行分组聚合操作。例如,当处理包含多个物料明细的XML文件时,可能需要将相同物料号的明细归为一组,或对相同物料号的数量进行求和计算。传统实现方式通常需要编写脚本代码,增加了开…
LBE-LEX系列工业语音播放器|预警播报器|喇叭蜂鸣器的上位机配置操作说明
LBE-LEX系列工业语音播放器|预警播报器|喇叭蜂鸣器专为工业环境精心打造,完美适配AGV和无人叉车。同时,集成以太网与语音合成技术,为各类高级系统(如MES、调度系统、库位管理、立库等)提供高效便捷的语音交互体验。
L…
(LeetCode 每日一题) 3442. 奇偶频次间的最大差值 I (哈希、字符串)
题目:3442. 奇偶频次间的最大差值 I 思路 :哈希,时间复杂度0(n)。 用哈希表来记录每个字符串中字符的分布情况,哈希表这里用数组即可实现。
C版本:
class Solution {
public:int maxDifference(string s) {int a[26]…
【大模型RAG】拍照搜题技术架构速览:三层管道、两级检索、兜底大模型
摘要
拍照搜题系统采用“三层管道(多模态 OCR → 语义检索 → 答案渲染)、两级检索(倒排 BM25 向量 HNSW)并以大语言模型兜底”的整体框架: 多模态 OCR 层 将题目图片经过超分、去噪、倾斜校正后,分别用…
【Axure高保真原型】引导弹窗
今天和大家中分享引导弹窗的原型模板,载入页面后,会显示引导弹窗,适用于引导用户使用页面,点击完成后,会显示下一个引导弹窗,直至最后一个引导弹窗完成后进入首页。具体效果可以点击下方视频观看或打开下方…
接口测试中缓存处理策略
在接口测试中,缓存处理策略是一个关键环节,直接影响测试结果的准确性和可靠性。合理的缓存处理策略能够确保测试环境的一致性,避免因缓存数据导致的测试偏差。以下是接口测试中常见的缓存处理策略及其详细说明:
一、缓存处理的核…
龙虎榜——20250610
上证指数放量收阴线,个股多数下跌,盘中受消息影响大幅波动。 深证指数放量收阴线形成顶分型,指数短线有调整的需求,大概需要一两天。 2025年6月10日龙虎榜行业方向分析 1. 金融科技
代表标的:御银股份、雄帝科技
驱动…
观成科技:隐蔽隧道工具Ligolo-ng加密流量分析
1.工具介绍
Ligolo-ng是一款由go编写的高效隧道工具,该工具基于TUN接口实现其功能,利用反向TCP/TLS连接建立一条隐蔽的通信信道,支持使用Let’s Encrypt自动生成证书。Ligolo-ng的通信隐蔽性体现在其支持多种连接方式,适应复杂网…
铭豹扩展坞 USB转网口 突然无法识别解决方法
当 USB 转网口扩展坞在一台笔记本上无法识别,但在其他电脑上正常工作时,问题通常出在笔记本自身或其与扩展坞的兼容性上。以下是系统化的定位思路和排查步骤,帮助你快速找到故障原因:
背景:
一个M-pard(铭豹)扩展坞的网卡突然无法识别了,扩展出来的三个USB接口正常。…
未来机器人的大脑:如何用神经网络模拟器实现更智能的决策?
编辑:陈萍萍的公主一点人工一点智能 未来机器人的大脑:如何用神经网络模拟器实现更智能的决策?RWM通过双自回归机制有效解决了复合误差、部分可观测性和随机动力学等关键挑战,在不依赖领域特定归纳偏见的条件下实现了卓越的预测准…
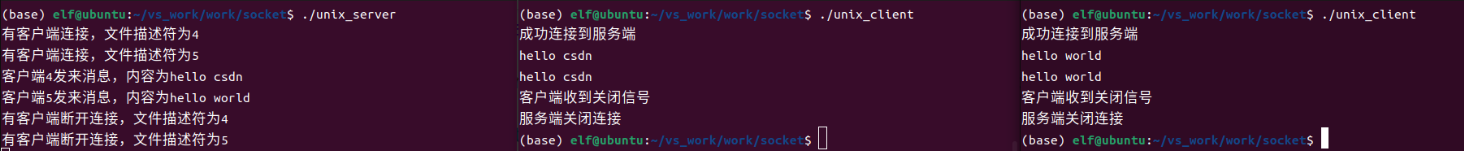
Linux应用开发之网络套接字编程(实例篇)
服务端与客户端单连接
服务端代码
#include <sys/socket.h>
#include <sys/types.h>
#include <netinet/in.h>
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <arpa/inet.h>
#include <pthread.h>
…
华为云AI开发平台ModelArts
华为云ModelArts:重塑AI开发流程的“智能引擎”与“创新加速器”!
在人工智能浪潮席卷全球的2025年,企业拥抱AI的意愿空前高涨,但技术门槛高、流程复杂、资源投入巨大的现实,却让许多创新构想止步于实验室。数据科学家…
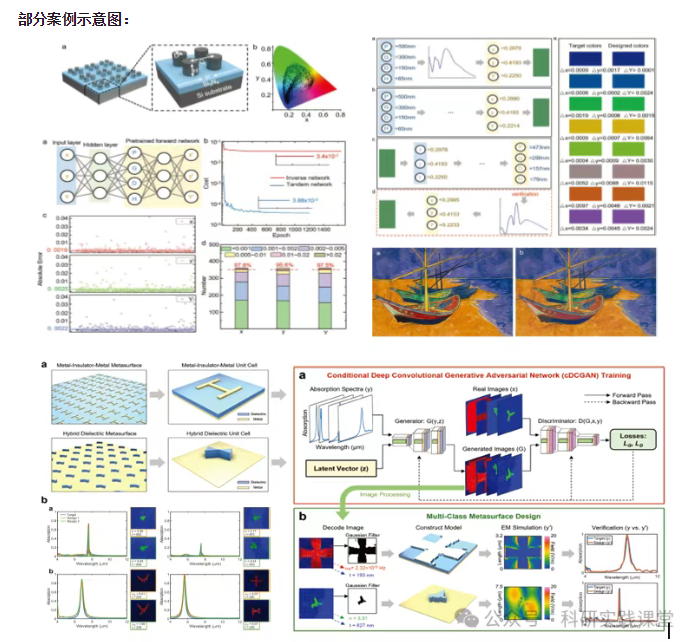
深度学习在微纳光子学中的应用
深度学习在微纳光子学中的主要应用方向
深度学习与微纳光子学的结合主要集中在以下几个方向:
逆向设计 通过神经网络快速预测微纳结构的光学响应,替代传统耗时的数值模拟方法。例如设计超表面、光子晶体等结构。
特征提取与优化 从复杂的光学数据中自…